cat k8s-events-elasticsearch.yaml# 采集k8s事件(events)到elasticsearch
# https://github.com/AliyunContainerService/kube-eventer
---
apiVersion: apps/v1
kind: Deployment
metadata:labels:name: kube-eventername: kube-eventernamespace: kube-system
spec:replicas: 1selector:matchLabels:app: kube-eventertemplate:metadata:labels:app: kube-eventerannotations: scheduler.alpha.kubernetes.io/critical-pod: ''spec:dnsPolicy: ClusterFirstWithHostNetserviceAccount: kube-eventercontainers:- image: registry.aliyuncs.com/acs/kube-eventer-amd64:v1.2.0-484d9cd-aliyunname: kube-eventercommand:- "/kube-eventer"- "--source=kubernetes:https://kubernetes.default"# elasticsearch- --sink=elasticsearch:http://10.10.2.139:9200?sniff=false&ver=7&index=k8s-event-prod&cluster_name=prodenv:- name: TZvalue: "Asia/Shanghai" volumeMounts:- name: localtimemountPath: /etc/localtimereadOnly: true- name: zoneinfomountPath: /usr/share/zoneinforeadOnly: trueresources:requests:cpu: 100mmemory: 100Milimits:cpu: 500mmemory: 250Mivolumes:- name: localtimehostPath:path: /etc/localtime- name: zoneinfohostPath:path: /usr/share/zoneinfo
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:name: kube-eventer
rules:- apiGroups:- ""resources:- configmaps- eventsverbs:- get- list- watch
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:name: kube-eventer
roleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: kube-eventer
subjects:- kind: ServiceAccountname: kube-eventernamespace: kube-system
---
apiVersion: v1
kind: ServiceAccount
metadata:name: kube-eventernamespace: kube-system
k8s 事件收集到es
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.hqwc.cn/news/738829.html
如若内容造成侵权/违法违规/事实不符,请联系编程知识网进行投诉反馈email:809451989@qq.com,一经查实,立即删除!相关文章
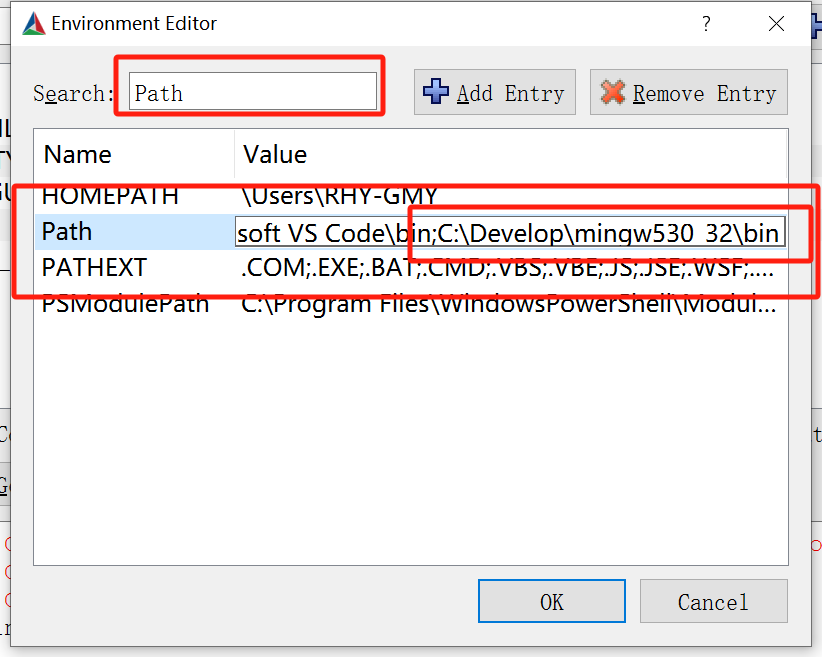
Mingw GCC 编译OpenCV报错: Project files may be invalid
这是一个通用报错弹窗:具体要看下边输出窗口:CMake Error: CMake was unable to find a build program corresponding to "MinGW Makefiles". CMAKE_MAKE_PROGRAM is not set. You probably need to select a different build tool.
