GitLab 是一个全球知名的一体化 DevOps 平台,很多人都通过私有化部署 GitLab 来进行源代码托管。极狐GitLab :https://gitlab.cn/install?channel=content&utm_source=csdn 是 GitLab 在中国的发行版,专门为中国程序员服务。可以一键式部署极狐GitLab。
更多关于极狐GitLab :https://gitlab.cn 或者 DevOps 的最佳实践,可以关注文末的极狐GitLab 公众号。
学习极狐GitLab 的相关资料:
- 极狐GitLab 官网:https://gitlab.cn
- 极狐GitLab 官网文档:https://docs.gitlab.cn
- 极狐GitLab 论坛:https://forum.gitlab.cn/
- 极狐GitLab 安装配置:https://gitlab.cn/install
- 极狐GitLab 资源中心:https://resources.gitlab.cn
搜索【极狐GitLab】公众号,后台输入加群,备注gitlab,即可加入官方微信技术交流群。
极狐GitLab 公众号后台回复新手指南,免费领取极狐GitLab 新手指南一份,从零到一快速上手极狐GitLab。
关联阅读
- 极狐GitLab 容器镜像安全扫描实践【上】
- 极狐GitLab 镜像仓库的使用技巧
极狐GitLab 镜像安全扫描实践
极狐GitLab 的镜像安全扫描是通过极狐GitLab 容器镜像分析器(container-scanning analyzer)来实现的,分析器使用的镜像有多个,这个取决于环境变量 CS_ANALYZER_IMAGE 的值,可用的选项有:
registry.gitlab.com/security-products/container-scanning:4
registry.gitlab.com/security-products/container-scanning/grype:4
registry.gitlab.com/security-products/container-scanning/trivy:4
可以用上面的任意一个镜像来构建分析器,从而完成镜像安全扫描。分析器可以单独使用,也可以和极狐GitLab CI/CD 做集成。先来看如何单独使用极狐GitLab 容器镜像分析器来做镜像安全扫描。
单独使用极狐GitLab 镜像扫描工具
使用如下命令即可单独使用极狐GitLab 容器镜像分析器来扫描容器镜像:
$ docker run -i --rm -e DOCKER_IMAGE=alpine registry.gitlab.com/security-products/container-scanning/trivy:4
参数含义:
- DOCKER_IMAGE:指定需要扫描的镜像,比如 alpine
- registry.gitlab.com/security-products/container-scanning/trivy:4 :极狐GitLab 镜像分析器所使用的镜像
可以看到如下结果:
[INFO] [2021-10-22 03:05:10 +0000] [] ▶ Remediation is disabled; /home/gitlab/Dockerfile cannot be found. Have you set `GIT_STRATEGY` and
`DOCKERFILE_PATH`?
See https://docs.gitlab.com/ee/user/application_security/container_scanning/#solutions-for-vulnerabilities-auto-remediation[INFO] [2021-10-22 03:05:10 +0000] [] ▶ Scanning container from registry alpine for vulnerabilities with severity level UNKNOWN or higher, with gcs 4.3.17 and Trivy Version: 0.19.2, advisories updated at 2021-10-21[INFO] [2021-10-22 03:05:17 +0000] [] ▶ 2021-10-22T03:05:17.677Z INFO Detected OS: alpine
2021-10-22T03:05:17.677Z INFO Detecting Alpine vulnerabilities...
可以看到极狐GitLab 容器扫描工具的版本:gcs 4.3.17,使用的 trivy 版本是:0.19.2。扫描的结果和前面的 trivy 、grype 是一样的。对于 alpine:latest 没有扫出来安全漏洞。再试一个有漏洞的镜像(alpine:3.10),再看看结果是如何展示的:
$ docker run -i --rm -e DOCKER_IMAGE=alpine:3.10 registry.gitlab.com/security-products/container-scanning/trivy:4
[INFO] [2021-10-22 03:12:20 +0000] [] ▶ Remediation is disabled; /home/gitlab/Dockerfile cannot be found. Have you set `GIT_STRATEGY` and
`DOCKERFILE_PATH`?
