文章目录
- 计算机系统
- 5G云计算
- 第三章 LINUX Kubernetes 对外服务之 Ingress
- 一、Ingress 简介
- 1.NodePort
- 2.LoadBalancer
- 3.externalIPs
- 4.Ingress
- 二.Ingress 组成
- 1.ingress
- 2.ingress-controller
- 3.总结
- 三、Ingress-Nginx 工作原理
- 四、ingress 暴露服务的方式
- 1.DaemonSet+HostNetwork+nodeSelector
- 2.Deployment+NodePort模式的Service
- 3.Deployment+LoadBalancer 模式的 Service
- 五、部署 nginx-ingress-controller
- 1.方式一:DaemonSet+HostNetwork+nodeSelector
- 2.方式二:Deployment+NodePort模式的Service
- 六、Ingress HTTP 代理访问 (基于URL路径转发)
- 七、Ingress HTTP 代理访问虚拟主机 (基于域名代理转发)
- 八、Ingress HTTPS 代理访问 (基于https代理转发)
计算机系统
5G云计算
第三章 LINUX Kubernetes 对外服务之 Ingress
一、Ingress 简介
service的作用体现在两个方面,对集群内部,它不断跟踪pod的变化,更新endpoint中对应pod的对象,提供了ip不断变化的pod的服务发现机制;对集群外部,他类似负载均衡器,可以在集群内外部对pod进行访问
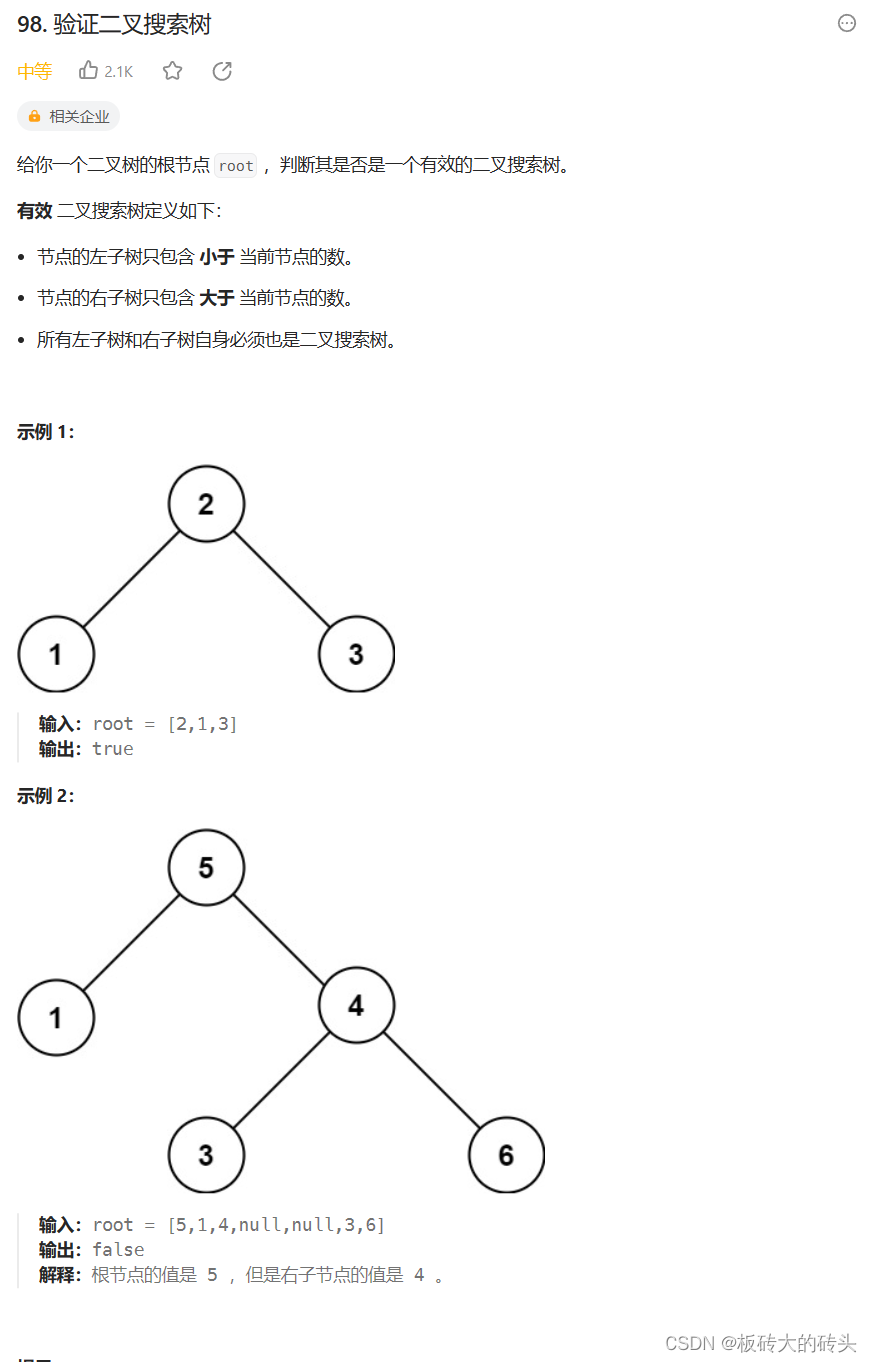
在Kubernetes中,Pod的IP地址和service的ClusterIP仅可以在集群网络内部使用,对于集群外的应用是不可见的。为了使外部的应用能够访问集群内的服务,Kubernetes目前提供了以下几种方案
1.NodePort
将service暴露在节点网络上,NodePort背后就是Kube-Proxy,Kube-Proxy是沟通service网络、Pod网络和节点网络的桥梁
测试环境使用还行,当有几十上百的服务在集群中运行时,NodePort的端口管理就是个灾难。因为每个端口只能是一种服务,默认端口范围只能是 30000-32767
2.LoadBalancer
通过设置LoadBalancer映射到云服务商提供的LoadBalancer地址。这种用法仅用于在公有云服务提供商的云平台上设置 Service 的场景。 受限于云平台,且通常在云平台部署LoadBalancer还需要额外的费用
在service提交后,Kubernetes就会调用CloudProvider在公有云上为你创建一个负载均衡服务,并且把被代理的Pod的IP地址配置给负载均衡服务做后端
3.externalIPs
service允许为其分配外部IP,如果外部IP路由到集群中一个或多个Node上,Service会被暴露给这些externalIPs。通过外部IP进入到集群的流量,将会被路由到Service的Endpoint上
4.Ingress
只需一个或者少量的公网IP和LB,即可同时将多个HTTP服务暴露到外网,七层反向代理。
可以简单理解为service的service,它其实就是一组基于域名和URL路径,把用户的请求转发到一个或多个service的规则
二.Ingress 组成
1.ingress
ingress是一个API对象,通过yaml文件来配置,ingress对象的作用是定义请求如何转发到service的规则,可以理解为配置模板
ingress通过http或https暴露集群内部service,给service提供外部URL、负载均衡、SSL/TLS能力以及基于域名的反向代理。ingress要依靠 ingress-controller 来具体实现以上功能
2.ingress-controller
ingress-controller是具体实现反向代理及负载均衡的程序,对ingress定义的规则进行解析,根据配置的规则来实现请求转发。
ingress-controller并不是k8s自带的组件,实际上ingress-controller只是一个统称,用户可以选择不同的ingress-controller实现,目前,由k8s维护的ingress-controller只有google云的GCE与ingress-nginx两个,其他还有很多第三方维护的ingress-controller,具体可以参考官方文档。但是不管哪一种ingress-controller,实现的机制都大同小异,只是在具体配置上有差异。
一般来说,ingress-controller的形式都是一个pod,里面跑着daemon程序和反向代理程序。daemon负责不断监控集群的变化,根据 ingress对象生成配置并应用新配置到反向代理,比如ingress-nginx就是动态生成nginx配置,动态更新upstream,并在需要的时候reload程序应用新配置。为了方便,后面的例子都以k8s官方维护的ingress-nginx为例
Ingress-Nginx github 地址:https://github.com/kubernetes/ingress-nginx
Ingress-Nginx 官方网站:https://kubernetes.github.io/ingress-nginx/
3.总结