CMake Error: CMAKE_CXX_COMPIL…
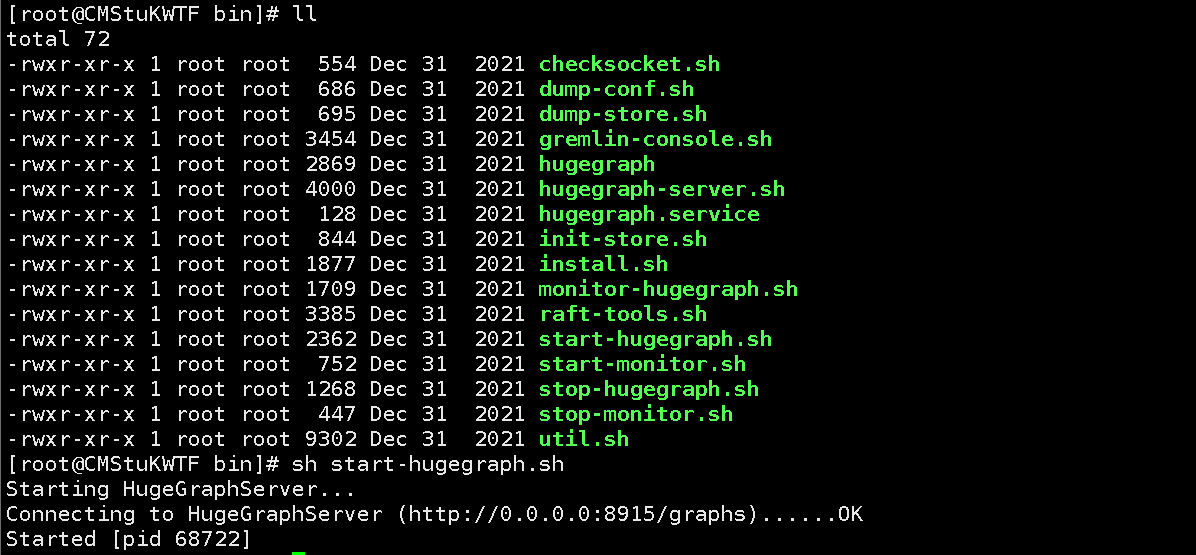
linux部署Hugegraph
HugeGraph是一款易用、高效、通用的开源图数据库系统(Graph Database)。
一、基本概述功能特性:HugeGraph实现了Apache TinkerPop3框架,并完全兼容Gremlin查询语言,具备完善的工具链组件,助力用户轻松构建基于图数据库之上的应用和产品。它支持百亿以上的顶点和边快速导入…
ComfyUI进阶篇:ComfyUI核心节点(一)
ComfyUI进阶篇:ComfyUI核心节点(一)前言:学习ComfyUI是一场持久战。当你掌握了ComfyUI的安装和运行之后,会发现大量五花八门的节点。面对各种各样的工作流和复杂的节点种类,可能会让人感到不知所措。在这篇文章中,我们将用通俗易懂的语言对ComfyUI的核心节点进行系统梳理,…
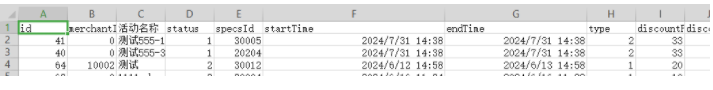
springboot实现登录demo
springboot,Jwt认证,登录实现简单的登录功能
实体类
定义实体类为User3类。
使用@Data:提供类的get,set,equals,hashCode,canEqual,toString方法;
使用@AllArgsConstructor:提供类的全参构造
使用@NoArgsConstructor:提供类的无参构造
类代码如下
@Data
@AllArgsCon…