See https://docs.gitlab.com/ee/user/application_security/container_scanning/#solutions-for-vulnerabilities-auto-remediation[INFO] [2021-10-22 03:12:20 +0000] [] ▶ Scanning container from registry alpine:3.10 for vulnerabilities with severity level UNKNOWN or higher, with gcs 4.3.17 and Trivy Version: 0.19.2, advisories updated at 2021-10-21[INFO] [2021-10-22 03:12:35 +0000] [] ▶ 2021-10-22T03:12:35.545Z INFO Detected OS: alpine
2021-10-22T03:12:35.545Z INFO Detecting Alpine vulnerabilities...
2021-10-22T03:12:35.545Z WARN This OS version is no longer supported by the distribution: alpine 3.10.9
2021-10-22T03:12:35.545Z WARN The vulnerability detection may be insufficient because security updates are not provided+------------+-------------------------+--------------+-----------------+------------------------------------------------------------------------+
| STATUS | CVE SEVERITY | PACKAGE NAME | PACKAGE VERSION | CVE DESCRIPTION |
+------------+-------------------------+--------------+-----------------+------------------------------------------------------------------------+
| Unapproved | Critical CVE-2021-36159 | apk-tools | 2.10.6-r0 | libfetch before 2021-07-26, as used in apk-tools, xbps, and other prod |
| | | | | ucts, mishandles numeric strings for the FTP and HTTP protocols. The F |
| | | | | TP passive mode implementation allows an out-of-bounds read because st |
| | | | | rtol is used to parse the relevant numbers into address bytes. It does |
| | | | | not check if the line ends prematurely. If it does, the for-loop cond |
| | | | | ition checks for the '\0' terminator one byte too late. |
+------------+-------------------------+--------------+-----------------+------------------------------------------------------------------------+
