正文
解压后得到图片:
图片属性正常,无特殊点,经测试,无隐写文件:

Stegsolve
运行方法:

可以看到出现二维码:

对其解密得到:

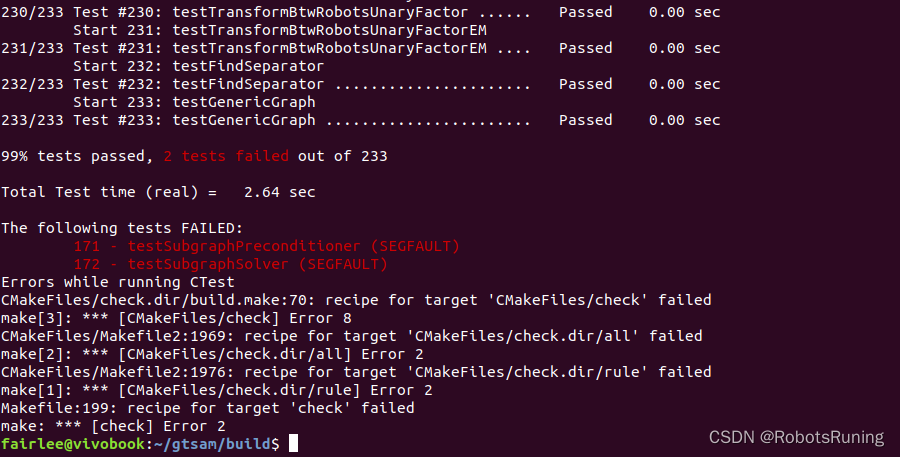
03F30D0A79CB05586300000000000000000100000040000000730D0000006400008400005A000064010053280200000063000000000300000016000000430000007378000000640100640200640300640400640500640600640700640300640800640900640A00640600640B00640A00640700640800640C00640C00640D00640E00640900640F006716007D00006410007D0100781E007C0000445D16007D02007C01007400007C0200830100377D0100715500577C010047486400005328110000004E6966000000696C00000069610000006967000000697B000000693300000069380000006935000000693700000069300000006932000000693400000069310000006965000000697D000