ingress-controller才是负责具体转发的组件,通过各种方式将它暴露在集群入口,外部对集群的请求流量会先到 ingress-controller, 而ingress对象是用来告诉ingress-controller该如何转发请求,比如哪些域名、哪些URL要转发到哪些service等等
三、Ingress-Nginx 工作原理
(1)ingress-controller通过和 kubernetes APIServer 交互,动态的去感知集群中ingress规则变化,
(2)然后读取它,按照自定义的规则,规则就是写明了哪个域名对应哪个service,生成一段nginx配置,
(3)再写到nginx-ingress-controller的pod里,这个ingress-controller的pod里运行着一个Nginx服务,控制器会把生成的 nginx配置写入 /etc/nginx.conf文件中,
(4)然后reload一下使配置生效。以此达到域名区分配置和动态更新的作用。
四、ingress 暴露服务的方式
1.DaemonSet+HostNetwork+nodeSelector
用DaemonSet结合nodeselector来部署ingress-controller到特定的node上,然后使用HostNetwork直接把该pod与宿主机node的网络打通,直接使用宿主机的80/433端口就能访问服务。这时,ingress-controller所在的node机器就很类似传统架构的边缘节点,比如机房入口的nginx服务器。该方式整个请求链路最简单,性能相对NodePort模式更好。缺点是由于直接利用宿主机节点的网络和端口,一个node只能部署一个ingress-controller pod。 比较适合大并发的生产环境使用
2.Deployment+NodePort模式的Service
同样用deployment模式部署ingress-controller,并创建对应的service,但是type为NodePort。这样,ingress就会暴露在集群节点ip的特定端口上。由于nodeport暴露的端口是随机端口,一般会在前面再搭建一套负载均衡器来转发请求。该方式一般用于宿主机是相对固定的环境ip地址不变的场景
NodePort方式暴露ingress虽然简单方便,但是NodePort多了一层NAT,在请求量级很大时可能对性能会有一定影响
3.Deployment+LoadBalancer 模式的 Service
如果要把ingress部署在公有云,那用这种方式比较合适。用Deployment部署ingress-controller,创建一个 type为 LoadBalancer 的 service 关联这组 pod。 大部分公有云,都会为 LoadBalancer 的 service 自动创建一个负载均衡器,通常还绑定了公网地址。只要把域名解析指向该地址,就实现了集群服务的对外暴露
五、部署 nginx-ingress-controller
1.方式一:DaemonSet+HostNetwork+nodeSelector
1、部署ingress-controller Pod及相关资源
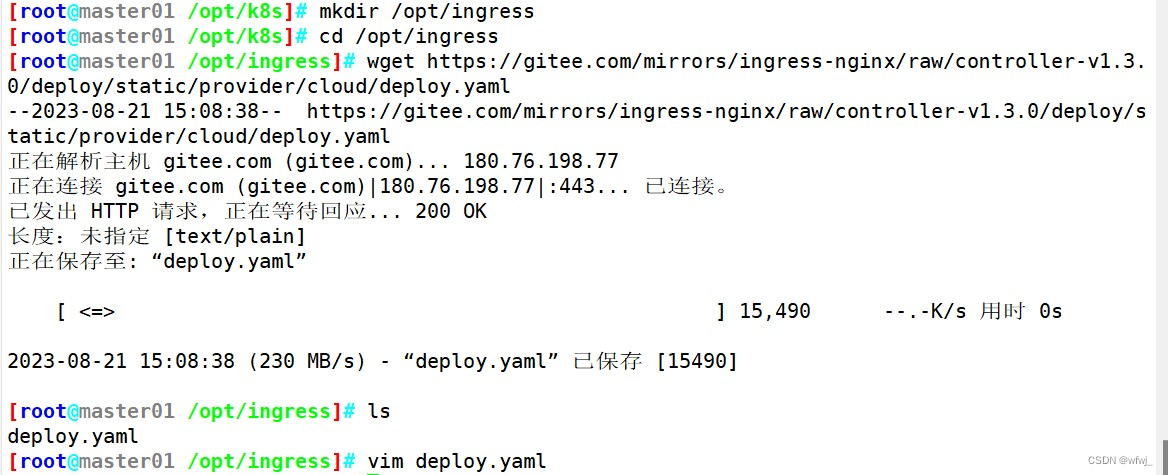
mkdir /opt/ingress
cd /opt/ingress官方下载地址:
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.3.0/deploy/static/provider/cloud/deploy.yaml上面可能无法下载,可用国内的 gitee
wget https://gitee.com/mirrors/ingress-nginx/raw/controller-v1.3.0/deploy/static/provider/cloud/deploy.yaml修改镜像地址为:
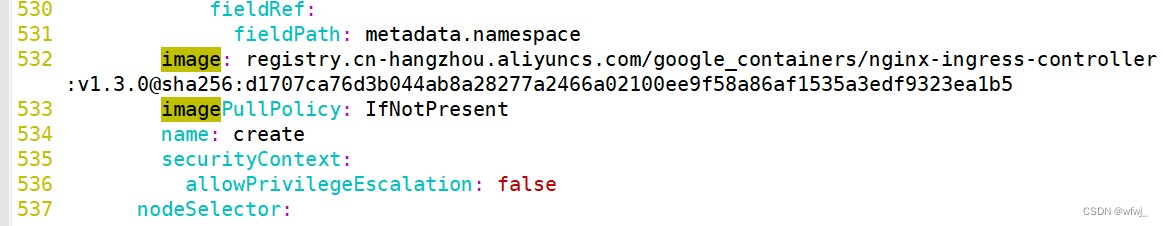
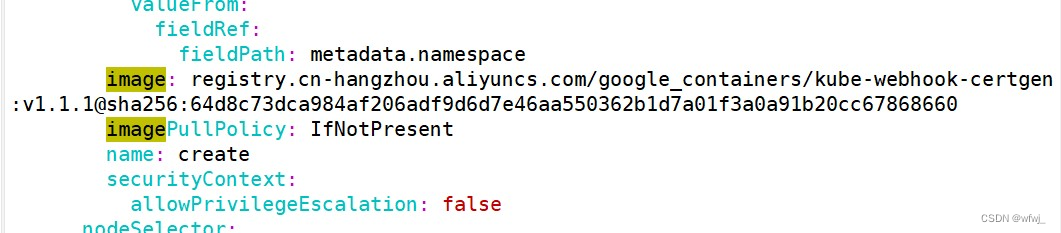
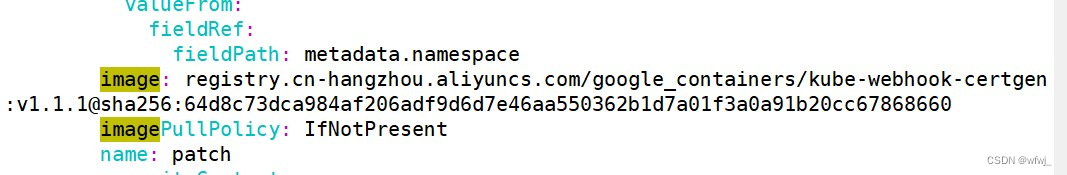
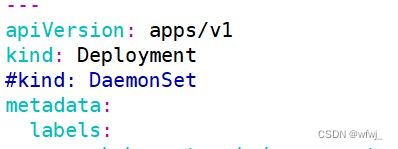
image: registry.cn-hangzhou.aliyuncs.com/google_containers/nginx-ingress-controller:v1.3.0@sha256:d1707ca76d3b044ab8a28277a2466a02100ee9f58a86af1535a3edf9323ea1b5image: registry.cn-hangzhou.aliyuncs.com/google_containers/kube-webhook-certgen:v1.1.1@sha256:64d8c73dca984af206adf9d6d7e46aa550362b1d7a01f3a0a91b20cc678686602、指定 nginx-ingress-controller 运行在 node02 节点
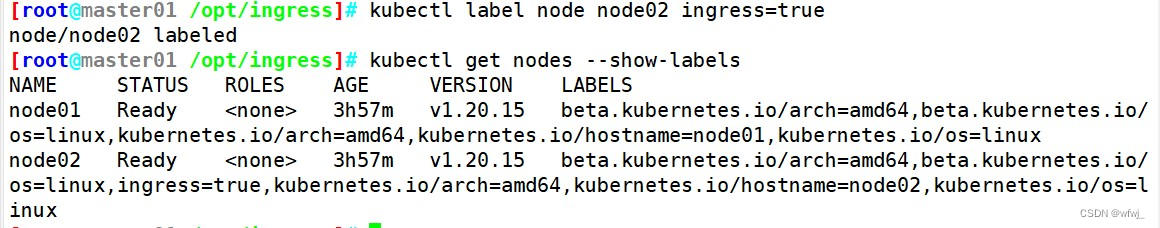
kubectl label node node02 ingress=truekubectl get nodes --show-labels3、修改 Deployment 为 DaemonSet ,指定节点运行,并开启 hostNetwork 网络
vim deploy.yaml
...
apiVersion: apps/v1
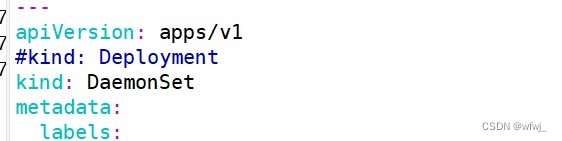