可以看到扫描结果会展示漏洞的严重等级(SEVERITY)、漏洞的详细内容(DESCRIPTION)。
和极狐GitLab CI 集成使用
可以很容易的在极狐GitLab CI 中集成镜像扫描:
variables:CS_ANALYZER_IMAGE: registry.gitlab.com/security-products/container-scanning/trivy:4services:- docker:20.10.7-dindstages: - testcontainer_scanning:image: "$CS_ANALYZER_IMAGE"stage: testvariables:GIT_STRATEGY: fetchDOCKER_IMAGE: alpine:3.10allow_failure: trueartifacts:reports:container_scanning: gl-container-scanning-report.jsonpaths: [gl-container-scanning-report.json]dependencies: []script:- gtcs scan
极狐GitLab CI 语法解释:
- CS_ANALYZER_IMAGE:指定极狐GitLab 镜像分析器所使用的镜像
- DOCKER_IMAGE:指定所要扫描的镜像,本例为 alpine:3.10
- allow_failure:允许 job 失败,同时不阻塞后续的 CI 流程
- artifacts:可以将构建结果,诸如此次的扫描结果存储在极狐GitLab 的 artifacts 中,方便用户下载查看
- gtcs scan:极狐GitLab 容器镜像分析器的镜像扫描命令
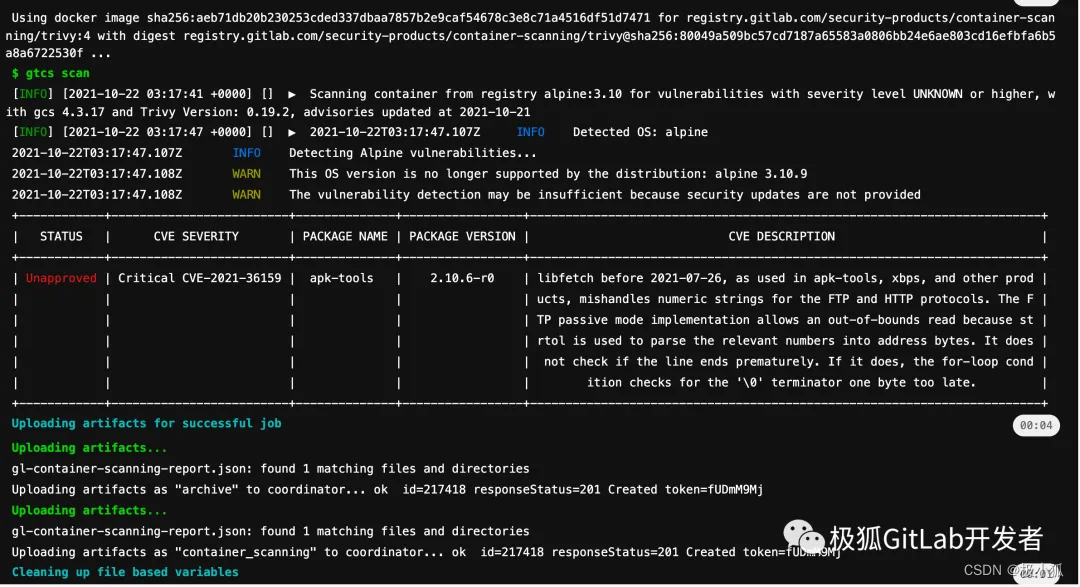
可以在 Pipeline 的构建中看到如下构建日志:
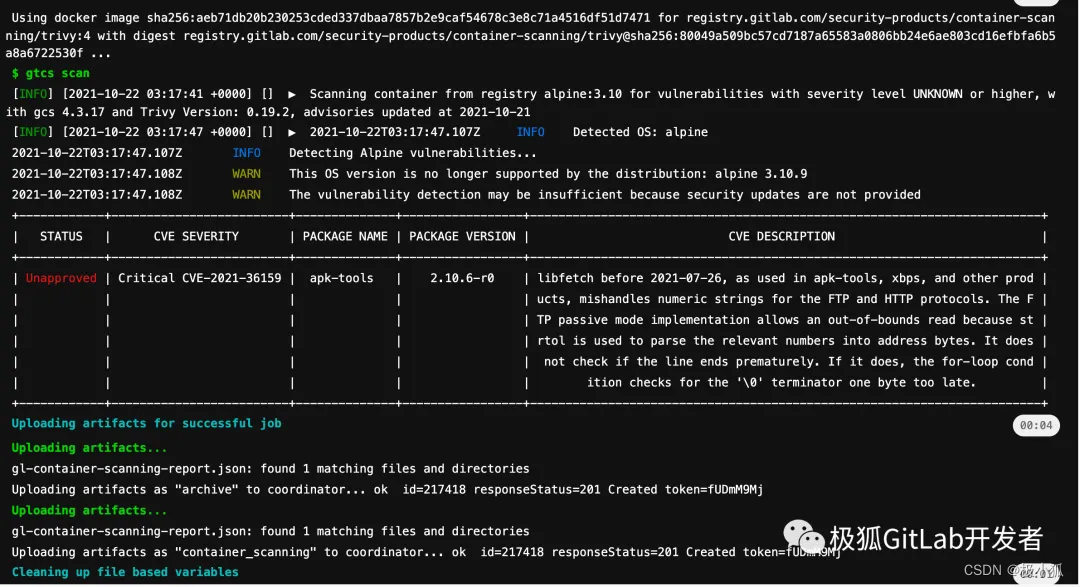
扫描结果和单独使用极狐GitLab 镜像分析器时的结果是一样的。
当然也可以很方便的下载镜像扫描报告:
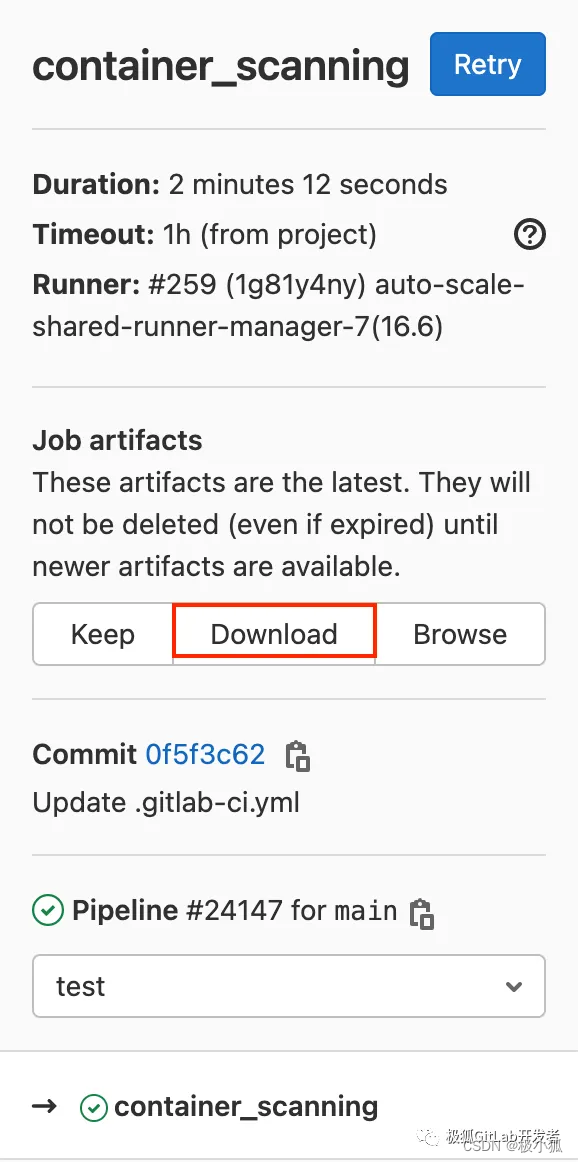
下载完毕之后,可以解析查看结果:
{"version": "14.0.3","vulnerabilities": [{"id": "0aa27b90612e559bb5accde4025d57ecc1932885","category": "container_scanning","message": "CVE-2021-36159 in apk-tools-2.10.6-r0","description": "libfetch before 2021-07-26, as used in apk-tools, xbps, and other products, mishandles numeric strings for the FTP and HTTP protocols. The FTP passive mode implementation allows an out-of-bounds read because strtol is used to parse the relevant numbers into address bytes. It does not check if the line ends prematurely. If it does, the for-loop condition checks for the '\\0' terminator one byte too late.","cve": "CVE-2021-36159","severity": "Critical","confidence": "Unknown","solution": "Upgrade apk-tools to 2.10.7-r0","scanner": {"id": "trivy","name": "trivy"},"location": {"dependency": {"package": {"name": "apk-tools"},"version": "2.10.6-r0"},"operating_system": "alpine 3.10.9","image": "registry.gitlab.cn/majinghe/go-demo:3.0.0"},"identifiers": [{"type": "cve","name": "CVE-2021-36159","value": "CVE-2021-36159","url": "https://github.com/freebsd/freebsd-src/commits/main/lib/libfetch"}],"links": [{"url": "https://github.com/freebsd/freebsd-src/commits/main/lib/libfetch"},{"url": "https://gitlab.alpinelinux.org/alpine/apk-tools/-/issues/10749"},{"url": "https://lists.apache.org/thread.html/r61db8e7dcb56dc000a5387a88f7a473bacec5ee01b9ff3f55308aacc@%3Cdev.kafka.apache.org%3E"},{"url": "https://lists.apache.org/thread.html/r61db8e7dcb56dc000a5387a88f7a473bacec5ee01b9ff3f55308aacc@%3Cusers.kafka.apache.org%3E"},{"url": "https://lists.apache.org/thread.html/rbf4ce74b0d1fa9810dec50ba3ace0caeea677af7c27a97111c06ccb7@%3Cdev.kafka.apache.org%3E"},{"url": "https://lists.apache.org/thread.html/rbf4ce74b0d1fa9810dec50ba3ace0caeea677af7c27a97111c06ccb7@%3Cusers.kafka.apache.org%3E"}]}],"remediations": [{"fixes": [{"cve": "CVE-2021-36159","id": "0aa27b90612e559bb5accde4025d57ecc1932885"}],"summary": "Upgrade apk-tools to 2.10.7-r0","diff": "ZGlmZiAtLWdpdCBhL0RvY2tlcmZpbGUgYi9Eb2NrZXJmaWxlCmluZGV4IGU3ZDI5ZWMuLjI4ODNiNzcgMTAwNjQ0Ci0tLSBhL0RvY2tlcmZpbGUKKysrIGIvRG9ja2VyZmlsZQpAQCAtOCw2ICs4LDcgQEAgUlVOIGdvIGJ1aWxkIGRldm9wcy5nbwogCiAjIEZST00gYWxwaW5lOmxhdGVzdAogRlJPTSBhbHBpbmU6My4xMAorUlVOIGFwayAtLW5vLWNhY2hlIHVwZGF0ZSAmJiBhcGsgLS1uby1jYWNoZSBhZGQgYXBrLXRvb2xzPTIuMTAuNy1yMAogCiBXT1JLRElSIC91c3Ivc3JjL2FwcC8="}],"scan": {"scanner": {"id": "trivy","name": "Trivy","url": "https://github.com/aquasecurity/trivy/","vendor": {"name": "GitLab"},"version": "0.19.2"},"analyzer": {"id": "gcs","name": "GitLab Container Scanning","vendor": {"name": "GitLab"},"version": "4.3.17"},"type": "container_scanning","start_time": "2021-10-22T06:38:27","end_time": "2021-10-22T06:38:29","status": "success"}