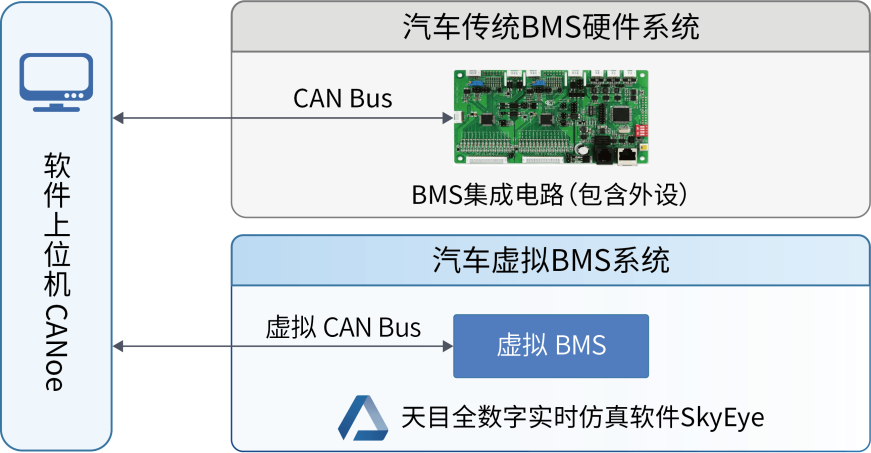
虚拟ECU:纯电动汽车发展下的新选择
人类文明的进步是一个不断自我否定、自我超越的过程。21世纪以来,随着科技进步和经济社会发展,能源和交通系统已从独立于自然环境的孤立系统,转变为与自然、技术、社会深度耦合的复杂系统。为实现可持续发展和应对气候变化,世界各国都在积极推进能源结构调整和技术创新,…
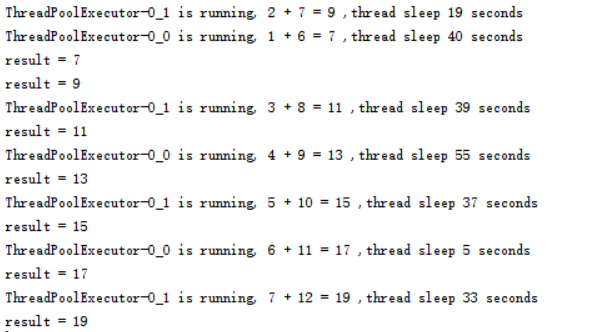
Python多线程-线程池ThreadPoolExecutor
1. 线程池
不是线程数量越多,程序的执行效率就越快。线程也是一个对象,是需要占用资源的,线程数量过多的话肯定会消耗过多的资源,同时线程间的上下文切换也是一笔不小的开销,所以有时候开辟过多的线程不但不会提高程序的执行效率,反而会适得其反使程序变慢,得不偿失。
为…
一个用来画拉氏图的简单Python脚本
这里我提供了一个用于画拉氏图的Python脚本源代码,供大家免费使用。虽然现在也有很多免费的平台和工具可以用,但很多都是黑箱,有需要的开发者可以直接在这个脚本基础上二次开发,定制自己的拉氏图绘制方法。技术背景
关于拉氏图的更多介绍,可以参考下这篇博客,这里简单引述…
如何实现超大场景的三维模型(3D)轻量化
三维工厂K3DMaker是一款三维模型浏览、分析、轻量化、顶层合并构建、几何校正、格式转换、调色裁切等功能专业处理软件。可以进行三维模型的网格简化、纹理压缩、层级优化等操作,从而实现三维模型轻量化。轻量化压缩比大,模型轻量化效率高,自动化处理能力高;采用多种算法对…