# 修改 kind
#kind: Deployment
kind: DaemonSet
......
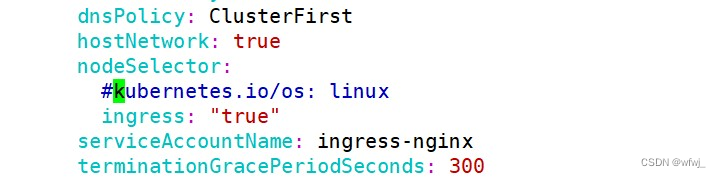
spec:......template:......spec:# 使用宿主机网络hostNetwork: true# 修改选择节点选择器nodeSelector:ingress: "true"
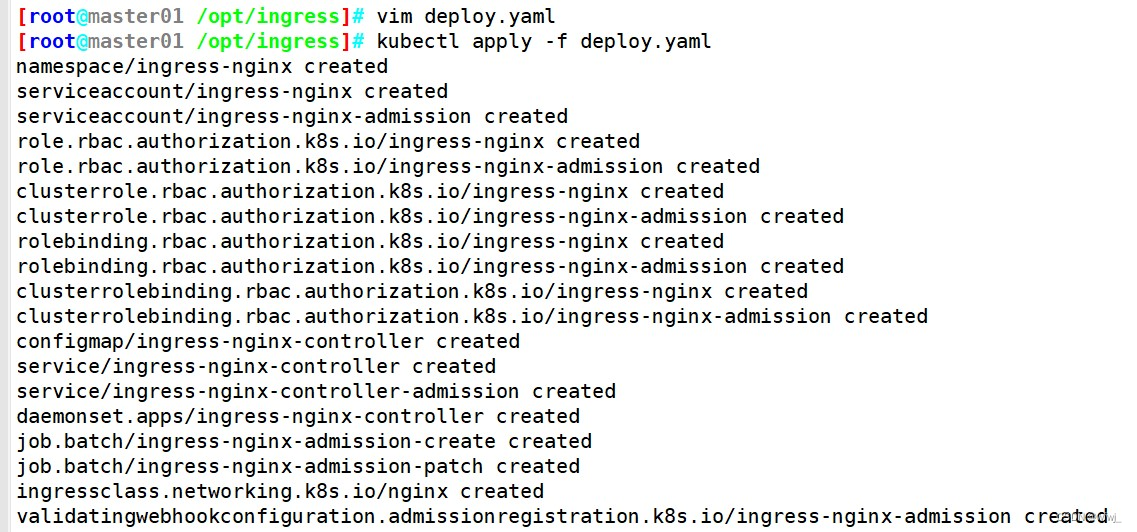
......5、启动 nginx-ingress-controller
kubectl apply -f deploy.yaml//nginx-ingress-controller 已经运行 node02 节点
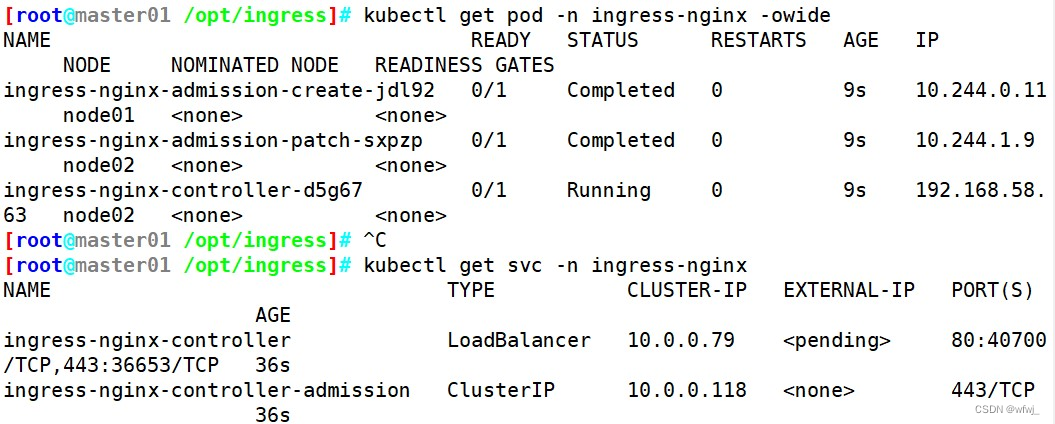
kubectl get pod -n ingress-nginx -owide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES
ingress-nginx-admission-create-jdl92 0/1 Completed 0 9s 10.244.0.11 node01 <none> <none>
ingress-nginx-admission-patch-sxpzp 0/1 Completed 0 9s 10.244.1.9 node02 <none> <none>
ingress-nginx-controller-d5g67 0/1 Running 0 9s 192.168.58.63 node02 <none> <none>kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller LoadBalancer 10.0.0.79 <pending> 80:40700/TCP,443:36653/TCP 36s
ingress-nginx-controller-admission ClusterIP 10.0.0.118 <none> 443/TCP 36s//到 node02 节点查看
netstat -lntp | grep nginx
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 47555/nginx: master
tcp 0 0 0.0.0.0:8181 0.0.0.0:* LISTEN 47555/nginx: master
tcp 0 0 0.0.0.0:443 0.0.0.0:* LISTEN 47555/nginx: master
......由于配置了 hostnetwork,nginx 已经在 node 主机本地监听 80/443/8181 端口。其中 8181 是 nginx-controller 默认配置的一个 default backend(Ingress 资源没有匹配的 rule 对象时,流量就会被导向这个 default backend)。
这样,只要访问 node 主机有公网 IP,就可以直接映射域名来对外网暴露服务了。如果要 nginx 高可用的话,可以在多个 node 上部署,并在前面再搭建一套 LVS+keepalived 做负载均衡。6、创建 ingress 规则
//创建一个 deploy 和 svc
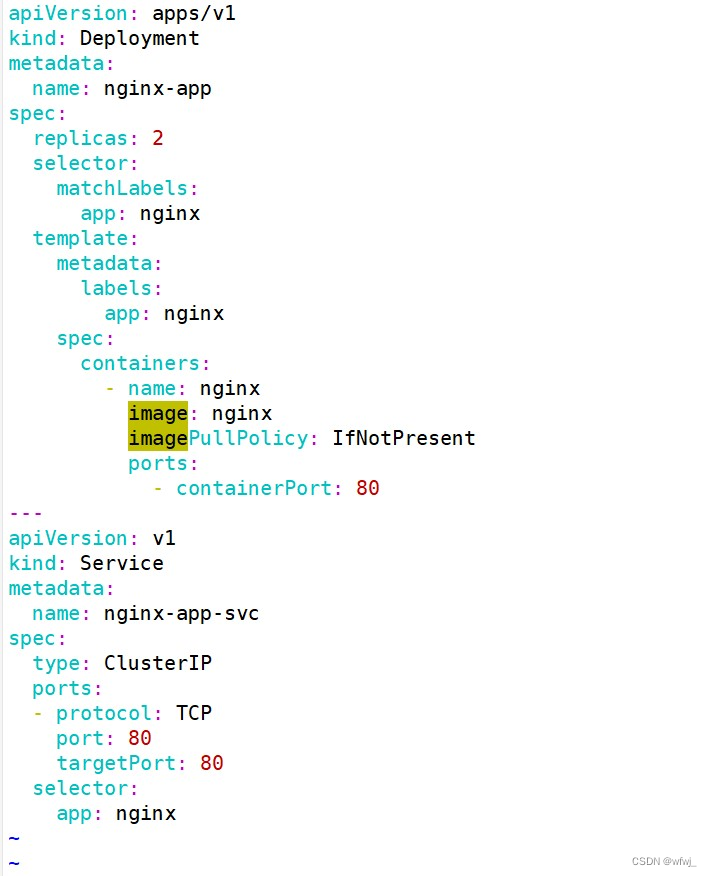
vim service-nginx.yaml
apiVersion: apps/v1
kind: Deployment
metadata:name: nginx-app
spec:replicas: 2selector:matchLabels:app: nginxtemplate:metadata:labels:app: nginxspec:containers:- name: nginximage: nginximagePullPolicy: IfNotPresentports:- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:name: nginx-app-svc
spec:type: ClusterIPports:- protocol: TCPport: 80targetPort: 80selector:app: nginx//创建 ingress
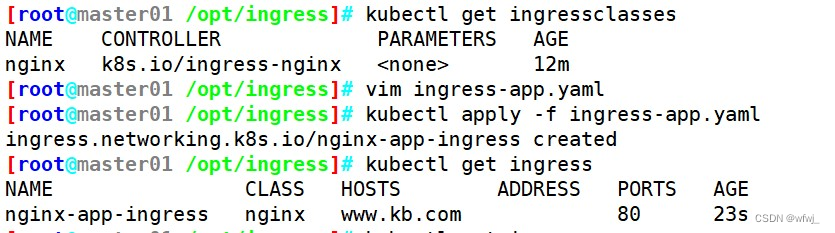
kubectl get ingressclasses
NAME CONTROLLER PARAMETERS AGE
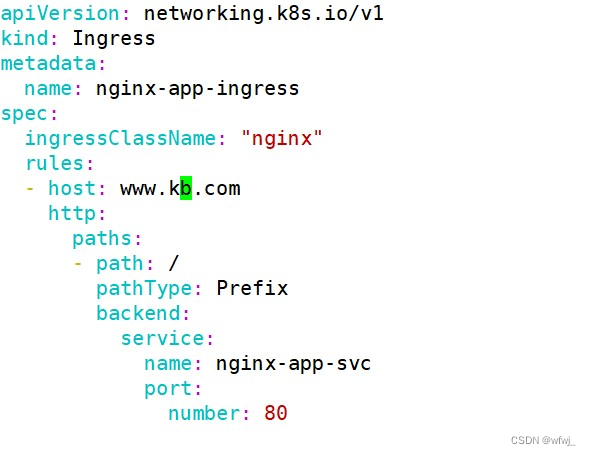
nginx k8s.io/ingress-nginx <none> 12mvim ingress-app.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-app-ingress
spec:ingressClassName: "nginx"rules:- host: www.kb.comhttp:paths:- path: /pathType: Prefixbackend:service:name: nginx-app-svcport:number: 80-------------------------------------------------------------------------------------------
ingressClassName 指定 IngressClass,用来指定选择的 Ingress Controllerhost 主机名可以是精确匹配,或者使用通配符来匹配,但通配符仅覆盖一个 DNS 标签(例如 *.foo.com 不匹配 baz.bar.foo.com)。pathType 支持的路径类型有三种:
●Exact:精确匹配 URL 路径,且区分大小写。●Prefix:基于以 / 分隔的 URL 路径前缀匹配。匹配区分大小写。如果路径的最后一个元素是请求路径中最后一个元素的子字符串,则不会匹配 (例如:/foo/bar 匹配 /foo/bar/baz, 但不匹配 /foo/barbaz)。●ImplementationSpecific:对于这种路径类型,匹配方法取决于 IngressClass。具体实现可以将其作为单独的 pathType 处理或者与 Prefix 或 Exact 类型作相同处理。
具体可详见:https://kubernetes.io/zh-cn/docs/concepts/services-networking/ingress/#the-ingress-resource
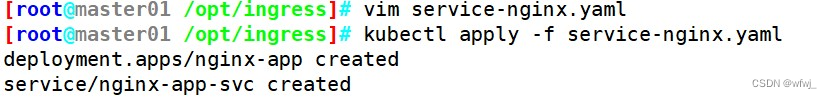
-------------------------------------------------------------------------------------------kubectl apply -f service-nginx.yaml
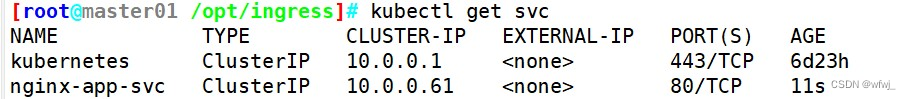
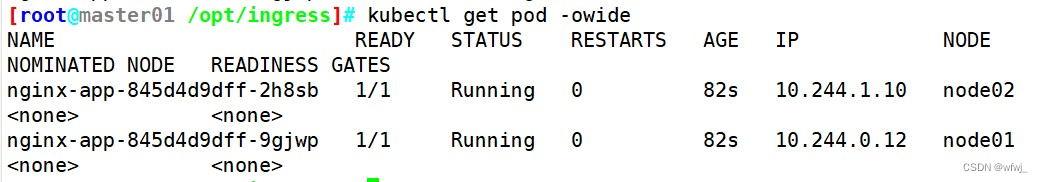
kubectl apply -f ingress-app.yamlkubectl get pods
NAME READY STATUS RESTARTS AGE
nginx-app-845d4d9dff-2h8sb 1/1 Running 0 46s
nginx-app-845d4d9dff-9gjwp 1/1 Running 0 46skubectl get ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
nginx-app-ingress nginx www.kb.com 80 2m53s7、测试访问
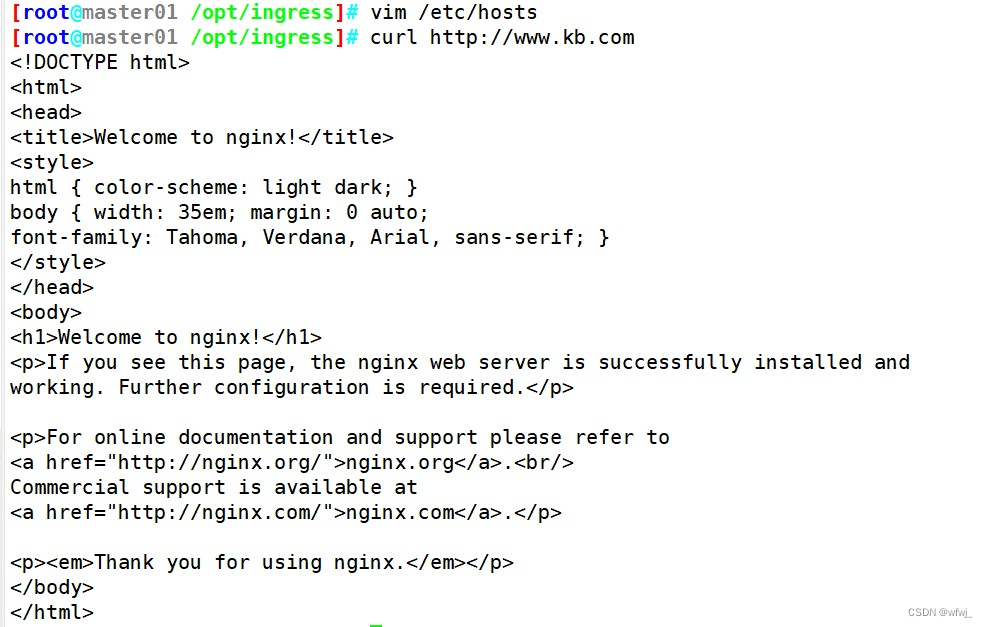
//本地 host 添加域名解析
vim /etc/hosts
192.168.80.10 master
192.168.80.11 node01
192.168.80.12 node02
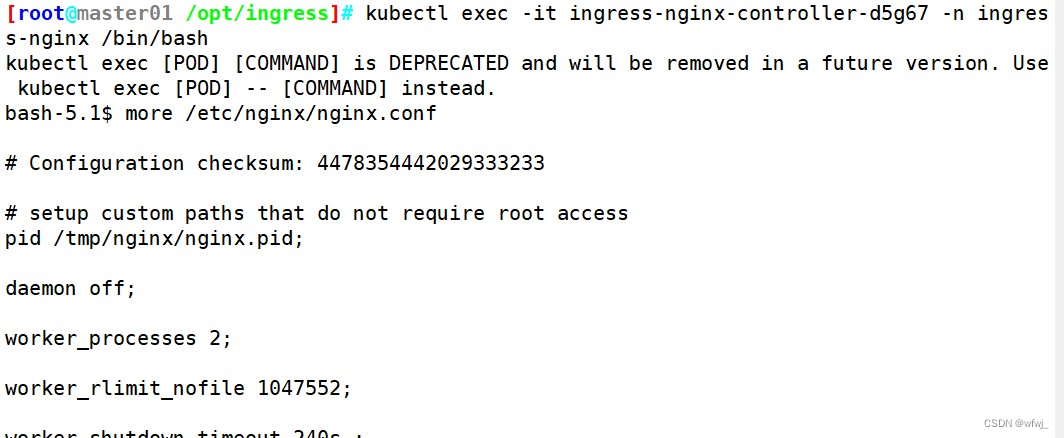
192.168.80.12 www.kb.comcurl http://www.kb.com8、查看 nginx-ingress-controller
kubectl get pod -n ingress-nginx -o wide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES
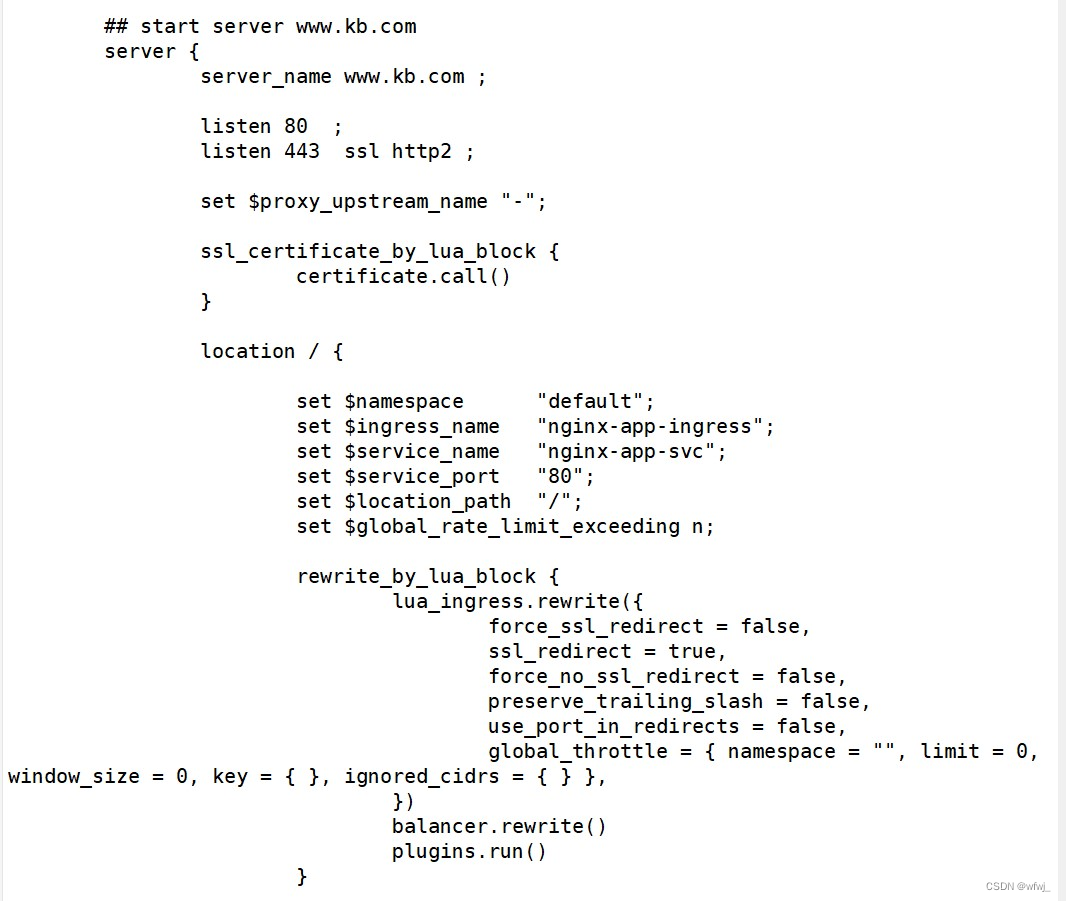
ingress-nginx-controller-d5g67 1/1 Running 0 16m 192.168.58.63 node02 <none> <none>kubectl exec -it ingress-nginx-controller-d5g67 -n ingress-nginx /bin/bash# more /etc/nginx/nginx.conf
//可以看到从 start server www.kb.com 到 end server www.kb.com 之间包含了此域名用于反向代理的配置
2.方式二:Deployment+NodePort模式的Service
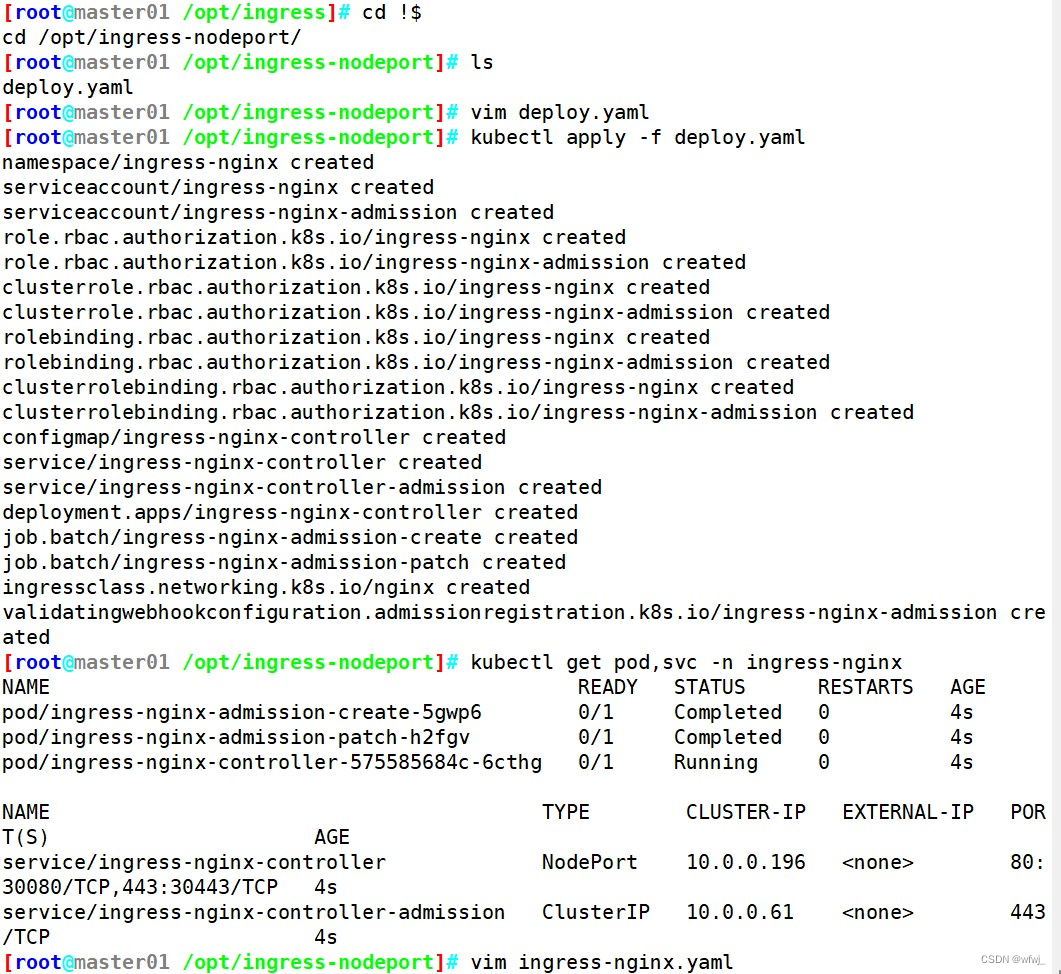
1、下载 nginx-ingress-controller 配置文件
mkdir /opt/ingress-nodeport
cd /opt/ingress-nodeport官方下载地址:
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.3.0/deploy/static/provider/cloud/deploy.yaml上面可能无法下载,可用国内的 gitee
wget https://gitee.com/mirrors/ingress-nginx/raw/controller-v1.3.0/deploy/static/provider/cloud/deploy.yaml修改镜像地址为:
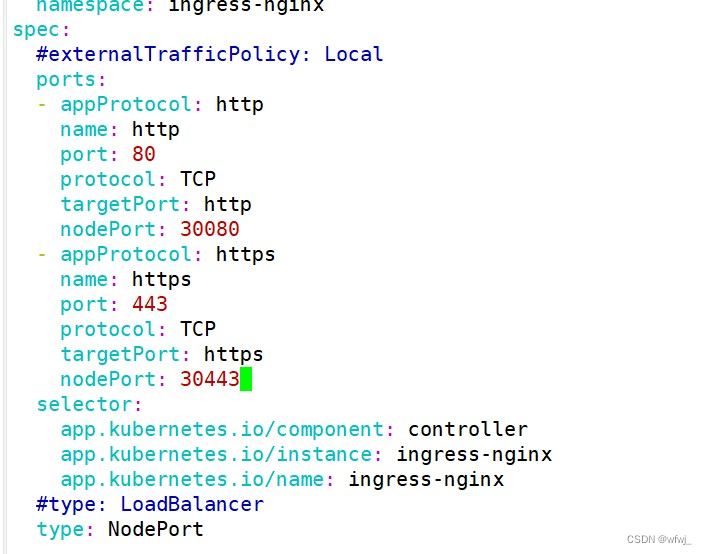
image: registry.cn-hangzhou.aliyuncs.com/google_containers/nginx-ingress-controller:v1.3.0@sha256:d1707ca76d3b044ab8a28277a2466a02100ee9f58a86af1535a3edf9323ea1b5image: registry.cn-hangzhou.aliyuncs.com/google_containers/kube-webhook-certgen:v1.1.1@sha256:64d8c73dca984af206adf9d6d7e46aa550362b1d7a01f3a0a91b20cc678686602、修改配置文件
apiVersion: v1
kind: Service
metadata:labels:app.kubernetes.io/component: controllerapp.kubernetes.io/instance: ingress-nginxapp.kubernetes.io/name: ingress-nginxapp.kubernetes.io/part-of: ingress-nginxapp.kubernetes.io/version: 1.3.0name: ingress-nginx-controllernamespace: ingress-nginx
spec:#externalTrafficPolicy: Local #注释此行,值为Cluster表示流量可以转发到其他节点上的Pod;Local表示:流量只发给本机的Podports:nodePort: 30080......nodePort: 30443type: NodePort #Service类型设置为 NodePort 或 LoadBalancer3、启动 nginx-ingress-controller
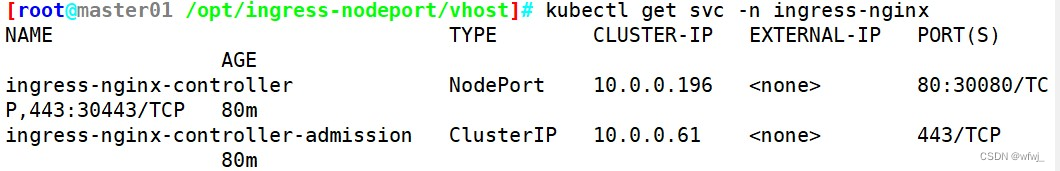
kubectl apply -f deploy.yamlkubectl get pod,svc -n ingress-nginx
NAME READY STATUS RESTARTS AGE
pod/ingress-nginx-admission-create-5gwp6 0/1 Completed 0 4s
pod/ingress-nginx-admission-patch-h2fgv 0/1 Completed 0 4s
pod/ingress-nginx-controller-575585684c-6cthg 0/1 Running 0 4sNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/ingress-nginx-controller NodePort 10.0.0.196 <none> 80:30080/TCP,443:30443/TCP 4s
service/ingress-nginx-controller-admission ClusterIP 10.0.0.61 <none> 443/TCP 4s
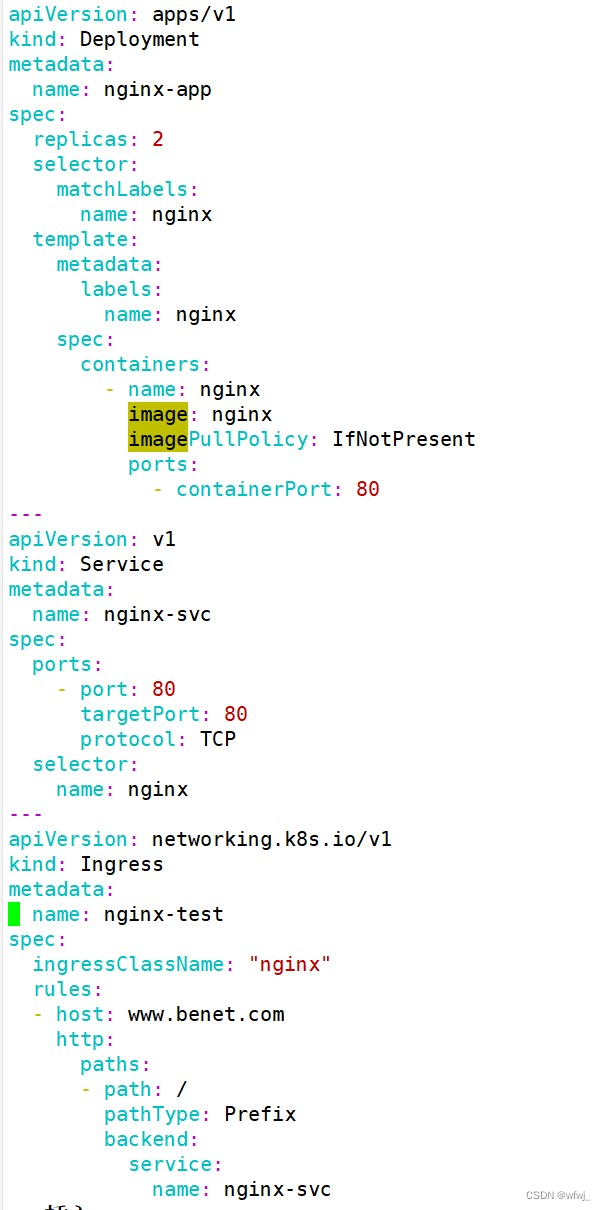
六、Ingress HTTP 代理访问 (基于URL路径转发)
cd /opt/ingress-nodeport#创建 deployment、Service、Ingress Yaml 资源
vim ingress-nginx.yaml
apiVersion: apps/v1
kind: Deployment
metadata:name: nginx-app
spec:replicas: 2selector:matchLabels:name: nginxtemplate:metadata:labels:name: nginxspec:containers:- name: nginximage: nginximagePullPolicy: IfNotPresentports:- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:name: nginx-svc
spec:ports:- port: 80targetPort: 80protocol: TCPselector:name: nginx
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-test
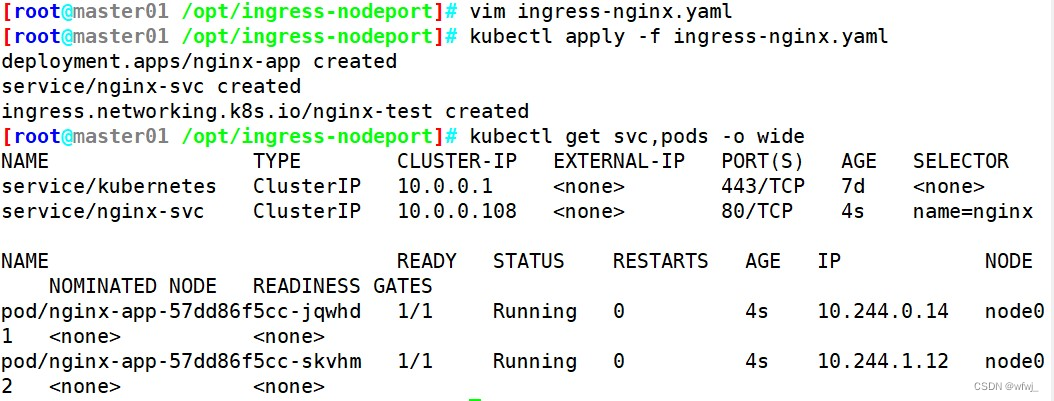
spec:ingressClassName: "nginx"rules:- host: www.benet.comhttp:paths:- path: /pathType: Prefixbackend:service: name: nginx-svcport:number: 80kubectl apply -f ingress-nginx.yamlkubectl get svc,pods -o wide
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTOR
service/kubernetes ClusterIP 10.0.0.1 <none> 443/TCP 7d <none>
service/nginx-svc ClusterIP 10.0.0.108 <none> 80/TCP 4s name=nginxNAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES
pod/nginx-app-57dd86f5cc-jqwhd 1/1 Running 0 4s 10.244.0.14 node01 <none> <none>
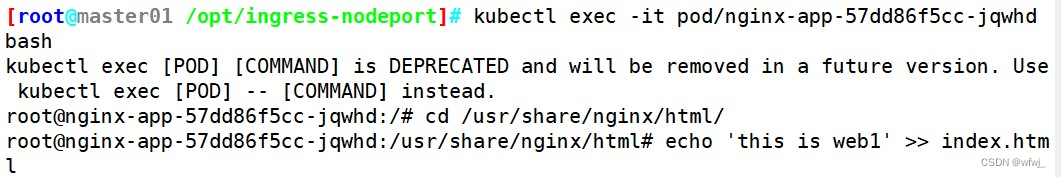
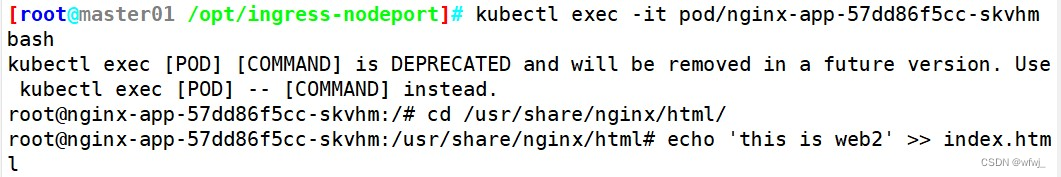
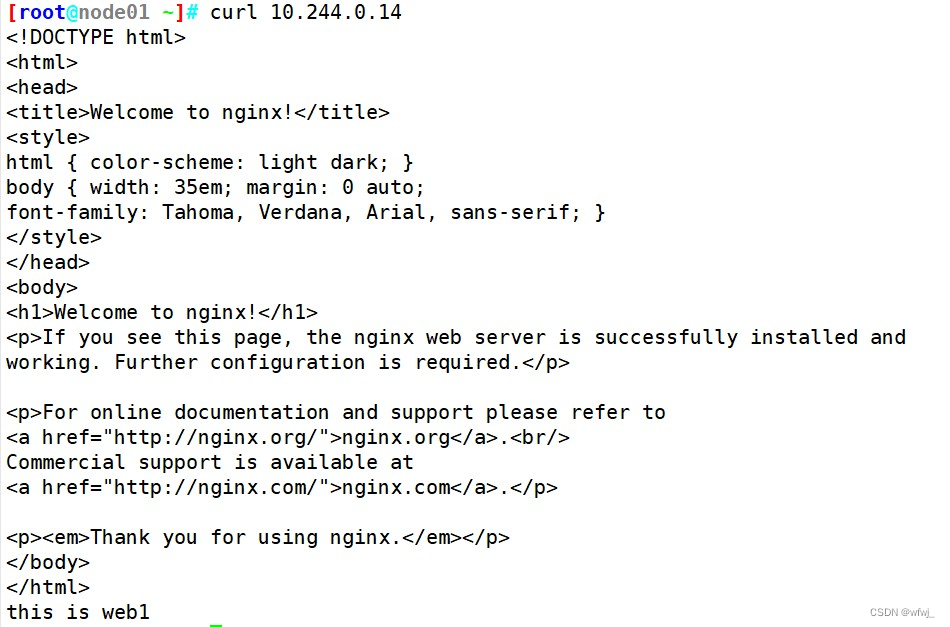
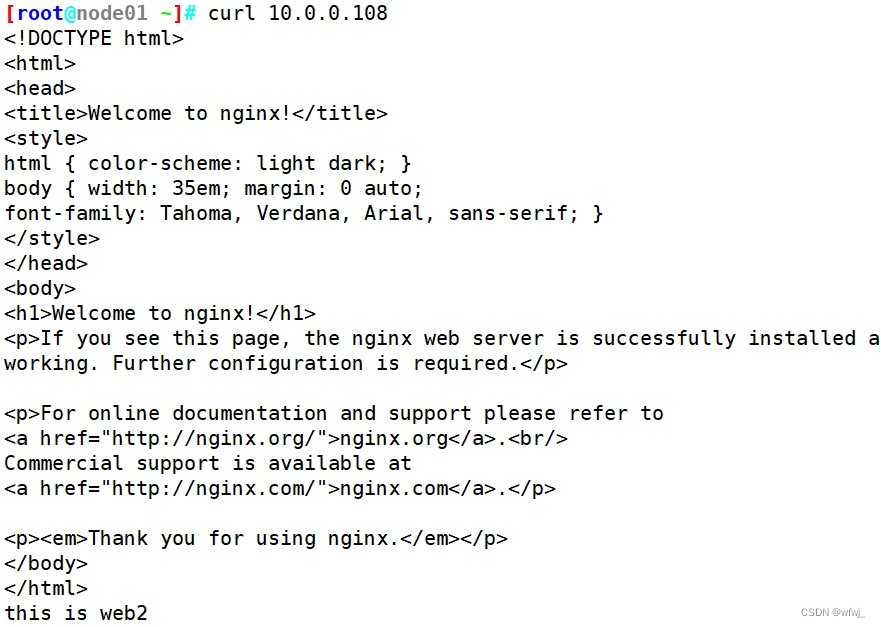
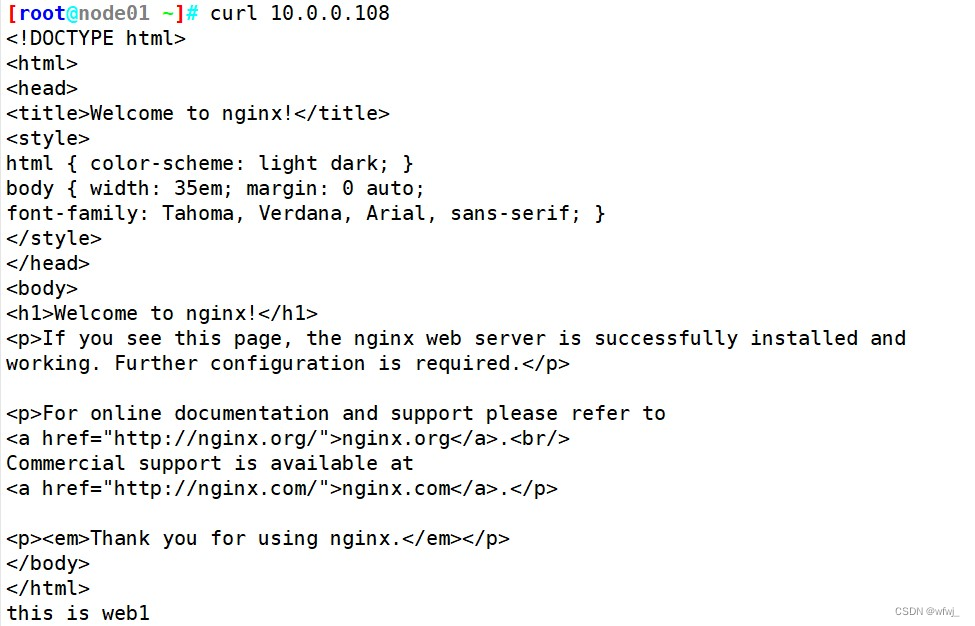