}
和极狐GitLab 镜像仓库的集成
极狐GitLab 不仅提供开箱即用的 DevSecOps 功能。也提供开箱即用的镜像仓库功能,关于镜像仓库的使用可以查看公众号文章极狐GitLab 镜像仓库的使用技巧。可以直接在极狐 GitLab CI 中使用极狐GitLab 镜像仓库和镜像扫描功能,只需要简单的配置即可,.gitlab-ci.yml 的内容如下:
variables:CS_ANALYZER_IMAGE: registry.gitlab.com/security-products/container-scanning/trivy:4KUBECONFIG: /tmp/.kube/configservices:- docker:20.10.7-dindstages: - build- test- deploybuild:image: docker:lateststage: buildservices:- docker:20.10.7-dindscript:- docker login -u "$CI_REGISTRY_USER" -p "$CI_REGISTRY_PASSWORD" $CI_REGISTRY- docker build -t $CI_REGISTRY_IMAGE:3.0.0 .- docker push $CI_REGISTRY_IMAGE:3.0.0container_scanning:image: "$CS_ANALYZER_IMAGE"stage: testvariables:GIT_STRATEGY: fetchDOCKER_USER: "$CI_REGISTRY_USER"DOCKER_PASSWORD: "$CI_REGISTRY_PASSWORD"DOCKER_IMAGE: $CI_REGISTRY_IMAGE:3.0.0allow_failure: falseartifacts:reports:container_scanning: gl-container-scanning-report.jsonpaths: [gl-container-scanning-report.json]dependencies: []script:- gtcs scandeploy:stage: deployimage:name: bitnami/kubectl:latestentrypoint: [""]script:- mkdir -p /tmp/.kube- echo $kube_config | base64 -d > $KUBECONFIG- kubectl -n gitlab-k8s-demo apply -f deployment.yaml
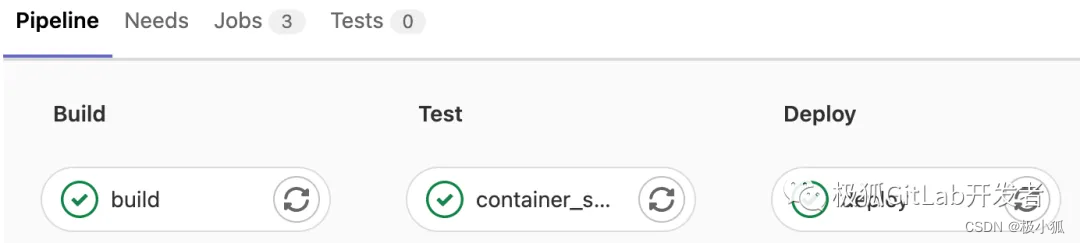
可以在构建结果中看到 Pipeline 流水线如下
 以及在构建日志中看到镜像扫描日志:
以及在构建日志中看到镜像扫描日志:
可以看到,可以用极狐GitLab 一体化 DevOps 平台来完成源码管理、镜像构建、镜像扫描以及应用程序的部署。只需要简单配置即可。
结束语
安全是一个必须要重视的话题,现在讲的 DevOps 其实就等同于 DevSecOps,真正的 DevOps 是必须要融入安全的,人人为安全负责、处处有安全意识,才能构建起软件供应链安全的护城河。
而极狐GitLab 开箱即用的 DevSecOps 功能是能够为软件开发生命周期的不同阶段提供安全保障能力。从而来保证软件供应链的安全。