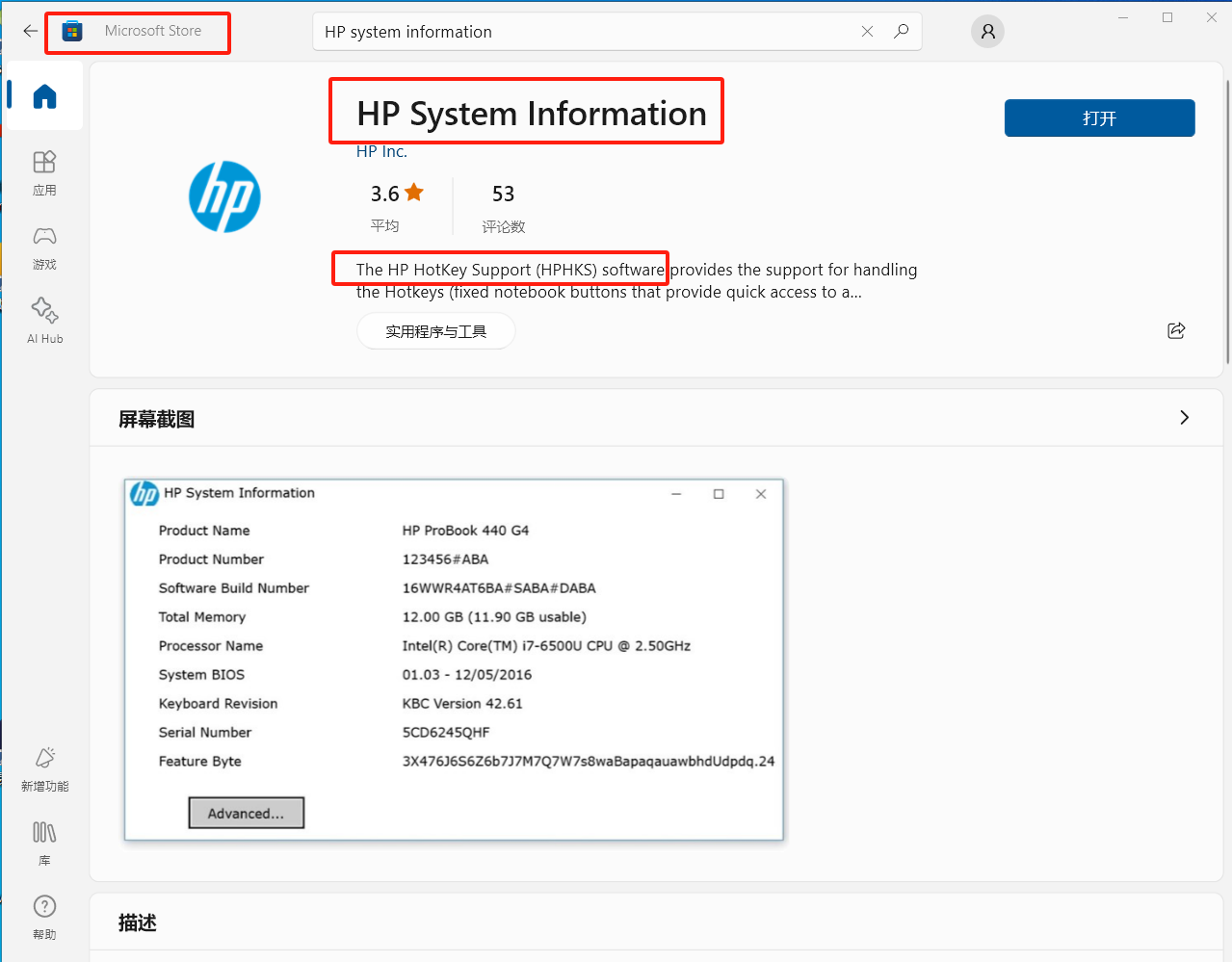
HP惠普笔记本使用问题和开启TPM
HP电脑使用
开机按F10,进入BIOS,如果是英文,切换到 Advanced,选择 Display Language,选择 简体中文然后返回上一页,切换到 安全引导配置 选择“启用传统支持和禁用安全引导”,然后F10 保存退出
开机+ESC是进入主菜单,可以从这里选择,进入引导
HP电脑在桌面使用快捷键…
Mysql之基本操作(库,表,用户管理)
库中有表,表中有数据
一、查看帮助信息点击查看代码
mysql> help create
//help 后面跟上具体命令可以查看帮助二、查看支持的字符集点击查看代码
show charset;
//查看支持的字符集 默认拉丁文字 latin1utf8 | UTF-8 Unicode //阉割版的
utf8mb4 | UTF-8 Unicode …
海康SDK报错Structure.getFieldOrder()
就是你调用的这个结构体以及其引用的其他结构体,可能没有getFieldOrder()的方法,你只要按照顺序把他填上去就好了。比如
public static class NET_DVR_TIME extends Structure {//校时结构参数public int dwYear; //年public int dwMonth; //月public int dwDa…