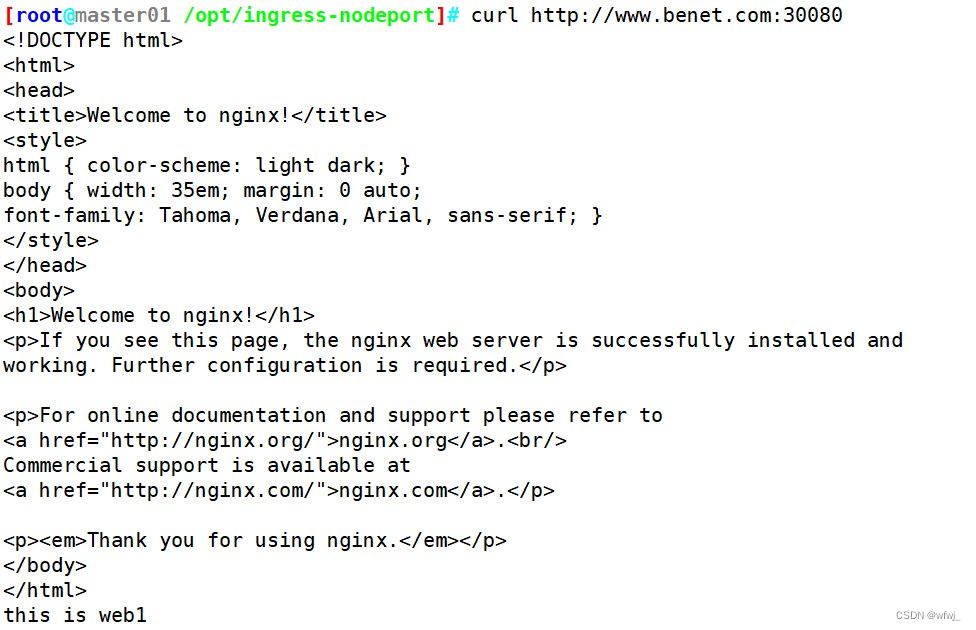
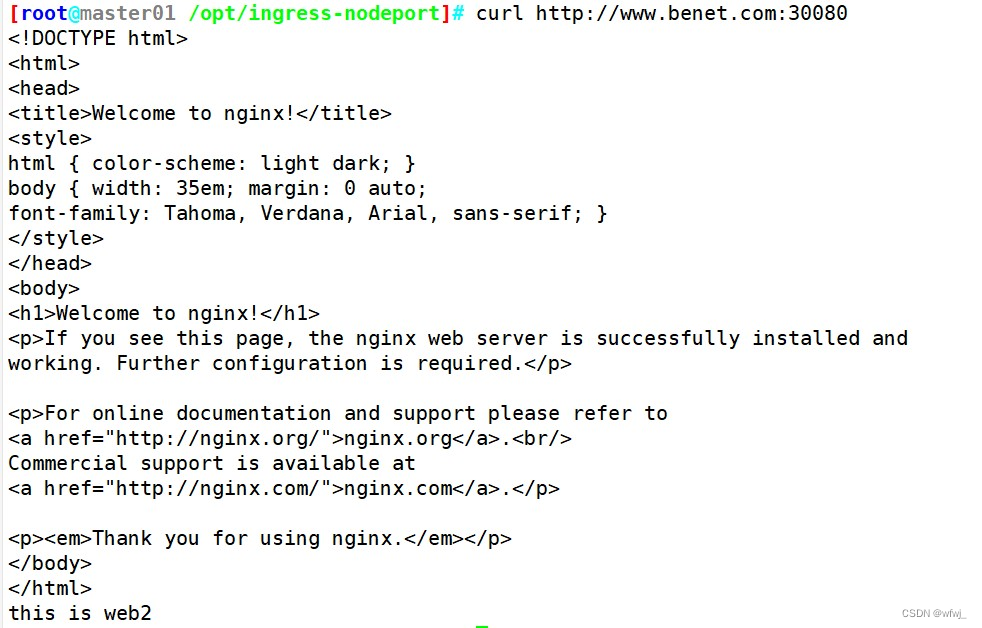
pod/nginx-app-57dd86f5cc-skvhm 1/1 Running 0 4s 10.244.1.12 node02 <none> <none>kubectl exec -it pod/nginx-app-57dd86f5cc-jqwhd bash# cd /usr/share/nginx/html/# echo 'this is web1' >> index.html kubectl exec -it pod/nginx-app-57dd86f5cc-skvhm bash# cd /usr/share/nginx/html/# echo 'this is web2' >> index.html#测试访问
curl 10.0.0.108kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.0.0.196 <none> 80:30080/TCP,443:30443/TCP 10m
ingress-nginx-controller-admission ClusterIP 10.0.0.61 <none> 443/TCP 10m#本地 host 添加域名解析
vim /etc/hosts
192.168.80.10 master
192.168.80.11 node01
192.168.80.12 node02
192.168.80.12 www.kb.com www.benet.com#外部访问
curl http://www.benet.com:30080
七、Ingress HTTP 代理访问虚拟主机 (基于域名代理转发)
mkdir /opt/ingress-nodeport/vhost
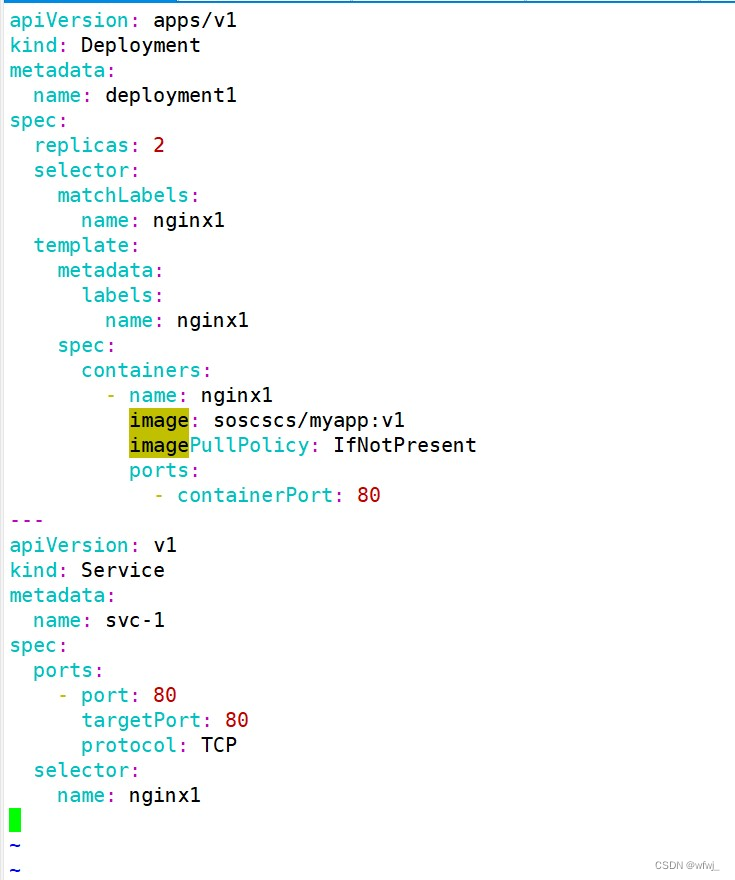
cd /opt/ingress-nodeport/vhost#创建虚拟主机1资源
vim deployment1.yaml
apiVersion: apps/v1
kind: Deployment
metadata:name: deployment1
spec:replicas: 2selector:matchLabels:name: nginx1template:metadata:labels:name: nginx1spec:containers:- name: nginx1image: soscscs/myapp:v1imagePullPolicy: IfNotPresentports:- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:name: svc-1
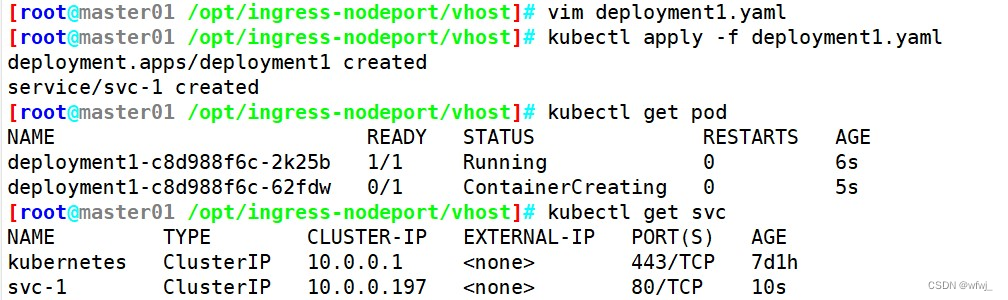
spec:ports:- port: 80targetPort: 80protocol: TCPselector:name: nginx1kubectl apply -f deployment1.yaml#创建虚拟主机2资源
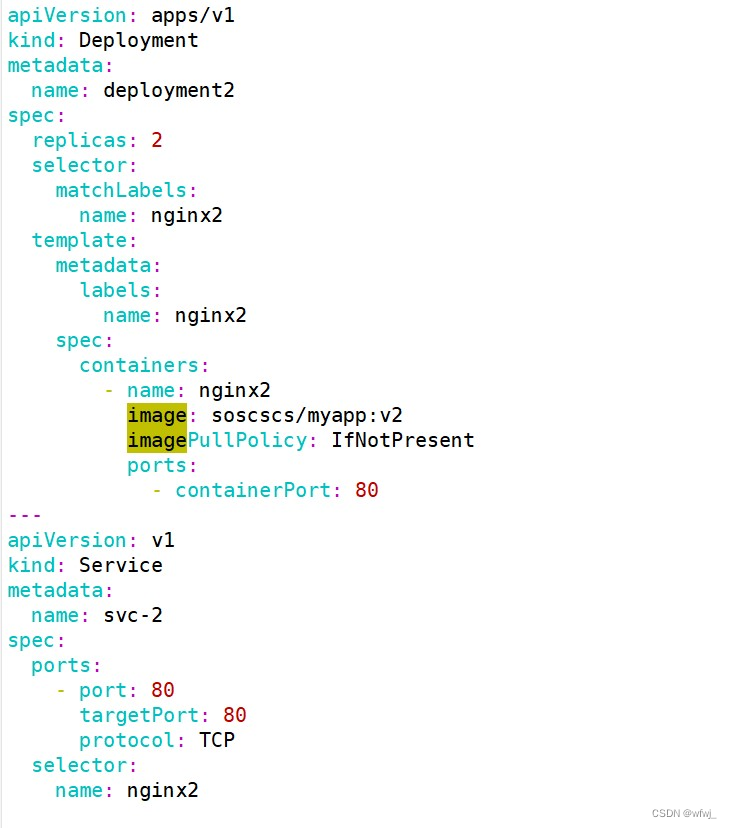
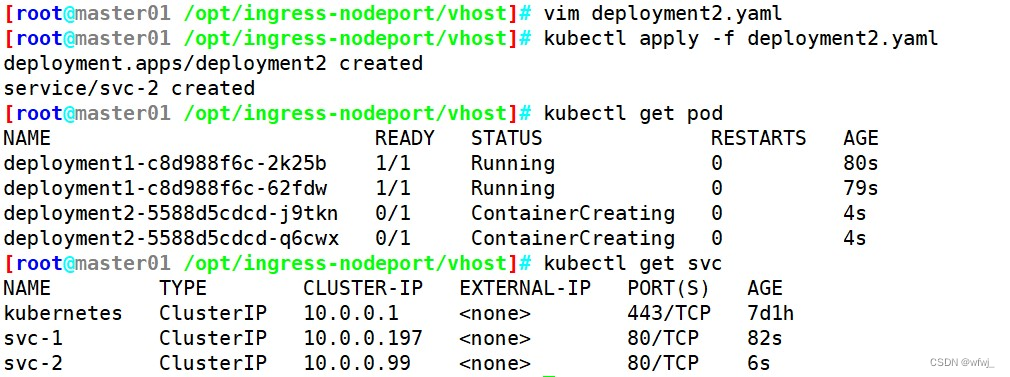
vim deployment2.yaml
apiVersion: apps/v1
kind: Deployment
metadata:name: deployment2
spec:replicas: 2selector:matchLabels:name: nginx2template:metadata:labels:name: nginx2spec:containers:- name: nginx2image: soscscs/myapp:v2imagePullPolicy: IfNotPresentports:- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:name: svc-2
spec:ports:- port: 80targetPort: 80protocol: TCPselector:name: nginx2kubectl apply -f deployment2.yaml#创建ingress资源
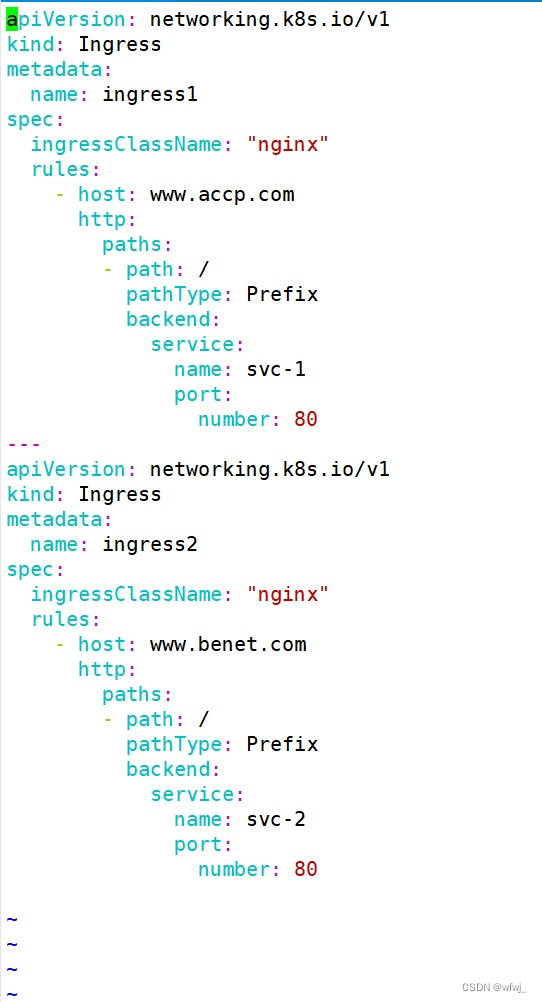
vim ingress-nginx.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress1
spec:ingressClassName: "nginx"rules:- host: www.accp.comhttp:paths:- path: /pathType: Prefixbackend:service: name: svc-1port:number: 80
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress2
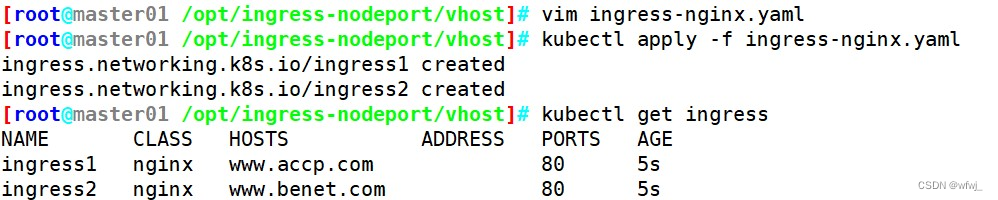
spec:ingressClassName: "nginx"rules:- host: www.benet.comhttp:paths:- path: /pathType: Prefixbackend:service: name: svc-2port:number: 80kubectl apply -f ingress-nginx.yaml#测试访问
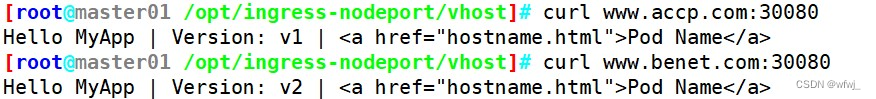
kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.0.0.196 <none> 80:30080/TCP,443:30443/TCP 80m
ingress-nginx-controller-admission ClusterIP 10.0.0.61 <none> 443/TCP 80m#本地 host 添加域名解析
vim /etc/hosts
192.168.80.10 master
192.168.80.11 node01
192.168.80.12 node02
192.168.80.12 www.kb.com www.benet.com www.accp.comcurl www.accp.com:30080
Hello MyApp | Version: v1 | <a href="hostname.html">Pod Name</a>curl www.benet.com:30080
Hello MyApp | Version: v2 | <a href="hostname.html">Pod Name</a>
八、Ingress HTTPS 代理访问 (基于https代理转发)
mkdir /opt/ingress-nodeport/https
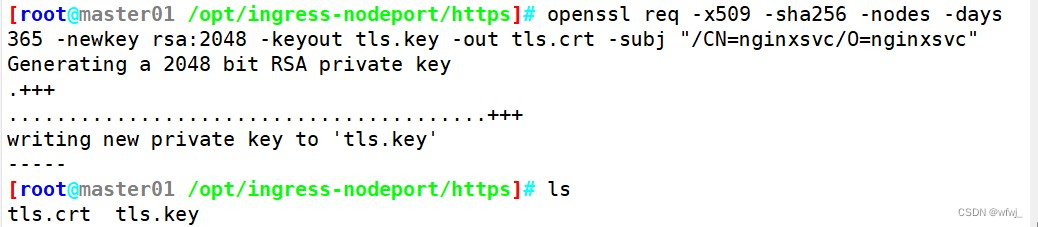
cd /opt/ingress-nodeport/https#创建ssl证书
openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=nginxsvc/O=nginxsvc"#创建 secret 资源进行存储
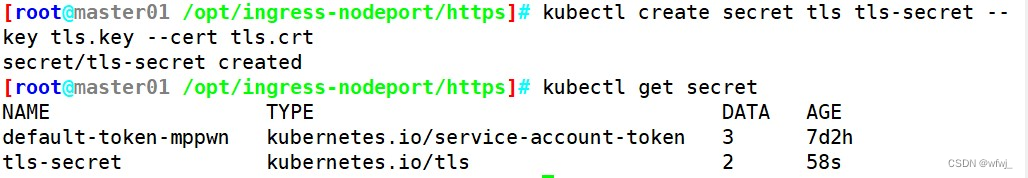
kubectl create secret tls tls-secret --key tls.key --cert tls.crtkubectl get secret
NAME TYPE DATA AGE
tls-secret kubernetes.io/tls 2 58skubectl describe secret tls-secret
Name: tls-secret
Namespace: default
Labels: <none>
Annotations: <none>Type: kubernetes.io/tlsData
====
tls.crt: 1143 bytes
tls.key: 1704 bytes#创建 deployment、Service、Ingress Yaml 资源
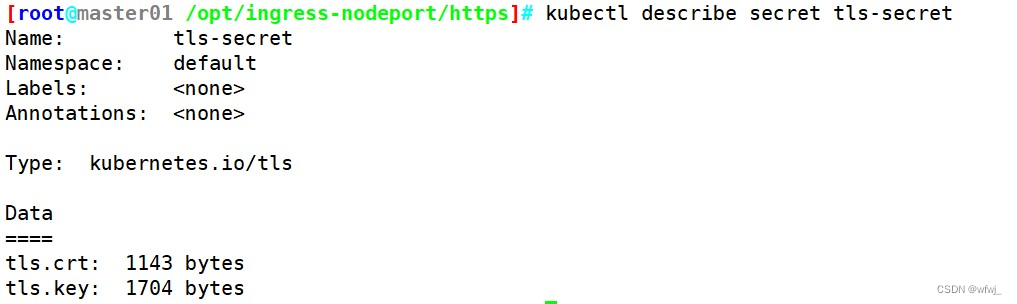
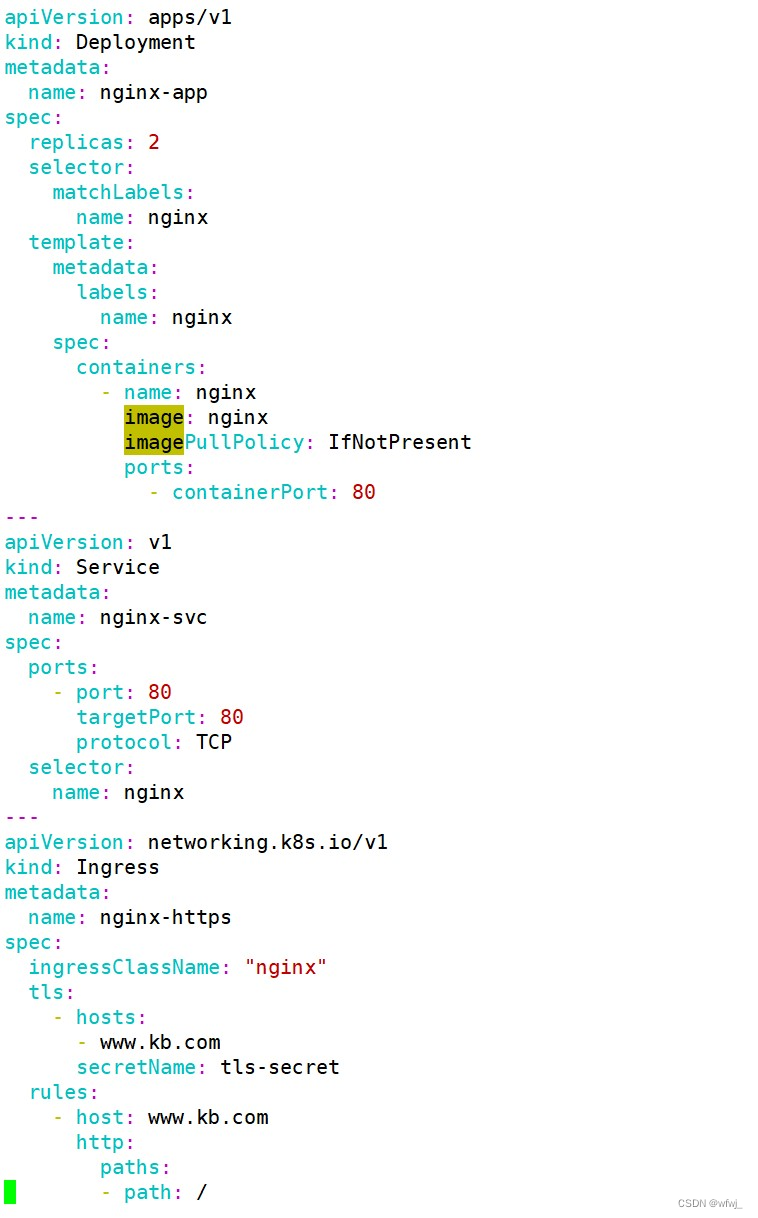
vim ingress-https.yaml
apiVersion: apps/v1
kind: Deployment
metadata:name: nginx-app
spec:replicas: 2selector:matchLabels:name: nginxtemplate:metadata:labels:name: nginxspec:containers:- name: nginximage: nginximagePullPolicy: IfNotPresentports:- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:name: nginx-svc
spec:ports:- port: 80targetPort: 80protocol: TCPselector:name: nginx
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-https
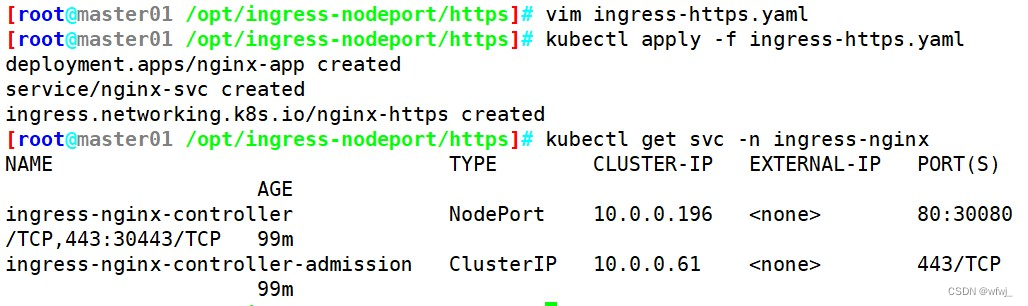
spec:ingressClassName: "nginx"tls:- hosts:- www.kb.comsecretName: tls-secretrules:- host: www.kb.comhttp:paths:- path: /pathType: Prefixbackend:service: name: nginx-svcport:number: 80kubectl apply -f ingress-https.yamlkubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.0.0.196 <none> 80:30080/TCP,443:30443/TCP 99m
ingress-nginx-controller-admission ClusterIP 10.0.0.61 <none> 443/TCP 99m#访问测试
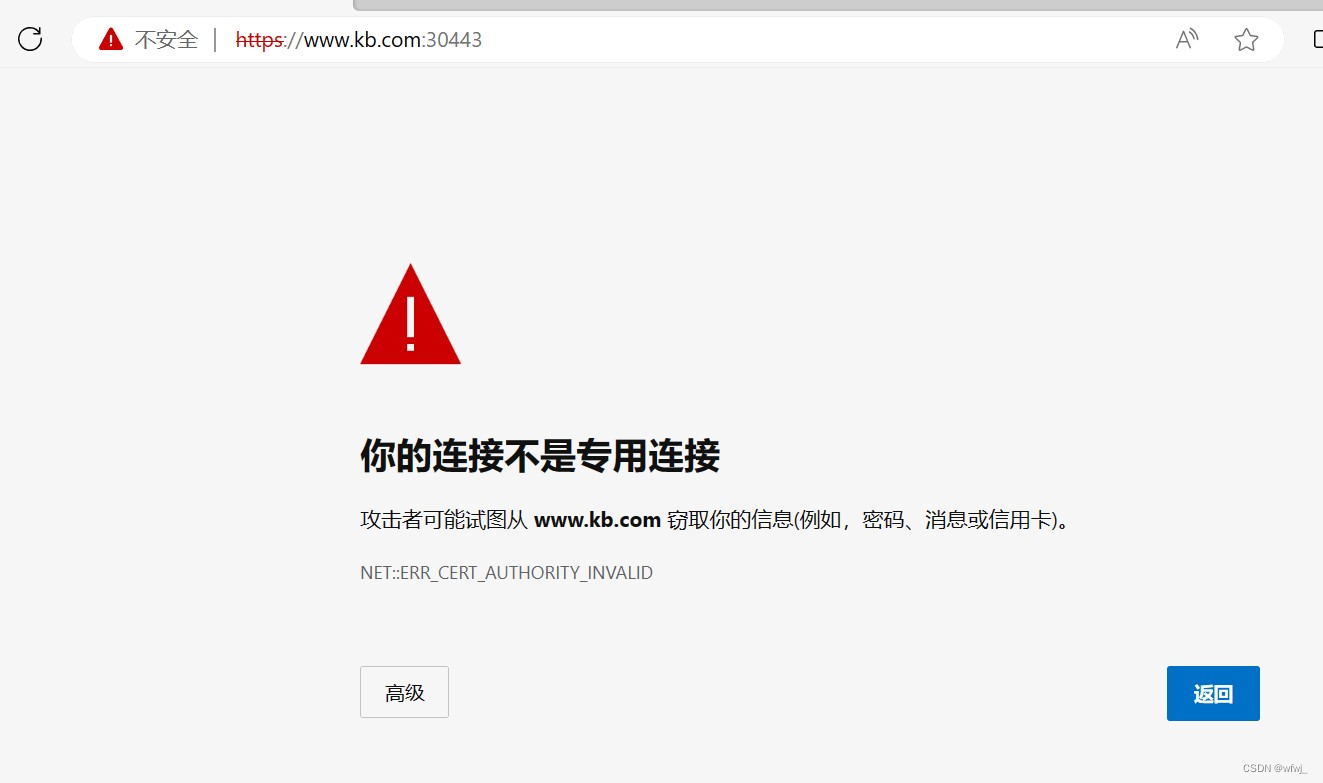
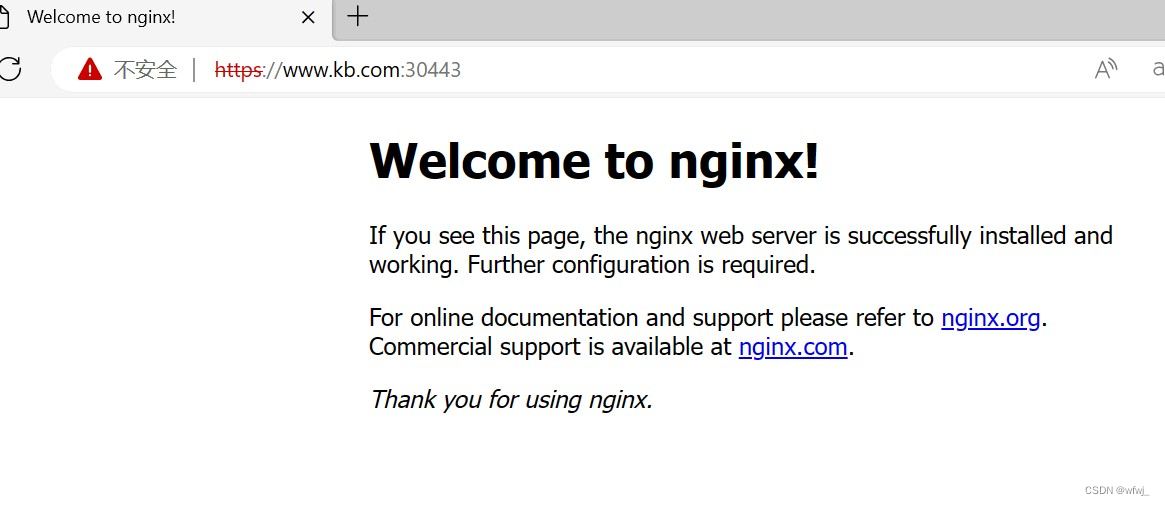
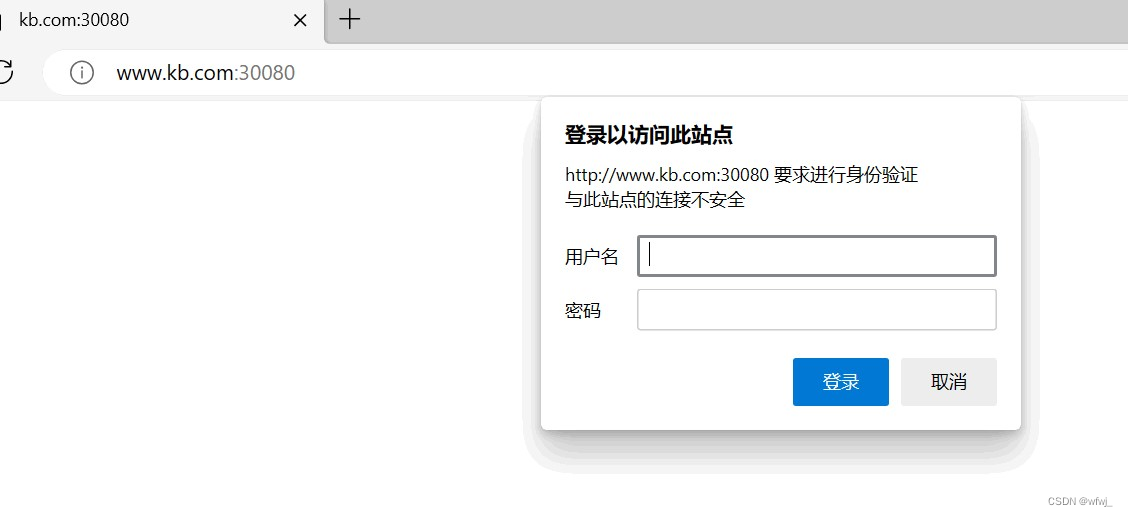
在宿主机的 C:\Windows\System32\drivers\etc\hosts 文件中添加 192.168.58.63 www.kb.com 记录。
使用谷歌浏览器访问 https://www.kb.com:30443//Nginx 进行 BasicAuth
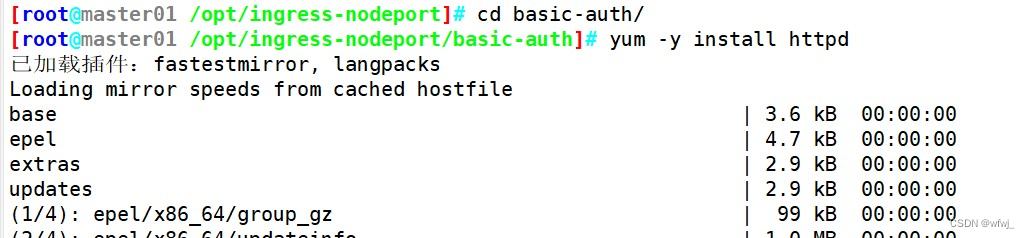
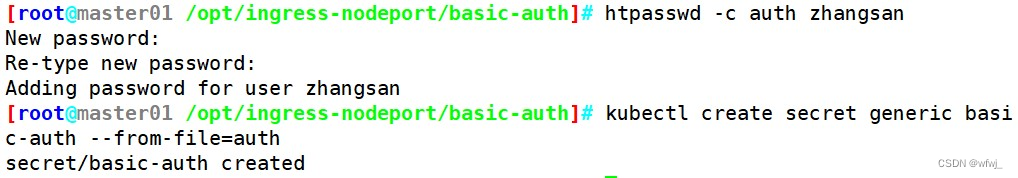
mkdir /opt/ingress-nodeport/basic-auth
cd /opt/ingress-nodeport/basic-auth/#生成用户密码认证文件,创建 secret 资源进行存储
yum -y install httpd
htpasswd -c auth zhangsan #认证文件名必须为 auth
kubectl create secret generic basic-auth --from-file=auth#创建 ingress 资源
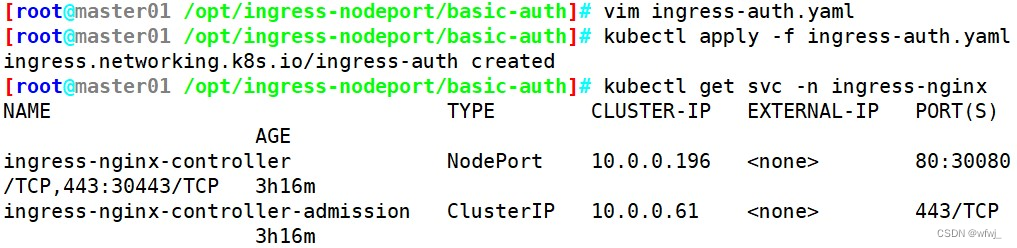
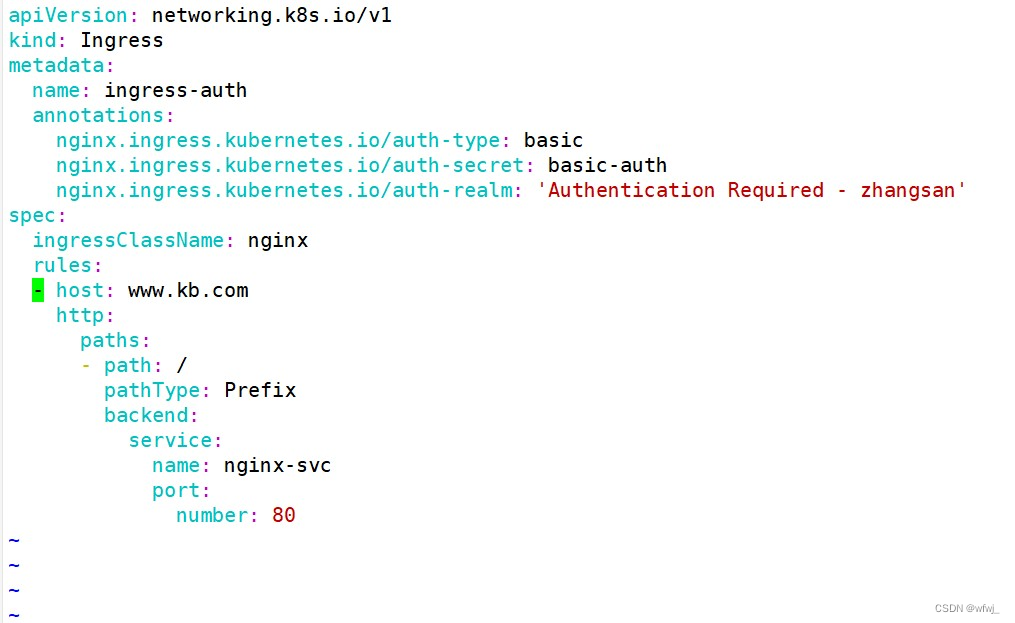
vim ingress-auth.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress-authannotations:#设置认证类型basicnginx.ingress.kubernetes.io/auth-type: basic#设置secret资源名称basic-authnginx.ingress.kubernetes.io/auth-secret: basic-auth#设置认证窗口提示信息nginx.ingress.kubernetes.io/auth-realm: 'Authentication Required - zhangsan'
spec:ingressClassName: nginxrules:- host: www.kb.comhttp:paths:- path: /pathType: Prefixbackend:service: name: nginx-svcport:number: 80
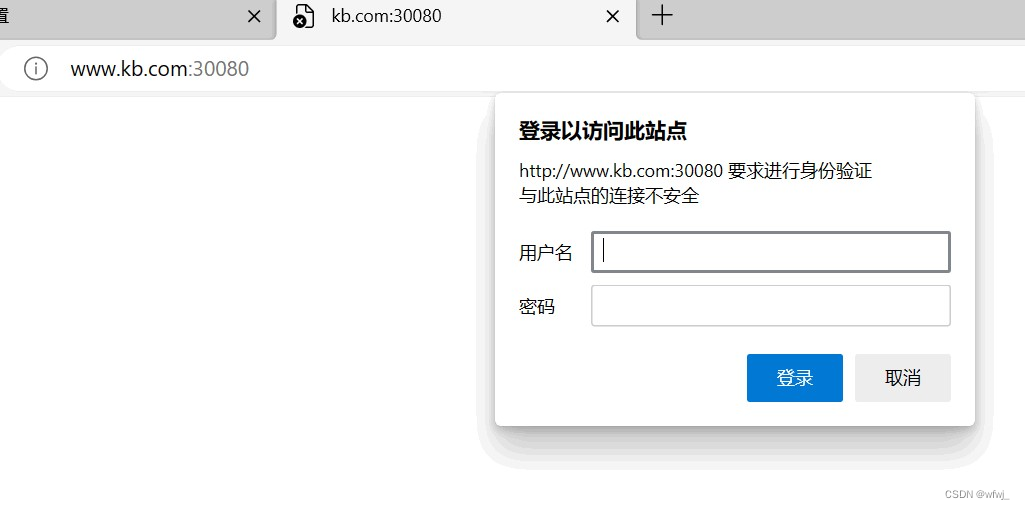
//具体详细设置方法可参考官网https://kubernetes.github.io/ingress-nginx/examples/auth/basic/kubectl apply -f ingress-auth.yaml#访问测试
kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.0.0.196 <none> 80:30080/TCP,443:30443/TCP 3h16m
ingress-nginx-controller-admission ClusterIP 10.0.0.61 <none> 443/TCP 3h16mecho '192.168.58.63 www.kb.com' >> /etc/hosts浏览器访问:http://www.kb.com:30080//Nginx 进行重写
#metadata.annotations 配置说明
●nginx.ingress.kubernetes.io/rewrite-target: <字符串> #必须重定向流量的目标URI
●nginx.ingress.kubernetes.io/ssl-redirect: <布尔值> #指示位置部分是否仅可访问SSL(当Ingress包含证书时,默认为true)
●nginx.ingress.kubernetes.io/force-ssl-redirect: <布尔值> #即使Ingress未启用TLS,也强制重定向到HTTPS
●nginx.ingress.kubernetes.io/app-root: <字符串> #定义Controller必须重定向的应用程序根,如果它在'/'上下文中
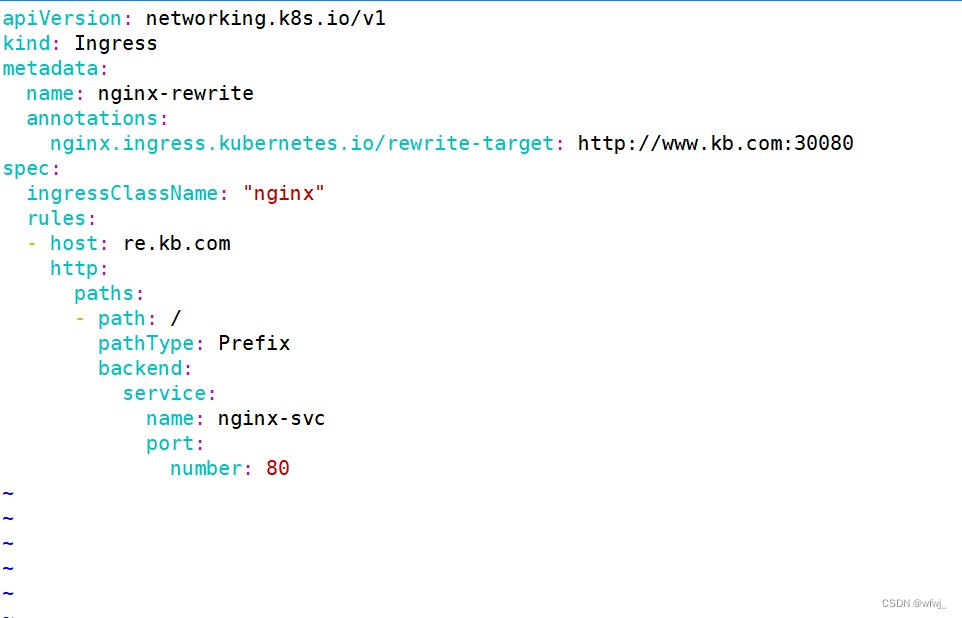
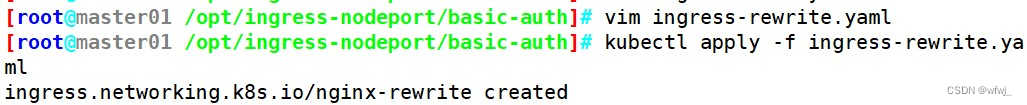
●nginx.ingress.kubernetes.io/use-regex: <布尔值> #指示Ingress上定义的路径是否使用正则表达式vim ingress-rewrite.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: nginx-rewriteannotations:nginx.ingress.kubernetes.io/rewrite-target: http://www.kb.com:30080
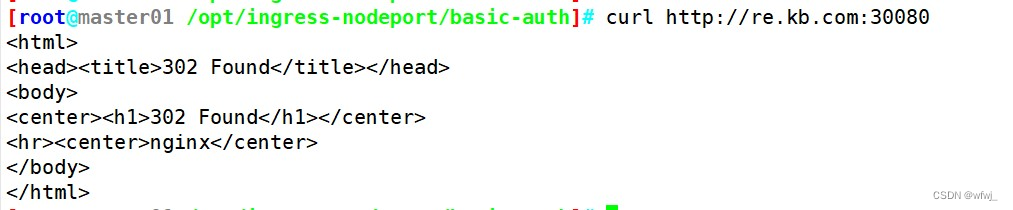
spec:ingressClassName: "nginx"rules:- host: re.kb.comhttp:paths:- path: /pathType: Prefixbackend:#由于re.kb.com只是用于跳转不需要真实站点存在,因此svc资源名称可随意定义service: name: nginx-svcport:number: 80kubectl apply -f ingress-rewrite.yamlecho '192.168.58.63 re.kb.com' >> /etc/hosts浏览器访问:http://re.kb.com:30080//总结
ingress是k8s集群的请求入口,可以理解为对多个service的再次抽象
通常说的ingress一般包括ingress资源对象及ingress-controller两部分组成
ingress-controller有多种实现,社区原生的是ingress-nginx,根据具体需求选择
ingress自身的暴露有多种方式,需要根据基础环境及业务类型选择合适的方式