000740000000028010000007403000000636872280300000074030000007374727404000000666C6167740100000069280000000028000000007304000000312E7079520300000001000000730A0000000001480106010D0114014E280100000052030000002800000000280000000028000000007304000000312E707974080000003C6D6F64756C653E010000007300000000
Winhex
使用 winhex 工具进行解码,选择 AscII Hex:
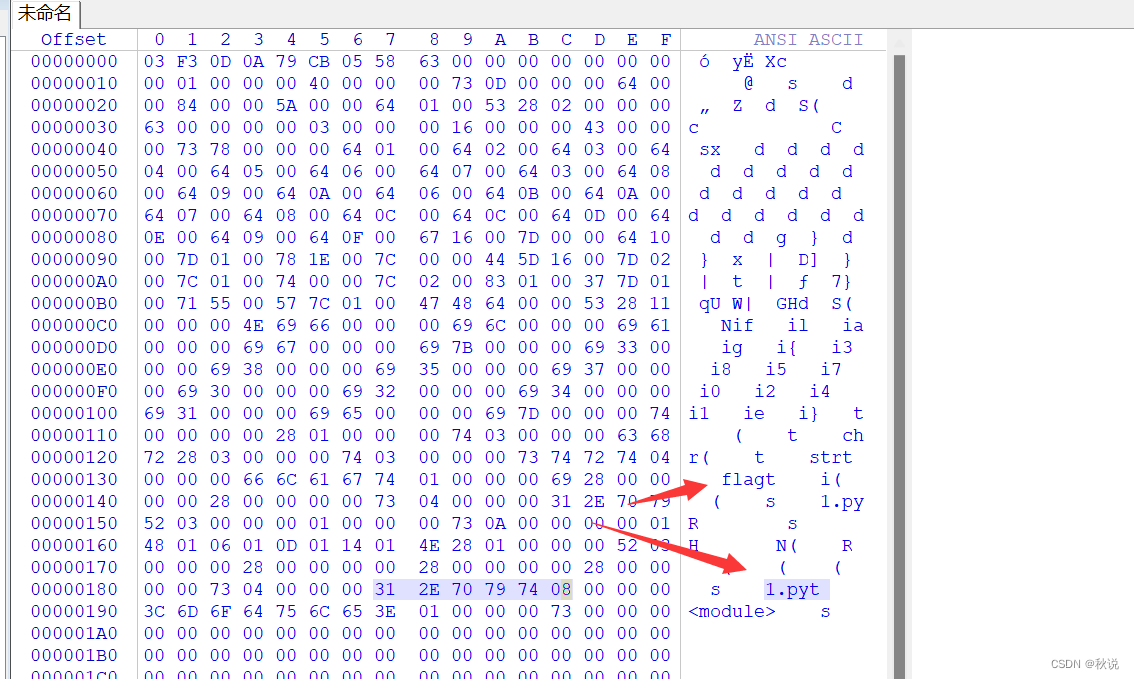
由图中字段,推断这是一个 python 进行编译之后生成的 pyc 文件(一种二进制文件)
将其反编译:
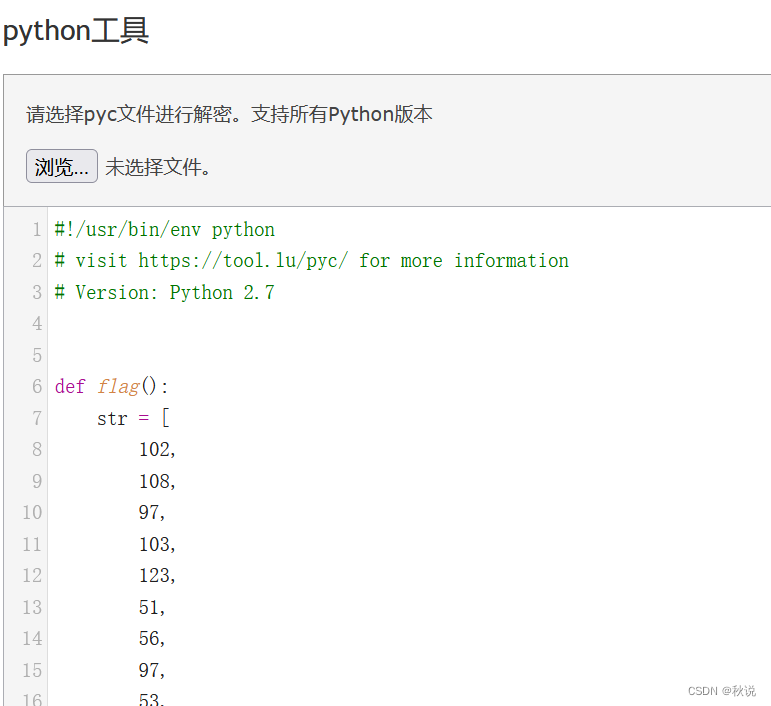
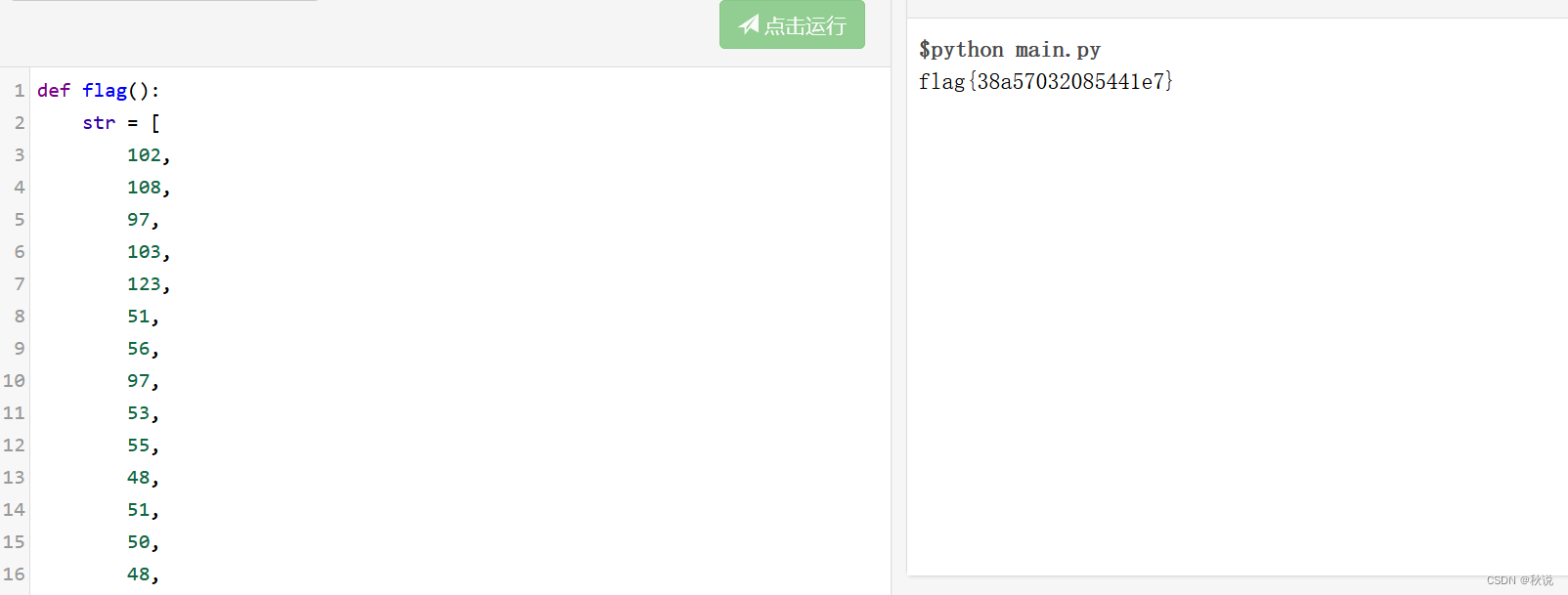
得到:
def flag():str = [102,108,97,103,123,51,56,97,53,55,48,51,50,48,56,53,52,52,49,101,55,125]flag = ''for i in str:flag += chr(i)print flag运行即可: